The steps in creating a secure information system Stock Photos and Images
(1)See the steps in creating a secure information system stock video clipsPage 1 of 1
The steps in creating a secure information system Stock Photos and Images
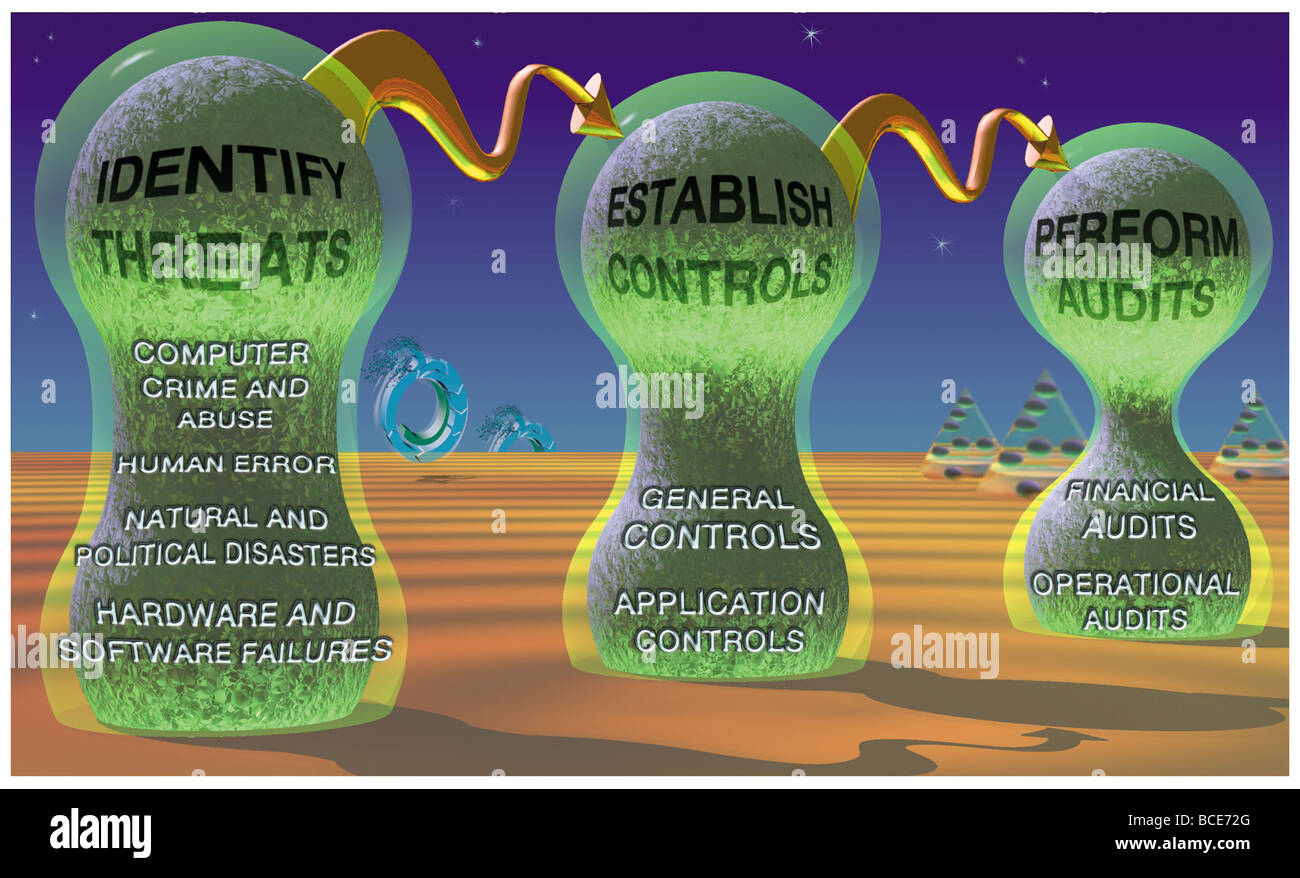 The steps in creating a secure information system: identify threats, establish controls and perform audits to discover breaches. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-the-steps-in-creating-a-secure-information-system-identify-threats-24899128.html
The steps in creating a secure information system: identify threats, establish controls and perform audits to discover breaches. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-the-steps-in-creating-a-secure-information-system-identify-threats-24899128.htmlRMBCE72G–The steps in creating a secure information system: identify threats, establish controls and perform audits to discover breaches.
Search Results for The steps in creating a secure information system Stock Photos and Images (1)
Page 1 of 1