Quick filters:
Page 1 of 10
Software vulnerabilities Stock Photos and Images
 Security system is compromised and is falling apart. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-system-is-compromised-and-is-falling-apart-corporate-data-leakage-hacker-attack-search-for-software-vulnerabilities-violation-of-integrit-image450439626.html
Security system is compromised and is falling apart. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-system-is-compromised-and-is-falling-apart-corporate-data-leakage-hacker-attack-search-for-software-vulnerabilities-violation-of-integrit-image450439626.htmlRF2H4R89E–Security system is compromised and is falling apart. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrit
 Text showing inspiration Ethical Hacking. Business showcase act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-ethical-hacking-business-showcase-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image547418863.html
Text showing inspiration Ethical Hacking. Business showcase act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-ethical-hacking-business-showcase-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image547418863.htmlRM2PPH29K–Text showing inspiration Ethical Hacking. Business showcase act of locating weaknesses and vulnerabilities of computer
 Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business approach Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-approach-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548181382.html
Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business approach Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-approach-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548181382.htmlRF2PRRPXE–Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business approach Protection of mobile phone from threats and vulnerabilities
 Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-for-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548202399.html
Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-for-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548202399.htmlRF2PRTNN3–Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities
 Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478662816.html
Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478662816.htmlRF2JPMY8G–Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News
 09 August 2019, Berlin: ILLUSTRATION - The Apple logo appears on the monitor when an iPhone SE is booted. Apple offers up to a million dollars in rewards for finding vulnerabilities in its software. This amount is intended to cover particularly serious vulnerabilities through which an attacker could access the core of the operating system without user intervention. For Apple, data security is an important selling point, especially for the iPhone. The Group is investing a great deal of time and effort in this, including a separate data safe in the processor. Photo: Stefan Jaitner/dpa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/09-august-2019-berlin-illustration-the-apple-logo-appears-on-the-monitor-when-an-iphone-se-is-booted-apple-offers-up-to-a-million-dollars-in-rewards-for-finding-vulnerabilities-in-its-software-this-amount-is-intended-to-cover-particularly-serious-vulnerabilities-through-which-an-attacker-could-access-the-core-of-the-operating-system-without-user-intervention-for-apple-data-security-is-an-important-selling-point-especially-for-the-iphone-the-group-is-investing-a-great-deal-of-time-and-effort-in-this-including-a-separate-data-safe-in-the-processor-photo-stefan-jaitnerdpa-image263336617.html
09 August 2019, Berlin: ILLUSTRATION - The Apple logo appears on the monitor when an iPhone SE is booted. Apple offers up to a million dollars in rewards for finding vulnerabilities in its software. This amount is intended to cover particularly serious vulnerabilities through which an attacker could access the core of the operating system without user intervention. For Apple, data security is an important selling point, especially for the iPhone. The Group is investing a great deal of time and effort in this, including a separate data safe in the processor. Photo: Stefan Jaitner/dpa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/09-august-2019-berlin-illustration-the-apple-logo-appears-on-the-monitor-when-an-iphone-se-is-booted-apple-offers-up-to-a-million-dollars-in-rewards-for-finding-vulnerabilities-in-its-software-this-amount-is-intended-to-cover-particularly-serious-vulnerabilities-through-which-an-attacker-could-access-the-core-of-the-operating-system-without-user-intervention-for-apple-data-security-is-an-important-selling-point-especially-for-the-iphone-the-group-is-investing-a-great-deal-of-time-and-effort-in-this-including-a-separate-data-safe-in-the-processor-photo-stefan-jaitnerdpa-image263336617.htmlRMW8C0F5–09 August 2019, Berlin: ILLUSTRATION - The Apple logo appears on the monitor when an iPhone SE is booted. Apple offers up to a million dollars in rewards for finding vulnerabilities in its software. This amount is intended to cover particularly serious vulnerabilities through which an attacker could access the core of the operating system without user intervention. For Apple, data security is an important selling point, especially for the iPhone. The Group is investing a great deal of time and effort in this, including a separate data safe in the processor. Photo: Stefan Jaitner/dpa
 1st Lt. Marvin Giron, the executive officer for the El Salvadoran cyber security unit, asks the 157th Communications Flight Airmen questions about an open-source scanning software during a joint exchange in the Centro de Etrenamiento Tactico, El Salvador Aug. 24, 2022. The meeting, coordinated through the State Partnership Program, provided a chance for Airmen to field questions from the El Salvadoran team and exchange policies, management structures and tools for identifying vulnerabilities. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/1st-lt-marvin-giron-the-executive-officer-for-the-el-salvadoran-cyber-security-unit-asks-the-157th-communications-flight-airmen-questions-about-an-open-source-scanning-software-during-a-joint-exchange-in-the-centro-de-etrenamiento-tactico-el-salvador-aug-24-2022-the-meeting-coordinated-through-the-state-partnership-program-provided-a-chance-for-airmen-to-field-questions-from-the-el-salvadoran-team-and-exchange-policies-management-structures-and-tools-for-identifying-vulnerabilities-image509330691.html
1st Lt. Marvin Giron, the executive officer for the El Salvadoran cyber security unit, asks the 157th Communications Flight Airmen questions about an open-source scanning software during a joint exchange in the Centro de Etrenamiento Tactico, El Salvador Aug. 24, 2022. The meeting, coordinated through the State Partnership Program, provided a chance for Airmen to field questions from the El Salvadoran team and exchange policies, management structures and tools for identifying vulnerabilities. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/1st-lt-marvin-giron-the-executive-officer-for-the-el-salvadoran-cyber-security-unit-asks-the-157th-communications-flight-airmen-questions-about-an-open-source-scanning-software-during-a-joint-exchange-in-the-centro-de-etrenamiento-tactico-el-salvador-aug-24-2022-the-meeting-coordinated-through-the-state-partnership-program-provided-a-chance-for-airmen-to-field-questions-from-the-el-salvadoran-team-and-exchange-policies-management-structures-and-tools-for-identifying-vulnerabilities-image509330691.htmlRM2MGJ0DR–1st Lt. Marvin Giron, the executive officer for the El Salvadoran cyber security unit, asks the 157th Communications Flight Airmen questions about an open-source scanning software during a joint exchange in the Centro de Etrenamiento Tactico, El Salvador Aug. 24, 2022. The meeting, coordinated through the State Partnership Program, provided a chance for Airmen to field questions from the El Salvadoran team and exchange policies, management structures and tools for identifying vulnerabilities.
 Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245135.html
Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245135.htmlRM2GPN35K–Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News
 Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604796.html
Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604796.htmlRFR9FB78–Concept on Penetration testing, exploits and vulnerabilities
 Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer and Finding Software Vulnerabilities. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/single-minded-professional-programmer-obsessively-writing-a-code-on-his-desktop-computer-late-at-night-it-specialist-ethical-hacker-working-on-computer-and-finding-software-vulnerabilities-image608207535.html
Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer and Finding Software Vulnerabilities. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/single-minded-professional-programmer-obsessively-writing-a-code-on-his-desktop-computer-late-at-night-it-specialist-ethical-hacker-working-on-computer-and-finding-software-vulnerabilities-image608207535.htmlRF2X9E6WK–Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer and Finding Software Vulnerabilities.
 Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/montreal-canada-april-9-2020-zoom-app-and-logo-on-screen-over-prohibited-ban-sign-zoom-communications-is-remote-conferencing-platform-and-softwa-image352836756.html
Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/montreal-canada-april-9-2020-zoom-app-and-logo-on-screen-over-prohibited-ban-sign-zoom-communications-is-remote-conferencing-platform-and-softwa-image352836756.htmlRF2BE12TM–Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa
 01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916801.html
01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916801.htmlRMEYNRN5–01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1.
 Vulnerabilities Equities Process with Binary code digital technology background. Abstract background with program code and Vulnerabilities Equities Pr Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerabilities-equities-process-with-binary-code-digital-technology-background-abstract-background-with-program-code-and-vulnerabilities-equities-pr-image449247385.html
Vulnerabilities Equities Process with Binary code digital technology background. Abstract background with program code and Vulnerabilities Equities Pr Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerabilities-equities-process-with-binary-code-digital-technology-background-abstract-background-with-program-code-and-vulnerabilities-equities-pr-image449247385.htmlRF2H2TYHD–Vulnerabilities Equities Process with Binary code digital technology background. Abstract background with program code and Vulnerabilities Equities Pr
 Eraser deleting the concept Trojan Horse Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-concept-trojan-horse-image449723413.html
Eraser deleting the concept Trojan Horse Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-concept-trojan-horse-image449723413.htmlRM2H3JJPD–Eraser deleting the concept Trojan Horse
 Shredded paper from a waste paper bin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-shredded-paper-from-a-waste-paper-bin-28007665.html
Shredded paper from a waste paper bin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-shredded-paper-from-a-waste-paper-bin-28007665.htmlRMBHFT1N–Shredded paper from a waste paper bin
 Eraser deleting the word Pop-ups Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-pop-ups-image449722774.html
Eraser deleting the word Pop-ups Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-pop-ups-image449722774.htmlRM2H3JHYJ–Eraser deleting the word Pop-ups
 vulnerability, behind door, leak, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-behind-door-leak-fragile-vulnerabilities-image455847056.html
vulnerability, behind door, leak, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-behind-door-leak-fragile-vulnerabilities-image455847056.htmlRF2HDHHG0–vulnerability, behind door, leak, fragile, vulnerabilities
 Eraser deleting the word Policy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-policy-image449722410.html
Eraser deleting the word Policy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-policy-image449722410.htmlRM2H3JHEJ–Eraser deleting the word Policy
 Expert running server hub diagnostic tests and error checking utilities to find and fix software problems. Engineer monitoring critical systems, checking for malfunctions Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/expert-running-server-hub-diagnostic-tests-and-error-checking-utilities-to-find-and-fix-software-problems-engineer-monitoring-critical-systems-checking-for-malfunctions-image605318538.html
Expert running server hub diagnostic tests and error checking utilities to find and fix software problems. Engineer monitoring critical systems, checking for malfunctions Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/expert-running-server-hub-diagnostic-tests-and-error-checking-utilities-to-find-and-fix-software-problems-engineer-monitoring-critical-systems-checking-for-malfunctions-image605318538.htmlRF2X4PHY6–Expert running server hub diagnostic tests and error checking utilities to find and fix software problems. Engineer monitoring critical systems, checking for malfunctions
 Security breach. Corporate data leakage. Hacker attack. Multilevel network protection. Search for software vulnerabilities. Violation of the integrity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-corporate-data-leakage-hacker-attack-multilevel-network-protection-search-for-software-vulnerabilities-violation-of-the-integrity-image449569031.html
Security breach. Corporate data leakage. Hacker attack. Multilevel network protection. Search for software vulnerabilities. Violation of the integrity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-corporate-data-leakage-hacker-attack-multilevel-network-protection-search-for-software-vulnerabilities-violation-of-the-integrity-image449569031.htmlRF2H3BHTR–Security breach. Corporate data leakage. Hacker attack. Multilevel network protection. Search for software vulnerabilities. Violation of the integrity
 Eraser deleting the word Leakage Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-leakage-image449721858.html
Eraser deleting the word Leakage Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-leakage-image449721858.htmlRM2H3JGPX–Eraser deleting the word Leakage
 Security perimeter breached. The threat of hacking, failure of secondary security systems. Software vulnerabilities. Alarm, property intrusion alert. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-perimeter-breached-the-threat-of-hacking-failure-of-secondary-security-systems-software-vulnerabilities-alarm-property-intrusion-alert-image523130821.html
Security perimeter breached. The threat of hacking, failure of secondary security systems. Software vulnerabilities. Alarm, property intrusion alert. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-perimeter-breached-the-threat-of-hacking-failure-of-secondary-security-systems-software-vulnerabilities-alarm-property-intrusion-alert-image523130821.htmlRF2NB2JKH–Security perimeter breached. The threat of hacking, failure of secondary security systems. Software vulnerabilities. Alarm, property intrusion alert.
 Sign displaying Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548197232.html
Sign displaying Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548197232.htmlRF2PRTF4G–Sign displaying Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities
 Security breach. Safety failure. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrity, destruction of sy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-safety-failure-corporate-data-leakage-hacker-attack-search-for-software-vulnerabilities-violation-of-integrity-destruction-of-sy-image476231673.html
Security breach. Safety failure. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrity, destruction of sy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-safety-failure-corporate-data-leakage-hacker-attack-search-for-software-vulnerabilities-violation-of-integrity-destruction-of-sy-image476231673.htmlRF2JJP6A1–Security breach. Safety failure. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrity, destruction of sy
 Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business showcase Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-showcase-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548176595.html
Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business showcase Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-showcase-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548176595.htmlRF2PRRGRF–Hand writing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business showcase Protection of mobile phone from threats and vulnerabilities
 Security chain gave a breakdown. Compromised security network. Hacker attack. Software vulnerabilities. Critical vulnerability. Defect and program err Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-chain-gave-a-breakdown-compromised-security-network-hacker-attack-software-vulnerabilities-critical-vulnerability-defect-and-program-err-image460397679.html
Security chain gave a breakdown. Compromised security network. Hacker attack. Software vulnerabilities. Critical vulnerability. Defect and program err Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-chain-gave-a-breakdown-compromised-security-network-hacker-attack-software-vulnerabilities-critical-vulnerability-defect-and-program-err-image460397679.htmlRF2HN0WX7–Security chain gave a breakdown. Compromised security network. Hacker attack. Software vulnerabilities. Critical vulnerability. Defect and program err
 Writing displaying text Mobile Security. Business overview Protection of mobile phone from threats and vulnerabilities Office Supplies Over Desk With Keyboard And Glasses And Coffee Cup For Working Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-displaying-text-mobile-security-business-overview-protection-of-mobile-phone-from-threats-and-vulnerabilities-office-supplies-over-desk-with-keyboard-and-glasses-and-coffee-cup-for-working-image483543487.html
Writing displaying text Mobile Security. Business overview Protection of mobile phone from threats and vulnerabilities Office Supplies Over Desk With Keyboard And Glasses And Coffee Cup For Working Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-displaying-text-mobile-security-business-overview-protection-of-mobile-phone-from-threats-and-vulnerabilities-office-supplies-over-desk-with-keyboard-and-glasses-and-coffee-cup-for-working-image483543487.htmlRF2K2K8J7–Writing displaying text Mobile Security. Business overview Protection of mobile phone from threats and vulnerabilities Office Supplies Over Desk With Keyboard And Glasses And Coffee Cup For Working
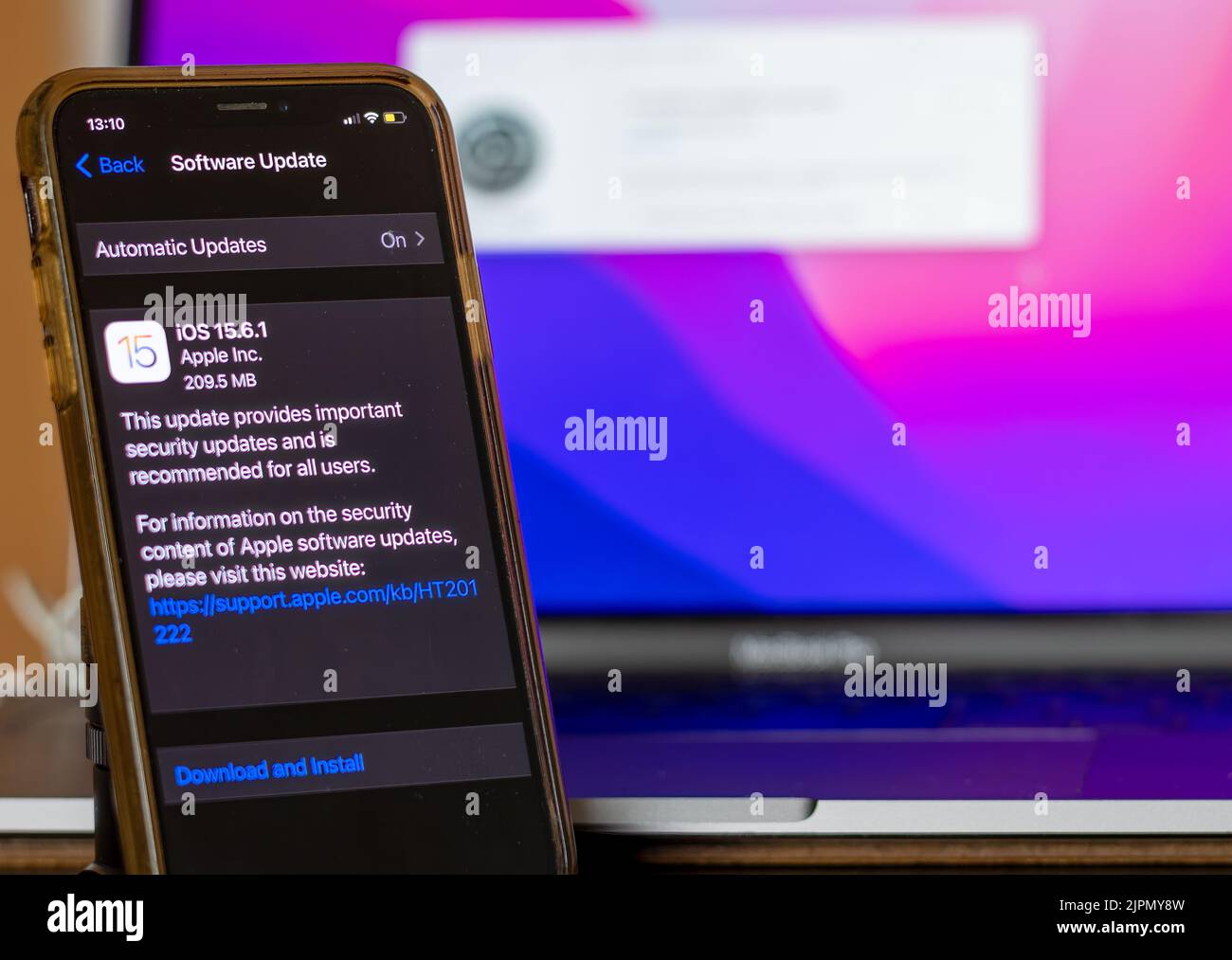 Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478662825.html
Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478662825.htmlRF2JPMY8W–Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News
 Fixing bugs and accumulating new ones. Development and testing. Finding vulnerabilities and errors in software for rewards. Debugging. Troubleshooting Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/fixing-bugs-and-accumulating-new-ones-development-and-testing-finding-vulnerabilities-and-errors-in-software-for-rewards-debugging-troubleshooting-image597175563.html
Fixing bugs and accumulating new ones. Development and testing. Finding vulnerabilities and errors in software for rewards. Debugging. Troubleshooting Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/fixing-bugs-and-accumulating-new-ones-development-and-testing-finding-vulnerabilities-and-errors-in-software-for-rewards-debugging-troubleshooting-image597175563.htmlRF2WKFKEK–Fixing bugs and accumulating new ones. Development and testing. Finding vulnerabilities and errors in software for rewards. Debugging. Troubleshooting
 Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245121.html
Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245121.htmlRM2GPN355–Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News
 Hacking a system component. Security breach, unauthorized access, threat to system integrity. Corporate data leakage. Hacker attack. Multilevel networ Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacking-a-system-component-security-breach-unauthorized-access-threat-to-system-integrity-corporate-data-leakage-hacker-attack-multilevel-networ-image449569171.html
Hacking a system component. Security breach, unauthorized access, threat to system integrity. Corporate data leakage. Hacker attack. Multilevel networ Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacking-a-system-component-security-breach-unauthorized-access-threat-to-system-integrity-corporate-data-leakage-hacker-attack-multilevel-networ-image449569171.htmlRF2H3BJ1R–Hacking a system component. Security breach, unauthorized access, threat to system integrity. Corporate data leakage. Hacker attack. Multilevel networ
 Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604693.html
Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604693.htmlRFR9FB3H–Concept on Penetration testing, exploits and vulnerabilities
 Lots of computer bugs and viruses. Finding vulnerabilities and errors in software for rewards. Debugging, testing and code review. Troubleshooting. Br Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lots-of-computer-bugs-and-viruses-finding-vulnerabilities-and-errors-in-software-for-rewards-debugging-testing-and-code-review-troubleshooting-br-image577149689.html
Lots of computer bugs and viruses. Finding vulnerabilities and errors in software for rewards. Debugging, testing and code review. Troubleshooting. Br Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lots-of-computer-bugs-and-viruses-finding-vulnerabilities-and-errors-in-software-for-rewards-debugging-testing-and-code-review-troubleshooting-br-image577149689.htmlRF2TEYC8W–Lots of computer bugs and viruses. Finding vulnerabilities and errors in software for rewards. Debugging, testing and code review. Troubleshooting. Br
 Conceptual display Mobile Security, Conceptual photo Protection of mobile phone from threats and vulnerabilities Downloading Documents Concept, Upload Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-security-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-downloading-documents-concept-upload-image461091396.html
Conceptual display Mobile Security, Conceptual photo Protection of mobile phone from threats and vulnerabilities Downloading Documents Concept, Upload Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-security-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-downloading-documents-concept-upload-image461091396.htmlRF2HP4ENT–Conceptual display Mobile Security, Conceptual photo Protection of mobile phone from threats and vulnerabilities Downloading Documents Concept, Upload
 Fixing a security vulnerability in the system. Cyber security and corporate data protection. Error correction. Hacker attack. Malfunction, breakdown, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/fixing-a-security-vulnerability-in-the-system-cyber-security-and-corporate-data-protection-error-correction-hacker-attack-malfunction-breakdown-image466764634.html
Fixing a security vulnerability in the system. Cyber security and corporate data protection. Error correction. Hacker attack. Malfunction, breakdown, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/fixing-a-security-vulnerability-in-the-system-cyber-security-and-corporate-data-protection-error-correction-hacker-attack-malfunction-breakdown-image466764634.htmlRF2J3AY1E–Fixing a security vulnerability in the system. Cyber security and corporate data protection. Error correction. Hacker attack. Malfunction, breakdown,
 Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer, Finding Software Vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/single-minded-professional-programmer-obsessively-writing-a-code-on-his-desktop-computer-late-at-night-it-specialist-ethical-hacker-working-on-computer-finding-software-vulnerabilities-image608205690.html
Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer, Finding Software Vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/single-minded-professional-programmer-obsessively-writing-a-code-on-his-desktop-computer-late-at-night-it-specialist-ethical-hacker-working-on-computer-finding-software-vulnerabilities-image608205690.htmlRF2X9E4FP–Single-Minded Professional Programmer Obsessively Writing a Code on His Desktop Computer, Late at Night. IT Specialist Ethical Hacker Working on Computer, Finding Software Vulnerabilities
 Security breach intrusion into the corporate network. Corporate data leakage. Hacker attack. Multilevel protection. Search for software vulnerabilitie Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-intrusion-into-the-corporate-network-corporate-data-leakage-hacker-attack-multilevel-protection-search-for-software-vulnerabilitie-image475412770.html
Security breach intrusion into the corporate network. Corporate data leakage. Hacker attack. Multilevel protection. Search for software vulnerabilitie Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-intrusion-into-the-corporate-network-corporate-data-leakage-hacker-attack-multilevel-protection-search-for-software-vulnerabilitie-image475412770.htmlRF2JHCWRE–Security breach intrusion into the corporate network. Corporate data leakage. Hacker attack. Multilevel protection. Search for software vulnerabilitie
 Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/montreal-canada-april-9-2020-zoom-app-and-logo-on-screen-over-prohibited-ban-sign-zoom-communications-is-remote-conferencing-platform-and-softwa-image352836755.html
Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/montreal-canada-april-9-2020-zoom-app-and-logo-on-screen-over-prohibited-ban-sign-zoom-communications-is-remote-conferencing-platform-and-softwa-image352836755.htmlRF2BE12TK–Montreal, Canada - April 9, 2020: Zoom app and logo on screen over prohibited ban sign. Zoom Communications is remote conferencing platform and softwa
 01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916803.html
01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916803.htmlRMEYNRN7–01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1.
 Eraser deleting the word Hacking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-hacking-image449721503.html
Eraser deleting the word Hacking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-hacking-image449721503.htmlRM2H3JGA7–Eraser deleting the word Hacking
 Shredded paper from a waste paper bin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-shredded-paper-from-a-waste-paper-bin-28006173.html
Shredded paper from a waste paper bin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-shredded-paper-from-a-waste-paper-bin-28006173.htmlRMBHFP4D–Shredded paper from a waste paper bin
 Inspiration showing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/inspiration-showing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-for-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548164237.html
Inspiration showing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/inspiration-showing-sign-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-for-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548164237.htmlRF2PRR125–Inspiration showing sign Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Word for Protection of mobile phone from threats and vulnerabilities
 Eraser deleting the word Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-malware-image449720800.html
Eraser deleting the word Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-malware-image449720800.htmlRM2H3JFD4–Eraser deleting the word Malware
 Reliable protection reflects all attacks. Hacker and cyber attack, firewall. Hybrid war. Data theft and industrial espionage. Safety and security, hig Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reliable-protection-reflects-all-attacks-hacker-and-cyber-attack-firewall-hybrid-war-data-theft-and-industrial-espionage-safety-and-security-hig-image484787188.html
Reliable protection reflects all attacks. Hacker and cyber attack, firewall. Hybrid war. Data theft and industrial espionage. Safety and security, hig Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reliable-protection-reflects-all-attacks-hacker-and-cyber-attack-firewall-hybrid-war-data-theft-and-industrial-espionage-safety-and-security-hig-image484787188.htmlRF2K4KY04–Reliable protection reflects all attacks. Hacker and cyber attack, firewall. Hybrid war. Data theft and industrial espionage. Safety and security, hig
 Eraser deleting the word Lurking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-lurking-image449720464.html
Eraser deleting the word Lurking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-lurking-image449720464.htmlRM2H3JF14–Eraser deleting the word Lurking
 Unauthorized entry into the system. Hacker attack, security breach. Weak link. System vulnerability. Data leakage and industrial espionage. Sabotage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unauthorized-entry-into-the-system-hacker-attack-security-breach-weak-link-system-vulnerability-data-leakage-and-industrial-espionage-sabotage-image478499227.html
Unauthorized entry into the system. Hacker attack, security breach. Weak link. System vulnerability. Data leakage and industrial espionage. Sabotage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unauthorized-entry-into-the-system-hacker-attack-security-breach-weak-link-system-vulnerability-data-leakage-and-industrial-espionage-sabotage-image478499227.htmlRF2JPDEJ3–Unauthorized entry into the system. Hacker attack, security breach. Weak link. System vulnerability. Data leakage and industrial espionage. Sabotage.
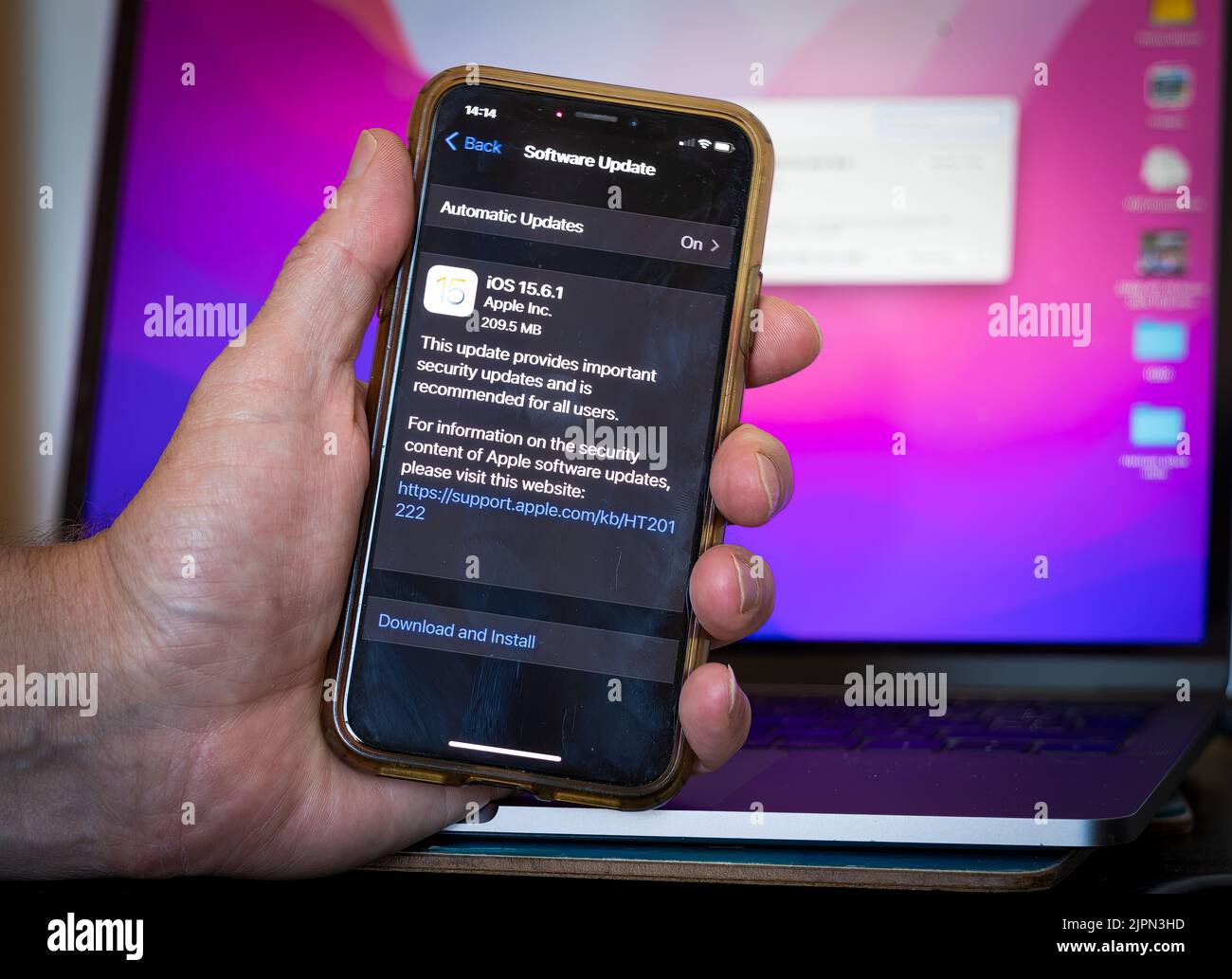 Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478666201.html
Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/billingshurst-west-sussex-uk-19th-aug-2022-apple-has-released-updates-to-fix-security-flaws-on-iphones-ipads-and-mac-devices-after-hackers-actively-exploited-security-vulnerabilities-and-flaws-credit-andy-solomanalamy-live-news-image478666201.htmlRF2JPN3HD–Billingshurst, West Sussex, UK. 19th Aug, 2022. Apple has released updates to fix security flaws on iPhones, iPads and Mac devices after hackers 'actively exploited' security vulnerabilities and flaws. Credit: Andy Soloman/Alamy Live News
 A hacker breaks into electronic cryptocurrency wallets. Spy agents parasitize on financial flows. Gain unauthorized access to users digital assets. Fi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-hacker-breaks-into-electronic-cryptocurrency-wallets-spy-agents-parasitize-on-financial-flows-gain-unauthorized-access-to-users-digital-assets-fi-image559860929.html
A hacker breaks into electronic cryptocurrency wallets. Spy agents parasitize on financial flows. Gain unauthorized access to users digital assets. Fi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-hacker-breaks-into-electronic-cryptocurrency-wallets-spy-agents-parasitize-on-financial-flows-gain-unauthorized-access-to-users-digital-assets-fi-image559860929.htmlRF2RERT95–A hacker breaks into electronic cryptocurrency wallets. Spy agents parasitize on financial flows. Gain unauthorized access to users digital assets. Fi
 Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245112.html
Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444245112.htmlRM2GPN34T–Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News
 A hacker breaks into the system and servers. Gain unauthorized access to users digital assets. Fight against cybercrime. Cyber security. Preserving da Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-hacker-breaks-into-the-system-and-servers-gain-unauthorized-access-to-users-digital-assets-fight-against-cybercrime-cyber-security-preserving-da-image594469031.html
A hacker breaks into the system and servers. Gain unauthorized access to users digital assets. Fight against cybercrime. Cyber security. Preserving da Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-hacker-breaks-into-the-system-and-servers-gain-unauthorized-access-to-users-digital-assets-fight-against-cybercrime-cyber-security-preserving-da-image594469031.htmlRF2WF4B8R–A hacker breaks into the system and servers. Gain unauthorized access to users digital assets. Fight against cybercrime. Cyber security. Preserving da
 Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604864.html
Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604864.htmlRFR9FB9M–Concept on Penetration testing, exploits and vulnerabilities
 The computer virus infects the team through one member. Corporate system security. Malware. Network defense breakthrough. Security holes and bugs. Esp Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-computer-virus-infects-the-team-through-one-member-corporate-system-security-malware-network-defense-breakthrough-security-holes-and-bugs-esp-image499312134.html
The computer virus infects the team through one member. Corporate system security. Malware. Network defense breakthrough. Security holes and bugs. Esp Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-computer-virus-infects-the-team-through-one-member-corporate-system-security-malware-network-defense-breakthrough-security-holes-and-bugs-esp-image499312134.htmlRF2M09HM6–The computer virus infects the team through one member. Corporate system security. Malware. Network defense breakthrough. Security holes and bugs. Esp
 Conceptual display Mobile Security, Word Written on Protection of mobile phone from threats and vulnerabilities Transcribing Internet Meeting Audio Re Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-security-word-written-on-protection-of-mobile-phone-from-threats-and-vulnerabilities-transcribing-internet-meeting-audio-re-image461084616.html
Conceptual display Mobile Security, Word Written on Protection of mobile phone from threats and vulnerabilities Transcribing Internet Meeting Audio Re Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-security-word-written-on-protection-of-mobile-phone-from-threats-and-vulnerabilities-transcribing-internet-meeting-audio-re-image461084616.htmlRF2HP463M–Conceptual display Mobile Security, Word Written on Protection of mobile phone from threats and vulnerabilities Transcribing Internet Meeting Audio Re
 Business communication through risks of interception threat. Secure communications and data transfer. Industrial and financial espionage. Spies and ha Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/business-communication-through-risks-of-interception-threat-secure-communications-and-data-transfer-industrial-and-financial-espionage-spies-and-ha-image499312116.html
Business communication through risks of interception threat. Secure communications and data transfer. Industrial and financial espionage. Spies and ha Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/business-communication-through-risks-of-interception-threat-secure-communications-and-data-transfer-industrial-and-financial-espionage-spies-and-ha-image499312116.htmlRF2M09HKG–Business communication through risks of interception threat. Secure communications and data transfer. Industrial and financial espionage. Spies and ha
 vulnerability, behind door, leak, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-behind-door-leak-fragile-vulnerabilities-image455847054.html
vulnerability, behind door, leak, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-behind-door-leak-fragile-vulnerabilities-image455847054.htmlRF2HDHHFX–vulnerability, behind door, leak, fragile, vulnerabilities
 Coworkers running data center hardware diagnostic tests to determine and service software issues. Servicemen using laptop and tablet to fix critical systems, checking for blips Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/coworkers-running-data-center-hardware-diagnostic-tests-to-determine-and-service-software-issues-servicemen-using-laptop-and-tablet-to-fix-critical-systems-checking-for-blips-image598657955.html
Coworkers running data center hardware diagnostic tests to determine and service software issues. Servicemen using laptop and tablet to fix critical systems, checking for blips Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/coworkers-running-data-center-hardware-diagnostic-tests-to-determine-and-service-software-issues-servicemen-using-laptop-and-tablet-to-fix-critical-systems-checking-for-blips-image598657955.htmlRF2WNY697–Coworkers running data center hardware diagnostic tests to determine and service software issues. Servicemen using laptop and tablet to fix critical systems, checking for blips
 MOBILE SECURITY - 3D Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-mobile-security-3d-concept-55222157.html
MOBILE SECURITY - 3D Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-mobile-security-3d-concept-55222157.htmlRMD5RGBW–MOBILE SECURITY - 3D Concept
 01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916804.html
01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916804.htmlRMEYNRN8–01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1.
 DevSecOps Concept - Integration of Security Testing Throughout the Development and Operations IT Lifecycle - Tools to Release Resilient Software Faste Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devsecops-concept-integration-of-security-testing-throughout-the-development-and-operations-it-lifecycle-tools-to-release-resilient-software-faste-image470408043.html
DevSecOps Concept - Integration of Security Testing Throughout the Development and Operations IT Lifecycle - Tools to Release Resilient Software Faste Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devsecops-concept-integration-of-security-testing-throughout-the-development-and-operations-it-lifecycle-tools-to-release-resilient-software-faste-image470408043.htmlRF2J98X77–DevSecOps Concept - Integration of Security Testing Throughout the Development and Operations IT Lifecycle - Tools to Release Resilient Software Faste
RF2E9MRB2–Certified Ethical Hacking - CEH icon set showing virus, exposing vulnerabilities, and hacker
 Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business overview Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-overview-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548163947.html
Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business overview Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-business-overview-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548163947.htmlRF2PRR0KR–Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Business overview Protection of mobile phone from threats and vulnerabilities
 Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/zero-day-exploit-concept-anxious-user-realizes-the-countdown-as-protection-shatters-indicating-unpatched-software-vulnerabilities-imminent-threat-timely-cyber-defense-flat-vector-illustration-image598705623.html
Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/zero-day-exploit-concept-anxious-user-realizes-the-countdown-as-protection-shatters-indicating-unpatched-software-vulnerabilities-imminent-threat-timely-cyber-defense-flat-vector-illustration-image598705623.htmlRF2WP1B3K–Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration
RF2T9XCAN–Adobe Flash Player discontinued software app logo icon symbol, obsolete technology, obsolete flash games and animations concept laptop computer monito
 Eraser deleting the word Virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-virus-image449720521.html
Eraser deleting the word Virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/eraser-deleting-the-word-virus-image449720521.htmlRM2H3JF35–Eraser deleting the word Virus
RF2R0CDJK–Wooden cubes with cyber icons with the concept of network security vulnerabilities
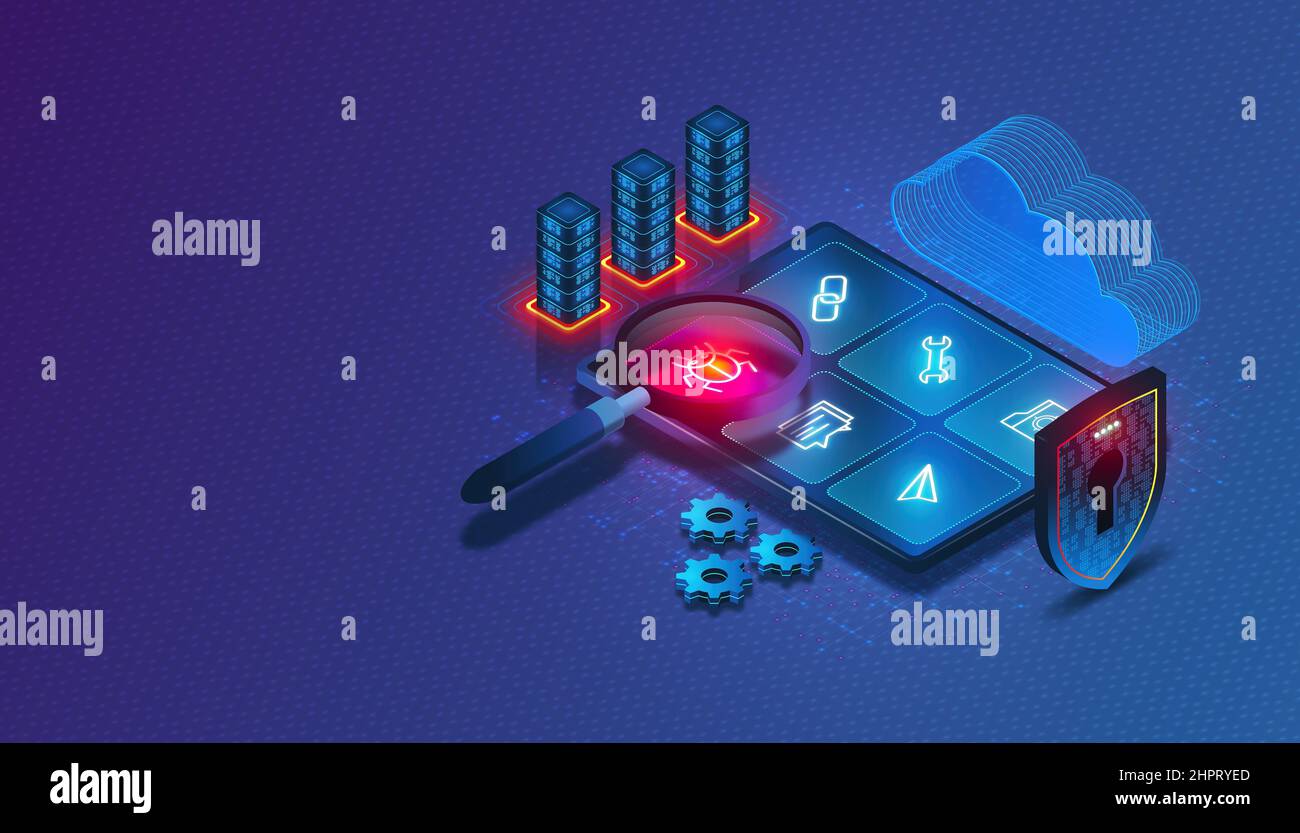 Application Security Testing Concept with Digital Magnifying Glass Scanning Applications to Detect Vulnerabilities - AST - Process of Making Apps Resi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/application-security-testing-concept-with-digital-magnifying-glass-scanning-applications-to-detect-vulnerabilities-ast-process-of-making-apps-resi-image461518469.html
Application Security Testing Concept with Digital Magnifying Glass Scanning Applications to Detect Vulnerabilities - AST - Process of Making Apps Resi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/application-security-testing-concept-with-digital-magnifying-glass-scanning-applications-to-detect-vulnerabilities-ast-process-of-making-apps-resi-image461518469.htmlRF2HPRYED–Application Security Testing Concept with Digital Magnifying Glass Scanning Applications to Detect Vulnerabilities - AST - Process of Making Apps Resi
RF2KAE0E2–A top view of wooden cubes with cyber icons with the concept of network security vulnerabilities
 Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444285930.html
Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/berlin-germany-30th-sep-2021-the-app-id-wallet-in-the-apple-app-store-which-is-necessary-for-the-display-of-the-digital-drivers-license-on-thursday-9302021-it-could-no-longer-be-found-there-after-experts-pointed-out-security-vulnerabilities-in-wallet-previously-the-app-had-received-an-extremely-poor-rating-of-just-11-stars-credit-christoph-dernbachdpaalamy-live-news-image444285930.htmlRM2GPPY6J–Berlin, Germany. 30th Sep, 2021. The app 'ID Wallet' in the Apple App Store, which is necessary for the display of the digital driver's license. On Thursday (9/30/2021), it could no longer be found there after experts pointed out security vulnerabilities in Wallet. Previously, the app had received an extremely poor rating of just 1.1 stars. Credit: Christoph Dernbach/dpa/Alamy Live News
 Vulnerabilities text written on Programming code abstract technology background of software developer and Computer script. Vulnerabilities concept of Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerabilities-text-written-on-programming-code-abstract-technology-background-of-software-developer-and-computer-script-vulnerabilities-concept-of-image449241568.html
Vulnerabilities text written on Programming code abstract technology background of software developer and Computer script. Vulnerabilities concept of Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerabilities-text-written-on-programming-code-abstract-technology-background-of-software-developer-and-computer-script-vulnerabilities-concept-of-image449241568.htmlRF2H2TM5M–Vulnerabilities text written on Programming code abstract technology background of software developer and Computer script. Vulnerabilities concept of
 Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604659.html
Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604659.htmlRFR9FB2B–Concept on Penetration testing, exploits and vulnerabilities
 Hamburg, Germany. 20th June, 2019. On the topic service report of 9 November 2020: 'In most cases the iPhone answers by itself. But it's never wrong to check for updates yourself. Credit: Christin Klose/dpa-tmn/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hamburg-germany-20th-june-2019-on-the-topic-service-report-of-9-november-2020-in-most-cases-the-iphone-answers-by-itself-but-its-never-wrong-to-check-for-updates-yourself-credit-christin-klosedpa-tmndpaalamy-live-news-image384854585.html
Hamburg, Germany. 20th June, 2019. On the topic service report of 9 November 2020: 'In most cases the iPhone answers by itself. But it's never wrong to check for updates yourself. Credit: Christin Klose/dpa-tmn/dpa/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hamburg-germany-20th-june-2019-on-the-topic-service-report-of-9-november-2020-in-most-cases-the-iphone-answers-by-itself-but-its-never-wrong-to-check-for-updates-yourself-credit-christin-klosedpa-tmndpaalamy-live-news-image384854585.htmlRM2DA3HXH–Hamburg, Germany. 20th June, 2019. On the topic service report of 9 November 2020: 'In most cases the iPhone answers by itself. But it's never wrong to check for updates yourself. Credit: Christin Klose/dpa-tmn/dpa/Alamy Live News
 Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-written-on-protection-of-mobile-phone-from-t-image548485448.html
Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-written-on-protection-of-mobile-phone-from-t-image548485448.htmlRF2PT9JP0–Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t
 Viruses attack the security system. Resistance to cyber attacks. Protection of data and network infrastructure. The probability of a defense breakthro Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/viruses-attack-the-security-system-resistance-to-cyber-attacks-protection-of-data-and-network-infrastructure-the-probability-of-a-defense-breakthro-image491715123.html
Viruses attack the security system. Resistance to cyber attacks. Protection of data and network infrastructure. The probability of a defense breakthro Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/viruses-attack-the-security-system-resistance-to-cyber-attacks-protection-of-data-and-network-infrastructure-the-probability-of-a-defense-breakthro-image491715123.htmlRF2KFYFJB–Viruses attack the security system. Resistance to cyber attacks. Protection of data and network infrastructure. The probability of a defense breakthro
 computer crime, vulnerability, backdoor, computer crimes, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-crime-vulnerability-backdoor-computer-crimes-fragile-vulnerabilities-image455847159.html
computer crime, vulnerability, backdoor, computer crimes, fragile, vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-crime-vulnerability-backdoor-computer-crimes-fragile-vulnerabilities-image455847159.htmlRF2HDHHKK–computer crime, vulnerability, backdoor, computer crimes, fragile, vulnerabilities
 Colleagues running data center electronics diagnostic tests to determine and patch software issues. Mechanics using laptop and tablet to repair critical systems, checking for flaws Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/colleagues-running-data-center-electronics-diagnostic-tests-to-determine-and-patch-software-issues-mechanics-using-laptop-and-tablet-to-repair-critical-systems-checking-for-flaws-image563627723.html
Colleagues running data center electronics diagnostic tests to determine and patch software issues. Mechanics using laptop and tablet to repair critical systems, checking for flaws Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/colleagues-running-data-center-electronics-diagnostic-tests-to-determine-and-patch-software-issues-mechanics-using-laptop-and-tablet-to-repair-critical-systems-checking-for-flaws-image563627723.htmlRF2RMYCWF–Colleagues running data center electronics diagnostic tests to determine and patch software issues. Mechanics using laptop and tablet to repair critical systems, checking for flaws
 Conceptual display Ethical Hacking. Internet Concept act of locating weaknesses and vulnerabilities of computer Researching Software Development Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-ethical-hacking-internet-concept-act-of-locating-weaknesses-and-vulnerabilities-of-computer-researching-software-development-image442177172.html
Conceptual display Ethical Hacking. Internet Concept act of locating weaknesses and vulnerabilities of computer Researching Software Development Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-ethical-hacking-internet-concept-act-of-locating-weaknesses-and-vulnerabilities-of-computer-researching-software-development-image442177172.htmlRF2GKAWDT–Conceptual display Ethical Hacking. Internet Concept act of locating weaknesses and vulnerabilities of computer Researching Software Development
 01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916799.html
01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-01-aug-2015-millions-of-pc-users-around-the-world-have-been-installing-85916799.htmlRMEYNRN3–01 Aug 2015 - Millions of PC users around the world have been installing Windows 10 as part of a free upgrade from Windows 7, 8 and 8.1.
 Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342168078.html
Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342168078.htmlRF2ATK2TE–Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer
RF2DMYXNG–Certified Ethical Hacking - CEH icon set showing virus, exposing vulnerabilities, and hacker
 Handwriting text Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Internet Concept Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-internet-concept-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548060304.html
Handwriting text Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Internet Concept Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-internet-concept-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548060304.htmlRF2PRJ8E8–Handwriting text Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Internet Concept Protection of mobile phone from threats and vulnerabilities
 Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/zero-day-exploit-concept-anxious-user-realizes-the-countdown-as-protection-shatters-indicating-unpatched-software-vulnerabilities-imminent-threat-timely-cyber-defense-flat-vector-illustration-image596689714.html
Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/zero-day-exploit-concept-anxious-user-realizes-the-countdown-as-protection-shatters-indicating-unpatched-software-vulnerabilities-imminent-threat-timely-cyber-defense-flat-vector-illustration-image596689714.htmlRF2WJNFPX–Zero-Day Exploit concept. Anxious user realizes the countdown as protection shatters, indicating unpatched software vulnerabilities. Imminent threat. Timely cyber defense. Flat vector illustration
 Antivirus software searching for viruses, malwares and vulnerabilities. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/antivirus-software-searching-for-viruses-malwares-and-vulnerabilities-image327449508.html
Antivirus software searching for viruses, malwares and vulnerabilities. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/antivirus-software-searching-for-viruses-malwares-and-vulnerabilities-image327449508.htmlRF2A0MH58–Antivirus software searching for viruses, malwares and vulnerabilities.
 Microsoft Windows XP operating system update, installing updates one percent progress, do not turn off or unplug your computer OS update message simpl Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/microsoft-windows-xp-operating-system-update-installing-updates-one-percent-progress-do-not-turn-off-or-unplug-your-computer-os-update-message-simpl-image574054424.html
Microsoft Windows XP operating system update, installing updates one percent progress, do not turn off or unplug your computer OS update message simpl Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/microsoft-windows-xp-operating-system-update-installing-updates-one-percent-progress-do-not-turn-off-or-unplug-your-computer-os-update-message-simpl-image574054424.htmlRF2T9XC7M–Microsoft Windows XP operating system update, installing updates one percent progress, do not turn off or unplug your computer OS update message simpl
 Brute-force attack displayed on a Pirate skull on Binary code background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/brute-force-attack-displayed-on-a-pirate-skull-on-binary-code-background-image424814359.html
Brute-force attack displayed on a Pirate skull on Binary code background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/brute-force-attack-displayed-on-a-pirate-skull-on-binary-code-background-image424814359.htmlRM2FK3Y1B–Brute-force attack displayed on a Pirate skull on Binary code background
 DevSecOps - Development, Security and Operations - The Seamless Integration of Security Testing Throughout the Software Development and Operations Lif Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devsecops-development-security-and-operations-the-seamless-integration-of-security-testing-throughout-the-software-development-and-operations-lif-image470509694.html
DevSecOps - Development, Security and Operations - The Seamless Integration of Security Testing Throughout the Software Development and Operations Lif Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devsecops-development-security-and-operations-the-seamless-integration-of-security-testing-throughout-the-software-development-and-operations-lif-image470509694.htmlRF2J9DFWJ–DevSecOps - Development, Security and Operations - The Seamless Integration of Security Testing Throughout the Software Development and Operations Lif
RF2ARFPKB–System vulnerabilities concept icon. Search for software bugs and virus protection. Home network defence idea thin line illustration. Vector isolated
 DevOps and DevSecOps - Approach to App Development and IT Operations that Integrates Security as a Shared Responsibility Throughout the Entire IT Life Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devops-and-devsecops-approach-to-app-development-and-it-operations-that-integrates-security-as-a-shared-responsibility-throughout-the-entire-it-life-image482351787.html
DevOps and DevSecOps - Approach to App Development and IT Operations that Integrates Security as a Shared Responsibility Throughout the Entire IT Life Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/devops-and-devsecops-approach-to-app-development-and-it-operations-that-integrates-security-as-a-shared-responsibility-throughout-the-entire-it-life-image482351787.htmlRF2K0N0HF–DevOps and DevSecOps - Approach to App Development and IT Operations that Integrates Security as a Shared Responsibility Throughout the Entire IT Life
 Various Devices Equipped with a Processor Affected by Meltdown and Spectre Critical Security Vulnerabilities, Which Enable Cyber Attacks, Password or Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/various-devices-equipped-with-a-processor-affected-by-meltdown-and-spectre-critical-security-vulnerabilities-which-enable-cyber-attacks-password-or-image560636977.html
Various Devices Equipped with a Processor Affected by Meltdown and Spectre Critical Security Vulnerabilities, Which Enable Cyber Attacks, Password or Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/various-devices-equipped-with-a-processor-affected-by-meltdown-and-spectre-critical-security-vulnerabilities-which-enable-cyber-attacks-password-or-image560636977.htmlRF2RG3655–Various Devices Equipped with a Processor Affected by Meltdown and Spectre Critical Security Vulnerabilities, Which Enable Cyber Attacks, Password or
 Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604645.html
Concept on Penetration testing, exploits and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-on-penetration-testing-exploits-and-vulnerabilities-image229604645.htmlRFR9FB1W–Concept on Penetration testing, exploits and vulnerabilities
 Web Application Firewall Concept - WAF - Firewall that Filters and Monitors HTTP Traffic Between Web Applications and the Internet - 3D illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-application-firewall-concept-waf-firewall-that-filters-and-monitors-http-traffic-between-web-applications-and-the-internet-3d-illustration-image471507007.html
Web Application Firewall Concept - WAF - Firewall that Filters and Monitors HTTP Traffic Between Web Applications and the Internet - 3D illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-application-firewall-concept-waf-firewall-that-filters-and-monitors-http-traffic-between-web-applications-and-the-internet-3d-illustration-image471507007.htmlRF2JB2YYY–Web Application Firewall Concept - WAF - Firewall that Filters and Monitors HTTP Traffic Between Web Applications and the Internet - 3D illustration
 Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-written-on-protection-of-mobile-phone-from-t-image547971665.html
Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-word-written-on-protection-of-mobile-phone-from-t-image547971665.htmlRF2PRE7CH–Text showing inspiration Mobile SecurityProtection of mobile phone from threats and vulnerabilities, Word Written on Protection of mobile phone from t
 Application Security Monitoring Concept - Cloud-based Solutions which Protect Against Application-level Threats by Identifying Attacks that Target Cod Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/application-security-monitoring-concept-cloud-based-solutions-which-protect-against-application-level-threats-by-identifying-attacks-that-target-cod-image468912383.html
Application Security Monitoring Concept - Cloud-based Solutions which Protect Against Application-level Threats by Identifying Attacks that Target Cod Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/application-security-monitoring-concept-cloud-based-solutions-which-protect-against-application-level-threats-by-identifying-attacks-that-target-cod-image468912383.htmlRF2J6TPER–Application Security Monitoring Concept - Cloud-based Solutions which Protect Against Application-level Threats by Identifying Attacks that Target Cod
RF2PH771C–Cyber space vector line icons set. Technology, Cyberspace, Information, Networking, Security, Online, Computing illustration outline concept symbols
 Overseerer running data center equipment diagnostic tests to determine and debug software issues. Repairman using laptop to analyse critical systems, checking for crashes, close up Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/overseerer-running-data-center-equipment-diagnostic-tests-to-determine-and-debug-software-issues-repairman-using-laptop-to-analyse-critical-systems-checking-for-crashes-close-up-image573124641.html
Overseerer running data center equipment diagnostic tests to determine and debug software issues. Repairman using laptop to analyse critical systems, checking for crashes, close up Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/overseerer-running-data-center-equipment-diagnostic-tests-to-determine-and-debug-software-issues-repairman-using-laptop-to-analyse-critical-systems-checking-for-crashes-close-up-image573124641.htmlRF2T8C295–Overseerer running data center equipment diagnostic tests to determine and debug software issues. Repairman using laptop to analyse critical systems, checking for crashes, close up
 Conceptual caption Ethical Hacking. Business approach act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-ethical-hacking-business-approach-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image491963490.html
Conceptual caption Ethical Hacking. Business approach act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-ethical-hacking-business-approach-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image491963490.htmlRF2KGATCJ–Conceptual caption Ethical Hacking. Business approach act of locating weaknesses and vulnerabilities of computer
RF2PNG4H1–Online security line icons collection. Encryption, Firewall, Antivirus, Malware, Cybercrime, Phishing, Identity theft vector and linear illustration
 Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342264618.html
Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342264618.htmlRF2ATRE0A–Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer
RF2E2H99A–Certified Ethical Hacking - CEH icon set showing virus, exposing vulnerabilities, and hacker
 Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548227611.html
Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-mobile-securityprotection-of-mobile-phone-from-threats-and-vulnerabilities-conceptual-photo-protection-of-mobile-phone-from-threats-and-vulnerabilities-image548227611.htmlRF2PRWWWF–Conceptual display Mobile SecurityProtection of mobile phone from threats and vulnerabilities. Conceptual photo Protection of mobile phone from threats and vulnerabilities
 Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342170395.html
Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-ethical-hacking-conceptual-photo-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image342170395.htmlRF2ATK5R7–Handwriting text Ethical Hacking. Conceptual photo act of locating weaknesses and vulnerabilities of computer
Search Results for Software vulnerabilities Stock Photos and Images (902)
Page 1 of 10