Quick filters:
Page 1 of 461
Security login Stock Photos and Images
 View of a Security login window displayed on a futuristic interface - Connection concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-view-of-a-security-login-window-displayed-on-a-futuristic-interface-161625527.html
View of a Security login window displayed on a futuristic interface - Connection concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-view-of-a-security-login-window-displayed-on-a-futuristic-interface-161625527.htmlRFKAXK07–View of a Security login window displayed on a futuristic interface - Connection concept
RF2T8B1J9–Isometric computer display with security login form and floating icons of security, network, virus, cloud. Ideal for clean tech visuals
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126097146.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126097146.htmlRFH9465E–Password Security Login Technology Business Concept
 ipad2 passcode security login screen Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-ipad2-passcode-security-login-screen-42044664.html
ipad2 passcode security login screen Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-ipad2-passcode-security-login-screen-42044664.htmlRMCCB8B4–ipad2 passcode security login screen
 a man looks at two padlocks and points to the open one. Concept of choice, new solutions. Electronic security login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-man-looks-at-two-padlocks-and-points-to-the-open-one-concept-of-choice-new-solutions-electronic-security-login-image334099203.html
a man looks at two padlocks and points to the open one. Concept of choice, new solutions. Electronic security login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-man-looks-at-two-padlocks-and-points-to-the-open-one-concept-of-choice-new-solutions-electronic-security-login-image334099203.htmlRF2ABFEXB–a man looks at two padlocks and points to the open one. Concept of choice, new solutions. Electronic security login
 Computer Security Login incorrect Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-computer-security-login-incorrect-88549715.html
Computer Security Login incorrect Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-computer-security-login-incorrect-88549715.htmlRFF41P1R–Computer Security Login incorrect
 Too easy password on sticky notes on laptop screen. Focus on password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-too-easy-password-on-sticky-notes-on-laptop-screen-focus-on-password-94694574.html
Too easy password on sticky notes on laptop screen. Focus on password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-too-easy-password-on-sticky-notes-on-laptop-screen-focus-on-password-94694574.htmlRFFE1KW2–Too easy password on sticky notes on laptop screen. Focus on password
 login and password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-and-password-image62365365.html
login and password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-and-password-image62365365.htmlRFDHCYJD–login and password
 Typing online account password on laptop computer keyboard, internet security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-typing-online-account-password-on-laptop-computer-keyboard-internet-129383655.html
Typing online account password on laptop computer keyboard, internet security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-typing-online-account-password-on-laptop-computer-keyboard-internet-129383655.htmlRFHEDX4R–Typing online account password on laptop computer keyboard, internet security concept
 Data Security Concept. Yellow paper note with closed padlock on a black keyboard. Close up. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-data-security-concept-yellow-paper-note-with-closed-padlock-on-a-black-164931131.html
Data Security Concept. Yellow paper note with closed padlock on a black keyboard. Close up. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-data-security-concept-yellow-paper-note-with-closed-padlock-on-a-black-164931131.htmlRFKG979F–Data Security Concept. Yellow paper note with closed padlock on a black keyboard. Close up.
 Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258848995.html
Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258848995.htmlRFW13GEY–Steel safe with login and password screen. 3D illustration.
 Businessman using tablet to login represents protection concept of cyber security and data security including secure login. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-using-tablet-to-login-represents-protection-concept-of-cyber-security-and-data-security-including-secure-login-image596257891.html
Businessman using tablet to login represents protection concept of cyber security and data security including secure login. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-using-tablet-to-login-represents-protection-concept-of-cyber-security-and-data-security-including-secure-login-image596257891.htmlRF2WJ1W0K–Businessman using tablet to login represents protection concept of cyber security and data security including secure login.
 Cyber security concept with manager providing authentication credentials (login, password) to business person to access confidential data on computer Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-cyber-security-concept-with-manager-providing-authentication-credentials-161062590.html
Cyber security concept with manager providing authentication credentials (login, password) to business person to access confidential data on computer Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-cyber-security-concept-with-manager-providing-authentication-credentials-161062590.htmlRFKA10YA–Cyber security concept with manager providing authentication credentials (login, password) to business person to access confidential data on computer
 Hacked. Cyber security and online fraud concept. Mobile hacker and criminal login to personal information and data with smartphone. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacked-cyber-security-and-online-fraud-concept-mobile-hacker-and-criminal-174838913.html
Hacked. Cyber security and online fraud concept. Mobile hacker and criminal login to personal information and data with smartphone. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacked-cyber-security-and-online-fraud-concept-mobile-hacker-and-criminal-174838913.htmlRFM4CGPW–Hacked. Cyber security and online fraud concept. Mobile hacker and criminal login to personal information and data with smartphone.
 Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-using-laptop-with-vr-interface-of-secure-access-to-users-personal-information-sign-in-or-register-with-username-and-password-cyber-security-image547152395.html
Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-using-laptop-with-vr-interface-of-secure-access-to-users-personal-information-sign-in-or-register-with-username-and-password-cyber-security-image547152395.htmlRF2PP4XCY–Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security.
RFM54KYP–Password isometric icon, isolated on color background
 closeup hand holding smatphone with application software security login screen. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/closeup-hand-holding-smatphone-with-application-software-security-login-screen-image385239331.html
closeup hand holding smatphone with application software security login screen. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/closeup-hand-holding-smatphone-with-application-software-security-login-screen-image385239331.htmlRF2DAN4KF–closeup hand holding smatphone with application software security login screen.
 Key with Login Key Ring Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-key-with-login-key-ring-19760707.html
Key with Login Key Ring Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-key-with-login-key-ring-19760707.htmlRFB444YF–Key with Login Key Ring
 hack concepts of computer security, with a message on keyboard enter key. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hack-concepts-of-computer-security-with-a-message-on-keyboard-enter-48948971.html
hack concepts of computer security, with a message on keyboard enter key. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hack-concepts-of-computer-security-with-a-message-on-keyboard-enter-48948971.htmlRFCRHPWF–hack concepts of computer security, with a message on keyboard enter key.
 Hand holding smartphone with password on display. Security login concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hand-holding-smartphone-with-password-on-display-security-login-concept-57036219.html
Hand holding smartphone with password on display. Security login concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hand-holding-smartphone-with-password-on-display-security-login-concept-57036219.htmlRFD8P67R–Hand holding smartphone with password on display. Security login concept
 Laptop displaying a security login form, with username and password close-up. Cyber security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/laptop-displaying-a-security-login-form-with-username-and-password-close-up-cyber-security-concept-image573102082.html
Laptop displaying a security login form, with username and password close-up. Cyber security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/laptop-displaying-a-security-login-form-with-username-and-password-close-up-cyber-security-concept-image573102082.htmlRF2T8B1FE–Laptop displaying a security login form, with username and password close-up. Cyber security concept
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126088666.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126088666.htmlRFH93RAJ–Password Security Login Technology Business Concept
RFJ4YHPE–Login icon and sign on a computer keyboard button Internet security concept 3d illustration.
 Login register password internet security computer business concept register online Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-login-register-password-internet-security-computer-business-concept-100365581.html
Login register password internet security computer business concept register online Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-login-register-password-internet-security-computer-business-concept-100365581.htmlRFFR8191–Login register password internet security computer business concept register online
 Computer Security Login Failed Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-computer-security-login-failed-88549716.html
Computer Security Login Failed Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-computer-security-login-failed-88549716.htmlRFF41P1T–Computer Security Login Failed
RF2WDMDFW–Online banking website login with lock, isolated icon
 fingerprint scan on smartphone digital device, secured access to private data, concept of biometrics Identity authorization Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/fingerprint-scan-on-smartphone-digital-device-secured-access-to-private-data-concept-of-biometrics-identity-authorization-image215192654.html
fingerprint scan on smartphone digital device, secured access to private data, concept of biometrics Identity authorization Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/fingerprint-scan-on-smartphone-digital-device-secured-access-to-private-data-concept-of-biometrics-identity-authorization-image215192654.htmlRFPE2TBX–fingerprint scan on smartphone digital device, secured access to private data, concept of biometrics Identity authorization
 Typing online account password on laptop computer keyboard, internet security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-typing-online-account-password-on-laptop-computer-keyboard-internet-131067762.html
Typing online account password on laptop computer keyboard, internet security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-typing-online-account-password-on-laptop-computer-keyboard-internet-131067762.htmlRFHH6J7E–Typing online account password on laptop computer keyboard, internet security concept
 Security internet login concept, red lock button or key on white keyboard Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-internet-login-concept-red-lock-button-or-key-on-white-keyboard-118062696.html
Security internet login concept, red lock button or key on white keyboard Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-internet-login-concept-red-lock-button-or-key-on-white-keyboard-118062696.htmlRFGT264T–Security internet login concept, red lock button or key on white keyboard
 Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258849561.html
Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258849561.htmlRFW13H75–Steel safe with login and password screen. 3D illustration.
 Personal data and password login information protection technology concept as a three dimensional connected network over a pixelated digital human eye as a symbol for privacy security on the internet. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-personal-data-and-password-login-information-protection-technology-82301321.html
Personal data and password login information protection technology concept as a three dimensional connected network over a pixelated digital human eye as a symbol for privacy security on the internet. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-personal-data-and-password-login-information-protection-technology-82301321.htmlRFENW44W–Personal data and password login information protection technology concept as a three dimensional connected network over a pixelated digital human eye as a symbol for privacy security on the internet.
 Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/secure-online-access-with-password-and-login-page-to-manage-personal-profile-account-secured-connection-and-data-security-on-internet-cybersecurity-image466246816.html
Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/secure-online-access-with-password-and-login-page-to-manage-personal-profile-account-secured-connection-and-data-security-on-internet-cybersecurity-image466246816.htmlRF2J2FAG0–Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity
 Hacked account on tablet. Cyber security and internet fraud concept. Mobile application login and personal information and data problem. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacked-account-on-tablet-cyber-security-and-internet-fraud-concept-174795364.html
Hacked account on tablet. Cyber security and internet fraud concept. Mobile application login and personal information and data problem. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacked-account-on-tablet-cyber-security-and-internet-fraud-concept-174795364.htmlRFM4AH7G–Hacked account on tablet. Cyber security and internet fraud concept. Mobile application login and personal information and data problem.
 Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-using-laptop-with-vr-interface-of-secure-access-to-users-personal-information-sign-in-or-register-with-username-and-password-cyber-security-image547152479.html
Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-using-laptop-with-vr-interface-of-secure-access-to-users-personal-information-sign-in-or-register-with-username-and-password-cyber-security-image547152479.htmlRF2PP4XFY–Woman using laptop with VR interface of secure access to user's personal information. Sign in or register with username and password. Cyber security.
 Security Button Shows Privacy Encryption And Safety Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-button-shows-privacy-encryption-and-safety-58495773.html
Security Button Shows Privacy Encryption And Safety Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-button-shows-privacy-encryption-and-safety-58495773.htmlRFDB4KXN–Security Button Shows Privacy Encryption And Safety
 barbed and razor wire for high security doors Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/barbed-and-razor-wire-for-high-security-doors-image64266119.html
barbed and razor wire for high security doors Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/barbed-and-razor-wire-for-high-security-doors-image64266119.htmlRFDMFG2F–barbed and razor wire for high security doors
 A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484851.html
A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484851.htmlRFHN4N83–A set of the password for the browser Internet
 fingerprint Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-fingerprint-166071722.html
fingerprint Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-fingerprint-166071722.htmlRFKJ564X–fingerprint
 to enter password, with message on enter key of computer keyboard. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-to-enter-password-with-message-on-enter-key-of-computer-keyboard-49061502.html
to enter password, with message on enter key of computer keyboard. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-to-enter-password-with-message-on-enter-key-of-computer-keyboard-49061502.htmlRFCRPXCE–to enter password, with message on enter key of computer keyboard.
 Woman working on a laptop, featuring a security login form hovering above. Merge productivity with the assurance of digital security Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-working-on-a-laptop-featuring-a-security-login-form-hovering-above-merge-productivity-with-the-assurance-of-digital-security-image573102028.html
Woman working on a laptop, featuring a security login form hovering above. Merge productivity with the assurance of digital security Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-working-on-a-laptop-featuring-a-security-login-form-hovering-above-merge-productivity-with-the-assurance-of-digital-security-image573102028.htmlRF2T8B1DG–Woman working on a laptop, featuring a security login form hovering above. Merge productivity with the assurance of digital security
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126036033.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126036033.htmlRFH91C6W–Password Security Login Technology Business Concept
 Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image229749442.html
Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image229749442.htmlRFR9NYN6–Server room, login and password request, data access and security.
RF2PRF636–Password login on computer laptop cyber security website with lock icon
 Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-touch-fingerprint-with-virtual-global-with-cyber-security-login-user-identification-information-cyber-security-and-encryption-secure-access-to-image612486747.html
Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-touch-fingerprint-with-virtual-global-with-cyber-security-login-user-identification-information-cyber-security-and-encryption-secure-access-to-image612486747.htmlRF2XGD52K–Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to
 Business touch scan fingerprint with virtual global and cyber security, Login, User, identification information security and encryption,secure access Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/business-touch-scan-fingerprint-with-virtual-global-and-cyber-security-login-user-identification-information-security-and-encryptionsecure-access-image576076405.html
Business touch scan fingerprint with virtual global and cyber security, Login, User, identification information security and encryption,secure access Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/business-touch-scan-fingerprint-with-virtual-global-and-cyber-security-login-user-identification-information-security-and-encryptionsecure-access-image576076405.htmlRF2TD6F99–Business touch scan fingerprint with virtual global and cyber security, Login, User, identification information security and encryption,secure access
 login and password, data protection and cyber security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-login-and-password-data-protection-and-cyber-security-concept-165641233.html
login and password, data protection and cyber security concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-login-and-password-data-protection-and-cyber-security-concept-165641233.htmlRFKHDH29–login and password, data protection and cyber security concept
 cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608671426.html
cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608671426.htmlRF2XA7AH6–cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec
 Security web login concept, red enter button or key on white keyboard Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-web-login-concept-red-enter-button-or-key-on-white-keyboard-97454388.html
Security web login concept, red enter button or key on white keyboard Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-web-login-concept-red-enter-button-or-key-on-white-keyboard-97454388.htmlRFFJFC1T–Security web login concept, red enter button or key on white keyboard
 Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258849444.html
Steel safe with login and password screen. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/steel-safe-with-login-and-password-screen-3d-illustration-image258849444.htmlRFW13H30–Steel safe with login and password screen. 3D illustration.
 man using login interface on touch screen. user name and password inputs on virtual digital tablet account online. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-using-login-interface-on-touch-screen-user-name-and-password-inputs-on-virtual-digital-tablet-account-online-image475718881.html
man using login interface on touch screen. user name and password inputs on virtual digital tablet account online. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-using-login-interface-on-touch-screen-user-name-and-password-inputs-on-virtual-digital-tablet-account-online-image475718881.htmlRF2JHXT81–man using login interface on touch screen. user name and password inputs on virtual digital tablet account online.
 Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/secure-online-access-with-password-and-login-page-to-manage-personal-profile-account-secured-connection-and-data-security-on-internet-cybersecurity-image466708127.html
Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/secure-online-access-with-password-and-login-page-to-manage-personal-profile-account-secured-connection-and-data-security-on-internet-cybersecurity-image466708127.htmlRF2J38AYB–Secure online access with password and login page to manage personal profile account. Secured connection and data security on internet. Cybersecurity
 Mobile banking hack and cyber security concept. Hacker and criminal login to persons online bank application and steal money from account. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-mobile-banking-hack-and-cyber-security-concept-hacker-and-criminal-174798850.html
Mobile banking hack and cyber security concept. Hacker and criminal login to persons online bank application and steal money from account. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-mobile-banking-hack-and-cyber-security-concept-hacker-and-criminal-174798850.htmlRFM4ANM2–Mobile banking hack and cyber security concept. Hacker and criminal login to persons online bank application and steal money from account.
 Laptop login and password Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/laptop-login-and-password-image150645557.html
Laptop login and password Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/laptop-login-and-password-image150645557.htmlRFJN2DXD–Laptop login and password
 vector - mobile security Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-vector-mobile-security-115476224.html
vector - mobile security Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-vector-mobile-security-115476224.htmlRFGKTB2T–vector - mobile security
 hand of hacker on keboard and login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hand-of-hacker-on-keboard-and-login-76941439.html
hand of hacker on keboard and login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hand-of-hacker-on-keboard-and-login-76941439.htmlRFED4YGF–hand of hacker on keboard and login
 A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484848.html
A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484848.htmlRFHN4N80–A set of the password for the browser Internet
 Businessman pushing virtual security button on digital background Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-businessman-pushing-virtual-security-button-on-digital-background-74544270.html
Businessman pushing virtual security button on digital background Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-businessman-pushing-virtual-security-button-on-digital-background-74544270.htmlRFE97NYA–Businessman pushing virtual security button on digital background
 Cybersecurity. The hand enters the login and password on the screen. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cybersecurity-the-hand-enters-the-login-and-password-on-the-screen-image472429001.html
Cybersecurity. The hand enters the login and password on the screen. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cybersecurity-the-hand-enters-the-login-and-password-on-the-screen-image472429001.htmlRF2JCH009–Cybersecurity. The hand enters the login and password on the screen.
 Autentication login form concept with hands on a laptop. Seamless security integration for a clean and functional tech visual Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/autentication-login-form-concept-with-hands-on-a-laptop-seamless-security-integration-for-a-clean-and-functional-tech-visual-image573102101.html
Autentication login form concept with hands on a laptop. Seamless security integration for a clean and functional tech visual Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/autentication-login-form-concept-with-hands-on-a-laptop-seamless-security-integration-for-a-clean-and-functional-tech-visual-image573102101.htmlRF2T8B1G5–Autentication login form concept with hands on a laptop. Seamless security integration for a clean and functional tech visual
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126060055.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126060055.htmlRFH92ETR–Password Security Login Technology Business Concept
 Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image229749438.html
Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image229749438.htmlRFR9NYN2–Server room, login and password request, data access and security.
RF2PRFW42–Cyber digital technology internet network online information security.Safety web hacker login and password icon business concept.
 Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-touch-fingerprint-with-virtual-global-with-cyber-security-login-user-identification-information-cyber-security-and-encryption-secure-access-to-image616736591.html
Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-touch-fingerprint-with-virtual-global-with-cyber-security-login-user-identification-information-cyber-security-and-encryption-secure-access-to-image616736591.htmlRF2XRANPR–Man touch fingerprint with virtual global with cyber security, login, User, identification information cyber security and encryption, secure access to
 Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-hold-smartphone-with-virtual-global-with-cyber-security-login-user-identification-information-security-and-encryption-secure-access-to-users-image552097062.html
Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-hold-smartphone-with-virtual-global-with-cyber-security-login-user-identification-information-security-and-encryption-secure-access-to-users-image552097062.htmlRF2R265C6–Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users
 data security concept, mobile application access, login and password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-data-security-concept-mobile-application-access-login-and-password-165639844.html
data security concept, mobile application access, login and password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-data-security-concept-mobile-application-access-login-and-password-165639844.htmlRFKHDF8M–data security concept, mobile application access, login and password
 cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608668314.html
cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608668314.htmlRF2XA76J2–cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec
 Laptop with authorization on the screen. Login and password of the user. Login to the system or account. Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-laptop-with-authorization-on-the-screen-login-and-password-of-the-172885132.html
Laptop with authorization on the screen. Login and password of the user. Login to the system or account. Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-laptop-with-authorization-on-the-screen-login-and-password-of-the-172885132.htmlRFM17GN0–Laptop with authorization on the screen. Login and password of the user. Login to the system or account. Vector illustration
 Half open empty steel safe. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/half-open-empty-steel-safe-3d-illustration-image258849201.html
Half open empty steel safe. 3D illustration. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/half-open-empty-steel-safe-3d-illustration-image258849201.htmlRFW13GP9–Half open empty steel safe. 3D illustration.
 Woman showing interface login and password on tablet. Data protection and secured internet access. Concept of security network. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-showing-interface-login-and-password-on-tablet-data-protection-and-secured-internet-access-concept-of-security-network-image490841471.html
Woman showing interface login and password on tablet. Data protection and secured internet access. Concept of security network. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-showing-interface-login-and-password-on-tablet-data-protection-and-secured-internet-access-concept-of-security-network-image490841471.htmlRF2KEFN8F–Woman showing interface login and password on tablet. Data protection and secured internet access. Concept of security network.
 Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-page-with-password-to-access-online-profile-account-secured-connection-and-personal-data-security-on-internet-cybersecurity-and-sign-in-form-image466246820.html
Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-page-with-password-to-access-online-profile-account-secured-connection-and-personal-data-security-on-internet-cybersecurity-and-sign-in-form-image466246820.htmlRF2J2FAG4–Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form.
 Identity theft and cyber security concept. Mobile hacker and criminal login to persons online social media account or personal information and data. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-identity-theft-and-cyber-security-concept-mobile-hacker-and-criminal-174798858.html
Identity theft and cyber security concept. Mobile hacker and criminal login to persons online social media account or personal information and data. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-identity-theft-and-cyber-security-concept-mobile-hacker-and-criminal-174798858.htmlRFM4ANMA–Identity theft and cyber security concept. Mobile hacker and criminal login to persons online social media account or personal information and data.
 A close-up image of a person's hands typing on a laptop computer with a login screen visible on the monitor. Cyber security and digital security conce Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-close-up-image-of-a-persons-hands-typing-on-a-laptop-computer-with-a-login-screen-visible-on-the-monitor-cyber-security-and-digital-security-conce-image612110027.html
A close-up image of a person's hands typing on a laptop computer with a login screen visible on the monitor. Cyber security and digital security conce Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-close-up-image-of-a-persons-hands-typing-on-a-laptop-computer-with-a-login-screen-visible-on-the-monitor-cyber-security-and-digital-security-conce-image612110027.htmlRF2XFT0GB–A close-up image of a person's hands typing on a laptop computer with a login screen visible on the monitor. Cyber security and digital security conce
 Security On Smartphone Shows Secure Password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-on-smartphone-shows-secure-password-59116856.html
Security On Smartphone Shows Secure Password Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-security-on-smartphone-shows-secure-password-59116856.htmlRFDC5048–Security On Smartphone Shows Secure Password
 Man inserts a Smartcard security card into a laptop to provide extra security Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-man-inserts-a-smartcard-security-card-into-a-laptop-to-provide-extra-41764618.html
Man inserts a Smartcard security card into a laptop to provide extra security Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-man-inserts-a-smartcard-security-card-into-a-laptop-to-provide-extra-41764618.htmlRFCBXF5E–Man inserts a Smartcard security card into a laptop to provide extra security
 A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484854.html
A set of the password for the browser Internet Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-a-set-of-the-password-for-the-browser-internet-133484854.htmlRFHN4N86–A set of the password for the browser Internet
 businessman show Facebook login page on his smartphone for using phone social app for business. 3 August 2018,Bangkok, Thailand. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-show-facebook-login-page-on-his-smartphone-for-using-phone-social-app-for-business-3-august-2018bangkok-thailand-image241610093.html
businessman show Facebook login page on his smartphone for using phone social app for business. 3 August 2018,Bangkok, Thailand. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-show-facebook-login-page-on-his-smartphone-for-using-phone-social-app-for-business-3-august-2018bangkok-thailand-image241610093.htmlRFT1283W–businessman show Facebook login page on his smartphone for using phone social app for business. 3 August 2018,Bangkok, Thailand.
 Smart Phone with Security Warning Login Screen Cut Out on White. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-phone-with-security-warning-login-screen-cut-out-on-white-image397405638.html
Smart Phone with Security Warning Login Screen Cut Out on White. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-phone-with-security-warning-login-screen-cut-out-on-white-image397405638.htmlRF2E2FAXE–Smart Phone with Security Warning Login Screen Cut Out on White.
 Security and technology with this autentication login form concept. Hands on a laptop portray seamless integration for a streamlined and secure digita Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/security-and-technology-with-this-autentication-login-form-concept-hands-on-a-laptop-portray-seamless-integration-for-a-streamlined-and-secure-digita-image573102116.html
Security and technology with this autentication login form concept. Hands on a laptop portray seamless integration for a streamlined and secure digita Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/security-and-technology-with-this-autentication-login-form-concept-hands-on-a-laptop-portray-seamless-integration-for-a-streamlined-and-secure-digita-image573102116.htmlRF2T8B1GM–Security and technology with this autentication login form concept. Hands on a laptop portray seamless integration for a streamlined and secure digita
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126045668.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126045668.htmlRFH91TF0–Password Security Login Technology Business Concept
 Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image241849243.html
Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image241849243.htmlRFT1D54Y–Server room, login and password request, data access and security.
RF2PRFW3C–Cyber digital technology internet network online information security.Safety web hacker login and password icon business concept.
 Security password personal identification safety login concept as a technology safety software as a human fingerprint with data code. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-security-password-personal-identification-safety-login-concept-as-160045432.html
Security password personal identification safety login concept as a technology safety software as a human fingerprint with data code. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-image-security-password-personal-identification-safety-login-concept-as-160045432.htmlRFK8AKG8–Security password personal identification safety login concept as a technology safety software as a human fingerprint with data code.
 Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-hold-smartphone-with-virtual-global-with-cyber-security-login-user-identification-information-security-and-encryption-secure-access-to-users-image552097049.html
Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-hold-smartphone-with-virtual-global-with-cyber-security-login-user-identification-information-security-and-encryption-secure-access-to-users-image552097049.htmlRF2R265BN–Woman hold Smartphone with virtual global with cyber security, Login, User, identification information security and encryption, secure access to users
 Login Word and lockpad on blue computer Keyboard Key. Technology security or hacking concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-word-and-lockpad-on-blue-computer-keyboard-key-technology-security-or-hacking-concept-image408415168.html
Login Word and lockpad on blue computer Keyboard Key. Technology security or hacking concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-word-and-lockpad-on-blue-computer-keyboard-key-technology-security-or-hacking-concept-image408415168.htmlRF2EMCWM0–Login Word and lockpad on blue computer Keyboard Key. Technology security or hacking concept
 cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608671411.html
cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-login-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-biotic-login-tec-image608671411.htmlRF2XA7AGK–cyber security login. user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock, biotic login tec
 Password login on computer screen, Unlock laptop, cyber lock internet security concept. Man working on an office desk Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-login-on-computer-screen-unlock-laptop-cyber-lock-internet-security-concept-man-working-on-an-office-desk-image337315720.html
Password login on computer screen, Unlock laptop, cyber lock internet security concept. Man working on an office desk Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-login-on-computer-screen-unlock-laptop-cyber-lock-internet-security-concept-man-working-on-an-office-desk-image337315720.htmlRF2AGP1J0–Password login on computer screen, Unlock laptop, cyber lock internet security concept. Man working on an office desk
RFRNFTFX–Smartphone security and communication in social media. Mobile phone on login screen. Smartphone application icons connected by lines. Flat design for
 Online banking on a tablet - login, password and security code Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-online-banking-on-a-tablet-login-password-and-security-code-78128302.html
Online banking on a tablet - login, password and security code Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-online-banking-on-a-tablet-login-password-and-security-code-78128302.htmlRFEF31CE–Online banking on a tablet - login, password and security code
 Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-page-with-password-to-access-online-profile-account-secured-connection-and-personal-data-security-on-internet-cybersecurity-and-sign-in-form-image466246823.html
Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/login-page-with-password-to-access-online-profile-account-secured-connection-and-personal-data-security-on-internet-cybersecurity-and-sign-in-form-image466246823.htmlRF2J2FAG7–Login page with password to access online profile account. Secured connection and personal data security on internet. Cybersecurity and sign in form.
 Password to personal data security and cyber protection in laptop. Login lock screen in computer in dark. Confidential information encrypted. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-to-personal-data-security-and-cyber-protection-in-laptop-login-lock-screen-in-computer-in-dark-confidential-information-encrypted-image491268268.html
Password to personal data security and cyber protection in laptop. Login lock screen in computer in dark. Confidential information encrypted. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-to-personal-data-security-and-cyber-protection-in-laptop-login-lock-screen-in-computer-in-dark-confidential-information-encrypted-image491268268.htmlRF2KF75K8–Password to personal data security and cyber protection in laptop. Login lock screen in computer in dark. Confidential information encrypted.
 Digital technology, security, protection, innovation in cyberspace. Editable Stroke. EPS 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/digital-technology-security-protection-innovation-in-cyberspace-editable-stroke-eps-10-image244233187.html
Digital technology, security, protection, innovation in cyberspace. Editable Stroke. EPS 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/digital-technology-security-protection-innovation-in-cyberspace-editable-stroke-eps-10-image244233187.htmlRFT59NWR–Digital technology, security, protection, innovation in cyberspace. Editable Stroke. EPS 10
 Access Word On Computer Screen Showing Login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-access-word-on-computer-screen-showing-login-58722321.html
Access Word On Computer Screen Showing Login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-access-word-on-computer-screen-showing-login-58722321.htmlRFDBF0WN–Access Word On Computer Screen Showing Login
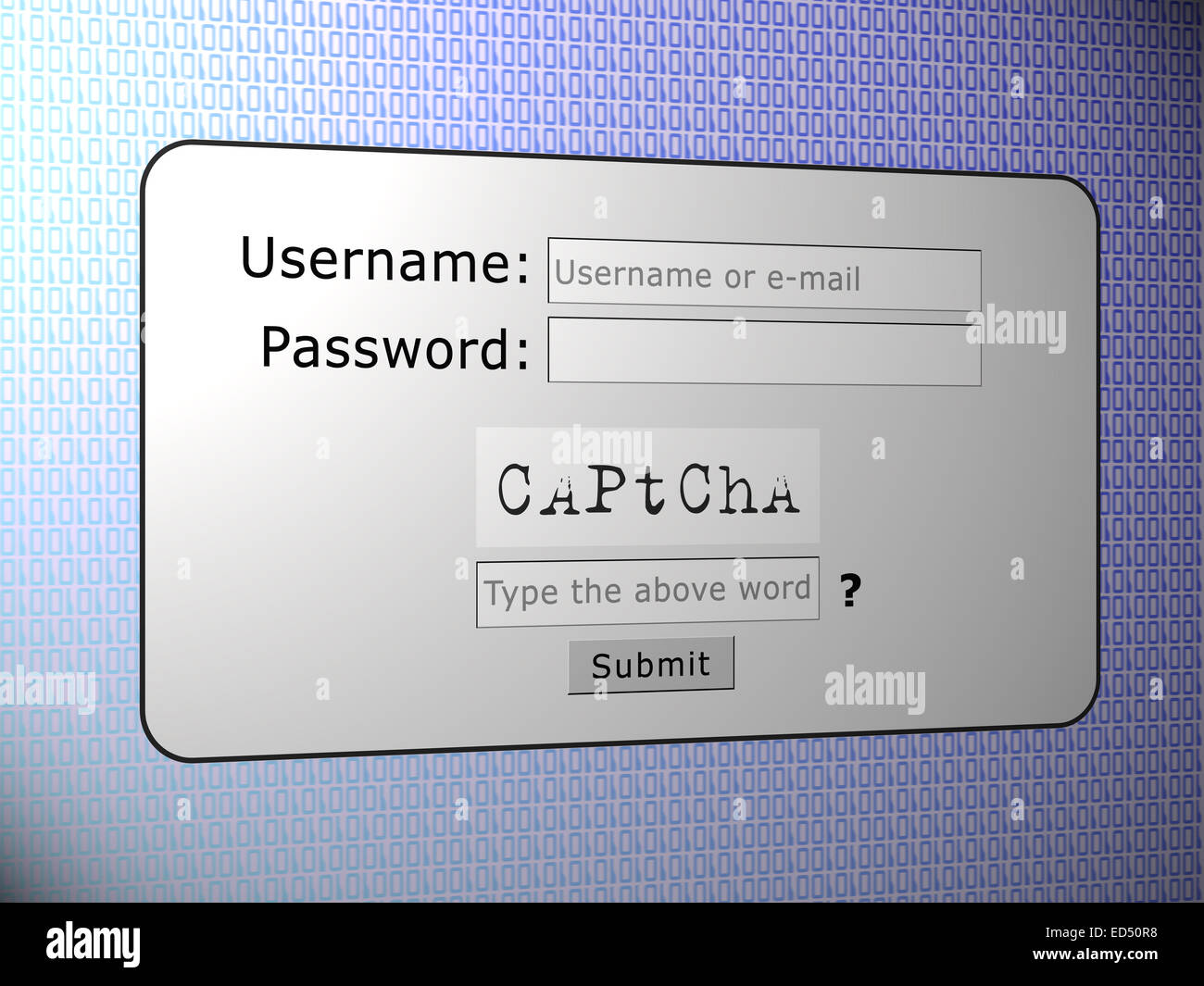 Captcha words for human security login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-captcha-words-for-human-security-login-76942412.html
Captcha words for human security login Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-captcha-words-for-human-security-login-76942412.htmlRFED50R8–Captcha words for human security login
 Businessman using computer to login represents protection concept of cyber security and data security including secure login. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-using-computer-to-login-represents-protection-concept-of-cyber-security-and-data-security-including-secure-login-image596257931.html
Businessman using computer to login represents protection concept of cyber security and data security including secure login. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/businessman-using-computer-to-login-represents-protection-concept-of-cyber-security-and-data-security-including-secure-login-image596257931.htmlRF2WJ1W23–Businessman using computer to login represents protection concept of cyber security and data security including secure login.
 People login Facebook app with smartphone, Facebook is most popular social network application by Mark Zuckerberg. 04 April 2020. Bangkok,THAILAND. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/people-login-facebook-app-with-smartphone-facebook-is-most-popular-social-network-application-by-mark-zuckerberg-04-april-2020-bangkokthailand-image360035544.html
People login Facebook app with smartphone, Facebook is most popular social network application by Mark Zuckerberg. 04 April 2020. Bangkok,THAILAND. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/people-login-facebook-app-with-smartphone-facebook-is-most-popular-social-network-application-by-mark-zuckerberg-04-april-2020-bangkokthailand-image360035544.htmlRF2BWN108–People login Facebook app with smartphone, Facebook is most popular social network application by Mark Zuckerberg. 04 April 2020. Bangkok,THAILAND.
 Woman use digital tablet to login with holographic authentication interface. Cyber security concept. Data protection and secured internet access. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-use-digital-tablet-to-login-with-holographic-authentication-interface-cyber-security-concept-data-protection-and-secured-internet-access-image574477320.html
Woman use digital tablet to login with holographic authentication interface. Cyber security concept. Data protection and secured internet access. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/woman-use-digital-tablet-to-login-with-holographic-authentication-interface-cyber-security-concept-data-protection-and-secured-internet-access-image574477320.htmlRF2TAHKK4–Woman use digital tablet to login with holographic authentication interface. Cyber security concept. Data protection and secured internet access.
 White door, symbolizing secure access with login form, username and password. Concept of online security and open internet service accounts. Unlock di Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/white-door-symbolizing-secure-access-with-login-form-username-and-password-concept-of-online-security-and-open-internet-service-accounts-unlock-di-image573101610.html
White door, symbolizing secure access with login form, username and password. Concept of online security and open internet service accounts. Unlock di Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/white-door-symbolizing-secure-access-with-login-form-username-and-password-concept-of-online-security-and-open-internet-service-accounts-unlock-di-image573101610.htmlRF2T8B0XJ–White door, symbolizing secure access with login form, username and password. Concept of online security and open internet service accounts. Unlock di
 Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126065993.html
Password Security Login Technology Business Concept Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-password-security-login-technology-business-concept-126065993.htmlRFH92PCW–Password Security Login Technology Business Concept
 Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image239213276.html
Server room, login and password request, data access and security. Stock Photohttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/server-room-login-and-password-request-data-access-and-security-image239213276.htmlRFRW52Y8–Server room, login and password request, data access and security.
RF2PRMMC7–Cyber digital technology internet network online information security.Safety web hacker login and password icon business concept.
Search Results for Security login Stock Photos and Images (46,011)
Page 1 of 461