Quick filters:
Page 1 of 500
Secure communication Stock Photos and Images
 Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-image550265608.html
Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-image550265608.htmlRF2PY6NB4–Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing
 Sign displaying Secure Communication. Business showcase preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-image550266338.html
Sign displaying Secure Communication. Business showcase preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-image550266338.htmlRF2PY6P96–Sign displaying Secure Communication. Business showcase preventing unauthorized interceptors from accessing
RF2RNR81M–Secure Communication Icon. Security, Privacy, Message. Editable Stroke. Simple Vector Icon
 Vector of business people and clients having secure communication Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vector-of-business-people-and-clients-having-secure-communication-image417093868.html
Vector of business people and clients having secure communication Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vector-of-business-people-and-clients-having-secure-communication-image417093868.htmlRF2F6G7DG–Vector of business people and clients having secure communication
RF2HFNA80–Modern flat design vector illustration, secure communication icon, for graphic and web design
 Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/macro-closeup-of-the-hypertext-transfer-protocol-secure-https-and-a-padlock-symbol-in-a-website-internet-address-bar-showing-it-is-secure-image433626186.html
Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/macro-closeup-of-the-hypertext-transfer-protocol-secure-https-and-a-padlock-symbol-in-a-website-internet-address-bar-showing-it-is-secure-image433626186.htmlRM2G5DAHE–Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure
 Damaged microwave dishes in secure area Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-damaged-microwave-dishes-in-secure-area-23836239.html
Damaged microwave dishes in secure area Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-damaged-microwave-dishes-in-secure-area-23836239.htmlRMBANRA7–Damaged microwave dishes in secure area
 Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-with-antivirus-for-protection-security-and-blocking-of-receiving-138604112.html
Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-with-antivirus-for-protection-security-and-blocking-of-receiving-138604112.htmlRFJ1DXXT–Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i
 Mobile phone sim card vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/mobile-phone-sim-card-vector-image554881454.html
Mobile phone sim card vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/mobile-phone-sim-card-vector-image554881454.htmlRF2R6N0XP–Mobile phone sim card vector
 Image of cyber security data processing and world map over server room against view of cityscape Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-cyber-security-data-processing-and-world-map-over-server-room-against-view-of-cityscape-image607599440.html
Image of cyber security data processing and world map over server room against view of cityscape Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-cyber-security-data-processing-and-world-map-over-server-room-against-view-of-cityscape-image607599440.htmlRF2X8EF80–Image of cyber security data processing and world map over server room against view of cityscape
 SOCIAL SECURITY TRACE, PRIVACY POLICY, Login, Private account, Lock, Remain anonymous, Secure Communication, Unauthorized Person, Prison, Security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-security-trace-privacy-policy-login-private-account-lock-remain-anonymous-secure-communication-unauthorized-person-prison-security-image569701582.html
SOCIAL SECURITY TRACE, PRIVACY POLICY, Login, Private account, Lock, Remain anonymous, Secure Communication, Unauthorized Person, Prison, Security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-security-trace-privacy-policy-login-private-account-lock-remain-anonymous-secure-communication-unauthorized-person-prison-security-image569701582.htmlRF2T2T452–SOCIAL SECURITY TRACE, PRIVACY POLICY, Login, Private account, Lock, Remain anonymous, Secure Communication, Unauthorized Person, Prison, Security
 Old office desk and typewriter from early 1900s. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-from-early-1900s-105111681.html
Old office desk and typewriter from early 1900s. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-from-early-1900s-105111681.htmlRMG3070H–Old office desk and typewriter from early 1900s.
 Expert Pressing SECURE COMMUNICATION Onscreen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-expert-pressing-secure-communication-onscreen-103627092.html
Expert Pressing SECURE COMMUNICATION Onscreen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-expert-pressing-secure-communication-onscreen-103627092.htmlRFG0GHBG–Expert Pressing SECURE COMMUNICATION Onscreen
 Handwriting text Secure Conversation. Business approach Secured Encrypted Communication between Web Services Typing Device Instruction Manual, Posting Product Review Online Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-secure-conversation-business-approach-secured-encrypted-communication-between-web-services-typing-device-instruction-manual-posting-product-review-online-image460889627.html
Handwriting text Secure Conversation. Business approach Secured Encrypted Communication between Web Services Typing Device Instruction Manual, Posting Product Review Online Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-secure-conversation-business-approach-secured-encrypted-communication-between-web-services-typing-device-instruction-manual-posting-product-review-online-image460889627.htmlRM2HNR9BR–Handwriting text Secure Conversation. Business approach Secured Encrypted Communication between Web Services Typing Device Instruction Manual, Posting Product Review Online
 Internet connection protect, secure communication network concept. 3D rendering isolated on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-internet-connection-protect-secure-communication-network-concept-3d-165414904.html
Internet connection protect, secure communication network concept. 3D rendering isolated on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-internet-connection-protect-secure-communication-network-concept-3d-165414904.htmlRFKH38B4–Internet connection protect, secure communication network concept. 3D rendering isolated on white background
 Scissors cutting internet modem router cable - Concept of network and data protection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scissors-cutting-internet-modem-router-cable-concept-of-network-and-data-protection-image247378505.html
Scissors cutting internet modem router cable - Concept of network and data protection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scissors-cutting-internet-modem-router-cable-concept-of-network-and-data-protection-image247378505.htmlRFTAD1PH–Scissors cutting internet modem router cable - Concept of network and data protection
 Two yellow rubber duck talking with an encrypted call. Symbolized by a maze-like string attached to two tin can telephone on a blue paper. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/two-yellow-rubber-duck-talking-with-an-encrypted-call-symbolized-by-a-maze-like-string-attached-to-two-tin-can-telephone-on-a-blue-paper-image222340926.html
Two yellow rubber duck talking with an encrypted call. Symbolized by a maze-like string attached to two tin can telephone on a blue paper. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/two-yellow-rubber-duck-talking-with-an-encrypted-call-symbolized-by-a-maze-like-string-attached-to-two-tin-can-telephone-on-a-blue-paper-image222340926.htmlRFPWME3A–Two yellow rubber duck talking with an encrypted call. Symbolized by a maze-like string attached to two tin can telephone on a blue paper.
 Concept of email security, secure communication, secret and confidential. umbrella above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-umbrella-above-white-envolope-over-a-blue-background-image559131951.html
Concept of email security, secure communication, secret and confidential. umbrella above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-umbrella-above-white-envolope-over-a-blue-background-image559131951.htmlRF2RDJJE7–Concept of email security, secure communication, secret and confidential. umbrella above white envolope over a blue background.
 Unrecognizable male doctor of medicine accessing medical records via a secure communication network. Information technology and healthcare concept for Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unrecognizable-male-doctor-of-medicine-accessing-medical-records-via-a-secure-communication-network-information-technology-and-healthcare-concept-for-image596891016.html
Unrecognizable male doctor of medicine accessing medical records via a secure communication network. Information technology and healthcare concept for Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unrecognizable-male-doctor-of-medicine-accessing-medical-records-via-a-secure-communication-network-information-technology-and-healthcare-concept-for-image596891016.htmlRF2WK2MG8–Unrecognizable male doctor of medicine accessing medical records via a secure communication network. Information technology and healthcare concept for
 Text caption presenting Secure Communication. Word for preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-secure-communication-word-for-preventing-unauthorized-interceptors-from-accessing-image550272554.html
Text caption presenting Secure Communication. Word for preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-secure-communication-word-for-preventing-unauthorized-interceptors-from-accessing-image550272554.htmlRF2PY7276–Text caption presenting Secure Communication. Word for preventing unauthorized interceptors from accessing
 Text caption presenting Secure Communication, Business showcase preventing unauthorized interceptors from accessing Creating Interesting Short Stories Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-creating-interesting-short-stories-image447086070.html
Text caption presenting Secure Communication, Business showcase preventing unauthorized interceptors from accessing Creating Interesting Short Stories Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-creating-interesting-short-stories-image447086070.htmlRF2GYAERJ–Text caption presenting Secure Communication, Business showcase preventing unauthorized interceptors from accessing Creating Interesting Short Stories
 question and answer communication via smartphone vector illustration EPS10 Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/question-and-answer-communication-via-smartphone-vector-illustration-eps10-image239137318.html
question and answer communication via smartphone vector illustration EPS10 Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/question-and-answer-communication-via-smartphone-vector-illustration-eps10-image239137318.htmlRFRW1J2E–question and answer communication via smartphone vector illustration EPS10
 Concept of marketing online business education, building a success and modern secure communication Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-marketing-online-business-education-building-a-success-and-modern-secure-communication-image570049099.html
Concept of marketing online business education, building a success and modern secure communication Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-marketing-online-business-education-building-a-success-and-modern-secure-communication-image570049099.htmlRF2T3BYCB–Concept of marketing online business education, building a success and modern secure communication
RF2HFNEN7–Modern flat design vector illustration, security icon, for graphic and web design
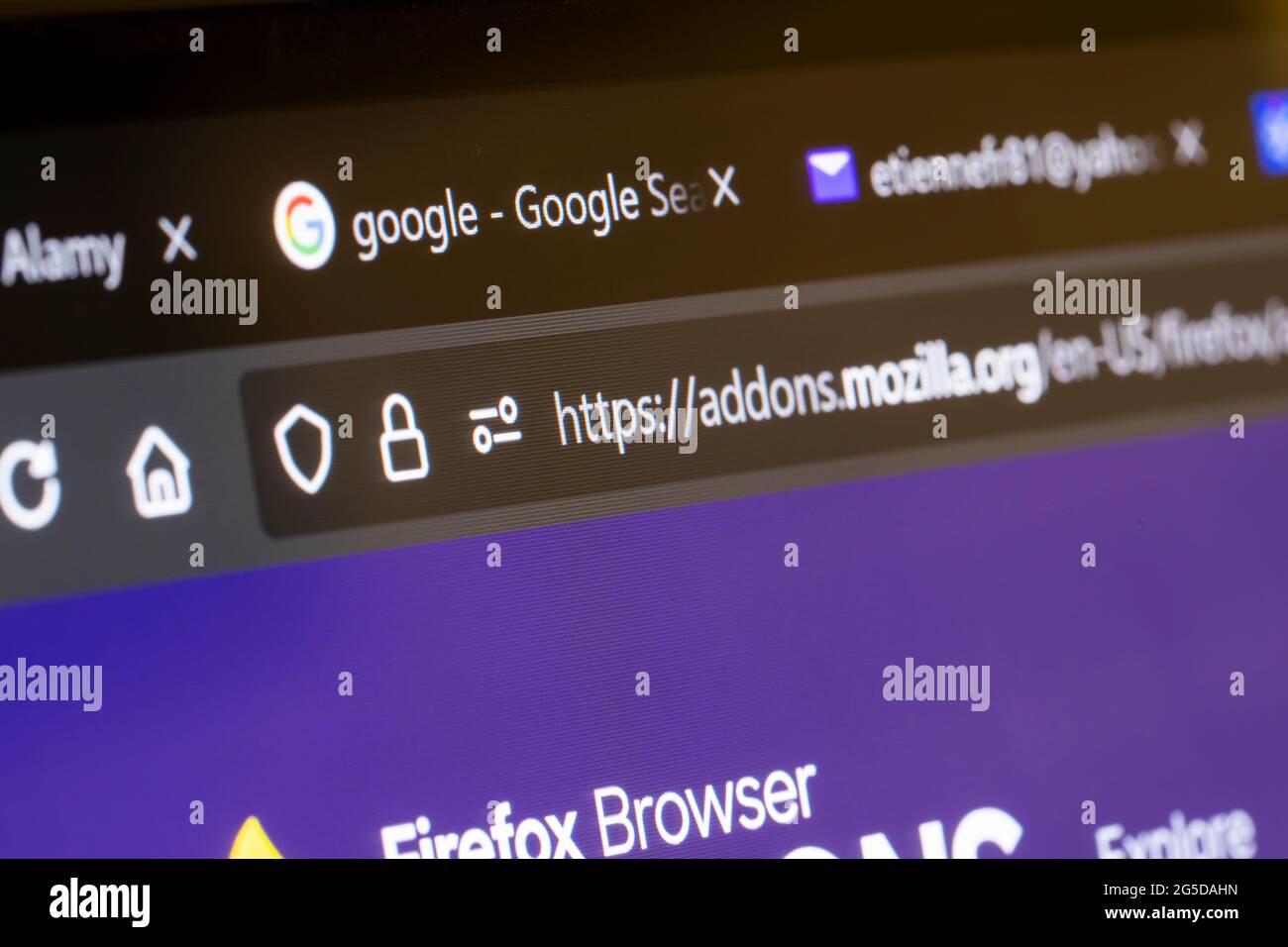 Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/macro-closeup-of-the-hypertext-transfer-protocol-secure-https-and-a-padlock-symbol-in-a-website-internet-address-bar-showing-it-is-secure-image433626193.html
Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/macro-closeup-of-the-hypertext-transfer-protocol-secure-https-and-a-padlock-symbol-in-a-website-internet-address-bar-showing-it-is-secure-image433626193.htmlRM2G5DAHN–Macro closeup of the Hypertext Transfer Protocol Secure (HTTPS) and a padlock symbol in a website internet address bar showing it is secure
RF2RP4H31–Secure Messaging Icon. Security, Communication, Privacy. Editable Stroke. Simple Vector Icon
 Email protection and secure communication on internet. Antivirus for protection, security and blocking of spam. Template in flat design for web banner Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-protection-and-secure-communication-on-internet-antivirus-for-protection-security-and-blocking-of-spam-template-in-flat-design-for-web-banner-image236991040.html
Email protection and secure communication on internet. Antivirus for protection, security and blocking of spam. Template in flat design for web banner Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-protection-and-secure-communication-on-internet-antivirus-for-protection-security-and-blocking-of-spam-template-in-flat-design-for-web-banner-image236991040.htmlRFRNFTDM–Email protection and secure communication on internet. Antivirus for protection, security and blocking of spam. Template in flat design for web banner
RF2R7FRMD–Simple Vector Object Icons - Vector Icon Set
 Digital biometric fingerprint scan for secure global communication on blue. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/digital-biometric-fingerprint-scan-for-secure-global-communication-on-blue-image599695964.html
Digital biometric fingerprint scan for secure global communication on blue. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/digital-biometric-fingerprint-scan-for-secure-global-communication-on-blue-image599695964.htmlRF2WRJE90–Digital biometric fingerprint scan for secure global communication on blue.
 Smartphone mockup with protection type protocole. Finger print secure. Vector colorful technology illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-mockup-with-protection-type-protocole-finger-print-secure-vector-colorful-technology-illustration-image336174352.html
Smartphone mockup with protection type protocole. Finger print secure. Vector colorful technology illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-mockup-with-protection-type-protocole-finger-print-secure-vector-colorful-technology-illustration-image336174352.htmlRF2AEX1PT–Smartphone mockup with protection type protocole. Finger print secure. Vector colorful technology illustration
 Old office desk and typewriter on board a ship from WW!. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-on-board-a-ship-from-ww!-105111677.html
Old office desk and typewriter on board a ship from WW!. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-on-board-a-ship-from-ww!-105111677.htmlRMG3070D–Old office desk and typewriter on board a ship from WW!.
 New York, USA - August 20, 2023: Options of Secure VPN app on smartphone screen close up with blurred logo background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/new-york-usa-august-20-2023-options-of-secure-vpn-app-on-smartphone-screen-close-up-with-blurred-logo-background-image566558259.html
New York, USA - August 20, 2023: Options of Secure VPN app on smartphone screen close up with blurred logo background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/new-york-usa-august-20-2023-options-of-secure-vpn-app-on-smartphone-screen-close-up-with-blurred-logo-background-image566558259.htmlRF2RWMXRF–New York, USA - August 20, 2023: Options of Secure VPN app on smartphone screen close up with blurred logo background
 Maximize security online. Cybersecurity expert securing data through encryption, firewall and authentication. Trust a secure network for excellent IT Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/maximize-security-online-cybersecurity-expert-securing-data-through-encryption-firewall-and-authentication-trust-a-secure-network-for-excellent-it-image599608290.html
Maximize security online. Cybersecurity expert securing data through encryption, firewall and authentication. Trust a secure network for excellent IT Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/maximize-security-online-cybersecurity-expert-securing-data-through-encryption-firewall-and-authentication-trust-a-secure-network-for-excellent-it-image599608290.htmlRF2WREEDP–Maximize security online. Cybersecurity expert securing data through encryption, firewall and authentication. Trust a secure network for excellent IT
 Inspection of secured network cables with a magnifying glass Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-inspection-of-secured-network-cables-with-a-magnifying-glass-55065937.html
Inspection of secured network cables with a magnifying glass Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-inspection-of-secured-network-cables-with-a-magnifying-glass-55065937.htmlRFD5GD4H–Inspection of secured network cables with a magnifying glass
 Childhood environment outdoors Infant blond boy 4-6 years outdoors concentrating with his smart tablet iPad computer in sunlit secure floral garden Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/childhood-environment-outdoors-infant-blond-boy-4-6-years-outdoors-concentrating-with-his-smart-tablet-ipad-computer-in-sunlit-secure-floral-garden-image418932543.html
Childhood environment outdoors Infant blond boy 4-6 years outdoors concentrating with his smart tablet iPad computer in sunlit secure floral garden Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/childhood-environment-outdoors-infant-blond-boy-4-6-years-outdoors-concentrating-with-his-smart-tablet-ipad-computer-in-sunlit-secure-floral-garden-image418932543.htmlRM2F9G0MF–Childhood environment outdoors Infant blond boy 4-6 years outdoors concentrating with his smart tablet iPad computer in sunlit secure floral garden
 Closeup of Secret Service man using headset for communication Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-closeup-of-secret-service-man-using-headset-for-communication-54338054.html
Closeup of Secret Service man using headset for communication Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-closeup-of-secret-service-man-using-headset-for-communication-54338054.htmlRFD4B8MP–Closeup of Secret Service man using headset for communication
 Concept of email security, secure communication, secret and confidential. Padlock above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-padlock-above-white-envolope-over-a-blue-background-image559130245.html
Concept of email security, secure communication, secret and confidential. Padlock above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-padlock-above-white-envolope-over-a-blue-background-image559130245.htmlRF2RDJG99–Concept of email security, secure communication, secret and confidential. Padlock above white envolope over a blue background.
 Forum communication community internet blog media discussion blue computer web keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-forum-communication-community-internet-blog-media-discussion-blue-134957563.html
Forum communication community internet blog media discussion blue computer web keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-forum-communication-community-internet-blog-media-discussion-blue-134957563.htmlRFHRFRMY–Forum communication community internet blog media discussion blue computer web keyboard
 Conceptual caption Secure Communication. Business showcase preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-image550275814.html
Conceptual caption Secure Communication. Business showcase preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-business-showcase-preventing-unauthorized-interceptors-from-accessing-image550275814.htmlRF2PY76BJ–Conceptual caption Secure Communication. Business showcase preventing unauthorized interceptors from accessing
 Sign displaying Secure Communication, Conceptual photo preventing unauthorized interceptors from accessing Social Media Influencer Creating Online Pre Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-social-media-influencer-creating-online-pre-image447090674.html
Sign displaying Secure Communication, Conceptual photo preventing unauthorized interceptors from accessing Social Media Influencer Creating Online Pre Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sign-displaying-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-social-media-influencer-creating-online-pre-image447090674.htmlRF2GYAMM2–Sign displaying Secure Communication, Conceptual photo preventing unauthorized interceptors from accessing Social Media Influencer Creating Online Pre
 Reliable and secure communication between people. Avoid problems, dangers and conflicts. Eliminate surveillance, maintain confidentiality. Data protec Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reliable-and-secure-communication-between-people-avoid-problems-dangers-and-conflicts-eliminate-surveillance-maintain-confidentiality-data-protec-image565474658.html
Reliable and secure communication between people. Avoid problems, dangers and conflicts. Eliminate surveillance, maintain confidentiality. Data protec Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reliable-and-secure-communication-between-people-avoid-problems-dangers-and-conflicts-eliminate-surveillance-maintain-confidentiality-data-protec-image565474658.htmlRF2RRYGKE–Reliable and secure communication between people. Avoid problems, dangers and conflicts. Eliminate surveillance, maintain confidentiality. Data protec
 Secure cloud document with computer and mobile flat design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-cloud-document-with-computer-and-mobile-flat-design-image464716313.html
Secure cloud document with computer and mobile flat design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-cloud-document-with-computer-and-mobile-flat-design-image464716313.htmlRF2J01JB5–Secure cloud document with computer and mobile flat design
 Secure digital space. Virtual confidential, programming protection. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-image568920197.html
Secure digital space. Virtual confidential, programming protection. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-image568920197.htmlRF2T1GFED–Secure digital space. Virtual confidential, programming protection.
RF2J99BET–Cloud and shield vector icon. Secure storage filled symbol.
 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo--38077386.html
Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo--38077386.htmlRFC5XG2J–
 Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-computer-with-antivirus-for-protection-security-and-blocking-of-receiving-168315588.html
Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-computer-with-antivirus-for-protection-security-and-blocking-of-receiving-168315588.htmlRFKNRC70–Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i
 A Colourful Sim Card Illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-colourful-sim-card-illustration-image554531604.html
A Colourful Sim Card Illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-colourful-sim-card-illustration-image554531604.htmlRF2R652M4–A Colourful Sim Card Illustration
 Internet Security - Message on the White Keyboard Key. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-security-message-on-the-white-keyboard-key-3d-133921797.html
Internet Security - Message on the White Keyboard Key. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-security-message-on-the-white-keyboard-key-3d-133921797.htmlRFHNTJH9–Internet Security - Message on the White Keyboard Key. 3D.
 Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516053.html
Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516053.htmlRF2RHF7CN–Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock.
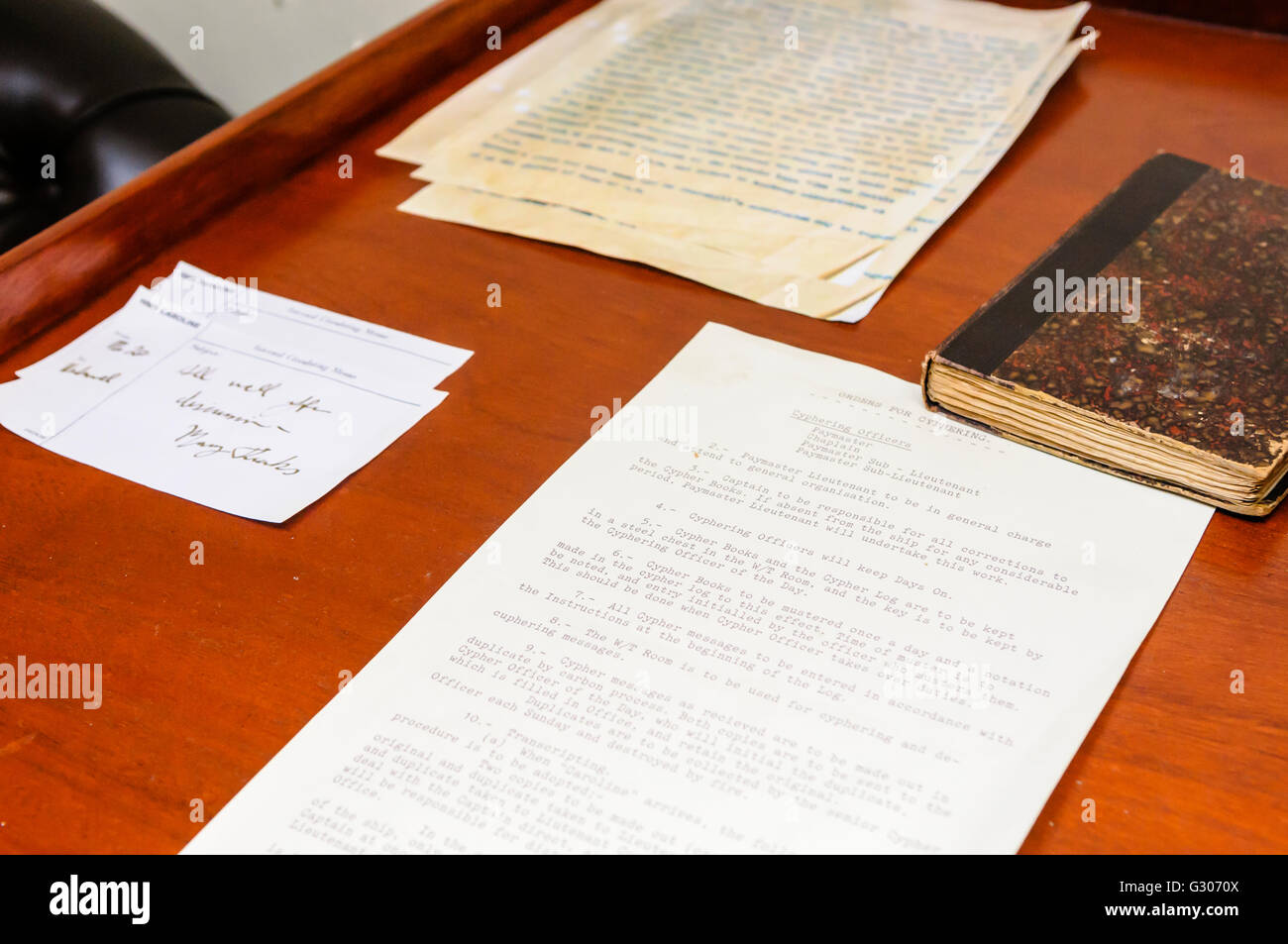 Typed instructions for the use and deployment of cyphers and coded messages. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-typed-instructions-for-the-use-and-deployment-of-cyphers-and-coded-105111690.html
Typed instructions for the use and deployment of cyphers and coded messages. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-typed-instructions-for-the-use-and-deployment-of-cyphers-and-coded-105111690.htmlRMG3070X–Typed instructions for the use and deployment of cyphers and coded messages.
 cloud space 3d illustration, modern database platform, secure storage space with password protection, 3d cloud space storage illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-space-3d-illustration-modern-database-platform-secure-storage-space-with-password-protection-3d-cloud-space-storage-illustration-image512286242.html
cloud space 3d illustration, modern database platform, secure storage space with password protection, 3d cloud space storage illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-space-3d-illustration-modern-database-platform-secure-storage-space-with-password-protection-3d-cloud-space-storage-illustration-image512286242.htmlRF2MNCJ96–cloud space 3d illustration, modern database platform, secure storage space with password protection, 3d cloud space storage illustration
 Security and cybersecurity concept lock symbol. Protection against thieves, cyber attacks, fraud, data breach. Secure access to network, internet and Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-and-cybersecurity-concept-lock-symbol-protection-against-thieves-cyber-attacks-fraud-data-breach-secure-access-to-network-internet-and-image491441372.html
Security and cybersecurity concept lock symbol. Protection against thieves, cyber attacks, fraud, data breach. Secure access to network, internet and Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-and-cybersecurity-concept-lock-symbol-protection-against-thieves-cyber-attacks-fraud-data-breach-secure-access-to-network-internet-and-image491441372.htmlRF2KFF2DG–Security and cybersecurity concept lock symbol. Protection against thieves, cyber attacks, fraud, data breach. Secure access to network, internet and
 Clicking a secure button Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-clicking-a-secure-button-78328377.html
Clicking a secure button Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-clicking-a-secure-button-78328377.htmlRFEFC4J1–Clicking a secure button
 Communication Room Overhead power supply system Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-communication-room-overhead-power-supply-system-47575692.html
Communication Room Overhead power supply system Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-communication-room-overhead-power-supply-system-47575692.htmlRMCNB77T–Communication Room Overhead power supply system
 cyber security and privacy concept. people using personal computer with text GDPR or General Data Protection Regulation text secure with a padlock log Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-and-privacy-concept-people-using-personal-computer-with-text-gdpr-or-general-data-protection-regulation-text-secure-with-a-padlock-log-image329469949.html
cyber security and privacy concept. people using personal computer with text GDPR or General Data Protection Regulation text secure with a padlock log Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-and-privacy-concept-people-using-personal-computer-with-text-gdpr-or-general-data-protection-regulation-text-secure-with-a-padlock-log-image329469949.htmlRF2A40J7W–cyber security and privacy concept. people using personal computer with text GDPR or General Data Protection Regulation text secure with a padlock log
 Concept of email security, secure communication, secret and confidential. Key above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-key-above-white-envolope-over-a-blue-background-image559131955.html
Concept of email security, secure communication, secret and confidential. Key above white envolope over a blue background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-email-security-secure-communication-secret-and-confidential-key-above-white-envolope-over-a-blue-background-image559131955.htmlRF2RDJJEB–Concept of email security, secure communication, secret and confidential. Key above white envolope over a blue background.
RF2G0584K–Business people click on the icon best protection for internet business and business security ideas.
 Conceptual caption Secure Communication. Business concept preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-business-concept-preventing-unauthorized-interceptors-from-accessing-image550263079.html
Conceptual caption Secure Communication. Business concept preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-business-concept-preventing-unauthorized-interceptors-from-accessing-image550263079.htmlRF2PY6J4R–Conceptual caption Secure Communication. Business concept preventing unauthorized interceptors from accessing
 Text sign showing Secure Communication, Internet Concept preventing unauthorized interceptors from accessing Creating New Programming Guidebook, Typin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-secure-communication-internet-concept-preventing-unauthorized-interceptors-from-accessing-creating-new-programming-guidebook-typin-image447092248.html
Text sign showing Secure Communication, Internet Concept preventing unauthorized interceptors from accessing Creating New Programming Guidebook, Typin Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-secure-communication-internet-concept-preventing-unauthorized-interceptors-from-accessing-creating-new-programming-guidebook-typin-image447092248.htmlRF2GYAPM8–Text sign showing Secure Communication, Internet Concept preventing unauthorized interceptors from accessing Creating New Programming Guidebook, Typin
 Smartphone mockup with different protection type protocoles. Fingerprint, password and key protect. Vector colorful technology illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-mockup-with-different-protection-type-protocoles-fingerprint-password-and-key-protect-vector-colorful-technology-illustration-image336172546.html
Smartphone mockup with different protection type protocoles. Fingerprint, password and key protect. Vector colorful technology illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-mockup-with-different-protection-type-protocoles-fingerprint-password-and-key-protect-vector-colorful-technology-illustration-image336172546.htmlRF2AEWYEA–Smartphone mockup with different protection type protocoles. Fingerprint, password and key protect. Vector colorful technology illustration
 New York, USA - August 21, 2023: Using Wikipedia app on smartphone screen close up with blurred logo background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/new-york-usa-august-21-2023-using-wikipedia-app-on-smartphone-screen-close-up-with-blurred-logo-background-image566558240.html
New York, USA - August 21, 2023: Using Wikipedia app on smartphone screen close up with blurred logo background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/new-york-usa-august-21-2023-using-wikipedia-app-on-smartphone-screen-close-up-with-blurred-logo-background-image566558240.htmlRF2RWMXPT–New York, USA - August 21, 2023: Using Wikipedia app on smartphone screen close up with blurred logo background
 Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294876.html
Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294876.htmlRF2T25HBT–Secure digital space. Virtual confidential, programming protection. Vector
 At Sign Padlock Shows Secure Internet Mail Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-at-sign-padlock-shows-secure-internet-mail-58495309.html
At Sign Padlock Shows Secure Internet Mail Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-at-sign-padlock-shows-secure-internet-mail-58495309.htmlRFDB4KA5–At Sign Padlock Shows Secure Internet Mail
RM2BE7WBE–Signal App, Secure encrypted messenger service, app icon, detail, full format
 Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-with-antivirus-for-protection-security-and-blocking-of-receiving-spam-by-email-spam-blocker-email-protection-and-secure-communication-on-i-image221830143.html
Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-with-antivirus-for-protection-security-and-blocking-of-receiving-spam-by-email-spam-blocker-email-protection-and-secure-communication-on-i-image221830143.htmlRFPTW6H3–Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i
RF2R76BDW–Mail Vector and Letter -Vector Icon Set 2
 Network Security Concept on Book Title. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-network-security-concept-on-book-title-3d-172088249.html
Network Security Concept on Book Title. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-network-security-concept-on-book-title-3d-172088249.htmlRFKYY88W–Network Security Concept on Book Title. 3D.
 Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516038.html
Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516038.htmlRF2RHF7C6–Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock.
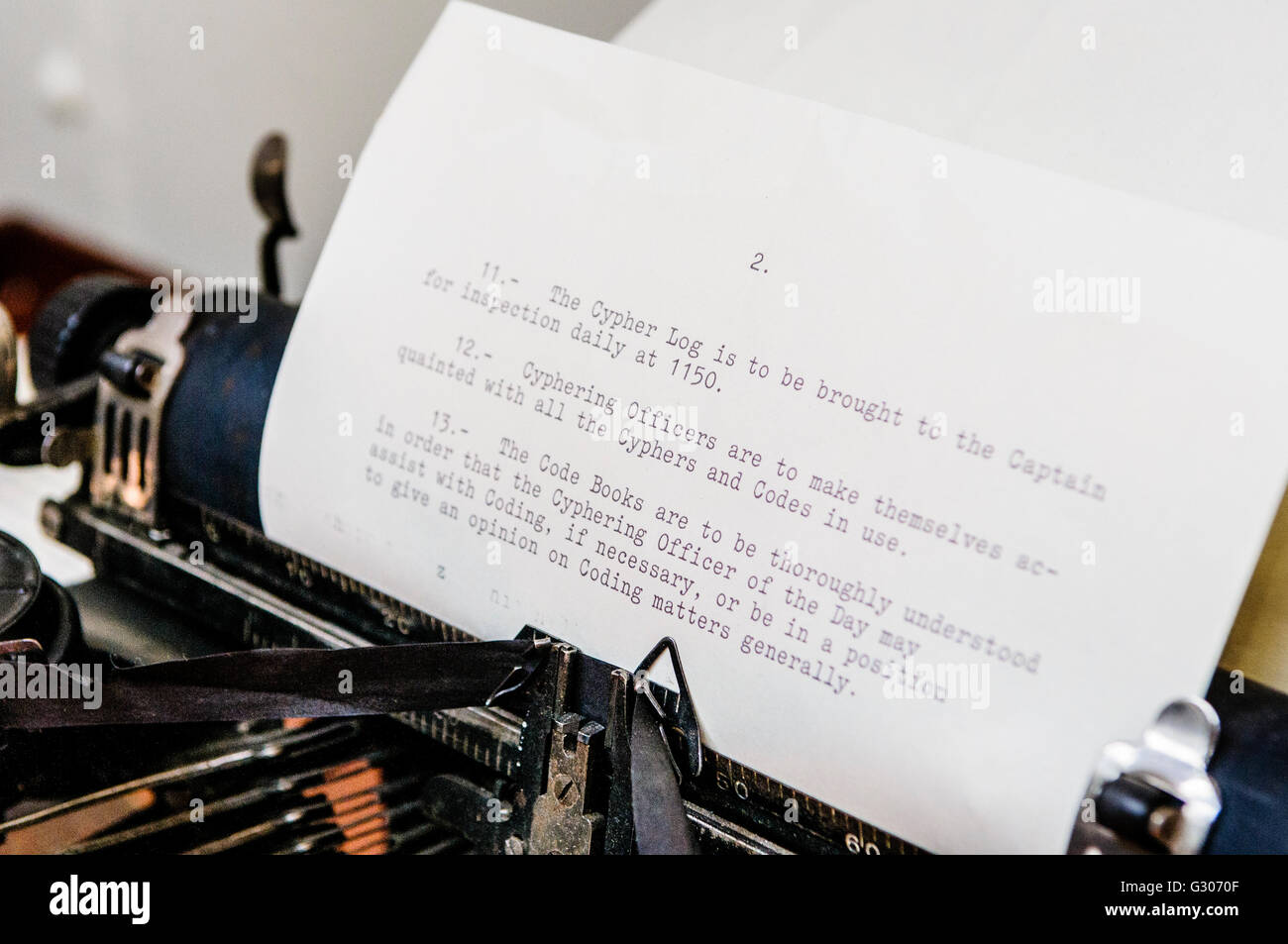 Old-fashioned typewriter with instructions for Cypher messages on board a WW1 warship. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-fashioned-typewriter-with-instructions-for-cypher-messages-on-105111679.html
Old-fashioned typewriter with instructions for Cypher messages on board a WW1 warship. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-fashioned-typewriter-with-instructions-for-cypher-messages-on-105111679.htmlRMG3070F–Old-fashioned typewriter with instructions for Cypher messages on board a WW1 warship.
 Computer keyboard with padlock for secure transactions against white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-keyboard-with-padlock-for-secure-transactions-against-white-55794595.html
Computer keyboard with padlock for secure transactions against white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-keyboard-with-padlock-for-secure-transactions-against-white-55794595.htmlRFD6NJG3–Computer keyboard with padlock for secure transactions against white background
 Secure login on mobile phone with username and password for securely accessing online bank and payment Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-secure-login-on-mobile-phone-with-username-and-password-for-securely-123374409.html
Secure login on mobile phone with username and password for securely accessing online bank and payment Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-secure-login-on-mobile-phone-with-username-and-password-for-securely-123374409.htmlRFH4M58W–Secure login on mobile phone with username and password for securely accessing online bank and payment
RFR9CC97–Secure privacy data in internet. Symbol of shield protections of icon man, which consists digit code. The protection of personal data in cloud storage. Cyber security tech concept.
 Communication Room Overhead power supply system Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-communication-room-overhead-power-supply-system-47575744.html
Communication Room Overhead power supply system Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-communication-room-overhead-power-supply-system-47575744.htmlRMCNB79M–Communication Room Overhead power supply system
RF2X8EF2Y–Image of multiple security padlock icons floating against aerial view of cityscape
 GDPR - People with hidden faces with an inscription General Data Protection Regulation. Blured Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/gdpr-people-with-hidden-faces-with-an-inscription-general-data-protection-regulation-blured-image218500562.html
GDPR - People with hidden faces with an inscription General Data Protection Regulation. Blured Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/gdpr-people-with-hidden-faces-with-an-inscription-general-data-protection-regulation-blured-image218500562.htmlRFPKDFKE–GDPR - People with hidden faces with an inscription General Data Protection Regulation. Blured
 data protection button on the keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-protection-button-on-the-keyboard-96160667.html
data protection button on the keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-protection-button-on-the-keyboard-96160667.htmlRFFGCDWF–data protection button on the keyboard
 Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-image550264256.html
Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-conceptual-photo-preventing-unauthorized-interceptors-from-accessing-image550264256.htmlRF2PY6KJT–Conceptual caption Secure Communication. Conceptual photo preventing unauthorized interceptors from accessing
 Conceptual caption Secure Communication, Word Written on preventing unauthorized interceptors from accessing Two Men Illustration Trying To Lift Extra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-word-written-on-preventing-unauthorized-interceptors-from-accessing-two-men-illustration-trying-to-lift-extra-image447092107.html
Conceptual caption Secure Communication, Word Written on preventing unauthorized interceptors from accessing Two Men Illustration Trying To Lift Extra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-secure-communication-word-written-on-preventing-unauthorized-interceptors-from-accessing-two-men-illustration-trying-to-lift-extra-image447092107.htmlRF2GYAPF7–Conceptual caption Secure Communication, Word Written on preventing unauthorized interceptors from accessing Two Men Illustration Trying To Lift Extra
 Secure Wifi communication logo. Editable Vector. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-wifi-communication-logo-editable-vector-image463713510.html
Secure Wifi communication logo. Editable Vector. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-wifi-communication-logo-editable-vector-image463713510.htmlRF2HXBY8P–Secure Wifi communication logo. Editable Vector.
 General Data Protection Regulation - GDPR. padlock symbol, data secure. Stars on blue matrix background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/general-data-protection-regulation-gdpr-padlock-symbol-data-secure-stars-on-blue-matrix-background-vector-illustration-image177757391.html
General Data Protection Regulation - GDPR. padlock symbol, data secure. Stars on blue matrix background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/general-data-protection-regulation-gdpr-padlock-symbol-data-secure-stars-on-blue-matrix-background-vector-illustration-image177757391.htmlRFM95FA7–General Data Protection Regulation - GDPR. padlock symbol, data secure. Stars on blue matrix background. Vector illustration
 Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294861.html
Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294861.htmlRF2T25HB9–Secure digital space. Virtual confidential, programming protection. Vector
 Internet lan and wan wired connection. Data transmission, hardware, Datacenter for secure information. Hacking or hackers safety services. Global communication Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-lan-and-wan-wired-connection-data-transmission-hardware-datacenter-for-secure-information-hacking-or-hackers-safety-services-global-communication-image469883199.html
Internet lan and wan wired connection. Data transmission, hardware, Datacenter for secure information. Hacking or hackers safety services. Global communication Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-lan-and-wan-wired-connection-data-transmission-hardware-datacenter-for-secure-information-hacking-or-hackers-safety-services-global-communication-image469883199.htmlRF2J8D0PR–Internet lan and wan wired connection. Data transmission, hardware, Datacenter for secure information. Hacking or hackers safety services. Global communication
RM2BC71GP–Wire, secure messenger service, app icon, display on display of mobile phone, smartphone, detail, full format
 Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-with-antivirus-for-protection-security-and-blocking-of-receiving-spam-by-email-spam-blocker-email-protection-and-secure-communication-on-i-image221830154.html
Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-with-antivirus-for-protection-security-and-blocking-of-receiving-spam-by-email-spam-blocker-email-protection-and-secure-communication-on-i-image221830154.htmlRFPTW6HE–Computer with antivirus for protection, security and blocking of receiving spam by email. Spam blocker. Email protection and secure communication on i
 Clicking on the submit button over a gradient background inside a laptop computer Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/clicking-on-the-submit-button-over-a-gradient-background-inside-a-laptop-computer-image555352398.html
Clicking on the submit button over a gradient background inside a laptop computer Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/clicking-on-the-submit-button-over-a-gradient-background-inside-a-laptop-computer-image555352398.htmlRF2R7EDJ6–Clicking on the submit button over a gradient background inside a laptop computer
 Internet Security - Business Book Title. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-security-business-book-title-3d-135735140.html
Internet Security - Business Book Title. 3D. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-security-business-book-title-3d-135735140.htmlRFHTR7FG–Internet Security - Business Book Title. 3D.
 Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516044.html
Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-concept-user-privacy-security-and-encryption-secure-internet-access-future-technology-and-cybernetics-screen-padlock-image561516044.htmlRF2RHF7CC–Cybersecurity concept, user privacy security and encryption, secure internet access Future technology and cybernetics, screen padlock.
 Old office desk and typewriter from early 1900s. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-from-early-1900s-105111680.html
Old office desk and typewriter from early 1900s. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-old-office-desk-and-typewriter-from-early-1900s-105111680.htmlRMG3070G–Old office desk and typewriter from early 1900s.
 Hand writing sign Secure Chat. Internet Concept approach to protect messages when sent beyond the corporate Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-secure-chat-internet-concept-approach-to-protect-messages-when-sent-beyond-the-corporate-image547445998.html
Hand writing sign Secure Chat. Internet Concept approach to protect messages when sent beyond the corporate Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-secure-chat-internet-concept-approach-to-protect-messages-when-sent-beyond-the-corporate-image547445998.htmlRM2PPJ8XP–Hand writing sign Secure Chat. Internet Concept approach to protect messages when sent beyond the corporate
 Internet privacy communication protection, antivirus security technology vector illustration. UX, UI onboarding mobile app page screen set with line cloud connection symbols, secure cyber web shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-privacy-communication-protection-antivirus-security-technology-vector-illustration-ux-ui-onboarding-mobile-app-page-screen-set-with-line-cloud-connection-symbols-secure-cyber-web-shield-image408283915.html
Internet privacy communication protection, antivirus security technology vector illustration. UX, UI onboarding mobile app page screen set with line cloud connection symbols, secure cyber web shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-privacy-communication-protection-antivirus-security-technology-vector-illustration-ux-ui-onboarding-mobile-app-page-screen-set-with-line-cloud-connection-symbols-secure-cyber-web-shield-image408283915.htmlRF2EM6X8B–Internet privacy communication protection, antivirus security technology vector illustration. UX, UI onboarding mobile app page screen set with line cloud connection symbols, secure cyber web shield
 Cybersecurity and global communication, secure data network technology, cyberattack protection for worldwide connections, finance, IoT and cryptocurre Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-and-global-communication-secure-data-network-technology-cyberattack-protection-for-worldwide-connections-finance-iot-and-cryptocurre-image184784146.html
Cybersecurity and global communication, secure data network technology, cyberattack protection for worldwide connections, finance, IoT and cryptocurre Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-and-global-communication-secure-data-network-technology-cyberattack-protection-for-worldwide-connections-finance-iot-and-cryptocurre-image184784146.htmlRFMMHJ1P–Cybersecurity and global communication, secure data network technology, cyberattack protection for worldwide connections, finance, IoT and cryptocurre
 Home Security Logo Template. Concept of smart home security. Control of house using smartphone. Picture in the form of smartphone with logo of the Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/home-security-logo-template-concept-of-smart-home-security-control-of-house-using-smartphone-picture-in-the-form-of-smartphone-with-logo-of-the-image249240163.html
Home Security Logo Template. Concept of smart home security. Control of house using smartphone. Picture in the form of smartphone with logo of the Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/home-security-logo-template-concept-of-smart-home-security-control-of-house-using-smartphone-picture-in-the-form-of-smartphone-with-logo-of-the-image249240163.htmlRFTDDTAB–Home Security Logo Template. Concept of smart home security. Control of house using smartphone. Picture in the form of smartphone with logo of the
RF2X8E8GP–Image of white spots over security padlock icon against spinning globe and world map
RFE4EWXK–Businessman touching virtual futuristic display with icon for secure email communication
RFDN0FFP–Secure announcement icon
 Text showing inspiration Secure Communication. Business overview preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-secure-communication-business-overview-preventing-unauthorized-interceptors-from-accessing-image550269314.html
Text showing inspiration Secure Communication. Business overview preventing unauthorized interceptors from accessing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-secure-communication-business-overview-preventing-unauthorized-interceptors-from-accessing-image550269314.htmlRF2PY6X3E–Text showing inspiration Secure Communication. Business overview preventing unauthorized interceptors from accessing
 secure or censure internet concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-secure-or-censure-internet-concept-112978905.html
secure or censure internet concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-secure-or-censure-internet-concept-112978905.htmlRFGFPHMW–secure or censure internet concept
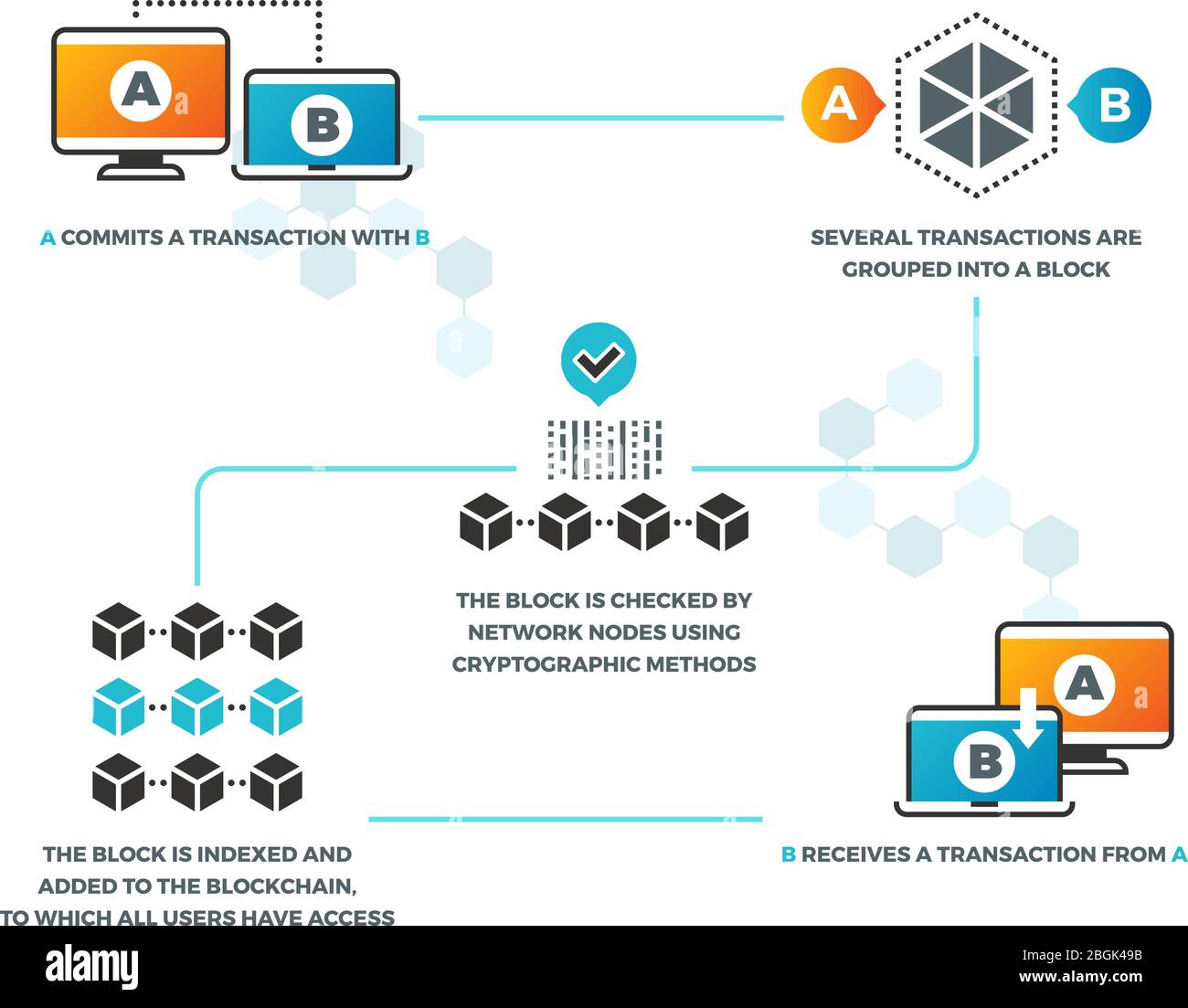 Smart contract. How smart contracts work in blockchain with cryptocurrency. Business networking, digital validation vector infographics. Illustration of business system communication web payment Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smart-contract-how-smart-contracts-work-in-blockchain-with-cryptocurrency-business-networking-digital-validation-vector-infographics-illustration-of-business-system-communication-web-payment-image354462343.html
Smart contract. How smart contracts work in blockchain with cryptocurrency. Business networking, digital validation vector infographics. Illustration of business system communication web payment Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smart-contract-how-smart-contracts-work-in-blockchain-with-cryptocurrency-business-networking-digital-validation-vector-infographics-illustration-of-business-system-communication-web-payment-image354462343.htmlRF2BGK49B–Smart contract. How smart contracts work in blockchain with cryptocurrency. Business networking, digital validation vector infographics. Illustration of business system communication web payment
 General Data Protection Regulation - GDPR. Shild with padlock, data secure. Stars on blue matrix background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/general-data-protection-regulation-gdpr-shild-with-padlock-data-secure-stars-on-blue-matrix-background-vector-illustration-image177757400.html
General Data Protection Regulation - GDPR. Shild with padlock, data secure. Stars on blue matrix background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/general-data-protection-regulation-gdpr-shild-with-padlock-data-secure-stars-on-blue-matrix-background-vector-illustration-image177757400.htmlRFM95FAG–General Data Protection Regulation - GDPR. Shild with padlock, data secure. Stars on blue matrix background. Vector illustration
 Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294791.html
Secure digital space. Virtual confidential, programming protection. Vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/secure-digital-space-virtual-confidential-programming-protection-vector-image569294791.htmlRF2T25H8R–Secure digital space. Virtual confidential, programming protection. Vector
Search Results for Secure communication Stock Photos and Images (88,768)
Page 1 of 500