Page 1 of 6
Online phishing Black & White Stock Photos
 Spam email. Man forefinger pressing on enter button for blocking junk mail, unsolicited messages, ads for money scams. Black and white. Male working on laptop. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spam-email-man-forefinger-pressing-on-enter-button-for-blocking-junk-mail-unsolicited-messages-ads-for-money-scams-black-and-white-male-working-on-laptop-high-quality-photo-image470977183.html
Spam email. Man forefinger pressing on enter button for blocking junk mail, unsolicited messages, ads for money scams. Black and white. Male working on laptop. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spam-email-man-forefinger-pressing-on-enter-button-for-blocking-junk-mail-unsolicited-messages-ads-for-money-scams-black-and-white-male-working-on-laptop-high-quality-photo-image470977183.htmlRF2JA6T5K–Spam email. Man forefinger pressing on enter button for blocking junk mail, unsolicited messages, ads for money scams. Black and white. Male working on laptop. High quality photo
 photo of padlocks in macro that symbolize union in black and white Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/photo-of-padlocks-in-macro-that-symbolize-union-in-black-and-white-image187526907.html
photo of padlocks in macro that symbolize union in black and white Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/photo-of-padlocks-in-macro-that-symbolize-union-in-black-and-white-image187526907.htmlRFMW2GDF–photo of padlocks in macro that symbolize union in black and white
 Spam emails, email account, email, Internet, Internet fraud, phishing, symbolic image, screenshot Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-spam-emails-email-account-email-internet-internet-fraud-phishing-symbolic-133708718.html
Spam emails, email account, email, Internet, Internet fraud, phishing, symbolic image, screenshot Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-spam-emails-email-account-email-internet-internet-fraud-phishing-symbolic-133708718.htmlRFHNEXRA–Spam emails, email account, email, Internet, Internet fraud, phishing, symbolic image, screenshot
 Spam. Drawn envelopes falling into bin with crumpled paper near white wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spam-drawn-envelopes-falling-into-bin-with-crumpled-paper-near-white-wall-image557462102.html
Spam. Drawn envelopes falling into bin with crumpled paper near white wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spam-drawn-envelopes-falling-into-bin-with-crumpled-paper-near-white-wall-image557462102.htmlRF2RAXGGP–Spam. Drawn envelopes falling into bin with crumpled paper near white wall
 Computer mouses are like Fish gathering to Click a Bait Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-mouses-are-like-fish-gathering-to-click-a-bait-concept-135631742.html
Computer mouses are like Fish gathering to Click a Bait Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-mouses-are-like-fish-gathering-to-click-a-bait-concept-135631742.htmlRFHTJFJP–Computer mouses are like Fish gathering to Click a Bait Concept.
RF2G57XTG–Phishing malware for login password on notebook computer or smartphone symbols vector illustration icon set
RF2J3FDDN–Concept of phishing with connected icons
 Computer hacker in white gloves stealing information on laptop Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-hacker-in-white-gloves-stealing-information-on-laptop-133896139.html
Computer hacker in white gloves stealing information on laptop Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-hacker-in-white-gloves-stealing-information-on-laptop-133896139.htmlRFHNRDTY–Computer hacker in white gloves stealing information on laptop
 Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-using-smartphone-men-in-black-clothes-with-hidden-face-looks-at-smartphone-screen-image457007561.html
Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-using-smartphone-men-in-black-clothes-with-hidden-face-looks-at-smartphone-screen-image457007561.htmlRF2HFEDPH–Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen
 Close-up of a keyboard on which there is a credit card and a padlock. Concepts related to internet security, personal or bank data Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-of-a-keyboard-on-which-there-is-a-credit-card-and-a-padlock-concepts-related-to-internet-security-personal-or-bank-data-image357839380.html
Close-up of a keyboard on which there is a credit card and a padlock. Concepts related to internet security, personal or bank data Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-of-a-keyboard-on-which-there-is-a-credit-card-and-a-padlock-concepts-related-to-internet-security-personal-or-bank-data-image357839380.htmlRF2BP4YNT–Close-up of a keyboard on which there is a credit card and a padlock. Concepts related to internet security, personal or bank data
 Scammer Using Smartphone to make a call. Men in black clothes with hidden face. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scammer-using-smartphone-to-make-a-call-men-in-black-clothes-with-hidden-face-image457007399.html
Scammer Using Smartphone to make a call. Men in black clothes with hidden face. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scammer-using-smartphone-to-make-a-call-men-in-black-clothes-with-hidden-face-image457007399.htmlRF2HFEDGR–Scammer Using Smartphone to make a call. Men in black clothes with hidden face.
RF2HPF1T6–Phishing scam vector icon illustration
RF2HNEGF9–Phishing Simple vector icon. Illustration symbol design template for web mobile UI element.
RF2HFF9NA–Phishing scam vector icon illustration (internet browser )
 Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Bright city background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/portrait-of-an-anonymous-man-in-a-black-hoodie-and-neon-mask-hacking-into-a-smartphone-bright-city-background-image336332840.html
Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Bright city background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/portrait-of-an-anonymous-man-in-a-black-hoodie-and-neon-mask-hacking-into-a-smartphone-bright-city-background-image336332840.htmlRF2AF57Y4–Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Bright city background
 Illustration of muslim woman with credit card almost get scammed by submit password concept of phishing. Single line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-muslim-woman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-single-line-art-style-design-image504015388.html
Illustration of muslim woman with credit card almost get scammed by submit password concept of phishing. Single line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-muslim-woman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-single-line-art-style-design-image504015388.htmlRF2M7YTNG–Illustration of muslim woman with credit card almost get scammed by submit password concept of phishing. Single line art style design
 The word SCAM! handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-word-scam!-handwritten-on-a-white-background-image396961509.html
The word SCAM! handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-word-scam!-handwritten-on-a-white-background-image396961509.htmlRF2E1R4CN–The word SCAM! handwritten on a white background.
 Masked robber with a fishing rode stealing credit card from a smartphone. Cartoon flat vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-robber-with-a-fishing-rode-stealing-credit-card-from-a-smartphone-cartoon-flat-vector-illustration-image385322065.html
Masked robber with a fishing rode stealing credit card from a smartphone. Cartoon flat vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-robber-with-a-fishing-rode-stealing-credit-card-from-a-smartphone-cartoon-flat-vector-illustration-image385322065.htmlRF2DATX69–Masked robber with a fishing rode stealing credit card from a smartphone. Cartoon flat vector illustration.
 Cybercrime, a laptop hacker, writes codes to access unauthorized things, an illegal way, hacker, crime, cyber Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybercrime-a-laptop-hacker-writes-codes-to-access-unauthorized-things-an-illegal-way-hacker-crime-cyber-image207886028.html
Cybercrime, a laptop hacker, writes codes to access unauthorized things, an illegal way, hacker, crime, cyber Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybercrime-a-laptop-hacker-writes-codes-to-access-unauthorized-things-an-illegal-way-hacker-crime-cyber-image207886028.htmlRFP260N0–Cybercrime, a laptop hacker, writes codes to access unauthorized things, an illegal way, hacker, crime, cyber
 Computer hacker in hood working in dark room Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-hacker-in-hood-working-in-dark-room-image179093926.html
Computer hacker in hood working in dark room Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-hacker-in-hood-working-in-dark-room-image179093926.htmlRFMBAC3J–Computer hacker in hood working in dark room
 skull and crossbones with the word HACKER on a old wooden floor with reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/skull-and-crossbones-with-the-word-hacker-on-a-old-wooden-floor-with-reflection-image382841320.html
skull and crossbones with the word HACKER on a old wooden floor with reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/skull-and-crossbones-with-the-word-hacker-on-a-old-wooden-floor-with-reflection-image382841320.htmlRF2D6RX08–skull and crossbones with the word HACKER on a old wooden floor with reflection
 Security concept: Phishing on tablet pc computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-security-concept-phishing-on-tablet-pc-computer-119561817.html
Security concept: Phishing on tablet pc computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-security-concept-phishing-on-tablet-pc-computer-119561817.htmlRFGXEE8W–Security concept: Phishing on tablet pc computer
RF2A8HATJ–Spam mail icon. Envelope symbol with word SPAM on it.
 Computer mouses are like Fish gathering to Click a Bait Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-mouses-are-like-fish-gathering-to-click-a-bait-concept-135631745.html
Computer mouses are like Fish gathering to Click a Bait Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-mouses-are-like-fish-gathering-to-click-a-bait-concept-135631745.htmlRFHTJFJW–Computer mouses are like Fish gathering to Click a Bait Concept.
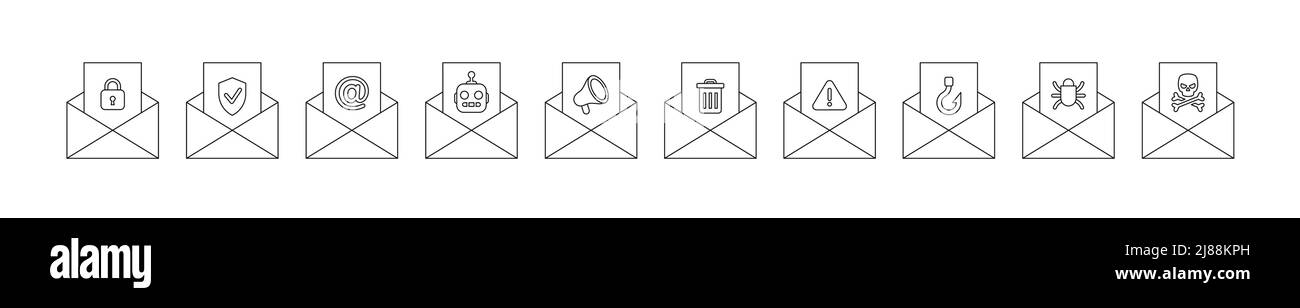 Line set email envelope with letter options from safe protected to the dangerous virus, set vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/line-set-email-envelope-with-letter-options-from-safe-protected-to-the-dangerous-virus-set-vector-illustration-image469788329.html
Line set email envelope with letter options from safe protected to the dangerous virus, set vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/line-set-email-envelope-with-letter-options-from-safe-protected-to-the-dangerous-virus-set-vector-illustration-image469788329.htmlRF2J88KPH–Line set email envelope with letter options from safe protected to the dangerous virus, set vector illustration
RF2PK84N3–Insecure computer protection icon. Line style vector EPS.
RFT6N3DH–Account password and fishing hook, data phishing, hacking online scam line icon.
RF2PK5WJC–Insecure computer protection icon. Flat style vector EPS.
RF2GHKBW3–Account password and fishing hook, data phishing, hacking online scam grey icon.
 Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-using-smartphone-men-in-black-clothes-with-hidden-face-looks-at-smartphone-screen-image457007402.html
Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-using-smartphone-men-in-black-clothes-with-hidden-face-looks-at-smartphone-screen-image457007402.htmlRF2HFEDGX–Hacker Using Smartphone. Men in black clothes with hidden face looks at smartphone screen
RF2E2M3KC–Cybersecurity outline icon. Phishing attack concept. Malicious email with fishing hook. Simple line art isolated illustration
 Virus word cloud concept over dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-virus-word-cloud-concept-over-dark-background-163446800.html
Virus word cloud concept over dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-virus-word-cloud-concept-over-dark-background-163446800.htmlRFKDWJ1M–Virus word cloud concept over dark background
RF2HFF79K–Phishing scam vector icon illustration (laptop pc)
 Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Studio shot. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/portrait-of-an-anonymous-man-in-a-black-hoodie-and-neon-mask-hacking-into-a-smartphone-studio-shot-image336332841.html
Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Studio shot. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/portrait-of-an-anonymous-man-in-a-black-hoodie-and-neon-mask-hacking-into-a-smartphone-studio-shot-image336332841.htmlRF2AF57Y5–Portrait of an anonymous man in a black hoodie and neon mask hacking into a smartphone. Studio shot.
 Cartoon of businessman as cyber thief hacker try to get credit card concept of phishing. One line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-of-businessman-as-cyber-thief-hacker-try-to-get-credit-card-concept-of-phishing-one-line-art-style-design-image503996507.html
Cartoon of businessman as cyber thief hacker try to get credit card concept of phishing. One line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-of-businessman-as-cyber-thief-hacker-try-to-get-credit-card-concept-of-phishing-one-line-art-style-design-image503996507.htmlRF2M7Y0K7–Cartoon of businessman as cyber thief hacker try to get credit card concept of phishing. One line art style design
 Scam Alert! handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scam-alert!-handwritten-on-a-white-background-image396961511.html
Scam Alert! handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/scam-alert!-handwritten-on-a-white-background-image396961511.htmlRF2E1R4CR–Scam Alert! handwritten on a white background.
 Man, Businessman or Office Worker Get Hit by Fist From Computer, Vector Cartoon Stick Figure Illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/man-businessman-or-office-worker-get-hit-by-fist-from-computer-vector-cartoon-stick-figure-illustration-image418157292.html
Man, Businessman or Office Worker Get Hit by Fist From Computer, Vector Cartoon Stick Figure Illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/man-businessman-or-office-worker-get-hit-by-fist-from-computer-vector-cartoon-stick-figure-illustration-image418157292.htmlRF2F88KW0–Man, Businessman or Office Worker Get Hit by Fist From Computer, Vector Cartoon Stick Figure Illustration
 Illustration of little men on a pen. Vector. Smartphone as bait. Dependence on the phone and the Internet. Linear style. Illustration for website or p Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-little-men-on-a-pen-vector-smartphone-as-bait-dependence-on-the-phone-and-the-internet-linear-style-illustration-for-website-or-p-image260745944.html
Illustration of little men on a pen. Vector. Smartphone as bait. Dependence on the phone and the Internet. Linear style. Illustration for website or p Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-little-men-on-a-pen-vector-smartphone-as-bait-dependence-on-the-phone-and-the-internet-linear-style-illustration-for-website-or-p-image260745944.htmlRFW46034–Illustration of little men on a pen. Vector. Smartphone as bait. Dependence on the phone and the Internet. Linear style. Illustration for website or p
 Vector cartoon stick figure drawing conceptual illustration of man, hacker or businessman sitting in front of six computer monitors mounted on wall hacking or analyzing data. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vector-cartoon-stick-figure-drawing-conceptual-illustration-of-man-hacker-or-businessman-sitting-in-front-of-six-computer-monitors-mounted-on-wall-hacking-or-analyzing-data-image331822322.html
Vector cartoon stick figure drawing conceptual illustration of man, hacker or businessman sitting in front of six computer monitors mounted on wall hacking or analyzing data. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vector-cartoon-stick-figure-drawing-conceptual-illustration-of-man-hacker-or-businessman-sitting-in-front-of-six-computer-monitors-mounted-on-wall-hacking-or-analyzing-data-image331822322.htmlRF2A7RPN6–Vector cartoon stick figure drawing conceptual illustration of man, hacker or businessman sitting in front of six computer monitors mounted on wall hacking or analyzing data.
RF2GG5Y6A–Vector illustration. flat design. Criminal robber internet icon
 Illustration of a phishing concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-a-phishing-concept-image453262245.html
Illustration of a phishing concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-a-phishing-concept-image453262245.htmlRF2H9BTH9–Illustration of a phishing concept
 pop-up alert with pirate skull and net grabbing other people's data, concept of ransomware cyber attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-pop-up-alert-with-pirate-skull-and-net-grabbing-other-peoples-data-140663286.html
pop-up alert with pirate skull and net grabbing other people's data, concept of ransomware cyber attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-pop-up-alert-with-pirate-skull-and-net-grabbing-other-peoples-data-140663286.htmlRFJ4RNCP–pop-up alert with pirate skull and net grabbing other people's data, concept of ransomware cyber attack
RFRG3GHT–Conceptual hand writing showing Mobile Secure Gateway. Business photo showcasing Securing devices from phishing or malicious attack Polka Dots Pixel E
RF2T9R96P–PC monitor icon with skull. Computer virus attack icon. Vector illustration
 Virus word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-word-cloud-concept-image227515589.html
Virus word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-word-cloud-concept-image227515589.htmlRFR646CN–Virus word cloud concept
RF2HNF530–Spyware Simple vector icon. Illustration symbol design template for web mobile UI element.
RF2AE48EJ–Malware, threat, mobile virus icon
RF2HNJF5K–Social engineering Simple vector icon. Illustration symbol design template for web mobile UI element.
RF2RCF7PB–Computer hacker with laptop icon, vector
RF2HNEKC8–Data leak Simple vector icon. Illustration symbol design template for web mobile UI element.
 hacker word on keyboard, attack, internet terrorism concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-word-on-keyboard-attack-internet-terrorism-concept-96179590.html
hacker word on keyboard, attack, internet terrorism concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-word-on-keyboard-attack-internet-terrorism-concept-96179590.htmlRFFGDA1A–hacker word on keyboard, attack, internet terrorism concept
 message in a smartphone vector graphic design illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/message-in-a-smartphone-vector-graphic-design-illustration-image356919042.html
message in a smartphone vector graphic design illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/message-in-a-smartphone-vector-graphic-design-illustration-image356919042.htmlRF2BMK1TJ–message in a smartphone vector graphic design illustration
 hacker word on keyboard, attack, internet terrorism concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-word-on-keyboard-attack-internet-terrorism-concept-96183681.html
hacker word on keyboard, attack, internet terrorism concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-word-on-keyboard-attack-internet-terrorism-concept-96183681.htmlRFFGDF7D–hacker word on keyboard, attack, internet terrorism concept
 Illustration of businesswoman as cyber thief hacker try to get credit card concept of phishing. Single continuous line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-businesswoman-as-cyber-thief-hacker-try-to-get-credit-card-concept-of-phishing-single-continuous-line-art-style-design-image503998729.html
Illustration of businesswoman as cyber thief hacker try to get credit card concept of phishing. Single continuous line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/illustration-of-businesswoman-as-cyber-thief-hacker-try-to-get-credit-card-concept-of-phishing-single-continuous-line-art-style-design-image503998729.htmlRF2M7Y3EH–Illustration of businesswoman as cyber thief hacker try to get credit card concept of phishing. Single continuous line art style design
 Phone Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phone-scam-handwritten-on-a-white-background-image396961512.html
Phone Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phone-scam-handwritten-on-a-white-background-image396961512.htmlRF2E1R4CT–Phone Scam handwritten on a white background.
 black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-credit-card-on-easy-overview-simple-outline-modern-finance-inquiry-logotype-graphic-design-isolated-on-white-concept-of-banking-risk-image563316025.html
black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-credit-card-on-easy-overview-simple-outline-modern-finance-inquiry-logotype-graphic-design-isolated-on-white-concept-of-banking-risk-image563316025.htmlRF2RMD79D–black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk
 Cartoon style black and white doodle of mobile phone with attacking virus on screen. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-style-black-and-white-doodle-of-mobile-phone-with-attacking-virus-on-screen-image467639636.html
Cartoon style black and white doodle of mobile phone with attacking virus on screen. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-style-black-and-white-doodle-of-mobile-phone-with-attacking-virus-on-screen-image467639636.htmlRF2J4PR3G–Cartoon style black and white doodle of mobile phone with attacking virus on screen.
 email, connect, internet, www, worldwideweb, net, web, computers, computer, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-email-connect-internet-www-worldwideweb-net-web-computers-computer-143649520.html
email, connect, internet, www, worldwideweb, net, web, computers, computer, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-email-connect-internet-www-worldwideweb-net-web-computers-computer-143649520.htmlRFJ9KPC0–email, connect, internet, www, worldwideweb, net, web, computers, computer,
RF2J9H00N–Phishing black glyph icon
RF2JH8509–Hacker phishing icon
RF2WMWYGB–Money crime line icons. Fraud, Online thief and Steal cash set. Vector
 Folder with virus in black and white Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/folder-with-virus-in-black-and-white-image216933497.html
Folder with virus in black and white Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/folder-with-virus-in-black-and-white-image216933497.htmlRFPGX4TW–Folder with virus in black and white
 technology virus bug skull bones alert pattern Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-technology-virus-bug-skull-bones-alert-pattern-176068422.html
technology virus bug skull bones alert pattern Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-technology-virus-bug-skull-bones-alert-pattern-176068422.htmlRFM6CH1X–technology virus bug skull bones alert pattern
 Web piracy Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-81409491.html
Web piracy Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-81409491.htmlRFEMCEHR–Web piracy
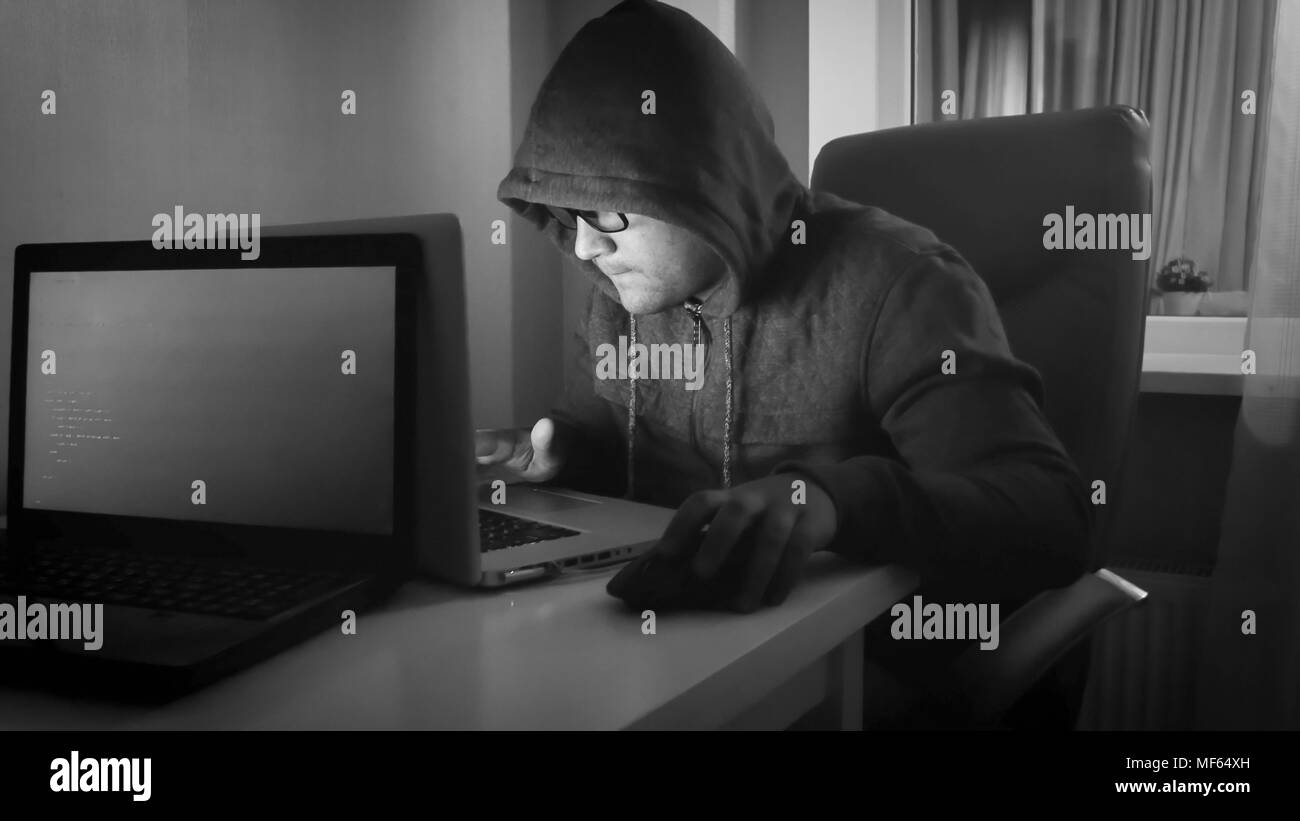 Black and white portrait of young hacker working on laptop at home Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-and-white-portrait-of-young-hacker-working-on-laptop-at-home-image181459113.html
Black and white portrait of young hacker working on laptop at home Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-and-white-portrait-of-young-hacker-working-on-laptop-at-home-image181459113.htmlRFMF64XH–Black and white portrait of young hacker working on laptop at home
RF2AE48F1–Malware, threat, mobile virus icon
RFW36RG4–Email Notification, Quick Message. Flat Vector Icon illustration. Simple black symbol on white background. Email Notification, Quick Message sign desi
RF2PMN7BT–Data Phishing Vector Thick Line Icon For Personal And Commercial Use.
 skull and crossbones with the word HACKER on a old wooden floor with reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/skull-and-crossbones-with-the-word-hacker-on-a-old-wooden-floor-with-reflection-image382853542.html
skull and crossbones with the word HACKER on a old wooden floor with reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/skull-and-crossbones-with-the-word-hacker-on-a-old-wooden-floor-with-reflection-image382853542.htmlRF2D6TDGP–skull and crossbones with the word HACKER on a old wooden floor with reflection
 Text sign showing Scam Alert. Business photo showcasing fraudulently obtain money from victim by persuading him Straight Line Doodles Creating Abstrac Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-scam-alert-business-photo-showcasing-fraudulently-obtain-money-from-victim-by-persuading-him-straight-line-doodles-creating-abstrac-image241089725.html
Text sign showing Scam Alert. Business photo showcasing fraudulently obtain money from victim by persuading him Straight Line Doodles Creating Abstrac Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-scam-alert-business-photo-showcasing-fraudulently-obtain-money-from-victim-by-persuading-him-straight-line-doodles-creating-abstrac-image241089725.htmlRFT06GB9–Text sign showing Scam Alert. Business photo showcasing fraudulently obtain money from victim by persuading him Straight Line Doodles Creating Abstrac
RF2N315X0–Data phishing icon simple vector. Virus hacker. Internet online
RF2CRYTWA–Cyber security and crime black glyph icon. Internet fraud. Thief stealing confidential data, personal information. Sign for web page, mobile app
 Drawing of businessman with credit card almost get scammed by submit password concept of phishing. Continuous line art design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/drawing-of-businessman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-continuous-line-art-design-image504000829.html
Drawing of businessman with credit card almost get scammed by submit password concept of phishing. Continuous line art design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/drawing-of-businessman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-continuous-line-art-design-image504000829.htmlRF2M7Y65H–Drawing of businessman with credit card almost get scammed by submit password concept of phishing. Continuous line art design
 Financial Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/financial-scam-handwritten-on-a-white-background-image396961513.html
Financial Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/financial-scam-handwritten-on-a-white-background-image396961513.htmlRF2E1R4CW–Financial Scam handwritten on a white background.
 black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-credit-card-on-easy-overview-simple-outline-modern-finance-inquiry-logotype-graphic-design-isolated-on-white-concept-of-banking-risk-image563315808.html
black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-credit-card-on-easy-overview-simple-outline-modern-finance-inquiry-logotype-graphic-design-isolated-on-white-concept-of-banking-risk-image563315808.htmlRF2RMD71M–black thin line credit card on easy overview. simple outline modern finance inquiry logotype graphic design isolated on white. concept of banking risk
RF2CRYNPY–Cyber security and crime black line icon. Internet fraud. Thief stealing confidential data, personal information. Sign for web page, mobile app
 thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thin-line-credit-card-with-black-magnifying-glass-concept-of-banking-risk-detection-or-check-falsification-flat-outline-trend-modern-logotype-graphi-image563315310.html
thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thin-line-credit-card-with-black-magnifying-glass-concept-of-banking-risk-detection-or-check-falsification-flat-outline-trend-modern-logotype-graphi-image563315310.htmlRF2RMD6BX–thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi
RF2G6M77M–Email phishing linear icon
 thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thin-line-credit-card-with-black-magnifying-glass-concept-of-banking-risk-detection-or-check-falsification-flat-outline-trend-modern-logotype-graphi-image563314237.html
thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thin-line-credit-card-with-black-magnifying-glass-concept-of-banking-risk-detection-or-check-falsification-flat-outline-trend-modern-logotype-graphi-image563314237.htmlRF2RMD51H–thin line credit card with black magnifying glass. concept of banking risk detection or check falsification. flat outline trend modern logotype graphi
RF2JGY6AM–Protection and security phishing icon .
RF2RMD2GN–customer brand magnet icon, target strategy, influence social or media, attract user, generate marketing people, awareness in phone, thin line symbol
 Smartphone and email with virus in black and white Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-and-email-with-virus-in-black-and-white-image216933501.html
Smartphone and email with virus in black and white Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/smartphone-and-email-with-virus-in-black-and-white-image216933501.htmlRFPGX4W1–Smartphone and email with virus in black and white
 risk shopping buy theft stealing fraud swindling security safety online type Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-risk-shopping-buy-theft-stealing-fraud-swindling-security-safety-online-141732562.html
risk shopping buy theft stealing fraud swindling security safety online type Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-risk-shopping-buy-theft-stealing-fraud-swindling-security-safety-online-141732562.htmlRFJ6GD96–risk shopping buy theft stealing fraud swindling security safety online type
RFHEDCRR–security system concept bomb icon outline
RF2AE48E1–Malware, threat, mobile virus icon
RF2CT1GCF–Email scam black glyph icon on white background. Web fraud. Mailing of letters. Spamming attack. Pictogram for web page, mobile app, promo. UI UX GUI
 cyber security virus bug attack system Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-virus-bug-attack-system-image181764773.html
cyber security virus bug attack system Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-virus-bug-attack-system-image181764773.htmlRFMFM2R1–cyber security virus bug attack system
RF2CT1NCC–Email scam black line icon on white background. Web fraud. Mailing of letters. Spamming attack. Pictogram for web page, mobile app, promo. UI UX GUI
RFRFAJ5G–Thief hacker avatar symbol in black and white
RF2N31JAH–Data phishing icon outline vector. Virus hacker. Internet online
RF2X6GBN4–Email Notification, Quick Message flat vector icon. Simple solid symbol isolated on white background. Email Notification, Quick Message sign design te
 Cartoon of businesswoman with credit card almost get scammed by submit password concept of phishing. Single line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-of-businesswoman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-single-line-art-style-design-image503996596.html
Cartoon of businesswoman with credit card almost get scammed by submit password concept of phishing. Single line art style design Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cartoon-of-businesswoman-with-credit-card-almost-get-scammed-by-submit-password-concept-of-phishing-single-line-art-style-design-image503996596.htmlRF2M7Y0PC–Cartoon of businesswoman with credit card almost get scammed by submit password concept of phishing. Single line art style design
 Financial Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/financial-scam-handwritten-on-a-white-background-image396961515.html
Financial Scam handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/financial-scam-handwritten-on-a-white-background-image396961515.htmlRF2E1R4CY–Financial Scam handwritten on a white background.
 Side view of a female hacker stealing information from multiple computers - 3d rendering Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/side-view-of-a-female-hacker-stealing-information-from-multiple-computers-3d-rendering-image401911732.html
Side view of a female hacker stealing information from multiple computers - 3d rendering Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/side-view-of-a-female-hacker-stealing-information-from-multiple-computers-3d-rendering-image401911732.htmlRF2E9TJEC–Side view of a female hacker stealing information from multiple computers - 3d rendering
 continuous single line drawing of computer hacker stereotype, line art vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/continuous-single-line-drawing-of-computer-hacker-stereotype-line-art-vector-illustration-image605012672.html
continuous single line drawing of computer hacker stereotype, line art vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/continuous-single-line-drawing-of-computer-hacker-stereotype-line-art-vector-illustration-image605012672.htmlRF2X48KRC–continuous single line drawing of computer hacker stereotype, line art vector illustration
 Cloud storage, internet data security and exchange protections, web phishing and hacking. Vector cloud storage and hosting server network technology, Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-storage-internet-data-security-and-exchange-protections-web-phishing-and-hacking-vector-cloud-storage-and-hosting-server-network-technology-image408079837.html
Cloud storage, internet data security and exchange protections, web phishing and hacking. Vector cloud storage and hosting server network technology, Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-storage-internet-data-security-and-exchange-protections-web-phishing-and-hacking-vector-cloud-storage-and-hosting-server-network-technology-image408079837.htmlRF2EKWHYW–Cloud storage, internet data security and exchange protections, web phishing and hacking. Vector cloud storage and hosting server network technology,
RF2G6RGK9–Email phishing black glyph icon
RF2GJKX4R–Criminal, robber, internet icon. Vector illustration. flat design.
RF2JH84BA–Hacker mail icon
 world map with laptops with skull popping out of the screen on a spring and message Virus Found, concept of worldwide cyber attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-world-map-with-laptops-with-skull-popping-out-of-the-screen-on-a-spring-140662964.html
world map with laptops with skull popping out of the screen on a spring and message Virus Found, concept of worldwide cyber attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-world-map-with-laptops-with-skull-popping-out-of-the-screen-on-a-spring-140662964.htmlRFJ4RN18–world map with laptops with skull popping out of the screen on a spring and message Virus Found, concept of worldwide cyber attack
Search Results for Online phishing Black & White Stock Photos and Images (501)
Page 1 of 6