Page 1 of 1
False identity card Stock Vectors & Vector Art
RF2D6C3EK–Employees hide behind smiling face mask when boss is around. Vector illustration for on putting a false front at work concept isolated on grey backgro

RF2J15B4W–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and

RF2J4X1ND–Phone frauding. Internet scammer attract people and blackmail money identity call, cyber theft hacking banking card on calls, vector illustration. Fraud and scammer criminal
RF2AP7RR7–Banking scam chalk icon. Skimming. Identity theft. Credit card phishing. Financial fraud. Fake loan offer. Illegal money gain. Malicious, fraudulent s
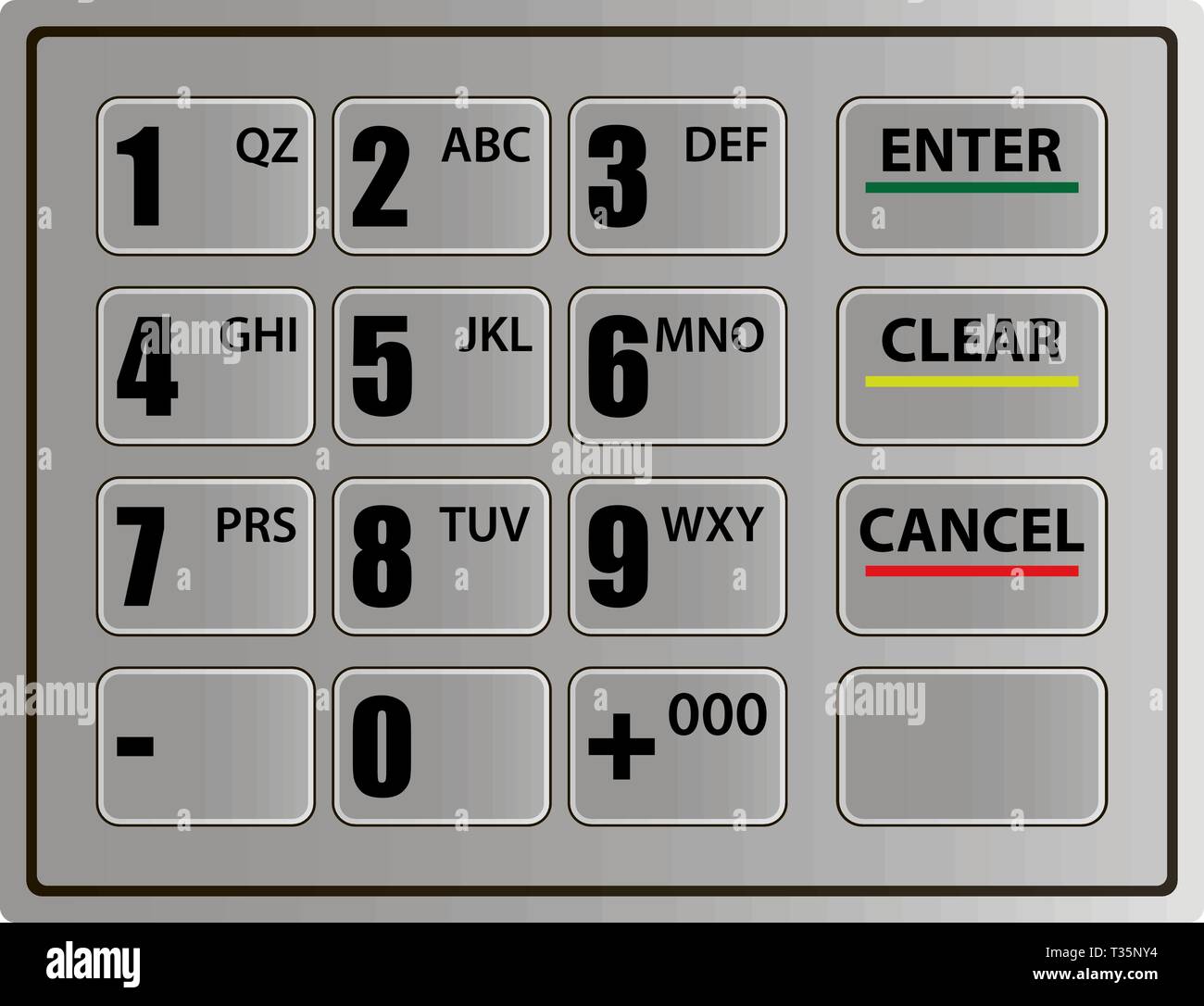
RFT35NY4–Realistic keypad of an automated teller machine, vector illustration on white background. template
RF2PP57MK–White-collar crime linear icons set. Embezzlement, Corruption, Fraud, Insider-trading, Ponzi-scheme, Forgery, Cybercrime line vector and concept signs
RF2JE5AAT–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and
RF2AP7PMA–Banking scam color icon. Skimming. Identity theft. Credit card phishing. Financial fraud. Fake loan offer. Illegal money gain. Malicious practice. Fra
RF2PP5BYP–White-collar crime linear icons set. Embezzlement, Corruption, Fraud, Insider-trading, Ponzi-scheme, Forgery, Cybercrime line vector and concept signs

RF2J7J0FP–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and
RF2AP861N–Banking scam linear icon. Skimming. Identity theft. Credit card phishing. Financial fraud. Fake loan offer. Thin line illustration. Contour symbol. Ve
RF2J15B25–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and
RF2R8X4F0–A frustrated and sad man looks into a computer in which a hacker and thief steals his card data and social networks. hack attack. internet phishing. A
RF2R8XKK8–A frustrated and sad man looks into a computer in which a hacker and thief steals his card data and social networks. hack attack. internet phishing. A

RF2G7JRXH–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and

RF2J1585F–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and

RF2G7JRPJ–Hacker attack. Fraud with user data on social networks. Credit or debit card theft. Internet phishing, hacked username and password. Cybercrime and
Search Results for False identity card Stock Vector Images (21)
Page 1 of 1