SAVE 40% ON SINGLE IMAGE PURCHASES - OFFER ENDS SOON, USE CODE: SAVEIMAGE40%
Quick filters:
Page 1 of 60
Deep dark web Stock Photos and Images
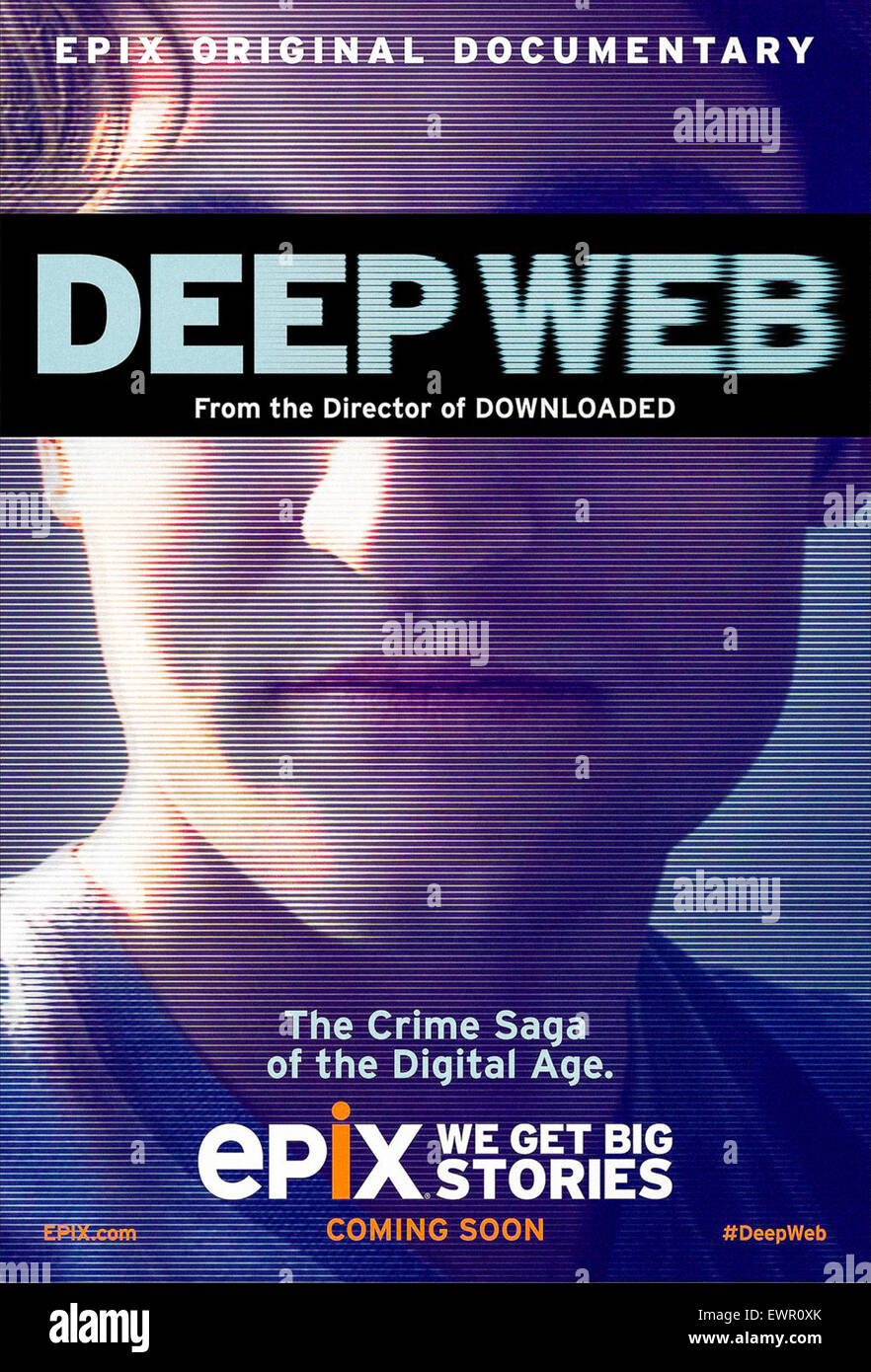 Poster for 'Deep Web' a documentary film about the illicit Silk Road marketplace for drugs and its curious libertarian community accessed anonymously via the dark web. The film explores the arrest and trial of Ross Ulbricht featuring interviews with hackers, cryptographers and law enforcement agents Directed by Alex Winter, narrated by Keanu Reeve and released in 2015. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-poster-for-deep-web-a-documentary-film-about-the-illicit-silk-road-84713515.html
Poster for 'Deep Web' a documentary film about the illicit Silk Road marketplace for drugs and its curious libertarian community accessed anonymously via the dark web. The film explores the arrest and trial of Ross Ulbricht featuring interviews with hackers, cryptographers and law enforcement agents Directed by Alex Winter, narrated by Keanu Reeve and released in 2015. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-poster-for-deep-web-a-documentary-film-about-the-illicit-silk-road-84713515.htmlRMEWR0XK–Poster for 'Deep Web' a documentary film about the illicit Silk Road marketplace for drugs and its curious libertarian community accessed anonymously via the dark web. The film explores the arrest and trial of Ross Ulbricht featuring interviews with hackers, cryptographers and law enforcement agents Directed by Alex Winter, narrated by Keanu Reeve and released in 2015.
 Ctrl key grunge graffiti Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ctrl-key-grunge-graffiti-image483374910.html
Ctrl key grunge graffiti Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ctrl-key-grunge-graffiti-image483374910.htmlRF2K2BHHJ–Ctrl key grunge graffiti
 Hacker typing code on a keyboard, cybercrime and dark web concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hacker-typing-code-on-a-keyboard-cybercrime-and-dark-web-concept-169663583.html
Hacker typing code on a keyboard, cybercrime and dark web concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hacker-typing-code-on-a-keyboard-cybercrime-and-dark-web-concept-169663583.htmlRMKT0RHK–Hacker typing code on a keyboard, cybercrime and dark web concept
 Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-concept-image-of-hooded-cyber-criminal-man-using-computer-to-access-165413688.html
Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-concept-image-of-hooded-cyber-criminal-man-using-computer-to-access-165413688.htmlRMKH36RM–Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns,
 Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599735.html
Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599735.htmlRME7MN5Y–Representation of the Internet 'Deep Web' on computer screen, London
 Colorful ethernet network cables Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-colorful-ethernet-network-cables-169523219.html
Colorful ethernet network cables Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-colorful-ethernet-network-cables-169523219.htmlRFKRPCGK–Colorful ethernet network cables
 Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114054.html
Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114054.htmlRMM00D6E–Crypto currency bitcoins with real money.
 Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-look-to-the-magical-forest-early-morning-with-fantasy-mood-and-fresh-breeze-in-the-north-of-bohemia-image607705007.html
Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-look-to-the-magical-forest-early-morning-with-fantasy-mood-and-fresh-breeze-in-the-north-of-bohemia-image607705007.htmlRF2X8K9X7–Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia.
 SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926420.html
SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926420.htmlRF2F4K2B0–SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo
 MILAN,ITALY, May 2017: Businessman wear anonymus mask and hold sniper rifle.Editorial photo. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-milanitaly-may-2017-businessman-wear-anonymus-mask-and-hold-sniper-143226319.html
MILAN,ITALY, May 2017: Businessman wear anonymus mask and hold sniper rifle.Editorial photo. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-milanitaly-may-2017-businessman-wear-anonymus-mask-and-hold-sniper-143226319.htmlRFJ90EHK–MILAN,ITALY, May 2017: Businessman wear anonymus mask and hold sniper rifle.Editorial photo.
 Two direction signs, one pointing left (Deep web) and the other one, pointing right (Dark web). Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/two-direction-signs-one-pointing-left-deep-web-and-the-other-one-pointing-right-dark-web-image592425991.html
Two direction signs, one pointing left (Deep web) and the other one, pointing right (Dark web). Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/two-direction-signs-one-pointing-left-deep-web-and-the-other-one-pointing-right-dark-web-image592425991.htmlRF2WBR9B3–Two direction signs, one pointing left (Deep web) and the other one, pointing right (Dark web).
 The word dark web on wooden cube with computer keyboard against black background. Cyber crime and illegal outlets in cyberspace or internet technology Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-word-dark-web-on-wooden-cube-with-computer-keyboard-against-black-background-cyber-crime-and-illegal-outlets-in-cyberspace-or-internet-technology-image376306756.html
The word dark web on wooden cube with computer keyboard against black background. Cyber crime and illegal outlets in cyberspace or internet technology Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-word-dark-web-on-wooden-cube-with-computer-keyboard-against-black-background-cyber-crime-and-illegal-outlets-in-cyberspace-or-internet-technology-image376306756.htmlRF2CT6730–The word dark web on wooden cube with computer keyboard against black background. Cyber crime and illegal outlets in cyberspace or internet technology
 A silky spider web in front of a blurred rain forest view. Beautiful Nature concept. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-silky-spider-web-in-front-of-a-blurred-rain-forest-view-beautiful-nature-concept-high-quality-photo-image366259821.html
A silky spider web in front of a blurred rain forest view. Beautiful Nature concept. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-silky-spider-web-in-front-of-a-blurred-rain-forest-view-beautiful-nature-concept-high-quality-photo-image366259821.htmlRF2C7TG3W–A silky spider web in front of a blurred rain forest view. Beautiful Nature concept. High quality photo
 Spiderweb over vintage stone wall with hole Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spiderweb-over-vintage-stone-wall-with-hole-image218192372.html
Spiderweb over vintage stone wall with hole Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spiderweb-over-vintage-stone-wall-with-hole-image218192372.htmlRFPJYEGM–Spiderweb over vintage stone wall with hole
 Crew fantasy geometric abstraction of deep dark colors Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/crew-fantasy-geometric-abstraction-of-deep-dark-colors-image384964257.html
Crew fantasy geometric abstraction of deep dark colors Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/crew-fantasy-geometric-abstraction-of-deep-dark-colors-image384964257.htmlRF2DA8HRD–Crew fantasy geometric abstraction of deep dark colors
 Late night male computer hacking code in messy hotel room dark web cybercrime security breach information act credit card fraud identity theft. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/late-night-male-computer-hacking-code-in-messy-hotel-room-dark-web-cybercrime-security-breach-information-act-credit-card-fraud-identity-theft-image348672513.html
Late night male computer hacking code in messy hotel room dark web cybercrime security breach information act credit card fraud identity theft. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/late-night-male-computer-hacking-code-in-messy-hotel-room-dark-web-cybercrime-security-breach-information-act-credit-card-fraud-identity-theft-image348672513.htmlRF2B77B9N–Late night male computer hacking code in messy hotel room dark web cybercrime security breach information act credit card fraud identity theft.
 Computer hacker. Young man in black hoodie using multiple computers for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-hacker-young-man-in-black-hoodie-using-multiple-computers-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431123.html
Computer hacker. Young man in black hoodie using multiple computers for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-hacker-young-man-in-black-hoodie-using-multiple-computers-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431123.htmlRFTC50C3–Computer hacker. Young man in black hoodie using multiple computers for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security
 Hooded computer hacker working on desktop PC computer. P2P and piracy, computer virus and trojans, phishing, malware and ransomware concept with glitc Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-working-on-desktop-pc-computer-p2p-and-piracy-163539897.html
Hooded computer hacker working on desktop PC computer. P2P and piracy, computer virus and trojans, phishing, malware and ransomware concept with glitc Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-working-on-desktop-pc-computer-p2p-and-piracy-163539897.htmlRFKE1TPH–Hooded computer hacker working on desktop PC computer. P2P and piracy, computer virus and trojans, phishing, malware and ransomware concept with glitc
 Silhouette in the woods, alone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silhouette-in-the-woods-alone-173931744.html
Silhouette in the woods, alone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silhouette-in-the-woods-alone-173931744.htmlRFM2Y7M0–Silhouette in the woods, alone
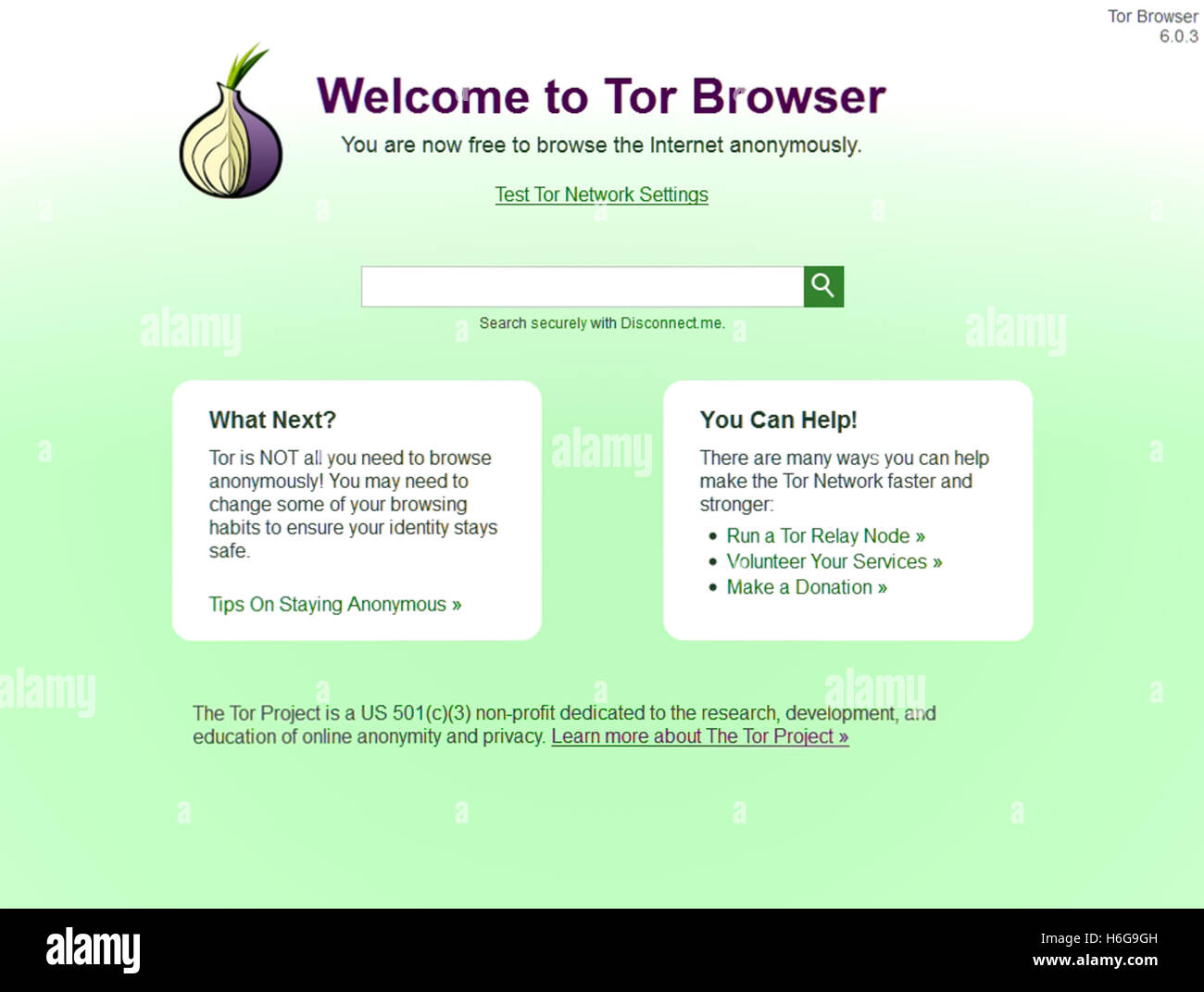 Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-start-up-screen-for-the-onion-browser-better-know-as-tor-that-allows-124519265.html
Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-start-up-screen-for-the-onion-browser-better-know-as-tor-that-allows-124519265.htmlRMH6G9GH–Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection.
 Raster abstract dark blue blurred background, smooth gradient texture color Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/raster-abstract-dark-blue-blurred-background-smooth-gradient-texture-image159261269.html
Raster abstract dark blue blurred background, smooth gradient texture color Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/raster-abstract-dark-blue-blurred-background-smooth-gradient-texture-image159261269.htmlRFK72YAD–Raster abstract dark blue blurred background, smooth gradient texture color
 deep web concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-deep-web-concept-166200170.html
deep web concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-deep-web-concept-166200170.htmlRMKJB20A–deep web concept
 Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-concept-image-of-hooded-cyber-criminal-man-using-computer-to-access-165413685.html
Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns, Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-concept-image-of-hooded-cyber-criminal-man-using-computer-to-access-165413685.htmlRMKH36RH–Concept image of Hooded cyber criminal, man using computer to access internet deep web page offering guns,
 Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599736.html
Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599736.htmlRME7MN60–Representation of the Internet 'Deep Web' on computer screen, London
 bitcoin concept coin and euro banknotes cryptocurrency impact on economy alternative currency concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bitcoin-concept-coin-and-euro-banknotes-cryptocurrency-impact-on-economy-alternative-currency-concept-image493502932.html
bitcoin concept coin and euro banknotes cryptocurrency impact on economy alternative currency concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bitcoin-concept-coin-and-euro-banknotes-cryptocurrency-impact-on-economy-alternative-currency-concept-image493502932.htmlRF2KJW00M–bitcoin concept coin and euro banknotes cryptocurrency impact on economy alternative currency concept
 Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114154.html
Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114154.htmlRMM00DA2–Crypto currency bitcoins with real money.
 Cyberspace is a deep, dark world. an unrecognizable hacker cracking a computer code in the dark. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyberspace-is-a-deep-dark-world-an-unrecognizable-hacker-cracking-a-computer-code-in-the-dark-image501580169.html
Cyberspace is a deep, dark world. an unrecognizable hacker cracking a computer code in the dark. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyberspace-is-a-deep-dark-world-an-unrecognizable-hacker-cracking-a-computer-code-in-the-dark-image501580169.htmlRF2M40XHD–Cyberspace is a deep, dark world. an unrecognizable hacker cracking a computer code in the dark.
 SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926431.html
SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926431.htmlRF2F4K2BB–SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo
 A antique key on top of the computer's keyboard. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-antique-key-on-top-of-the-computers-keyboard-image368152721.html
A antique key on top of the computer's keyboard. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-antique-key-on-top-of-the-computers-keyboard-image368152721.htmlRM2CAXPFD–A antique key on top of the computer's keyboard.
 Dark Web on a street sign with post, Storm and lightning in the background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-web-on-a-street-sign-with-post-storm-and-lightning-in-the-background-image450870490.html
Dark Web on a street sign with post, Storm and lightning in the background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-web-on-a-street-sign-with-post-storm-and-lightning-in-the-background-image450870490.htmlRM2H5EWWE–Dark Web on a street sign with post, Storm and lightning in the background
 Group of Teenage Hackers Organize Attack on Corporate Data Servers. Their Lair is Dark and Full of Operating Displays. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/group-of-teenage-hackers-organize-attack-on-corporate-data-servers-their-lair-is-dark-and-full-of-operating-displays-image177830350.html
Group of Teenage Hackers Organize Attack on Corporate Data Servers. Their Lair is Dark and Full of Operating Displays. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/group-of-teenage-hackers-organize-attack-on-corporate-data-servers-their-lair-is-dark-and-full-of-operating-displays-image177830350.htmlRFM98TBX–Group of Teenage Hackers Organize Attack on Corporate Data Servers. Their Lair is Dark and Full of Operating Displays.
 Masked Hacker is Using Computer for Organizing Massive Data Breach Attack on Corporate Servers. They're in Underground Secret Location Surrounded by Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-is-using-computer-for-organizing-massive-data-breach-attack-on-corporate-servers-theyre-in-underground-secret-location-surrounded-by-image466925069.html
Masked Hacker is Using Computer for Organizing Massive Data Breach Attack on Corporate Servers. They're in Underground Secret Location Surrounded by Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-is-using-computer-for-organizing-massive-data-breach-attack-on-corporate-servers-theyre-in-underground-secret-location-surrounded-by-image466925069.htmlRF2J3J7K9–Masked Hacker is Using Computer for Organizing Massive Data Breach Attack on Corporate Servers. They're in Underground Secret Location Surrounded by
 Spiderweb over stone wall with hole Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spiderweb-over-stone-wall-with-hole-image217862475.html
Spiderweb over stone wall with hole Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spiderweb-over-stone-wall-with-hole-image217862475.htmlRFPJCDPK–Spiderweb over stone wall with hole
 Crew fantasy geometric abstraction of deep dark black and white colors Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/crew-fantasy-geometric-abstraction-of-deep-dark-black-and-white-colors-image384964296.html
Crew fantasy geometric abstraction of deep dark black and white colors Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/crew-fantasy-geometric-abstraction-of-deep-dark-black-and-white-colors-image384964296.htmlRF2DA8HTT–Crew fantasy geometric abstraction of deep dark black and white colors
 Male computer hacker in messy hotel room. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/male-computer-hacker-in-messy-hotel-room-image348672614.html
Male computer hacker in messy hotel room. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/male-computer-hacker-in-messy-hotel-room-image348672614.htmlRF2B77BDA–Male computer hacker in messy hotel room.
 Data security. Top view of young hacker's hands stealing data while sitting in front of monitor with binary code in dark room. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-security-top-view-of-young-hackers-hands-stealing-data-while-sitting-in-front-of-monitor-with-binary-code-in-dark-room-cyber-attack-cyber-security-image248431093.html
Data security. Top view of young hacker's hands stealing data while sitting in front of monitor with binary code in dark room. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-security-top-view-of-young-hackers-hands-stealing-data-while-sitting-in-front-of-monitor-with-binary-code-in-dark-room-cyber-attack-cyber-security-image248431093.htmlRFTC50B1–Data security. Top view of young hacker's hands stealing data while sitting in front of monitor with binary code in dark room. Cyber attack. Cyber security
 Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-hacking-network-male-with-black-hoodie-using-163539871.html
Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-hacking-network-male-with-black-hoodie-using-163539871.htmlRFKE1TNK–Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity.
 Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-look-to-the-magical-forest-early-morning-with-fantasy-mood-and-fresh-breeze-in-the-north-of-bohemia-image606736542.html
Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-look-to-the-magical-forest-early-morning-with-fantasy-mood-and-fresh-breeze-in-the-north-of-bohemia-image606736542.htmlRF2X736J6–Close look to the magical forest early morning with fantasy mood and fresh breeze in the north of Bohemia.
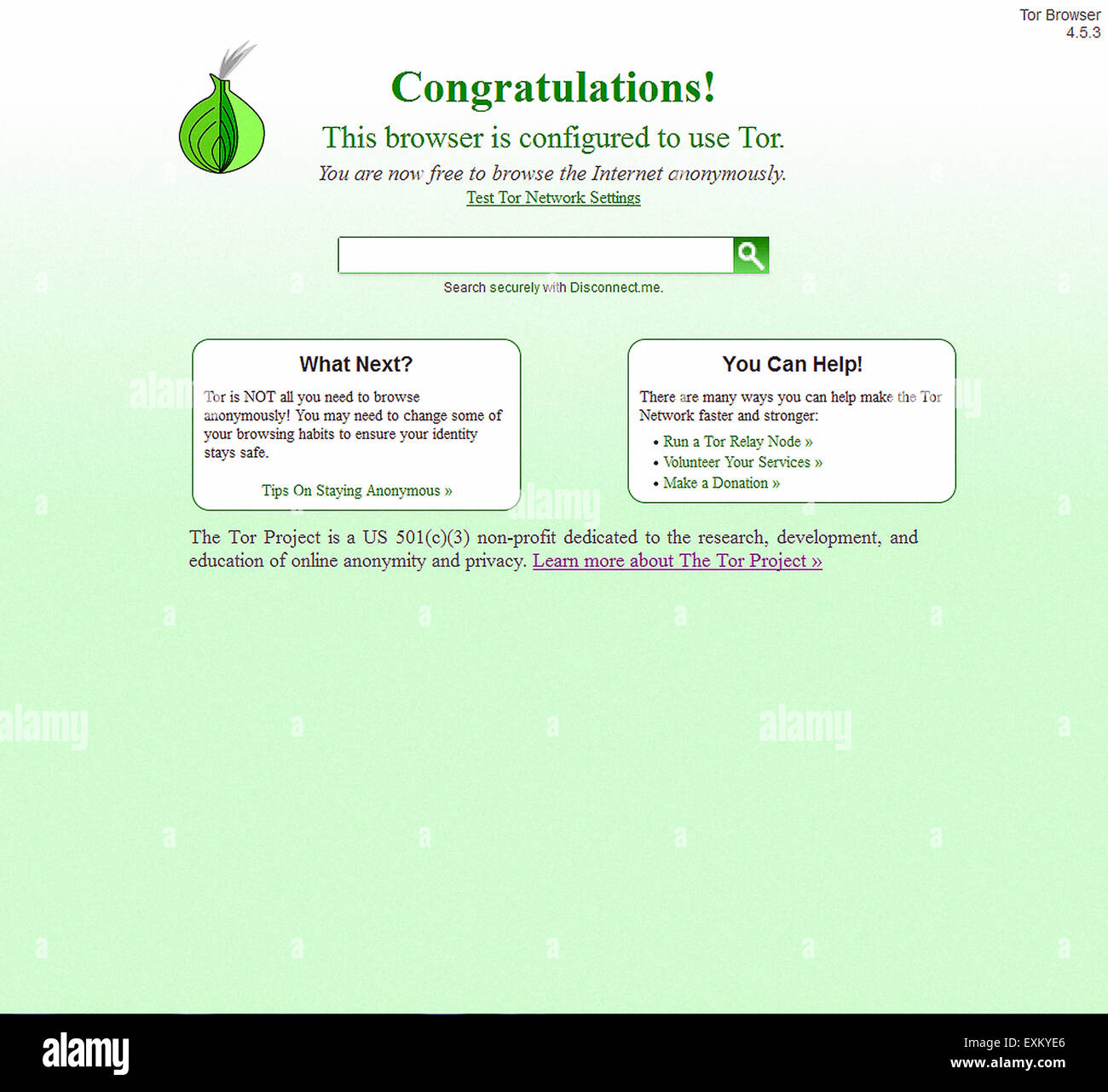 Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-start-up-screen-for-the-onion-browser-better-know-as-tor-that-allows-85261182.html
Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-start-up-screen-for-the-onion-browser-better-know-as-tor-that-allows-85261182.htmlRMEXKYE6–Start up screen for The Onion Browser, better know as 'Tor' that allows users to access the Internet anonymously. The Tor anonymity network bounces Internet traffic around a distributed network ('onion routing') of relays run around the world preventing third parties monitoring your connection.
 Image of data processing over dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-data-processing-over-dark-background-image603048423.html
Image of data processing over dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-data-processing-over-dark-background-image603048423.htmlRF2X136BK–Image of data processing over dark background
 mysterious man in hood and deep web background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-mysterious-man-in-hood-and-deep-web-background-166200158.html
mysterious man in hood and deep web background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-mysterious-man-in-hood-and-deep-web-background-166200158.htmlRMKJB1YX–mysterious man in hood and deep web background
 Dark blue broken wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-dark-blue-broken-wall-169104326.html
Dark blue broken wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-dark-blue-broken-wall-169104326.htmlRFKR3A86–Dark blue broken wall
 Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599739.html
Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599739.htmlRME7MN63–Representation of the Internet 'Deep Web' on computer screen, London
 Abstract gradient color background. Green Color mix with Dark Blue. Background color for graphic design, banner, poster. Color Trend 2023 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-gradient-color-background-green-color-mix-with-dark-blue-background-color-for-graphic-design-banner-poster-color-trend-2023-image548010192.html
Abstract gradient color background. Green Color mix with Dark Blue. Background color for graphic design, banner, poster. Color Trend 2023 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-gradient-color-background-green-color-mix-with-dark-blue-background-color-for-graphic-design-banner-poster-color-trend-2023-image548010192.htmlRF2PRG0GG–Abstract gradient color background. Green Color mix with Dark Blue. Background color for graphic design, banner, poster. Color Trend 2023
 Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114129.html
Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114129.htmlRMM00D95–Crypto currency bitcoins with real money.
 Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885556.html
Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885556.htmlRF2KG7918–Deep web phrase written with a typewriter.
 SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926428.html
SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/silk-web-in-glowing-amber-light-summer-colours-of-lesvos-deep-orange-morning-sunlight-on-a-bed-of-coniferous-leaves-creative-dark-background-photo-image415926428.htmlRF2F4K2B8–SILK WEB IN GLOWING AMBER LIGHT - Summer colours of Lesvos. Deep orange morning sunlight on a bed of coniferous leaves creative dark background. Photo
 A antique key on top of the computer's keyboard. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-antique-key-on-top-of-the-computers-keyboard-image368152665.html
A antique key on top of the computer's keyboard. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-antique-key-on-top-of-the-computers-keyboard-image368152665.htmlRM2CAXPDD–A antique key on top of the computer's keyboard.
 Dangerous hooded hacker in his hideout place which has a dark atmosphere, multiple displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-in-his-hideout-place-which-has-a-dark-atmosphere-multiple-displays-image341380911.html
Dangerous hooded hacker in his hideout place which has a dark atmosphere, multiple displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-in-his-hideout-place-which-has-a-dark-atmosphere-multiple-displays-image341380911.htmlRF2ARB6RB–Dangerous hooded hacker in his hideout place which has a dark atmosphere, multiple displays
 Team of Internationally Wanted Teenage Hackers Infect Servers and Infrastructure with Ransomware. Their Hideout is Dark, Neon Lit and Lots of displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/team-of-internationally-wanted-teenage-hackers-infect-servers-and-infrastructure-with-ransomware-their-hideout-is-dark-neon-lit-and-lots-of-displays-image177830539.html
Team of Internationally Wanted Teenage Hackers Infect Servers and Infrastructure with Ransomware. Their Hideout is Dark, Neon Lit and Lots of displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/team-of-internationally-wanted-teenage-hackers-infect-servers-and-infrastructure-with-ransomware-their-hideout-is-dark-neon-lit-and-lots-of-displays-image177830539.htmlRFM98TJK–Team of Internationally Wanted Teenage Hackers Infect Servers and Infrastructure with Ransomware. Their Hideout is Dark, Neon Lit and Lots of displays
 Dark black abstract background,backdrop Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-black-abstract-backgroundbackdrop-image368514906.html
Dark black abstract background,backdrop Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-black-abstract-backgroundbackdrop-image368514906.htmlRF2CBF8EJ–Dark black abstract background,backdrop
 Front Shot from to Hacker Breaking into Corporate Data Servers from His Underground Hideout. Place has dark atmosphere, multiple displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/front-shot-from-to-hacker-breaking-into-corporate-data-servers-from-his-underground-hideout-place-has-dark-atmosphere-multiple-displays-image466924773.html
Front Shot from to Hacker Breaking into Corporate Data Servers from His Underground Hideout. Place has dark atmosphere, multiple displays Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/front-shot-from-to-hacker-breaking-into-corporate-data-servers-from-his-underground-hideout-place-has-dark-atmosphere-multiple-displays-image466924773.htmlRF2J3J78N–Front Shot from to Hacker Breaking into Corporate Data Servers from His Underground Hideout. Place has dark atmosphere, multiple displays
 Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lilac-is-a-colour-that-is-a-pale-violet-tone-representing-the-average-colour-of-most-lilac-flowers-it-might-also-be-described-as-dark-mauve-or-light-image345724436.html
Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lilac-is-a-colour-that-is-a-pale-violet-tone-representing-the-average-colour-of-most-lilac-flowers-it-might-also-be-described-as-dark-mauve-or-light-image345724436.htmlRF2B2D318–Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light
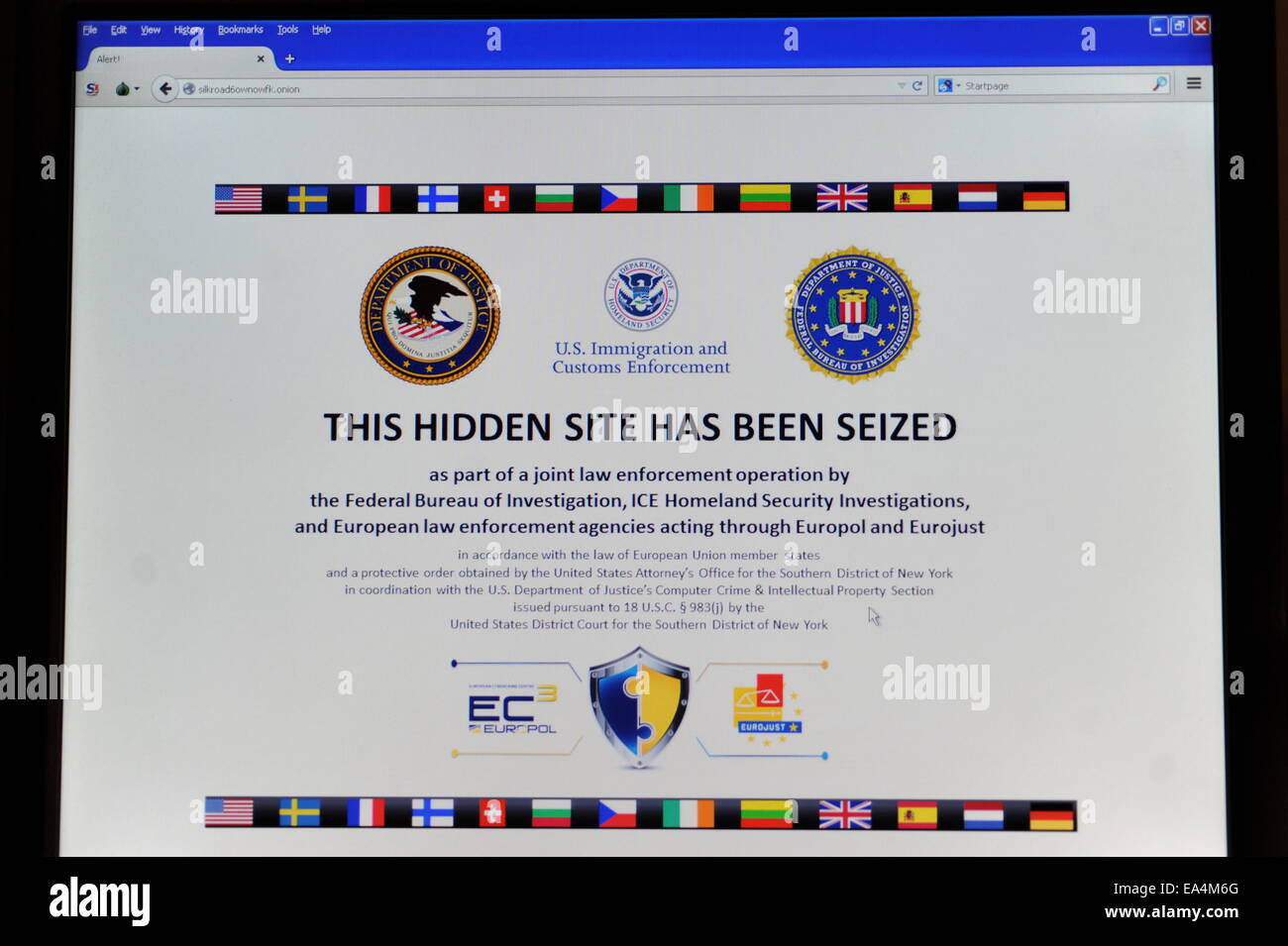 Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091704.html
Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091704.htmlRMEA4M6G–Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News
 Computer security. Young man in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-young-man-in-black-hoodie-using-multiple-computers-and-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431113.html
Computer security. Young man in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-young-man-in-black-hoodie-using-multiple-computers-and-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431113.htmlRFTC50BN–Computer security. Young man in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security
 Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-hacking-network-male-with-black-hoodie-using-163539876.html
Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hooded-computer-hacker-hacking-network-male-with-black-hoodie-using-163539876.htmlRFKE1TNT–Hooded computer hacker hacking network. Male with black hoodie using computer for identity theft or other criminal online activity.
 An abandoned spider web is cover of dew after the rain in the deep forest- dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-abandoned-spider-web-is-cover-of-dew-after-the-rain-in-the-deep-forest-dark-background-image602820230.html
An abandoned spider web is cover of dew after the rain in the deep forest- dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-abandoned-spider-web-is-cover-of-dew-after-the-rain-in-the-deep-forest-dark-background-image602820230.htmlRF2X0MR9X–An abandoned spider web is cover of dew after the rain in the deep forest- dark background
 Dark Web, Typewriter, Technology, Retrofuturism Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-web-typewriter-technology-retrofuturism-image431017743.html
Dark Web, Typewriter, Technology, Retrofuturism Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-web-typewriter-technology-retrofuturism-image431017743.htmlRM2G16FER–Dark Web, Typewriter, Technology, Retrofuturism
 Image of level up text over computer matrix on dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-level-up-text-over-computer-matrix-on-dark-background-image603104919.html
Image of level up text over computer matrix on dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-level-up-text-over-computer-matrix-on-dark-background-image603104919.htmlRF2X15PDB–Image of level up text over computer matrix on dark background
 laptop computer with a hand, palm open, coming out of the screen with a gun - concept for illegal traffic of arms in the deep web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-with-a-hand-palm-open-coming-out-of-the-screen-with-a-gun-concept-for-illegal-traffic-of-arms-in-the-deep-web-image239403717.html
laptop computer with a hand, palm open, coming out of the screen with a gun - concept for illegal traffic of arms in the deep web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-with-a-hand-palm-open-coming-out-of-the-screen-with-a-gun-concept-for-illegal-traffic-of-arms-in-the-deep-web-image239403717.htmlRMRWDNTN–laptop computer with a hand, palm open, coming out of the screen with a gun - concept for illegal traffic of arms in the deep web
 dark blue broken wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-dark-blue-broken-wall-169103472.html
dark blue broken wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-dark-blue-broken-wall-169103472.htmlRFKR395M–dark blue broken wall
 Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599737.html
Representation of the Internet 'Deep Web' on computer screen, London Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-representation-of-the-internet-deep-web-on-computer-screen-london-73599737.htmlRME7MN61–Representation of the Internet 'Deep Web' on computer screen, London
 Laptop computer displaying the warning sign of the dark web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-displaying-the-warning-sign-of-the-dark-web-image520593193.html
Laptop computer displaying the warning sign of the dark web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-displaying-the-warning-sign-of-the-dark-web-image520593193.htmlRF2N6Y1X1–Laptop computer displaying the warning sign of the dark web
 Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172113983.html
Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172113983.htmlRMM00D3Y–Crypto currency bitcoins with real money.
 Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885518.html
Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885518.htmlRF2KG78YX–Deep web phrase written with a typewriter.
 Morning light in dark autumn forest with wonderful orange leafs Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/morning-light-in-dark-autumn-forest-with-wonderful-orange-leafs-image352107031.html
Morning light in dark autumn forest with wonderful orange leafs Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/morning-light-in-dark-autumn-forest-with-wonderful-orange-leafs-image352107031.htmlRF2BCRT33–Morning light in dark autumn forest with wonderful orange leafs
 Dark mood and dark web, hackers surfing in deep web to find and steal NFT, neon light and flare effect Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-mood-and-dark-web-hackers-surfing-in-deep-web-to-find-and-steal-nft-neon-light-and-flare-effect-image503423719.html
Dark mood and dark web, hackers surfing in deep web to find and steal NFT, neon light and flare effect Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dark-mood-and-dark-web-hackers-surfing-in-deep-web-to-find-and-steal-nft-neon-light-and-flare-effect-image503423719.htmlRF2M70X2F–Dark mood and dark web, hackers surfing in deep web to find and steal NFT, neon light and flare effect
 Abstract red spotlight background with dark vignettes. Bright and vivid red texture, for web and design background templates Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-red-spotlight-background-with-dark-vignettes-bright-and-vivid-red-texture-for-web-and-design-background-templates-image364087651.html
Abstract red spotlight background with dark vignettes. Bright and vivid red texture, for web and design background templates Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-red-spotlight-background-with-dark-vignettes-bright-and-vivid-red-texture-for-web-and-design-background-templates-image364087651.htmlRF2C49HEB–Abstract red spotlight background with dark vignettes. Bright and vivid red texture, for web and design background templates
 Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-breaks-into-government-data-servers-and-infects-their-system-with-a-virus-his-hideout-place-has-dark-atmosphere-image177830456.html
Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-breaks-into-government-data-servers-and-infects-their-system-with-a-virus-his-hideout-place-has-dark-atmosphere-image177830456.htmlRFM98TFM–Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere.
 Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/grunge-graffiti-depicting-the-ctrl-key-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-web-hackers-image358151322.html
Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/grunge-graffiti-depicting-the-ctrl-key-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-web-hackers-image358151322.htmlRF2BPK5JJ–Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers
 Criminal team Hacker using computer for organizing massive data breach attack on government and big company servers. Dark room surrounded computers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/criminal-team-hacker-using-computer-for-organizing-massive-data-breach-attack-on-government-and-big-company-servers-dark-room-surrounded-computers-image469222616.html
Criminal team Hacker using computer for organizing massive data breach attack on government and big company servers. Dark room surrounded computers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/criminal-team-hacker-using-computer-for-organizing-massive-data-breach-attack-on-government-and-big-company-servers-dark-room-surrounded-computers-image469222616.htmlRF2J7AX6G–Criminal team Hacker using computer for organizing massive data breach attack on government and big company servers. Dark room surrounded computers
 Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lilac-is-a-colour-that-is-a-pale-violet-tone-representing-the-average-colour-of-most-lilac-flowers-it-might-also-be-described-as-dark-mauve-or-light-image345724532.html
Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lilac-is-a-colour-that-is-a-pale-violet-tone-representing-the-average-colour-of-most-lilac-flowers-it-might-also-be-described-as-dark-mauve-or-light-image345724532.htmlRF2B2D34M–Lilac is a colour that is a pale violet tone representing the average colour of most lilac flowers. It might also be described as dark mauve or light
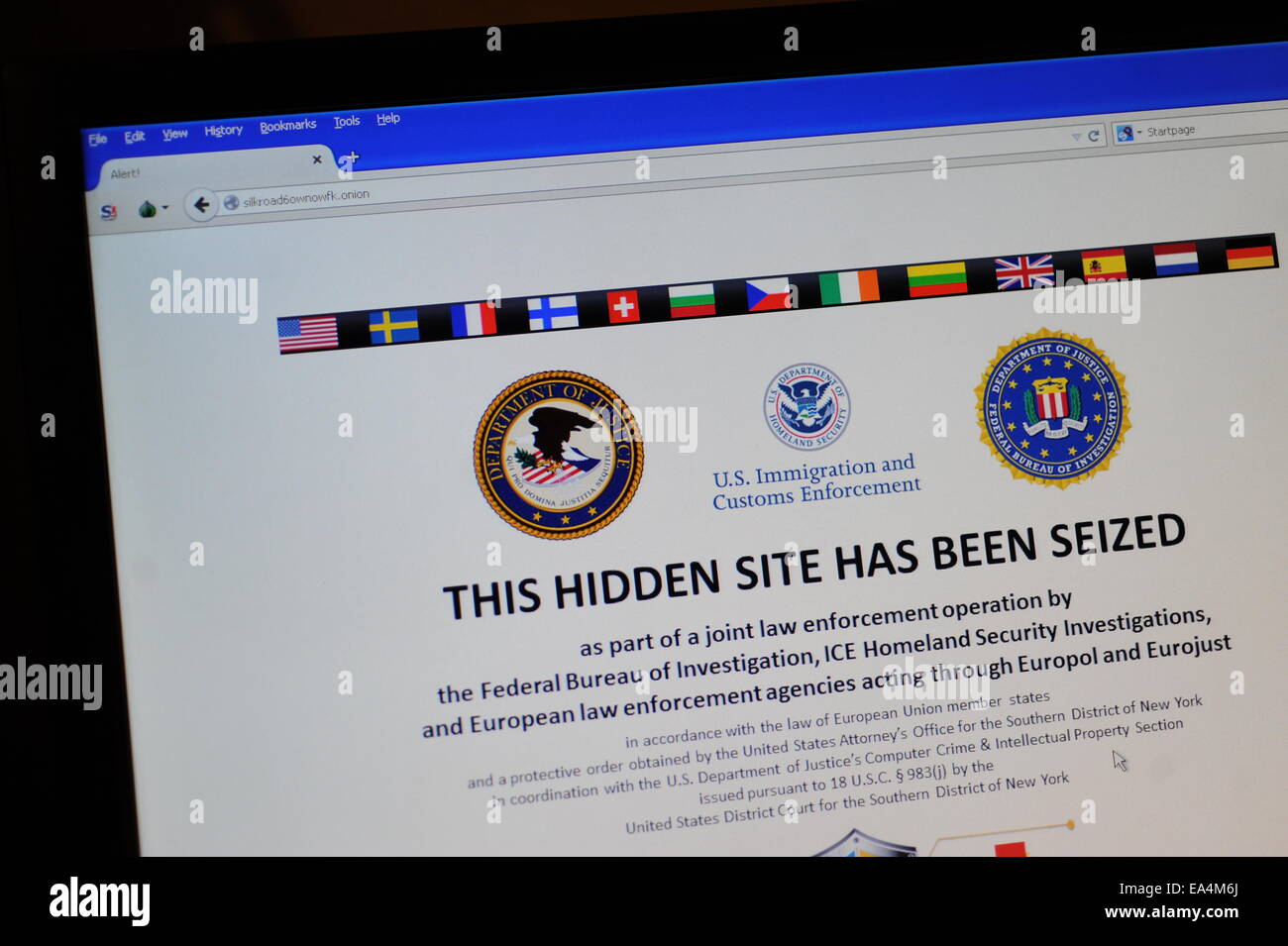 Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091706.html
Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091706.htmlRMEA4M6J–Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News
 Professional Hacker. Close-up photo of young hacker in black hoodie using his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/professional-hacker-close-up-photo-of-young-hacker-in-black-hoodie-using-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431099.html
Professional Hacker. Close-up photo of young hacker in black hoodie using his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/professional-hacker-close-up-photo-of-young-hacker-in-black-hoodie-using-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431099.htmlRFTC50B7–Professional Hacker. Close-up photo of young hacker in black hoodie using his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security
 Deep web hacking concept with faceless hooded male person, low key red and blue lit image and digital glitch effect Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-hacking-concept-with-faceless-hooded-male-person-low-key-red-and-blue-lit-image-and-digital-glitch-effect-image180214441.html
Deep web hacking concept with faceless hooded male person, low key red and blue lit image and digital glitch effect Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-hacking-concept-with-faceless-hooded-male-person-low-key-red-and-blue-lit-image-and-digital-glitch-effect-image180214441.htmlRFMD5DA1–Deep web hacking concept with faceless hooded male person, low key red and blue lit image and digital glitch effect
 Bearded man hacking internet web sites working on computer with multiple screens. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bearded-man-hacking-internet-web-sites-working-on-computer-with-multiple-screens-image353561419.html
Bearded man hacking internet web sites working on computer with multiple screens. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bearded-man-hacking-internet-web-sites-working-on-computer-with-multiple-screens-image353561419.htmlRF2BF635F–Bearded man hacking internet web sites working on computer with multiple screens.
 Ctrl key grungy graffiti. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep and dark web. Hackers. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ctrl-key-grungy-graffiti-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-and-dark-web-hackers-image459687462.html
Ctrl key grungy graffiti. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep and dark web. Hackers. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ctrl-key-grungy-graffiti-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-and-dark-web-hackers-image459687462.htmlRF2HKTG1A–Ctrl key grungy graffiti. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep and dark web. Hackers.
 Image of 6g text and data processing on dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-6g-text-and-data-processing-on-dark-background-image603150036.html
Image of 6g text and data processing on dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-6g-text-and-data-processing-on-dark-background-image603150036.htmlRF2X17T0M–Image of 6g text and data processing on dark background
 hacker in action in the dark Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-in-action-in-the-dark-108658404.html
hacker in action in the dark Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-hacker-in-action-in-the-dark-108658404.htmlRFG8NPW8–hacker in action in the dark
 Drops of dew on a web shined by morning light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drops-of-dew-on-a-web-shined-by-morning-light-168905814.html
Drops of dew on a web shined by morning light Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drops-of-dew-on-a-web-shined-by-morning-light-168905814.htmlRFKPP92E–Drops of dew on a web shined by morning light
 Online instructions for gaining access to black market Deep Web site Silk Road retailing Class A drugs Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/online-instructions-for-gaining-access-to-black-market-deep-web-site-image60994491.html
Online instructions for gaining access to black market Deep Web site Silk Road retailing Class A drugs Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/online-instructions-for-gaining-access-to-black-market-deep-web-site-image60994491.htmlRMDF6F2K–Online instructions for gaining access to black market Deep Web site Silk Road retailing Class A drugs
 Laptop computer displaying the warning sign of the dark web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-displaying-the-warning-sign-of-the-dark-web-image520593224.html
Laptop computer displaying the warning sign of the dark web Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-computer-displaying-the-warning-sign-of-the-dark-web-image520593224.htmlRF2N6Y1Y4–Laptop computer displaying the warning sign of the dark web
 Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114113.html
Crypto currency bitcoins with real money. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-crypto-currency-bitcoins-with-real-money-172114113.htmlRMM00D8H–Crypto currency bitcoins with real money.
 Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885500.html
Deep web phrase written with a typewriter. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/deep-web-phrase-written-with-a-typewriter-image491885500.htmlRF2KG78Y8–Deep web phrase written with a typewriter.
 Reddit app smartphone reddit logo screen background . Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reddit-app-smartphone-reddit-logo-screen-background-image369753616.html
Reddit app smartphone reddit logo screen background . Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/reddit-app-smartphone-reddit-logo-screen-background-image369753616.htmlRF2CDFME8–Reddit app smartphone reddit logo screen background .
 Amir Taaki, creator of Dark wallet is filmed by Alex Winter for upcoming movie Deep Web: The Untold Story of Bitcoin and The Silk Road Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-amir-taaki-creator-of-dark-wallet-is-filmed-by-alex-winter-for-upcoming-73810109.html
Amir Taaki, creator of Dark wallet is filmed by Alex Winter for upcoming movie Deep Web: The Untold Story of Bitcoin and The Silk Road Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-amir-taaki-creator-of-dark-wallet-is-filmed-by-alex-winter-for-upcoming-73810109.htmlRME829F9–Amir Taaki, creator of Dark wallet is filmed by Alex Winter for upcoming movie Deep Web: The Untold Story of Bitcoin and The Silk Road
 Hooded hacker sitting behind laptop against dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hooded-hacker-sitting-behind-laptop-against-dark-background-image456155983.html
Hooded hacker sitting behind laptop against dark background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hooded-hacker-sitting-behind-laptop-against-dark-background-image456155983.htmlRF2HE3KH3–Hooded hacker sitting behind laptop against dark background
 Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-breaks-into-government-data-servers-and-infects-their-system-with-a-virus-his-hideout-place-has-dark-atmosphere-image177830524.html
Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dangerous-hooded-hacker-breaks-into-government-data-servers-and-infects-their-system-with-a-virus-his-hideout-place-has-dark-atmosphere-image177830524.htmlRFM98TJ4–Dangerous Hooded Hacker Breaks into Government Data Servers and Infects Their System with a Virus. His Hideout Place has Dark Atmosphere
 Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/grunge-graffiti-depicting-the-ctrl-key-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-web-hackers-image362908853.html
Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/grunge-graffiti-depicting-the-ctrl-key-ideal-for-creative-backgrounds-computer-based-concepts-it-piracy-deep-web-hackers-image362908853.htmlRF2C2BWXD–Grunge graffiti depicting the Ctrl key. Ideal for creative backgrounds computer-based concepts. IT piracy. Deep web. Hackers
 Exquisite dark textile background for your imagine. Can be used for web templates, artworks. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/exquisite-dark-textile-background-for-your-imagine-can-be-used-for-web-templates-artworks-image327463360.html
Exquisite dark textile background for your imagine. Can be used for web templates, artworks. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/exquisite-dark-textile-background-for-your-imagine-can-be-used-for-web-templates-artworks-image327463360.htmlRF2A0N6T0–Exquisite dark textile background for your imagine. Can be used for web templates, artworks.
RF2A8WFRT–Darknet inscription in glithched style over dark pixelated background
 Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091712.html
Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silk-road-version-20-the-resurrected-marketplace-for-the-trade-of-75091712.htmlRMEA4M6T–Silk Road version 2.0, the resurrected marketplace for the trade of illegal drugs and contraband goods on the internet has been closed by the US authorities a second time. An arrest of a 26 year old, alleged operator of the site, in San Fransico, sparked an investigation and the appearance of a takedown notice from the FBI and Europol. This follows a similar arrest and takedown last year. Screengrab of Silk Road takedown notice. Thursday 6th November 2014. Credit: David Colbran/Alamy Live News
 Cyber crime. Side view of young hacker in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-side-view-of-young-hacker-in-black-hoodie-using-multiple-computers-and-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431109.html
Cyber crime. Side view of young hacker in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-side-view-of-young-hacker-in-black-hoodie-using-multiple-computers-and-his-smartphone-for-stealing-data-while-sitting-in-dark-room-binary-code-cyber-attack-cyber-security-image248431109.htmlRFTC50BH–Cyber crime. Side view of young hacker in black hoodie using multiple computers and his smartphone for stealing data while sitting in dark room. Binary code. Cyber attack. Cyber security
 abstract dark blue, purple blurred background, smooth gradient texture color. abstract purple graphic art image Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-dark-blue-purple-blurred-background-smooth-gradient-texture-color-abstract-purple-graphic-art-image-image344220745.html
abstract dark blue, purple blurred background, smooth gradient texture color. abstract purple graphic art image Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/abstract-dark-blue-purple-blurred-background-smooth-gradient-texture-color-abstract-purple-graphic-art-image-image344220745.htmlRF2B00H21–abstract dark blue, purple blurred background, smooth gradient texture color. abstract purple graphic art image
 A deep purple sunset with dark clouds in the morning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-deep-purple-sunset-with-dark-clouds-in-the-morning-image392494631.html
A deep purple sunset with dark clouds in the morning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-deep-purple-sunset-with-dark-clouds-in-the-morning-image392494631.htmlRF2DPFJWB–A deep purple sunset with dark clouds in the morning
 Lost stone bridge covered by the forest and stream Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lost-stone-bridge-covered-by-the-forest-and-stream-image419312697.html
Lost stone bridge covered by the forest and stream Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lost-stone-bridge-covered-by-the-forest-and-stream-image419312697.htmlRF2FA59HD–Lost stone bridge covered by the forest and stream
 the gun's barrel breaks the laptop screen and passes through it. Low key, front view Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-guns-barrel-breaks-the-laptop-screen-and-passes-through-it-low-55040937.html
the gun's barrel breaks the laptop screen and passes through it. Low key, front view Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-guns-barrel-breaks-the-laptop-screen-and-passes-through-it-low-55040937.htmlRMD5F97N–the gun's barrel breaks the laptop screen and passes through it. Low key, front view
 hacker wearing a hoodie in front of a computer code background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-wearing-a-hoodie-in-front-of-a-computer-code-background-image158719500.html
hacker wearing a hoodie in front of a computer code background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-wearing-a-hoodie-in-front-of-a-computer-code-background-image158719500.htmlRMK6689G–hacker wearing a hoodie in front of a computer code background
Search Results for Deep dark web Stock Photos and Images (5,941)
Page 1 of 60

