Page 1 of 52
Cyber cyberattack Stock Photos and Images
RF2DEKKM1–Hand holding smartphone that the system being locked by ransomware, showing on screen - cyber attack concept
RF2A9CJRN–Global cyber attack around the world with planet Earth viewed from space and internet network communication under cyberattack with red icons, worldwid

RF2JEW6RE–Cyberattack on computer screen. Cyber attack, security breach and russian hacker abstract concept 3d with glitch effect. Man typing keyboard.
RF2PYFEYE–Handwriting text Cyber Resilience. Word for measure of how well an enterprise can manage a cyberattack
RM2PPMM72–Sign displaying Cyber Resilience. Business showcase measure of how well an enterprise can manage a cyberattack
RFJGGRJH–Fake Dictionary, Dictionary definition of the word cyber-attack. including key descriptive words.

RF2HBG7RG–Cyberattack concept, hooded computer hacker working on laptop, glitch effect added in post, selective focus

RF2WJHHWD–Cyber security concept. System hacked warning alerts on a computer notebook screen. Cybercrime, virus, online hacking, cyber attack, malicious malware
RF2T7F7G2–Coder or hacker. Data programmer, developer or engineer in office. Cyber crime security software for fraud and theft online.
RF2WBREPY–Woman use smartphone with cyberattack window hologram interface. Cyber crime concept. Hacker attack.

RF2HEYDM3–System hacked alert after cyber attack on computer network. Cybersecurity vulnerability, data breach, illegal connection, compromised information conc
RF2JEW6T5–Cyberattack on computer screen. Cyber attack, security breach and russian hacker abstract concept 3d with glitch effect. Man typing keyboard.

RF2PY84P1–Sign displaying Cyber Resilience. Word for measure of how well an enterprise can manage a cyberattack

RM2PPJTM6–Sign displaying Cyber Resilience. Business overview measure of how well an enterprise can manage a cyberattack
RFJGGRJE–Fake Dictionary, Dictionary definition of the word cyber-attack. including key descriptive words.

RFPE2T6B–internet network security concept, business man touching lock on virtual screen, protection against cyberattack

RF2KFRKBC–Internet crime. Hacker hand reach through laptop screen for stealing data. Cyber attack, virus, malware, illegally and cyber security. colorful bright

RFM98TEJ–Cyber War Special Forces Fully Armed Soldier Uncovers Internationally Wanted Hacker's Hideout Place. Lair is Full of Monitors, Cables and Has Neon.
RM2WN042A–Symbolic image hacker, cyberattack on public buildings, administrations, institutions, transportation infrastructure, digital extortion, data theft, o

RF2WJHHWK–Cyber security concept. System hacked warning alerts on a computer notebook screen. Cybercrime, virus, online hacking, cyber attack, malicious malware
RF2T2FYM3–Hacker with malware code in computer screen. Cybersecurity, privacy or cyber attack. Programmer or fraud criminal writing virus software.

RF2K4E42A–Woman using laptop with digital warning pop up of cyberattack. Cyber crime concept. Cyber security data protection business technology.
RFR1P10H–Security breach, system hacked, internet cyber attack alert with red broken padlock icon showing unsecured data, vulnerable access, compromised passwo
RF2JEW67W–Cyberattack on computer screen. Cyber attack, security breach and russian hacker abstract concept 3d with glitch effect. Man typing keyboard.

RF2PY8DMP–Conceptual caption Cyber Resilience. Word for measure of how well an enterprise can manage a cyberattack
RM2PPKB43–Conceptual caption Cyber Resilience. Word Written on measure of how well an enterprise can manage a cyberattack
RFJGGRJN–Fake Dictionary, Dictionary definition of the word cyber-attack. including key descriptive words.

RFPYTTGR–hacker attack and data breach, information leak concept, futuristic cyber background with broken lock

RF2F1K5GG–Mobile phone with logo of US cyber security company CrowdStrike Holdings Inc. on screen in front of web page. Focus on center-left of phone display.

RFM98TEP–Cyber War Special Forces Fully Armed Soldier Uncovers Internationally Wanted Hacker's Hideout Place. Lair is Full of Monitors, Cables and Has Neon.
RM2WN042C–Symbolic image hacker, cyberattack on public buildings, administrations, institutions, transportation infrastructure, digital extortion, data theft, o

RFMD5D9A–Cyberattack concept with faceless hooded male person using tablet computer, low key red and blue lit image and digital glitch effect
RF2WJHHWE–Cyber security concept. Red system hacked warning sign alerts on a computer notebook screen. Cybercrime, virus, online hacking, cyber attack, maliciou
RF2T577T8–Hacker or code developer with laptop. Malware, game or website developing. Cyber criminal, programmer, engineer or coder. Fraud software or privacy.
RFR193PW–Security breach, system hacked alert with red broken padlock icon showing unsecure data under cyberattack, vulnerable access, compromised password, vi

RF2JEW6PN–Cyberattack on computer screen. Cyber attack, security breach and russian hacker abstract concept 3d with glitch effect. Man typing keyboard.

RF2PY933B–Conceptual display Cyber Resilience. Word for measure of how well an enterprise can manage a cyberattack
RM2PPJ8XK–Text caption presenting Cyber Resilience. Business approach measure of how well an enterprise can manage a cyberattack
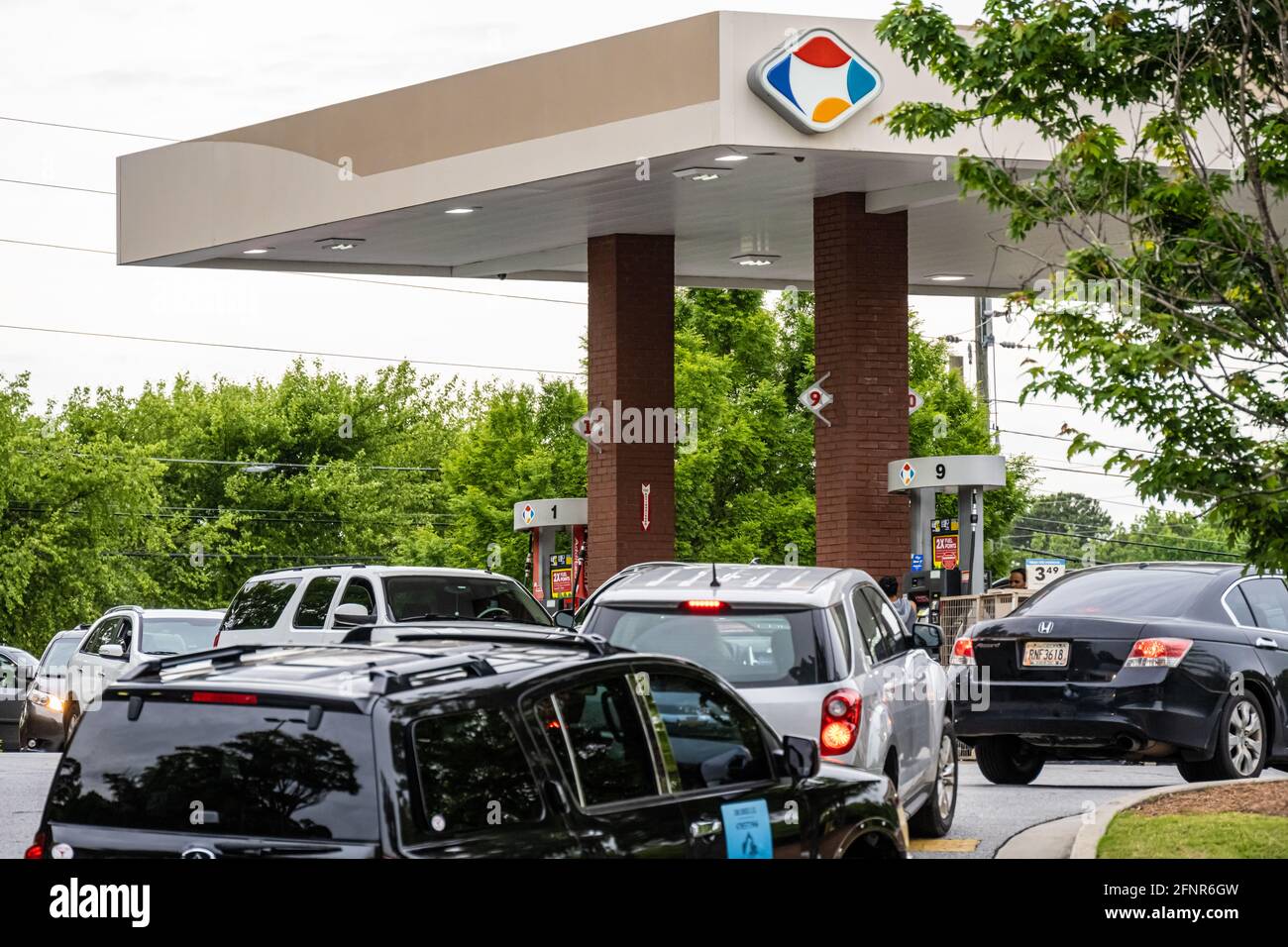
RM2FNR6GW–Fuel shortage creates long snaking lines at a Kroger gas station in Metro Atlanta, Georgia. (USA)

RF2C77M4M–Poland hacked state security. Cyberattack on the financial and banking structure. Theft of secret information. On a background of a flag the binary code.

RM2AYC5AX–Word writing text Cyber Warfare. Business concept for Virtual War Hackers System Attacks Digital Thief Stalker White pc keyboard

RFM98TEY–Cyber War Special Forces Fully Armed Soldier Uncovers Internationally Wanted Hacker's Hideout Place. Lair is Full of Monitors, Cables and Has Neon.

RM2WN041J–Symbolic image hacker, cyberattack on public buildings, administrations, institutions, town hall, authorities, digital blackmail, data theft, online c

RMR2M7WY–Polish Minister of the Interior and Administration Mariusz Blaszczak during the press conference about ransomware Petya cyberattack in Poland, at Chancellery of the Prime Minister in Warsaw, Poland on 28 June 2017

RFMCC110–Portrait of young dangerous hooded hacker in black hoodie looking at camera posing with code on monitors at background, stealing information, cyber se

RF2HEYDM8–System hacked alert after cyber attack on computer network. Cybersecurity vulnerability on internet, virus, data breach, malicious connection. Employe
RF2PY7T09–Conceptual display Cyber Resilience. Concept meaning measure of how well an enterprise can manage a cyberattack
RM2PPJWGW–Inspiration showing sign Cyber Resilience. Word Written on measure of how well an enterprise can manage a cyberattack

RF2TB4JP5–Incident response - organized approach to addressing and managing the aftermath of a security breach or cyberattack, text concept on notepad

RF2A1NPA8–Indonesia hacked state security. Cyberattack on the financial and banking structure. Theft of secret information. On a background of a flag the binary code.

RF2WA3M49–System hacked warning alert, Cyberattack computer network, Cybersecurity, Notification error maintenance, Virus cybercrime, Identity theft, Data
RF2K5X988–Hand on the keyboard with Russian layout. The concept of information protection, cyber attacks. The concept of work from home, business, online shopping.
RFERPK20–Close up of hand, focus on locking device, holding computer lock with keyboard in background.
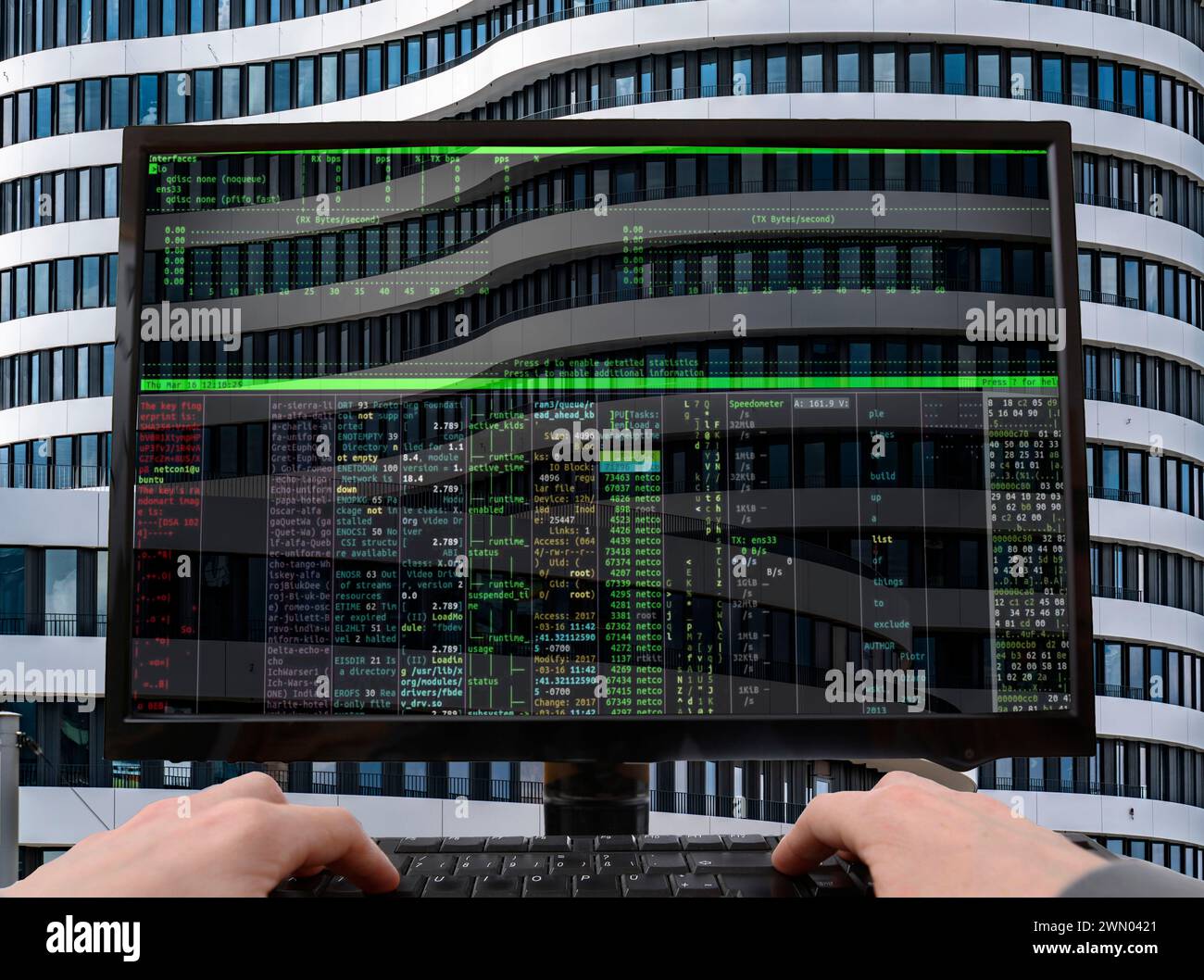
RM2WN0421–Symbolic image hacker, cyberattack on public buildings, administrations, institutions, town hall, authorities, digital blackmail, data theft, online c
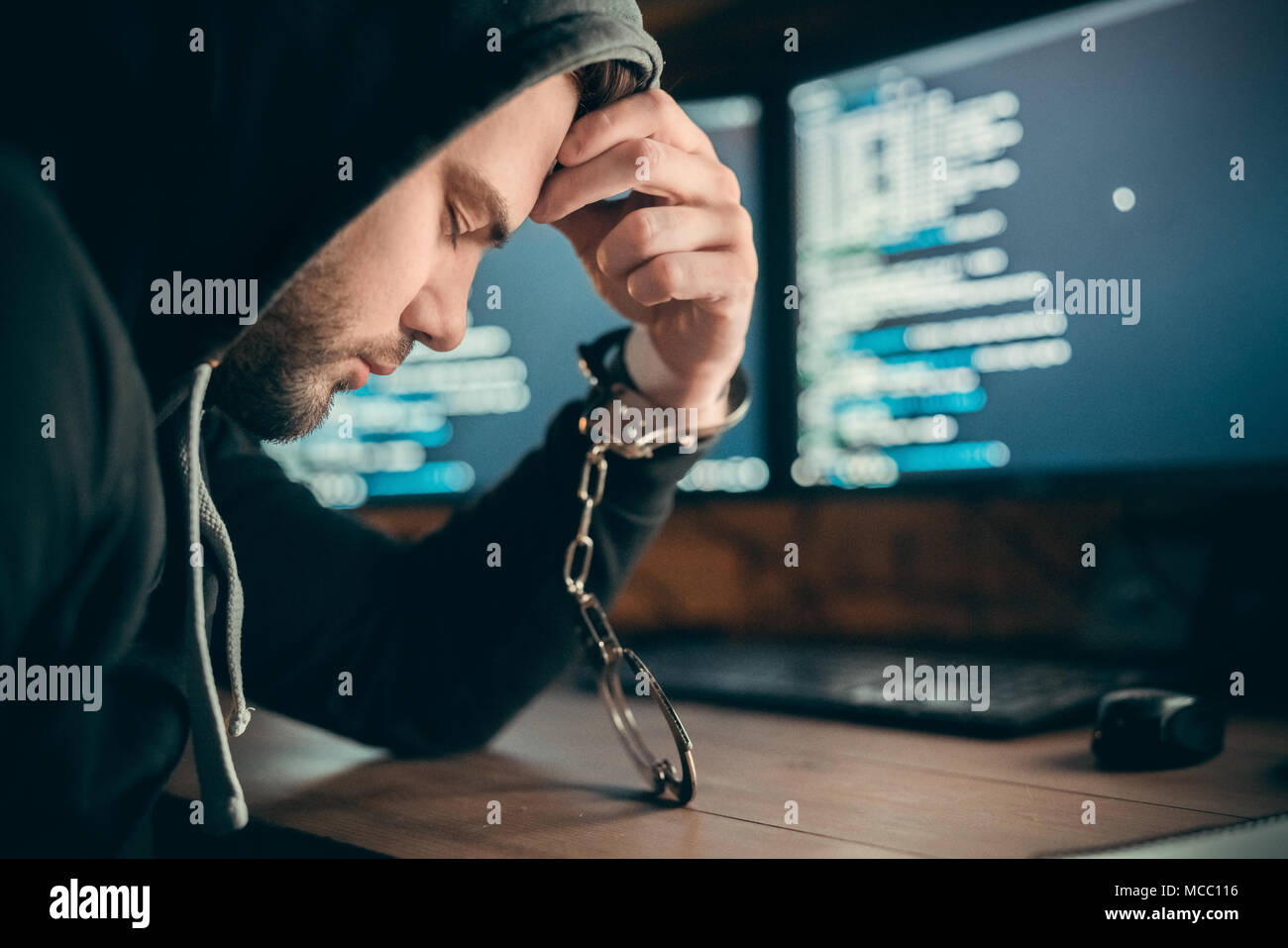
RFMCC116–Arrested upset hacker or sad internet criminal got caught to be imprisoned sitting with hand in handcuffs on computer code background, cyber crime law

RF2RAJ3BJ–Cyber security protecting network against cyberattack from hackers on internet. Secure access.
RF2K8F6AR–Laptop keyboard with warning of cyberattack on buttons. Cyber crime concept. Cyber security data protection business technology.

RF2HMCW45–System hacked alert on computer screen after cyber attack on network. Cybersecurity vulnerability on internet, virus, data breach, malicious connectio
Search Results for Cyber cyberattack Stock Photos and Images (5,169)
Page 1 of 52