Page 1 of 4
Cyber attack data breach Cut Out Stock Images
 Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/capital-one-bank-logo-on-the-background-screen-and-a-silhouette-of-the-opened-lock-in-front-conceptual-photo-for-news-about-the-data-breach-image262218160.html
Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/capital-one-bank-logo-on-the-background-screen-and-a-silhouette-of-the-opened-lock-in-front-conceptual-photo-for-news-about-the-data-breach-image262218160.htmlRFW6H1X8–Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach.
 Cyber Security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-cyber-security-163424628.html
Cyber Security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-cyber-security-163424628.htmlRFKDTHNT–Cyber Security
 Text sign showing Data Breach. Internet Concept security incident where sensitive protected information copied Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-data-breach-internet-concept-security-incident-where-sensitive-protected-information-copied-image548222297.html
Text sign showing Data Breach. Internet Concept security incident where sensitive protected information copied Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-data-breach-internet-concept-security-incident-where-sensitive-protected-information-copied-image548222297.htmlRF2PRWK3N–Text sign showing Data Breach. Internet Concept security incident where sensitive protected information copied
 Locked Keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-locked-keyboard-163424633.html
Locked Keyboard Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-locked-keyboard-163424633.htmlRFKDTHP1–Locked Keyboard
 Hexadecimal random numbers on a transparent background. Symbolic for data, crypto, fraud and hacking. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hexadecimal-random-numbers-on-a-transparent-background-symbolic-for-data-crypto-fraud-and-hacking-image594329101.html
Hexadecimal random numbers on a transparent background. Symbolic for data, crypto, fraud and hacking. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hexadecimal-random-numbers-on-a-transparent-background-symbolic-for-data-crypto-fraud-and-hacking-image594329101.htmlRF2WEX0R9–Hexadecimal random numbers on a transparent background. Symbolic for data, crypto, fraud and hacking.
 Keyboard Locked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-keyboard-locked-163424629.html
Keyboard Locked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-keyboard-locked-163424629.htmlRFKDTHNW–Keyboard Locked
 Internet privacy concept. Internet secure, privacy and password protection. Data Theft and Fraud as a Digital Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-privacy-concept-internet-secure-privacy-and-password-protection-144583858.html
Internet privacy concept. Internet secure, privacy and password protection. Data Theft and Fraud as a Digital Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-privacy-concept-internet-secure-privacy-and-password-protection-144583858.htmlRFJB6A56–Internet privacy concept. Internet secure, privacy and password protection. Data Theft and Fraud as a Digital Concept
 Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image431697106.html
Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image431697106.htmlRF2G29E1P–Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept
 3d rendering of a smartphone and A black padlock with a keyhole is floating on top of the center of the phone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/3d-rendering-of-a-smartphone-and-a-black-padlock-with-a-keyhole-is-floating-on-top-of-the-center-of-the-phone-image607126888.html
3d rendering of a smartphone and A black padlock with a keyhole is floating on top of the center of the phone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/3d-rendering-of-a-smartphone-and-a-black-padlock-with-a-keyhole-is-floating-on-top-of-the-center-of-the-phone-image607126888.htmlRF2X7N0F4–3d rendering of a smartphone and A black padlock with a keyhole is floating on top of the center of the phone
 CYBER ATTACK red Rubber Stamp over a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cyber-attack-red-rubber-stamp-over-a-white-background-133522736.html
CYBER ATTACK red Rubber Stamp over a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cyber-attack-red-rubber-stamp-over-a-white-background-133522736.htmlRFHN6DH4–CYBER ATTACK red Rubber Stamp over a white background.
 Data leak word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-leak-word-cloud-concept-image262841785.html
Data leak word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-leak-word-cloud-concept-image262841785.htmlRFW7HDAH–Data leak word cloud concept
 Cyber Attacks word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attacks-word-cloud-hand-sphere-concept-on-white-background-image222633670.html
Cyber Attacks word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attacks-word-cloud-hand-sphere-concept-on-white-background-image222633670.htmlRFPX5REE–Cyber Attacks word cloud hand sphere concept on white background.
 Cyber phishing. Unsecured accounts, theft account identity. Social media breach attack, hacker scam on email or data fraud utter vector concept Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-phishing-unsecured-accounts-theft-account-identity-social-media-breach-attack-hacker-scam-on-email-or-data-fraud-utter-vector-concept-image449657174.html
Cyber phishing. Unsecured accounts, theft account identity. Social media breach attack, hacker scam on email or data fraud utter vector concept Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-phishing-unsecured-accounts-theft-account-identity-social-media-breach-attack-hacker-scam-on-email-or-data-fraud-utter-vector-concept-image449657174.htmlRF2H3FJ8P–Cyber phishing. Unsecured accounts, theft account identity. Social media breach attack, hacker scam on email or data fraud utter vector concept
 Hacking activity, cybercrime flat vector illustration. Dangerous thief in mask working with computer cartoon character. Cybercriminal stealing data, cybersecurity breach, hacker attack concept Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacking-activity-cybercrime-flat-vector-illustration-dangerous-thief-in-mask-working-with-computer-cartoon-character-cybercriminal-stealing-data-cybersecurity-breach-hacker-attack-concept-image330413394.html
Hacking activity, cybercrime flat vector illustration. Dangerous thief in mask working with computer cartoon character. Cybercriminal stealing data, cybersecurity breach, hacker attack concept Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacking-activity-cybercrime-flat-vector-illustration-dangerous-thief-in-mask-working-with-computer-cartoon-character-cybercriminal-stealing-data-cybersecurity-breach-hacker-attack-concept-image330413394.htmlRF2A5FHJA–Hacking activity, cybercrime flat vector illustration. Dangerous thief in mask working with computer cartoon character. Cybercriminal stealing data, cybersecurity breach, hacker attack concept
 Cyber attack low poly art. Polygonal vector illustration of a key unlocks a lock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attack-low-poly-art-polygonal-vector-illustration-of-a-key-unlocks-a-lock-image477299042.html
Cyber attack low poly art. Polygonal vector illustration of a key unlocks a lock. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attack-low-poly-art-polygonal-vector-illustration-of-a-key-unlocks-a-lock-image477299042.htmlRF2JMERPA–Cyber attack low poly art. Polygonal vector illustration of a key unlocks a lock.
 Conceptual display Data Breach. Business showcase security incident where sensitive protected information copied Person delivering presentation displaying newest business strategies. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-data-breach-business-showcase-security-incident-where-sensitive-protected-information-copied-person-delivering-presentation-displaying-newest-business-strategies-image483699323.html
Conceptual display Data Breach. Business showcase security incident where sensitive protected information copied Person delivering presentation displaying newest business strategies. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-data-breach-business-showcase-security-incident-where-sensitive-protected-information-copied-person-delivering-presentation-displaying-newest-business-strategies-image483699323.htmlRF2K2XBBR–Conceptual display Data Breach. Business showcase security incident where sensitive protected information copied Person delivering presentation displaying newest business strategies.
RF2JP7P40–data breach line icon, outline symbol, vector illustration, concept sign
 Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image548932812.html
Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image548932812.htmlRF2PW21B8–Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something
RF2HNEKC8–Data leak Simple vector icon. Illustration symbol design template for web mobile UI element.
 Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/capital-one-bank-logo-on-the-background-screen-and-a-silhouette-of-the-opened-lock-in-front-conceptual-photo-for-news-about-the-data-breach-image262043383.html
Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/capital-one-bank-logo-on-the-background-screen-and-a-silhouette-of-the-opened-lock-in-front-conceptual-photo-for-news-about-the-data-breach-image262043383.htmlRFW69307–Capital One Bank logo on the background screen and a silhouette of the opened lock in front. Conceptual photo for news about the data breach.
RF2HNA0AJ–Data leak Simple vector icon. Illustration symbol design template for web mobile UI element.
RFR27W4M–Banner cyber security and brech data web icon application, attack, hacker, disaster, access
 Log4Shell cyber attack concept. Log4J security vulnerability.The code is red, a computer virus infection through the network. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4shell-cyber-attack-concept-log4j-security-vulnerabilitythe-code-is-red-a-computer-virus-infection-through-the-network-image455567665.html
Log4Shell cyber attack concept. Log4J security vulnerability.The code is red, a computer virus infection through the network. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4shell-cyber-attack-concept-log4j-security-vulnerabilitythe-code-is-red-a-computer-virus-infection-through-the-network-image455567665.htmlRF2HD4W5N–Log4Shell cyber attack concept. Log4J security vulnerability.The code is red, a computer virus infection through the network.
 Cyber cloud broken data, illustration, vector on white background. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-cloud-broken-data-illustration-vector-on-white-background-image484604828.html
Cyber cloud broken data, illustration, vector on white background. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-cloud-broken-data-illustration-vector-on-white-background-image484604828.htmlRF2K4BJB8–Cyber cloud broken data, illustration, vector on white background.
 Closeup view of newspaper with headline CYBER ATTACK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack-image515242667.html
Closeup view of newspaper with headline CYBER ATTACK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack-image515242667.htmlRF2MX797R–Closeup view of newspaper with headline CYBER ATTACK
 Cyber Incident Data Attack Alert 3d Rendering Shows Hacked Networks Or Computer Security Penetration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-incident-data-attack-alert-3d-rendering-shows-hacked-networks-or-computer-security-penetration-image219221808.html
Cyber Incident Data Attack Alert 3d Rendering Shows Hacked Networks Or Computer Security Penetration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-incident-data-attack-alert-3d-rendering-shows-hacked-networks-or-computer-security-penetration-image219221808.htmlRFPMJBJ8–Cyber Incident Data Attack Alert 3d Rendering Shows Hacked Networks Or Computer Security Penetration
 Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147764.html
Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147764.htmlRF2G4KGB0–Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept
 Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-threats-cyber-crime-risk-3d-rendering-shows-criminal-data-breach-vulnerability-and-system-warning-image214617778.html
Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-threats-cyber-crime-risk-3d-rendering-shows-criminal-data-breach-vulnerability-and-system-warning-image214617778.htmlRFPD4K4J–Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning
 DATA BREACH red Rubber Stamp over a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-breach-red-rubber-stamp-over-a-white-background-133522744.html
DATA BREACH red Rubber Stamp over a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-breach-red-rubber-stamp-over-a-white-background-133522744.htmlRFHN6DHC–DATA BREACH red Rubber Stamp over a white background.
 Password breach word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/password-breach-word-cloud-concept-image262839678.html
Password breach word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/password-breach-word-cloud-concept-image262839678.htmlRFW7HAKA–Password breach word cloud concept
 Data Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-security-word-cloud-hand-sphere-concept-on-white-background-image222633802.html
Data Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-security-word-cloud-hand-sphere-concept-on-white-background-image222633802.htmlRFPX5RK6–Data Security word cloud hand sphere concept on white background.
 Data Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-law-handwritten-on-a-white-background-image352944310.html
Data Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-law-handwritten-on-a-white-background-image352944310.htmlRF2BE601X–Data Law handwritten on a white background.
 Data Encryption word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-encryption-word-cloud-hand-sphere-concept-on-white-background-image222633800.html
Data Encryption word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-encryption-word-cloud-hand-sphere-concept-on-white-background-image222633800.htmlRFPX5RK4–Data Encryption word cloud hand sphere concept on white background.
 UI redressing word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ui-redressing-word-cloud-concept-on-white-background-image357009143.html
UI redressing word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ui-redressing-word-cloud-concept-on-white-background-image357009143.htmlRF2BMR4PF–UI redressing word cloud concept on white background
 Cyber fraud word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-fraud-word-cloud-hand-sphere-concept-on-white-background-image222633674.html
Cyber fraud word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-fraud-word-cloud-hand-sphere-concept-on-white-background-image222633674.htmlRFPX5REJ–Cyber fraud word cloud hand sphere concept on white background.
 Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-threats-cyber-crime-risk-3d-rendering-shows-criminal-data-breach-vulnerability-and-system-warning-image219221641.html
Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-threats-cyber-crime-risk-3d-rendering-shows-criminal-data-breach-vulnerability-and-system-warning-image219221641.htmlRFPMJBC9–Cybersecurity Threats Cyber Crime Risk 3d Rendering Shows Criminal Data Breach Vulnerability And System Warning
 Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image548808805.html
Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image548808805.htmlRF2PTTB6D–Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something
 Data Protection word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-protection-word-cloud-hand-sphere-concept-on-white-background-image222633801.html
Data Protection word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-protection-word-cloud-hand-sphere-concept-on-white-background-image222633801.htmlRFPX5RK5–Data Protection word cloud hand sphere concept on white background.
 Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image212233283.html
Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image212233283.htmlRFP981M3–Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk
 Phishing word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phishing-word-cloud-hand-sphere-concept-on-white-background-image222635344.html
Phishing word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phishing-word-cloud-hand-sphere-concept-on-white-background-image222635344.htmlRFPX5WJ8–Phishing word cloud hand sphere concept on white background.
 Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image219222890.html
Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image219222890.htmlRFPMJD0X–Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk
 Java problem. Log4Shell cyber attack concept. Log4J security vulnerability. The code is red, the concept of a computer virus infection over the netwo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/java-problem-log4shell-cyber-attack-concept-log4j-security-vulnerability-the-code-is-red-the-concept-of-a-computer-virus-infection-over-the-netwo-image455567680.html
Java problem. Log4Shell cyber attack concept. Log4J security vulnerability. The code is red, the concept of a computer virus infection over the netwo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/java-problem-log4shell-cyber-attack-concept-log4j-security-vulnerability-the-code-is-red-the-concept-of-a-computer-virus-infection-over-the-netwo-image455567680.htmlRF2HD4W68–Java problem. Log4Shell cyber attack concept. Log4J security vulnerability. The code is red, the concept of a computer virus infection over the netwo
 Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image219222662.html
Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-breach-system-hack-3d-rendering-shows-internet-digital-data-virtual-threat-and-vulnerability-problem-or-risk-image219222662.htmlRFPMJCMP–Cyber Security Breach System Hack 3d Rendering Shows Internet Digital Data Virtual Threat And Vulnerability Problem Or Risk
 Closeup view of newspaper with headline CYBER ATTACK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack-image515242666.html
Closeup view of newspaper with headline CYBER ATTACK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack-image515242666.htmlRF2MX797P–Closeup view of newspaper with headline CYBER ATTACK
 Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russian-hacking-election-attack-alert-3d-illustration-shows-spying-and-data-breach-online-digital-hacker-protection-against-moscow-to-protect-democra-image215185968.html
Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russian-hacking-election-attack-alert-3d-illustration-shows-spying-and-data-breach-online-digital-hacker-protection-against-moscow-to-protect-democra-image215185968.htmlRFPE2FW4–Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra
 Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147838.html
Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147838.htmlRF2G4KGDJ–Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept
 Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russian-hacking-election-attack-alert-3d-illustration-shows-spying-and-data-breach-online-digital-hacker-protection-against-moscow-to-protect-democra-image215186132.html
Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russian-hacking-election-attack-alert-3d-illustration-shows-spying-and-data-breach-online-digital-hacker-protection-against-moscow-to-protect-democra-image215186132.htmlRFPE2G30–Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democra
 Cyber criminals hacking into bank account. Cartoon hackers opening lock, carrying password and money. Hacker attack concept. Vector illustration can b Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-criminals-hacking-into-bank-account-cartoon-hackers-opening-lock-carrying-password-and-money-hacker-attack-concept-vector-illustration-can-b-image467634865.html
Cyber criminals hacking into bank account. Cartoon hackers opening lock, carrying password and money. Hacker attack concept. Vector illustration can b Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-criminals-hacking-into-bank-account-cartoon-hackers-opening-lock-carrying-password-and-money-hacker-attack-concept-vector-illustration-can-b-image467634865.htmlRF2J4PH15–Cyber criminals hacking into bank account. Cartoon hackers opening lock, carrying password and money. Hacker attack concept. Vector illustration can b
 Malware cyber security text - compromised computer security concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-cyber-security-text-compromised-computer-security-concept-word-cloud-image328513377.html
Malware cyber security text - compromised computer security concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-cyber-security-text-compromised-computer-security-concept-word-cloud-image328513377.htmlRF2A2D24H–Malware cyber security text - compromised computer security concept. Word cloud.
RF2J5FKB5–Set of vector isometric illustrations, hacker icons, computer security breach, information confidentiality, bank account hacking
 Data Protection handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-protection-handwritten-on-a-white-background-image352944308.html
Data Protection handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-protection-handwritten-on-a-white-background-image352944308.htmlRF2BE601T–Data Protection handwritten on a white background.
 Writing note showing Data Breach. Business photo showcasing security incident where sensitive protected information copied Black megaphone loudspeaker Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-note-showing-data-breach-business-photo-showcasing-security-incident-where-sensitive-protected-information-copied-black-megaphone-loudspeaker-image215565028.html
Writing note showing Data Breach. Business photo showcasing security incident where sensitive protected information copied Black megaphone loudspeaker Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-note-showing-data-breach-business-photo-showcasing-security-incident-where-sensitive-protected-information-copied-black-megaphone-loudspeaker-image215565028.htmlRFPEKRB0–Writing note showing Data Breach. Business photo showcasing security incident where sensitive protected information copied Black megaphone loudspeaker
 Click fraud word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/click-fraud-word-cloud-concept-on-white-background-image357008992.html
Click fraud word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/click-fraud-word-cloud-concept-on-white-background-image357008992.htmlRF2BMR4H4–Click fraud word cloud concept on white background
 Handwriting text writing Data Breach. Concept meaning security incident where sensitive protected information copied Megaphone loudspeaker speech bubb Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-writing-data-breach-concept-meaning-security-incident-where-sensitive-protected-information-copied-megaphone-loudspeaker-speech-bubb-image215540652.html
Handwriting text writing Data Breach. Concept meaning security incident where sensitive protected information copied Megaphone loudspeaker speech bubb Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-writing-data-breach-concept-meaning-security-incident-where-sensitive-protected-information-copied-megaphone-loudspeaker-speech-bubb-image215540652.htmlRFPEJM8C–Handwriting text writing Data Breach. Concept meaning security incident where sensitive protected information copied Megaphone loudspeaker speech bubb
 Ransomware attack concept. Hacker demands payment with locked files, showing danger of cyber threats. Secure your data urgently. Flat vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-attack-concept-hacker-demands-payment-with-locked-files-showing-danger-of-cyber-threats-secure-your-data-urgently-flat-vector-illustration-image606582033.html
Ransomware attack concept. Hacker demands payment with locked files, showing danger of cyber threats. Secure your data urgently. Flat vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-attack-concept-hacker-demands-payment-with-locked-files-showing-danger-of-cyber-threats-secure-your-data-urgently-flat-vector-illustration-image606582033.htmlRF2X6T5G1–Ransomware attack concept. Hacker demands payment with locked files, showing danger of cyber threats. Secure your data urgently. Flat vector illustration.
 Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image549066390.html
Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-caption-bank-fraud-word-for-intentional-perversion-of-truth-to-induce-another-to-part-with-something-image549066390.htmlRF2PW83NX–Conceptual caption Bank Fraud, Word for intentional perversion of truth to induce another to part with something
 Word writing text Data Breach. Business photo showcasing security incident where sensitive protected information copied Young Male Businessman Office Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/word-writing-text-data-breach-business-photo-showcasing-security-incident-where-sensitive-protected-information-copied-young-male-businessman-office-image327694313.html
Word writing text Data Breach. Business photo showcasing security incident where sensitive protected information copied Young Male Businessman Office Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/word-writing-text-data-breach-business-photo-showcasing-security-incident-where-sensitive-protected-information-copied-young-male-businessman-office-image327694313.htmlRF2A13NC9–Word writing text Data Breach. Business photo showcasing security incident where sensitive protected information copied Young Male Businessman Office
 Robot with shield. Virus protection concept. Isolated over white. Contains clipping path Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-robot-with-shield-virus-protection-concept-isolated-over-white-contains-96287046.html
Robot with shield. Virus protection concept. Isolated over white. Contains clipping path Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-robot-with-shield-virus-protection-concept-isolated-over-white-contains-96287046.htmlRFFGJ732–Robot with shield. Virus protection concept. Isolated over white. Contains clipping path
 Internet Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-security-word-cloud-hand-sphere-concept-on-white-background-image222634944.html
Internet Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-security-word-cloud-hand-sphere-concept-on-white-background-image222634944.htmlRFPX5W40–Internet Security word cloud hand sphere concept on white background.
 Writing note showing Data Breach. Business concept for incident in which sensitive or confidential data is copied Paper lines binder clip suare notebo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-note-showing-data-breach-business-concept-for-incident-in-which-sensitive-or-confidential-data-is-copied-paper-lines-binder-clip-suare-notebo-image347393958.html
Writing note showing Data Breach. Business concept for incident in which sensitive or confidential data is copied Paper lines binder clip suare notebo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-note-showing-data-breach-business-concept-for-incident-in-which-sensitive-or-confidential-data-is-copied-paper-lines-binder-clip-suare-notebo-image347393958.htmlRF2B554F2–Writing note showing Data Breach. Business concept for incident in which sensitive or confidential data is copied Paper lines binder clip suare notebo
 Email Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-security-word-cloud-hand-sphere-concept-on-white-background-image222634171.html
Email Security word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-security-word-cloud-hand-sphere-concept-on-white-background-image222634171.htmlRFPX5T4B–Email Security word cloud hand sphere concept on white background.
 Log4J illustration concept. Log4Shell security vulnerability. Data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4j-illustration-concept-log4shell-security-vulnerability-data-center-network-infection-concept-image455567670.html
Log4J illustration concept. Log4Shell security vulnerability. Data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4j-illustration-concept-log4shell-security-vulnerability-data-center-network-infection-concept-image455567670.htmlRF2HD4W5X–Log4J illustration concept. Log4Shell security vulnerability. Data center network infection concept.
 Closeup view of newspaper with headline CYBER ATTACK! Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack!-image515242656.html
Closeup view of newspaper with headline CYBER ATTACK! Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closeup-view-of-newspaper-with-headline-cyber-attack!-image515242656.htmlRF2MX797C–Closeup view of newspaper with headline CYBER ATTACK!
 Conceptual hand writing showing Data Breach. Business photo text security incident where sensitive protected information copied Cell phone receiving m Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-hand-writing-showing-data-breach-business-photo-text-security-incident-where-sensitive-protected-information-copied-cell-phone-receiving-m-image215729736.html
Conceptual hand writing showing Data Breach. Business photo text security incident where sensitive protected information copied Cell phone receiving m Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-hand-writing-showing-data-breach-business-photo-text-security-incident-where-sensitive-protected-information-copied-cell-phone-receiving-m-image215729736.htmlRFPEY9DC–Conceptual hand writing showing Data Breach. Business photo text security incident where sensitive protected information copied Cell phone receiving m
 Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147735.html
Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-laptop-computer-ransomware-malware-encrypt-and-hacking-data-security-concept-image433147735.htmlRF2G4KG9Y–Cyber crime. Internet cyber security concept with a padlock on laptop computer. Ransomware, Malware, Encrypt and Hacking. Data security concept
 Ransom Computer Hacker Data Extortion 3d Rendering Shows Ransomware Used To Attack Computer Data And Blackmail Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransom-computer-hacker-data-extortion-3d-rendering-shows-ransomware-used-to-attack-computer-data-and-blackmail-image219222386.html
Ransom Computer Hacker Data Extortion 3d Rendering Shows Ransomware Used To Attack Computer Data And Blackmail Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransom-computer-hacker-data-extortion-3d-rendering-shows-ransomware-used-to-attack-computer-data-and-blackmail-image219222386.htmlRFPMJCAX–Ransom Computer Hacker Data Extortion 3d Rendering Shows Ransomware Used To Attack Computer Data And Blackmail
 security breach with red abstract shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-with-red-abstract-shield-image343651672.html
security breach with red abstract shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-with-red-abstract-shield-image343651672.htmlRF2AY2K60–security breach with red abstract shield
 Spyware virus - computer security breach concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spyware-virus-computer-security-breach-concept-word-cloud-image337462608.html
Spyware virus - computer security breach concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spyware-virus-computer-security-breach-concept-word-cloud-image337462608.htmlRF2AH0N00–Spyware virus - computer security breach concept. Word cloud.
 Cybersecurity Hacker Online Cyber Attacks 3d Illustration Shows Digital Spying And Breach Security For Internet Protection Against Web Hacking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-hacker-online-cyber-attacks-3d-illustration-shows-digital-spying-and-breach-security-for-internet-protection-against-web-hacking-image215185953.html
Cybersecurity Hacker Online Cyber Attacks 3d Illustration Shows Digital Spying And Breach Security For Internet Protection Against Web Hacking Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cybersecurity-hacker-online-cyber-attacks-3d-illustration-shows-digital-spying-and-breach-security-for-internet-protection-against-web-hacking-image215185953.htmlRFPE2FTH–Cybersecurity Hacker Online Cyber Attacks 3d Illustration Shows Digital Spying And Breach Security For Internet Protection Against Web Hacking
 Privacy Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/privacy-law-handwritten-on-a-white-background-image352944312.html
Privacy Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/privacy-law-handwritten-on-a-white-background-image352944312.htmlRF2BE6020–Privacy Law handwritten on a white background.
 Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russia-hacking-american-elections-data-3d-illustration-shows-kremlin-spy-hackers-on-internet-attack-usa-election-security-or-cybersecurity-image215186096.html
Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russia-hacking-american-elections-data-3d-illustration-shows-kremlin-spy-hackers-on-internet-attack-usa-election-security-or-cybersecurity-image215186096.htmlRFPE2G1M–Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity
 Clickjacking word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/clickjacking-word-cloud-concept-on-white-background-image357009004.html
Clickjacking word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/clickjacking-word-cloud-concept-on-white-background-image357009004.htmlRF2BMR4HG–Clickjacking word cloud concept on white background
 Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russia-hacking-american-elections-data-3d-illustration-shows-kremlin-spy-hackers-on-internet-attack-usa-election-security-or-cybersecurity-image215186099.html
Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/russia-hacking-american-elections-data-3d-illustration-shows-kremlin-spy-hackers-on-internet-attack-usa-election-security-or-cybersecurity-image215186099.htmlRFPE2G1R–Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity
 Botnet attack illustration. Hacker orchestrating a network breach with multiple compromised computers, emphasizing cyber vulnerability. Stay alert, secure devices. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/botnet-attack-illustration-hacker-orchestrating-a-network-breach-with-multiple-compromised-computers-emphasizing-cyber-vulnerability-stay-alert-secure-devices-flat-vector-illustration-image598705562.html
Botnet attack illustration. Hacker orchestrating a network breach with multiple compromised computers, emphasizing cyber vulnerability. Stay alert, secure devices. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/botnet-attack-illustration-hacker-orchestrating-a-network-breach-with-multiple-compromised-computers-emphasizing-cyber-vulnerability-stay-alert-secure-devices-flat-vector-illustration-image598705562.htmlRF2WP1B1E–Botnet attack illustration. Hacker orchestrating a network breach with multiple compromised computers, emphasizing cyber vulnerability. Stay alert, secure devices. Flat vector illustration
 Website Hacked Cyber Security Alert 3d Illustration Shows Online Site Data Risks. Election Hacking Attacks On The Usa In 2018 And 2020 From Russia Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/website-hacked-cyber-security-alert-3d-illustration-shows-online-site-data-risks-election-hacking-attacks-on-the-usa-in-2018-and-2020-from-russia-image215185936.html
Website Hacked Cyber Security Alert 3d Illustration Shows Online Site Data Risks. Election Hacking Attacks On The Usa In 2018 And 2020 From Russia Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/website-hacked-cyber-security-alert-3d-illustration-shows-online-site-data-risks-election-hacking-attacks-on-the-usa-in-2018-and-2020-from-russia-image215185936.htmlRFPE2FT0–Website Hacked Cyber Security Alert 3d Illustration Shows Online Site Data Risks. Election Hacking Attacks On The Usa In 2018 And 2020 From Russia
 black thin line security breach like shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-security-breach-like-shield-image352775048.html
black thin line security breach like shield Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-thin-line-security-breach-like-shield-image352775048.htmlRF2BDX84T–black thin line security breach like shield
 Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-cyberattack-malicious-infected-spyware-3d-rendering-shows-computer-breach-of-infected-network-image214617437.html
Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-cyberattack-malicious-infected-spyware-3d-rendering-shows-computer-breach-of-infected-network-image214617437.htmlRFPD4JMD–Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network
RF2R8D6AJ–Data breach interconnected icon symbol concept of internet data security alert software bug alert
 Computer virus concept with character and text place. Can use for web banner, infographics, hero images, isometric vector modern illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-concept-with-character-and-text-place-can-use-for-web-banner-infographics-hero-images-isometric-vector-modern-illustration-image500023521.html
Computer virus concept with character and text place. Can use for web banner, infographics, hero images, isometric vector modern illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-concept-with-character-and-text-place-can-use-for-web-banner-infographics-hero-images-isometric-vector-modern-illustration-image500023521.htmlRF2M1E12W–Computer virus concept with character and text place. Can use for web banner, infographics, hero images, isometric vector modern illustration
 Firewall word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/firewall-word-cloud-hand-sphere-concept-on-white-background-image222634376.html
Firewall word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/firewall-word-cloud-hand-sphere-concept-on-white-background-image222634376.htmlRFPX5TBM–Firewall word cloud hand sphere concept on white background.
 Log4Shell. Log4J security vulnerability. Web world data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4shell-log4j-security-vulnerability-web-world-data-center-network-infection-concept-image455567653.html
Log4Shell. Log4J security vulnerability. Web world data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4shell-log4j-security-vulnerability-web-world-data-center-network-infection-concept-image455567653.htmlRF2HD4W59–Log4Shell. Log4J security vulnerability. Web world data center network infection concept.
 Identity theft word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/identity-theft-word-cloud-hand-sphere-concept-on-white-background-image222634836.html
Identity theft word cloud hand sphere concept on white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/identity-theft-word-cloud-hand-sphere-concept-on-white-background-image222634836.htmlRFPX5W04–Identity theft word cloud hand sphere concept on white background.
 Mobile app development concept banner with characters, Financial Consultant sitting at Office Desk with Documents for Tax Calculation, Computer virus Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/mobile-app-development-concept-banner-with-characters-financial-consultant-sitting-at-office-desk-with-documents-for-tax-calculation-computer-virus-image505806176.html
Mobile app development concept banner with characters, Financial Consultant sitting at Office Desk with Documents for Tax Calculation, Computer virus Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/mobile-app-development-concept-banner-with-characters-financial-consultant-sitting-at-office-desk-with-documents-for-tax-calculation-computer-virus-image505806176.htmlRF2MAWCX8–Mobile app development concept banner with characters, Financial Consultant sitting at Office Desk with Documents for Tax Calculation, Computer virus
 Cyber crime. Internet cyber security concept with a padlock on computer server. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-computer-server-ransomware-malware-encrypt-and-hacking-data-security-concept-image432713400.html
Cyber crime. Internet cyber security concept with a padlock on computer server. Ransomware, Malware, Encrypt and Hacking. Data security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-crime-internet-cyber-security-concept-with-a-padlock-on-computer-server-ransomware-malware-encrypt-and-hacking-data-security-concept-image432713400.htmlRF2G3YPA0–Cyber crime. Internet cyber security concept with a padlock on computer server. Ransomware, Malware, Encrypt and Hacking. Data security concept
 Computer virus concept. Scam alert. Spam, malicious application. Envelope with skull. Flat vector modern illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-concept-scam-alert-spam-malicious-application-envelope-with-skull-flat-vector-modern-illustration-image544178249.html
Computer virus concept. Scam alert. Spam, malicious application. Envelope with skull. Flat vector modern illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-concept-scam-alert-spam-malicious-application-envelope-with-skull-flat-vector-modern-illustration-image544178249.htmlRF2PH9CWD–Computer virus concept. Scam alert. Spam, malicious application. Envelope with skull. Flat vector modern illustration.
 Text showing inspiration Ethical Hacking, Business idea act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-ethical-hacking-business-idea-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image549032516.html
Text showing inspiration Ethical Hacking, Business idea act of locating weaknesses and vulnerabilities of computer Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-showing-inspiration-ethical-hacking-business-idea-act-of-locating-weaknesses-and-vulnerabilities-of-computer-image549032516.htmlRF2PW6GG4–Text showing inspiration Ethical Hacking, Business idea act of locating weaknesses and vulnerabilities of computer
 Malware virus software - compromised computer security concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-virus-software-compromised-computer-security-concept-word-cloud-image274698968.html
Malware virus software - compromised computer security concept. Word cloud. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-virus-software-compromised-computer-security-concept-word-cloud-image274698968.htmlRFWXWH9C–Malware virus software - compromised computer security concept. Word cloud.
RF2HA3DXF–Data breach insurance case linear icon
 Surveillance Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/surveillance-law-handwritten-on-a-white-background-image352944311.html
Surveillance Law handwritten on a white background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/surveillance-law-handwritten-on-a-white-background-image352944311.htmlRF2BE601Y–Surveillance Law handwritten on a white background.
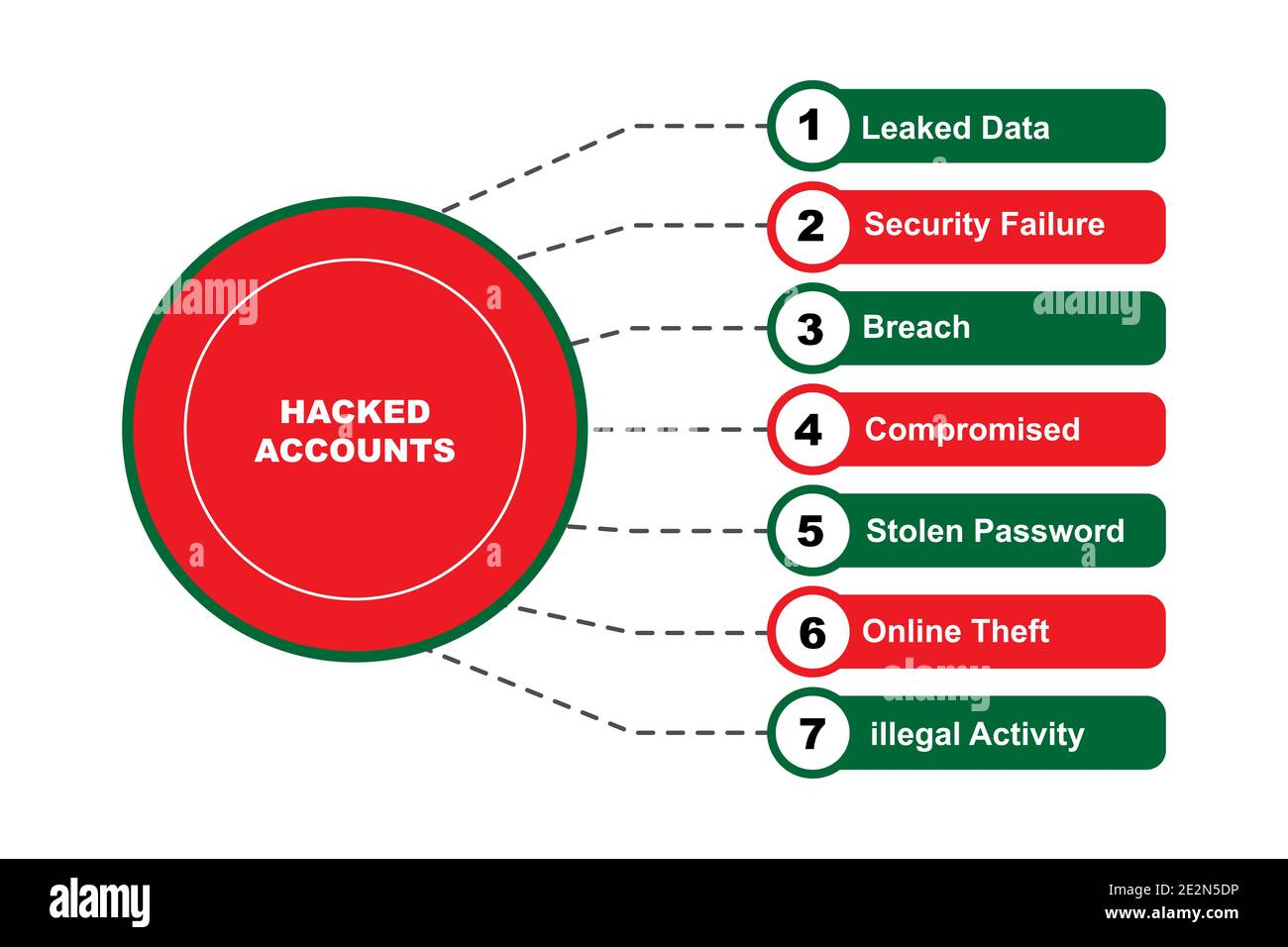 Diagram concept with Hacked Accounts text and keywords. EPS 10 isolated on pink background Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/diagram-concept-with-hacked-accounts-text-and-keywords-eps-10-isolated-on-pink-background-image397533074.html
Diagram concept with Hacked Accounts text and keywords. EPS 10 isolated on pink background Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/diagram-concept-with-hacked-accounts-text-and-keywords-eps-10-isolated-on-pink-background-image397533074.htmlRF2E2N5DP–Diagram concept with Hacked Accounts text and keywords. EPS 10 isolated on pink background
 Likejacking word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/likejacking-word-cloud-concept-on-white-background-image357009046.html
Likejacking word cloud concept on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/likejacking-word-cloud-concept-on-white-background-image357009046.htmlRF2BMR4K2–Likejacking word cloud concept on white background
 DATA BREACH red Rubber Stamp on white background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-breach-red-rubber-stamp-on-white-background-vector-illustration-image467325438.html
DATA BREACH red Rubber Stamp on white background. Vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-breach-red-rubber-stamp-on-white-background-vector-illustration-image467325438.htmlRF2J48EA6–DATA BREACH red Rubber Stamp on white background. Vector illustration
 Vulnerability word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-word-cloud-concept-image262843307.html
Vulnerability word cloud concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vulnerability-word-cloud-concept-image262843307.htmlRFW7HF8Y–Vulnerability word cloud concept
 Data breach or leak. Confidential information database breakout. Cybersecurity threat. Hacker got access to a database. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-breach-or-leak-confidential-information-database-breakout-cybersecurity-threat-hacker-got-access-to-a-database-flat-vector-illustration-image597227174.html
Data breach or leak. Confidential information database breakout. Cybersecurity threat. Hacker got access to a database. Flat vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-breach-or-leak-confidential-information-database-breakout-cybersecurity-threat-hacker-got-access-to-a-database-flat-vector-illustration-image597227174.htmlRF2WKJ19X–Data breach or leak. Confidential information database breakout. Cybersecurity threat. Hacker got access to a database. Flat vector illustration
 Thief hacking, cyber theft and online fraud, hacker using computer, stealing money Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thief-hacking-cyber-theft-and-online-fraud-hacker-using-computer-stealing-money-image452710875.html
Thief hacking, cyber theft and online fraud, hacker using computer, stealing money Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/thief-hacking-cyber-theft-and-online-fraud-hacker-using-computer-stealing-money-image452710875.htmlRF2H8EN9F–Thief hacking, cyber theft and online fraud, hacker using computer, stealing money
 Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-cyberattack-malicious-infected-spyware-3d-rendering-shows-computer-breach-of-infected-network-image214617362.html
Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-cyberattack-malicious-infected-spyware-3d-rendering-shows-computer-breach-of-infected-network-image214617362.htmlRFPD4JHP–Hacker Cyberattack Malicious Infected Spyware 3d Rendering Shows Computer Breach Of Infected Network
 Handwriting text Incident Response. Conceptual photo addressing and analysisaging the aftermath of a security breach Isolated Yellow Text Box Banner w Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-incident-response-conceptual-photo-addressing-and-analysisaging-the-aftermath-of-a-security-breach-isolated-yellow-text-box-banner-w-image248245657.html
Handwriting text Incident Response. Conceptual photo addressing and analysisaging the aftermath of a security breach Isolated Yellow Text Box Banner w Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/handwriting-text-incident-response-conceptual-photo-addressing-and-analysisaging-the-aftermath-of-a-security-breach-isolated-yellow-text-box-banner-w-image248245657.htmlRFTBTFT9–Handwriting text Incident Response. Conceptual photo addressing and analysisaging the aftermath of a security breach Isolated Yellow Text Box Banner w
 Problems with data Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/problems-with-data-image545742338.html
Problems with data Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/problems-with-data-image545742338.htmlRF2PKTKWP–Problems with data
RF2PNX9F2–Cyber analytics linear icons set. Cybersecurity, Analytics, Data, Vulnerability, Threat, Intelligence, Detection line vector and concept signs
 Log4J red warning symbol concept. Log4Shell security vulnerability. Data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4j-red-warning-symbol-concept-log4shell-security-vulnerability-data-center-network-infection-concept-image455567678.html
Log4J red warning symbol concept. Log4Shell security vulnerability. Data center network infection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/log4j-red-warning-symbol-concept-log4shell-security-vulnerability-data-center-network-infection-concept-image455567678.htmlRF2HD4W66–Log4J red warning symbol concept. Log4Shell security vulnerability. Data center network infection concept.
Search Results for Cyber attack data breach Cut Out Stock Images & Pictures (370)
Page 1 of 4