Quick filters:
Page 1 of 34
Concept software piracy Stock Photos and Images
 Internet piracy / online safety / cyber security / ransomware virus / cyber crime/ copyright concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-piracy-online-safety-cyber-security-ransomware-virus-cyber-53207880.html
Internet piracy / online safety / cyber security / ransomware virus / cyber crime/ copyright concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-internet-piracy-online-safety-cyber-security-ransomware-virus-cyber-53207880.htmlRFD2FR5C–Internet piracy / online safety / cyber security / ransomware virus / cyber crime/ copyright concept
 Software piracy grunge concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-grunge-concept-image483647879.html
Software piracy grunge concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-grunge-concept-image483647879.htmlRF2K2T1PF–Software piracy grunge concept
 Man installing software in laptop in dark at night. Hacker loading illegal program or guy downloading files. Cyber security, piracy or virus concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/man-installing-software-in-laptop-in-dark-at-night-hacker-loading-illegal-program-or-guy-downloading-files-cyber-security-piracy-or-virus-concept-image349405306.html
Man installing software in laptop in dark at night. Hacker loading illegal program or guy downloading files. Cyber security, piracy or virus concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/man-installing-software-in-laptop-in-dark-at-night-hacker-loading-illegal-program-or-guy-downloading-files-cyber-security-piracy-or-virus-concept-image349405306.htmlRF2B8CP0X–Man installing software in laptop in dark at night. Hacker loading illegal program or guy downloading files. Cyber security, piracy or virus concept.
 hand holding a dvd, data storage or software piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hand-holding-a-dvd-data-storage-or-software-piracy-concept-161402994.html
hand holding a dvd, data storage or software piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-hand-holding-a-dvd-data-storage-or-software-piracy-concept-161402994.htmlRFKAGF4J–hand holding a dvd, data storage or software piracy concept
 Pirate copy written on a flash drive. Copyright law. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/pirate-copy-written-on-a-flash-drive-copyright-law-image227151737.html
Pirate copy written on a flash drive. Copyright law. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/pirate-copy-written-on-a-flash-drive-copyright-law-image227151737.htmlRFR5FJA1–Pirate copy written on a flash drive. Copyright law.
 CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273379.html
CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273379.htmlRFBPTHEB–CD, DVD and Pirate Flag, concept of Piracy
 Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image343617438.html
Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image343617438.htmlRM2AY13FA–Web piracy concept
 Stop piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stop-piracy-concept-image483632315.html
Stop piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stop-piracy-concept-image483632315.htmlRF2K2R9XK–Stop piracy concept
 Copyright violation, piracy concept. Intellectual property crimes, infringements. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/copyright-violation-piracy-concept-intellectual-property-crimes-infringements-high-quality-photo-image506548524.html
Copyright violation, piracy concept. Intellectual property crimes, infringements. High quality photo Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/copyright-violation-piracy-concept-intellectual-property-crimes-infringements-high-quality-photo-image506548524.htmlRF2MC37PM–Copyright violation, piracy concept. Intellectual property crimes, infringements. High quality photo
 Small Miniature Pirate Standing On A Keyboard (Pirated Software) Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/small-miniature-pirate-standing-on-a-keyboard-pirated-software-image206908268.html
Small Miniature Pirate Standing On A Keyboard (Pirated Software) Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/small-miniature-pirate-standing-on-a-keyboard-pirated-software-image206908268.htmlRFP0HDH0–Small Miniature Pirate Standing On A Keyboard (Pirated Software)
 Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401461.html
Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401461.htmlRMCEH305–Web piracy
 pirate copy of software or video cd Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-pirate-copy-of-software-or-video-cd-35157857.html
pirate copy of software or video cd Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-pirate-copy-of-software-or-video-cd-35157857.htmlRFC15G5N–pirate copy of software or video cd
 Computer with illegal software Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-with-illegal-software-127014966.html
Computer with illegal software Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-with-illegal-software-127014966.htmlRFHAJ0TP–Computer with illegal software
 Server rack room digital security data protection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/server-rack-room-digital-security-data-protection-concept-image384903446.html
Server rack room digital security data protection concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/server-rack-room-digital-security-data-protection-concept-image384903446.htmlRF2DA5T7J–Server rack room digital security data protection concept.
 Hacker mask on a computer screen with the background of the Russian flag. Cyber attack concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-mask-on-a-computer-screen-with-the-background-of-the-russian-flag-cyber-attack-concept-image465554580.html
Hacker mask on a computer screen with the background of the Russian flag. Cyber attack concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-mask-on-a-computer-screen-with-the-background-of-the-russian-flag-cyber-attack-concept-image465554580.htmlRF2J1BRH8–Hacker mask on a computer screen with the background of the Russian flag. Cyber attack concept
 Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-alert-caution-and-warning-concept-yellow-barricade-tape-with-word-in-dark-black-background-image542116893.html
Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-alert-caution-and-warning-concept-yellow-barricade-tape-with-word-in-dark-black-background-image542116893.htmlRF2PDYFHH–Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background.
 Concept of internet security connection with safe Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-concept-of-internet-security-connection-with-safe-137997779.html
Concept of internet security connection with safe Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-concept-of-internet-security-connection-with-safe-137997779.htmlRFJ0E9G3–Concept of internet security connection with safe
 Banner of malware warning keyboard. Cyber security data protection business technology. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/banner-of-malware-warning-keyboard-cyber-security-data-protection-business-technology-image474823128.html
Banner of malware warning keyboard. Cyber security data protection business technology. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/banner-of-malware-warning-keyboard-cyber-security-data-protection-business-technology-image474823128.htmlRF2JGE1MT–Banner of malware warning keyboard. Cyber security data protection business technology.
 Text caption presenting Software Dedicated Team. Business approach people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-software-dedicated-team-business-approach-people-responcible-for-modification-of-software-for-new-features-image547472629.html
Text caption presenting Software Dedicated Team. Business approach people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-caption-presenting-software-dedicated-team-business-approach-people-responcible-for-modification-of-software-for-new-features-image547472629.htmlRM2PPKEWW–Text caption presenting Software Dedicated Team. Business approach people responcible for modification of software for new features
 Male hand points to the word piracy. Internet technology cyberspace piracy crime concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/male-hand-points-to-the-word-piracy-internet-technology-cyberspace-piracy-crime-concept-image425543638.html
Male hand points to the word piracy. Internet technology cyberspace piracy crime concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/male-hand-points-to-the-word-piracy-internet-technology-cyberspace-piracy-crime-concept-image425543638.htmlRF2FM9572–Male hand points to the word piracy. Internet technology cyberspace piracy crime concept.
 Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483647909.html
Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483647909.htmlRF2K2T1RH–Web piracy concept
 digital data security concept padlock locking cd dvd isolated on white Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-digital-data-security-concept-padlock-locking-cd-dvd-isolated-on-white-52749605.html
digital data security concept padlock locking cd dvd isolated on white Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-digital-data-security-concept-padlock-locking-cd-dvd-isolated-on-white-52749605.htmlRFD1PXJD–digital data security concept padlock locking cd dvd isolated on white
 software piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-software-piracy-concept-161774531.html
software piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-software-piracy-concept-161774531.htmlRMKB5D1R–software piracy concept
 computer antivirus umbrella Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-antivirus-umbrella-133373342.html
computer antivirus umbrella Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-antivirus-umbrella-133373342.htmlRFHMYK1J–computer antivirus umbrella
 CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273393.html
CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273393.htmlRFBPTHEW–CD, DVD and Pirate Flag, concept of Piracy
 Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/piracy-image343615409.html
Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/piracy-image343615409.htmlRM2AY10XW–Piracy
 Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483662001.html
Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483662001.htmlRF2K2TKPW–Web piracy concept
 Woman holding phone for illegal file download. Online piracy concept. Unlicensed software programs, unauthorized application using. Mobile malware. Hi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-holding-phone-for-illegal-file-download-online-piracy-concept-unlicensed-software-programs-unauthorized-application-using-mobile-malware-hi-image482292398.html
Woman holding phone for illegal file download. Online piracy concept. Unlicensed software programs, unauthorized application using. Mobile malware. Hi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-holding-phone-for-illegal-file-download-online-piracy-concept-unlicensed-software-programs-unauthorized-application-using-mobile-malware-hi-image482292398.htmlRF2K0J8TE–Woman holding phone for illegal file download. Online piracy concept. Unlicensed software programs, unauthorized application using. Mobile malware. Hi
 'Download' Writing On A Blue Colored Space Key, Technology Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/download-writing-on-a-blue-colored-space-key-technology-concept-image206908284.html
'Download' Writing On A Blue Colored Space Key, Technology Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/download-writing-on-a-blue-colored-space-key-technology-concept-image206908284.htmlRFP0HDHG–'Download' Writing On A Blue Colored Space Key, Technology Concept
 Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401426.html
Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401426.htmlRMCEH2XX–Web piracy
 Peer2peer word cloud shape concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-peer2peer-word-cloud-shape-concept-100701016.html
Peer2peer word cloud shape concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-peer2peer-word-cloud-shape-concept-100701016.htmlRFFRR94T–Peer2peer word cloud shape concept
 Hacker is scanning fingerprints in the dark. Concept of information security in internet networks and espionage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-scanning-fingerprints-in-the-dark-concept-of-information-security-in-internet-networks-and-espionage-image565920625.html
Hacker is scanning fingerprints in the dark. Concept of information security in internet networks and espionage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-scanning-fingerprints-in-the-dark-concept-of-information-security-in-internet-networks-and-espionage-image565920625.htmlRF2RTKWEW–Hacker is scanning fingerprints in the dark. Concept of information security in internet networks and espionage.
 Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image229749388.html
Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image229749388.htmlRFR9NYK8–Cyber security, information privacy and data protection concept on server room background.
 Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43759654.html
Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43759654.htmlRFCF5BTP–Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook
 Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-alert-caution-and-warning-concept-yellow-barricade-tape-with-word-in-dark-black-background-image542116079.html
Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/software-piracy-alert-caution-and-warning-concept-yellow-barricade-tape-with-word-in-dark-black-background-image542116079.htmlRF2PDYEGF–Software piracy alert, caution and warning concept. Yellow barricade tape with word in dark black background.
RFKCC9RX–Young businesswoman working in virtual glasses, select the icon RANSOMWARE on the virtual display
 Security technology - lock key, code ... Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-security-technology-lock-key-code-139043364.html
Security technology - lock key, code ... Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-security-technology-lock-key-code-139043364.htmlRFJ25Y6C–Security technology - lock key, code ...
 ransomware on paper blueprint background, technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-ransomware-on-paper-blueprint-background-technology-concept-102417196.html
ransomware on paper blueprint background, technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-ransomware-on-paper-blueprint-background-technology-concept-102417196.htmlRFFXHE50–ransomware on paper blueprint background, technology concept
RF2CT66MW–The word download with arrow icon on wooden cube with computer keyboard. Data downloading concept.
 Music piracy grunge concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/music-piracy-grunge-concept-image483647867.html
Music piracy grunge concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/music-piracy-grunge-concept-image483647867.htmlRF2K2T1P3–Music piracy grunge concept
 Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894571.html
Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894571.htmlRMK001GY–Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft
 CD DVD optical disc media inserted in a laptop computer disc tray, closeup, nobody. Films, movies software data storage and sharing, piracy, installat Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cd-dvd-optical-disc-media-inserted-in-a-laptop-computer-disc-tray-closeup-nobody-films-movies-software-data-storage-and-sharing-piracy-installat-image468797217.html
CD DVD optical disc media inserted in a laptop computer disc tray, closeup, nobody. Films, movies software data storage and sharing, piracy, installat Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cd-dvd-optical-disc-media-inserted-in-a-laptop-computer-disc-tray-closeup-nobody-films-movies-software-data-storage-and-sharing-piracy-installat-image468797217.htmlRF2J6KFHN–CD DVD optical disc media inserted in a laptop computer disc tray, closeup, nobody. Films, movies software data storage and sharing, piracy, installat
 Spam, Technology Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-spam-technology-concept-165246389.html
Spam, Technology Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-spam-technology-concept-165246389.htmlRFKGRHCN–Spam, Technology Concept
 CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31290970.html
CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31290970.htmlRFBPWBXJ–CD, DVD and Pirate Flag, concept of Piracy
 Piracy crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/piracy-crime-image343623854.html
Piracy crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/piracy-crime-image343623854.htmlRM2AY1BME–Piracy crime
 Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483634793.html
Web piracy concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/web-piracy-concept-image483634793.htmlRF2K2RD35–Web piracy concept
 Computer security concept. Padlock symbolizing data protection in the network and personal computers. Mixed media. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-concept-padlock-symbolizing-data-protection-in-the-network-and-personal-computers-mixed-media-image383566869.html
Computer security concept. Padlock symbolizing data protection in the network and personal computers. Mixed media. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-concept-padlock-symbolizing-data-protection-in-the-network-and-personal-computers-mixed-media-image383566869.htmlRF2D80YCN–Computer security concept. Padlock symbolizing data protection in the network and personal computers. Mixed media.
 padlock on computer keyboard, internet security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/padlock-on-computer-keyboard-internet-security-concept-image366686069.html
padlock on computer keyboard, internet security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/padlock-on-computer-keyboard-internet-security-concept-image366686069.htmlRF2C8FYR1–padlock on computer keyboard, internet security concept
 Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401573.html
Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401573.htmlRMCEH345–Web piracy
 Password security concept word cloud background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-password-security-concept-word-cloud-background-100757271.html
Password security concept word cloud background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-password-security-concept-word-cloud-background-100757271.htmlRFFRWTWY–Password security concept word cloud background
 Hacker is pointing his finger at a group of zeros on a dark background. Concept of information security in internet networks and espionage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-pointing-his-finger-at-a-group-of-zeros-on-a-dark-background-concept-of-information-security-in-internet-networks-and-espionage-image565920688.html
Hacker is pointing his finger at a group of zeros on a dark background. Concept of information security in internet networks and espionage. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-pointing-his-finger-at-a-group-of-zeros-on-a-dark-background-concept-of-information-security-in-internet-networks-and-espionage-image565920688.htmlRF2RTKWH4–Hacker is pointing his finger at a group of zeros on a dark background. Concept of information security in internet networks and espionage.
 Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image229749392.html
Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image229749392.htmlRFR9NYKC–Cyber security, information privacy and data protection concept on server room background.
 Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43760330.html
Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43760330.htmlRFCF5CMX–Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook
 Hand turns dice and changes the word piracy to privacy. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-turns-dice-and-changes-the-word-piracy-to-privacy-image396558572.html
Hand turns dice and changes the word piracy to privacy. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-turns-dice-and-changes-the-word-piracy-to-privacy-image396558572.htmlRF2E14PE4–Hand turns dice and changes the word piracy to privacy.
RFKCC9T1–Young businesswoman working in virtual glasses, select the icon RANSOMWARE on the virtual display
 internet spam scam security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-spam-scam-security-image359928015.html
internet spam scam security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-spam-scam-security-image359928015.htmlRF2BWG3RY–internet spam scam security
 hacker working with laptop are caught by handcuffed. internet crime , hacking and malware concept. anonymous face Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-working-with-laptop-are-caught-by-handcuffed-internet-crime-hacking-and-malware-concept-anonymous-face-image256844292.html
hacker working with laptop are caught by handcuffed. internet crime , hacking and malware concept. anonymous face Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-working-with-laptop-are-caught-by-handcuffed-internet-crime-hacking-and-malware-concept-anonymous-face-image256844292.htmlRFTWT7EC–hacker working with laptop are caught by handcuffed. internet crime , hacking and malware concept. anonymous face
 Phishing and cyber crime concept, 3D rendering isolated on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phishing-and-cyber-crime-concept-3d-rendering-isolated-on-white-background-image603539125.html
Phishing and cyber crime concept, 3D rendering isolated on white background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/phishing-and-cyber-crime-concept-3d-rendering-isolated-on-white-background-image603539125.htmlRF2X1WG8N–Phishing and cyber crime concept, 3D rendering isolated on white background
 Conceptual display Software Dedicated Team. Concept meaning people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-software-dedicated-team-concept-meaning-people-responcible-for-modification-of-software-for-new-features-image550236735.html
Conceptual display Software Dedicated Team. Concept meaning people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/conceptual-display-software-dedicated-team-concept-meaning-people-responcible-for-modification-of-software-for-new-features-image550236735.htmlRF2PY5CFY–Conceptual display Software Dedicated Team. Concept meaning people responcible for modification of software for new features
 Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894579.html
Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894579.htmlRMK001H7–Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft
 Modern smartphone with you have been hacked notification on screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/modern-smartphone-with-you-have-been-hacked-notification-on-screen-image330723276.html
Modern smartphone with you have been hacked notification on screen Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/modern-smartphone-with-you-have-been-hacked-notification-on-screen-image330723276.htmlRF2A61MWG–Modern smartphone with you have been hacked notification on screen
 Background with programmer's road and key symbol as 3D rendering Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/background-with-programmers-road-and-key-symbol-as-3d-rendering-image469551048.html
Background with programmer's road and key symbol as 3D rendering Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/background-with-programmers-road-and-key-symbol-as-3d-rendering-image469551048.htmlRF2J7WW48–Background with programmer's road and key symbol as 3D rendering
 CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31270774.html
CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31270774.htmlRFBPTE5A–CD, DVD and Pirate Flag, concept of Piracy
 Stop piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stop-piracy-image343623860.html
Stop piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stop-piracy-image343623860.htmlRM2AY1BMM–Stop piracy
 Music piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/music-piracy-image483643505.html
Music piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/music-piracy-image483643505.htmlRF2K2RT69–Music piracy
 Computer security concept. Hand and shield symbolizing data protection in the network and personal computers. Mixed media. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-concept-hand-and-shield-symbolizing-data-protection-in-the-network-and-personal-computers-mixed-media-image383566887.html
Computer security concept. Hand and shield symbolizing data protection in the network and personal computers. Mixed media. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-security-concept-hand-and-shield-symbolizing-data-protection-in-the-network-and-personal-computers-mixed-media-image383566887.htmlRF2D80YDB–Computer security concept. Hand and shield symbolizing data protection in the network and personal computers. Mixed media.
 padlock and wrench on computer keyboard, internet security and repair concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/padlock-and-wrench-on-computer-keyboard-internet-security-and-repair-concept-image366687276.html
padlock and wrench on computer keyboard, internet security and repair concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/padlock-and-wrench-on-computer-keyboard-internet-security-and-repair-concept-image366687276.htmlRF2C8G1A4–padlock and wrench on computer keyboard, internet security and repair concept
 Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401610.html
Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401610.htmlRMCEH35E–Web piracy
 'HACK' Red button keyboard on laptop computer for Business and Technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hack-red-button-keyboard-on-laptop-computer-for-business-and-technology-concept-image211437585.html
'HACK' Red button keyboard on laptop computer for Business and Technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hack-red-button-keyboard-on-laptop-computer-for-business-and-technology-concept-image211437585.htmlRFP7YPP9–'HACK' Red button keyboard on laptop computer for Business and Technology concept
 Hacker standing holding a magnifying glass with data protection sign on dark background. Concept of information security in internet networks and espi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-standing-holding-a-magnifying-glass-with-data-protection-sign-on-dark-background-concept-of-information-security-in-internet-networks-and-espi-image565920693.html
Hacker standing holding a magnifying glass with data protection sign on dark background. Concept of information security in internet networks and espi Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-standing-holding-a-magnifying-glass-with-data-protection-sign-on-dark-background-concept-of-information-security-in-internet-networks-and-espi-image565920693.htmlRF2RTKWH9–Hacker standing holding a magnifying glass with data protection sign on dark background. Concept of information security in internet networks and espi
 Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image236844228.html
Cyber security, information privacy and data protection concept on server room background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image236844228.htmlRFRN956C–Cyber security, information privacy and data protection concept on server room background.
 Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43759843.html
Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43759843.htmlRFCF5C3F–Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook
 Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-in-front-at-computer-into-dark-room-represents-the-danger-of-surfing-the-internet-internet-security-concept-image334250779.html
Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-in-front-at-computer-into-dark-room-represents-the-danger-of-surfing-the-internet-internet-security-concept-image334250779.htmlRF2ABPC7R–Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept.
RFKCC9R3–Young businesswoman working in virtual glasses, select the icon RANSOMWARE on the virtual display
 internet spam scam security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-spam-scam-security-image359927317.html
internet spam scam security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-spam-scam-security-image359927317.htmlRF2BWG2Y1–internet spam scam security
 Anonymous hacker programmer uses a laptop to hack the system. Stealing personal data. Creation and infection of malicious virus. The concept of cyber Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/anonymous-hacker-programmer-uses-a-laptop-to-hack-the-system-stealing-personal-data-creation-and-infection-of-malicious-virus-the-concept-of-cyber-image209698859.html
Anonymous hacker programmer uses a laptop to hack the system. Stealing personal data. Creation and infection of malicious virus. The concept of cyber Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/anonymous-hacker-programmer-uses-a-laptop-to-hack-the-system-stealing-personal-data-creation-and-infection-of-malicious-virus-the-concept-of-cyber-image209698859.htmlRFP54H0Y–Anonymous hacker programmer uses a laptop to hack the system. Stealing personal data. Creation and infection of malicious virus. The concept of cyber
 Girl works on the computer surrounded by UFOs. Concept of internet espionage and security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/girl-works-on-the-computer-surrounded-by-ufos-concept-of-internet-espionage-and-security-image344930499.html
Girl works on the computer surrounded by UFOs. Concept of internet espionage and security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/girl-works-on-the-computer-surrounded-by-ufos-concept-of-internet-espionage-and-security-image344930499.htmlRF2B14XAB–Girl works on the computer surrounded by UFOs. Concept of internet espionage and security
 Hand writing sign Software Dedicated Team. Concept meaning people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-software-dedicated-team-concept-meaning-people-responcible-for-modification-of-software-for-new-features-image550246580.html
Hand writing sign Software Dedicated Team. Concept meaning people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-software-dedicated-team-concept-meaning-people-responcible-for-modification-of-software-for-new-features-image550246580.htmlRF2PY5W3G–Hand writing sign Software Dedicated Team. Concept meaning people responcible for modification of software for new features
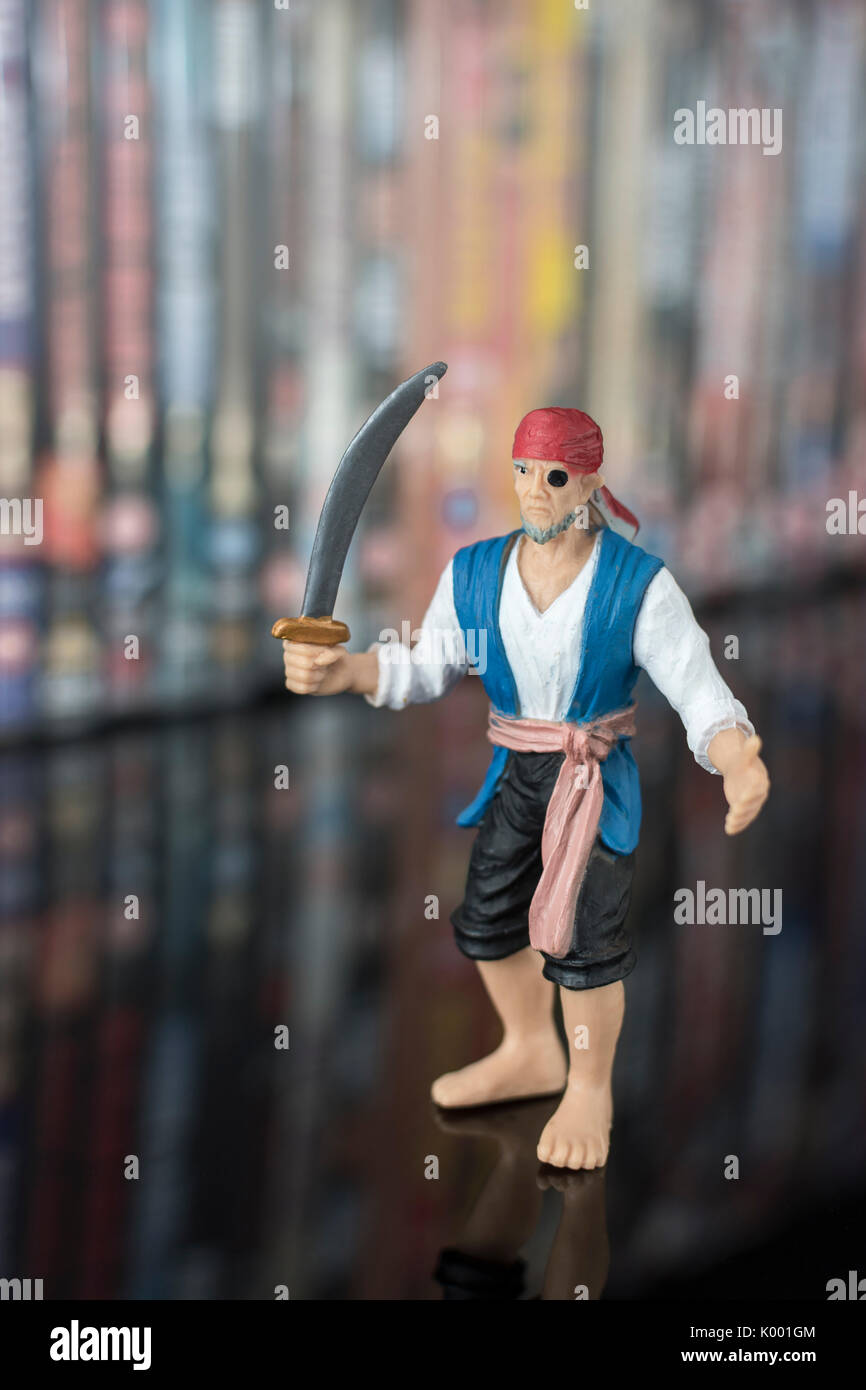 Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894564.html
Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894564.htmlRMK001GM–Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft
 You Have Been Hacked Concept text Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/you-have-been-hacked-concept-text-image433611976.html
You Have Been Hacked Concept text Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/you-have-been-hacked-concept-text-image433611976.htmlRM2G5CME0–You Have Been Hacked Concept text
 DVD between two paragraphs, concept of illegal copy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-dvd-between-two-paragraphs-concept-of-illegal-copy-38156398.html
DVD between two paragraphs, concept of illegal copy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-dvd-between-two-paragraphs-concept-of-illegal-copy-38156398.htmlRFC624TE–DVD between two paragraphs, concept of illegal copy
 CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273385.html
CD, DVD and Pirate Flag, concept of Piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cd-dvd-and-pirate-flag-concept-of-piracy-31273385.htmlRFBPTHEH–CD, DVD and Pirate Flag, concept of Piracy
 Risk concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/risk-concept-image343617396.html
Risk concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/risk-concept-image343617396.htmlRM2AY13DT–Risk concept
 Spy text on the screen concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spy-text-on-the-screen-concept-image483623967.html
Spy text on the screen concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spy-text-on-the-screen-concept-image483623967.htmlRF2K2PY8F–Spy text on the screen concept.
 Hand touching screen security scanning protect. Cyber Security and safety information, personal data concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-touching-screen-security-scanning-protect-cyber-security-and-safety-information-personal-data-concept-image607705911.html
Hand touching screen security scanning protect. Cyber Security and safety information, personal data concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-touching-screen-security-scanning-protect-cyber-security-and-safety-information-personal-data-concept-image607705911.htmlRF2X8KB2F–Hand touching screen security scanning protect. Cyber Security and safety information, personal data concept.
 The man is holding a key to the padlock under the mobile phone. The concept of securing the phone, cyber attack, data security problems on a personal Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-man-is-holding-a-key-to-the-padlock-under-the-mobile-phone-the-concept-of-securing-the-phone-cyber-attack-data-security-problems-on-a-personal-image187884934.html
The man is holding a key to the padlock under the mobile phone. The concept of securing the phone, cyber attack, data security problems on a personal Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-man-is-holding-a-key-to-the-padlock-under-the-mobile-phone-the-concept-of-securing-the-phone-cyber-attack-data-security-problems-on-a-personal-image187884934.htmlRFMWJW46–The man is holding a key to the padlock under the mobile phone. The concept of securing the phone, cyber attack, data security problems on a personal
 Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401503.html
Web piracy Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-web-piracy-43401503.htmlRMCEH31K–Web piracy
 'HACK' Red button keyboard on laptop computer for Business and Technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hack-red-button-keyboard-on-laptop-computer-for-business-and-technology-concept-image211437574.html
'HACK' Red button keyboard on laptop computer for Business and Technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hack-red-button-keyboard-on-laptop-computer-for-business-and-technology-concept-image211437574.htmlRFP7YPNX–'HACK' Red button keyboard on laptop computer for Business and Technology concept
 Hacker is pointing a pen at a group of zeros on a dark background. Concept of information security in internet networks and espionage. Network espiona Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-pointing-a-pen-at-a-group-of-zeros-on-a-dark-background-concept-of-information-security-in-internet-networks-and-espionage-network-espiona-image565920703.html
Hacker is pointing a pen at a group of zeros on a dark background. Concept of information security in internet networks and espionage. Network espiona Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-is-pointing-a-pen-at-a-group-of-zeros-on-a-dark-background-concept-of-information-security-in-internet-networks-and-espionage-network-espiona-image565920703.htmlRF2RTKWHK–Hacker is pointing a pen at a group of zeros on a dark background. Concept of information security in internet networks and espionage. Network espiona
 Cyber security, information privacy and data protection concept on server room background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image236090571.html
Cyber security, information privacy and data protection concept on server room background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-information-privacy-and-data-protection-concept-on-server-room-background-image236090571.htmlRFRM2RX3–Cyber security, information privacy and data protection concept on server room background
 Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook - Isolated on Black Background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43828420.html
Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook - Isolated on Black Background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-piracy-concept-burnt-cds-with-illegal-software-on-keyboard-of-notebook-43828420.htmlRFCF8FGM–Piracy Concept - Burnt CDs With Illegal Software on Keyboard of Notebook - Isolated on Black Background
 Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-in-front-at-computer-into-dark-room-represents-the-danger-of-surfing-the-internet-internet-security-concept-image334250598.html
Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/masked-hacker-in-front-at-computer-into-dark-room-represents-the-danger-of-surfing-the-internet-internet-security-concept-image334250598.htmlRF2ABPC1A–Masked hacker in front at computer into dark room represents the danger of surfing the internet. Internet security concept.
RFKCC9T5–Young businesswoman working in virtual glasses, select the icon cyber security on the virtual display
 business hand pushing license on Flipboard Display Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-hand-pushing-license-on-flipboard-display-88365656.html
business hand pushing license on Flipboard Display Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-hand-pushing-license-on-flipboard-display-88365656.htmlRFF3NB88–business hand pushing license on Flipboard Display
 Typewriter displaying Piracy in a blue tone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/typewriter-displaying-piracy-in-a-blue-tone-image450429300.html
Typewriter displaying Piracy in a blue tone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/typewriter-displaying-piracy-in-a-blue-tone-image450429300.htmlRM2H4PR4M–Typewriter displaying Piracy in a blue tone
 Internet security concept. Personal data and information Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-security-concept-personal-data-and-information-image557877511.html
Internet security concept. Personal data and information Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/internet-security-concept-personal-data-and-information-image557877511.htmlRF2RBHECR–Internet security concept. Personal data and information
 Hand writing sign Software Dedicated Team. Business concept people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-software-dedicated-team-business-concept-people-responcible-for-modification-of-software-for-new-features-image550244218.html
Hand writing sign Software Dedicated Team. Business concept people responcible for modification of software for new features Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-software-dedicated-team-business-concept-people-responcible-for-modification-of-software-for-new-features-image550244218.htmlRF2PY5P36–Hand writing sign Software Dedicated Team. Business concept people responcible for modification of software for new features
 Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894557.html
Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/sword-wielding-toy-pirate-standing-in-front-of-stacks-of-dvds-digital-image154894557.htmlRMK001GD–Sword wielding toy pirate standing in front of stacks of DVDs (Digital Versatile Disc) - metaphor software piracy, Chinese counterfeit goods, IP theft
 You Have Been Hacked Concept text Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/you-have-been-hacked-concept-text-image433616200.html
You Have Been Hacked Concept text Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/you-have-been-hacked-concept-text-image433616200.htmlRM2G5CWTT–You Have Been Hacked Concept text
 Smart phone in chain with lock. Isolated on white with clipping path. Security, data protection and software lock theme Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-smart-phone-in-chain-with-lock-isolated-on-white-with-clipping-path-144112252.html
Smart phone in chain with lock. Isolated on white with clipping path. Security, data protection and software lock theme Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-smart-phone-in-chain-with-lock-isolated-on-white-with-clipping-path-144112252.htmlRFJACTJ4–Smart phone in chain with lock. Isolated on white with clipping path. Security, data protection and software lock theme
Search Results for Concept software piracy Stock Photos and Images (3,322)
Page 1 of 34