SAVE 40% ON SINGLE IMAGE PURCHASES - OFFER ENDS SOON, USE CODE: IMAGESAVE40%
China hacking Stock Photos and Images
 Chinese soldiers march past part of the United States Embassy in Beijing on May 20, 2014. China summoned the U.S. ambassador and the Defense Ministry warned of 'serious damage' to military relations after the United States charged five Chinese army officers with hacking into American companies to steal trade secrets. UPI/Stephen Shaver Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-soldiers-march-past-part-of-the-united-states-embassy-in-beijing-on-may-20-2014-china-summoned-the-us-ambassador-and-the-defense-ministry-warned-of-serious-damage-to-military-relations-after-the-united-states-charged-five-chinese-army-officers-with-hacking-into-american-companies-to-steal-trade-secrets-upistephen-shaver-image258181733.html
Chinese soldiers march past part of the United States Embassy in Beijing on May 20, 2014. China summoned the U.S. ambassador and the Defense Ministry warned of 'serious damage' to military relations after the United States charged five Chinese army officers with hacking into American companies to steal trade secrets. UPI/Stephen Shaver Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-soldiers-march-past-part-of-the-united-states-embassy-in-beijing-on-may-20-2014-china-summoned-the-us-ambassador-and-the-defense-ministry-warned-of-serious-damage-to-military-relations-after-the-united-states-charged-five-chinese-army-officers-with-hacking-into-american-companies-to-steal-trade-secrets-upistephen-shaver-image258181733.htmlRMW015C5–Chinese soldiers march past part of the United States Embassy in Beijing on May 20, 2014. China summoned the U.S. ambassador and the Defense Ministry warned of 'serious damage' to military relations after the United States charged five Chinese army officers with hacking into American companies to steal trade secrets. UPI/Stephen Shaver
 Symbolic image, hacking China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear power Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-hacking-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-power-image559048967.html
Symbolic image, hacking China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear power Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-hacking-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-power-image559048967.htmlRF2RDETJF–Symbolic image, hacking China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear power
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37012416.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37012416.htmlRFC461M0–Photo illustration showing data and information streams representing national security and cyber crime
 American hacker trying to retrieve secret information from China. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/american-hacker-trying-to-retrieve-secret-information-from-china-image364684519.html
American hacker trying to retrieve secret information from China. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/american-hacker-trying-to-retrieve-secret-information-from-china-image364684519.htmlRF2C58PR3–American hacker trying to retrieve secret information from China.
 Chinese cyber hacking, conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-chinese-cyber-hacking-conceptual-illustration-92445834.html
Chinese cyber hacking, conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-chinese-cyber-hacking-conceptual-illustration-92445834.htmlRFFAB7GX–Chinese cyber hacking, conceptual illustration.
 Closed handcuffs on network wires and China flag on an abstract background, concept on the theme of punishment for crimes on the network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closed-handcuffs-on-network-wires-and-china-flag-on-an-abstract-background-concept-on-the-theme-of-punishment-for-crimes-on-the-network-image565927021.html
Closed handcuffs on network wires and China flag on an abstract background, concept on the theme of punishment for crimes on the network Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/closed-handcuffs-on-network-wires-and-china-flag-on-an-abstract-background-concept-on-the-theme-of-punishment-for-crimes-on-the-network-image565927021.htmlRF2RTM5K9–Closed handcuffs on network wires and China flag on an abstract background, concept on the theme of punishment for crimes on the network
 ATM machine in Beijing, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-machine-in-beijing-china-76052359.html
ATM machine in Beijing, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-machine-in-beijing-china-76052359.htmlRMEBMDFK–ATM machine in Beijing, China
 5 Dec 2023. Headline on front page of The Guardian reads Sellafield nuclear site hacked by groups linked to Russia and China. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/5-dec-2023-headline-on-front-page-of-the-guardian-reads-sellafield-nuclear-site-hacked-by-groups-linked-to-russia-and-china-image574906681.html
5 Dec 2023. Headline on front page of The Guardian reads Sellafield nuclear site hacked by groups linked to Russia and China. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/5-dec-2023-headline-on-front-page-of-the-guardian-reads-sellafield-nuclear-site-hacked-by-groups-linked-to-russia-and-china-image574906681.htmlRM2TB979D–5 Dec 2023. Headline on front page of The Guardian reads Sellafield nuclear site hacked by groups linked to Russia and China.
 ATM and currency exchange machine in Beijing, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-and-currency-exchange-machine-in-beijing-china-76052117.html
ATM and currency exchange machine in Beijing, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-and-currency-exchange-machine-in-beijing-china-76052117.htmlRMEBMD71–ATM and currency exchange machine in Beijing, China
 Chinese hooded hacker with mask holding smartphone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-hooded-hacker-with-mask-holding-smartphone-image246273865.html
Chinese hooded hacker with mask holding smartphone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-hooded-hacker-with-mask-holding-smartphone-image246273865.htmlRFT8JMR5–Chinese hooded hacker with mask holding smartphone
 China flag and modern backlit computer mouse. The concept of digital threat, illegal actions on the Internet Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-flag-and-modern-backlit-computer-mouse-the-concept-of-digital-threat-illegal-actions-on-the-internet-image236831505.html
China flag and modern backlit computer mouse. The concept of digital threat, illegal actions on the Internet Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-flag-and-modern-backlit-computer-mouse-the-concept-of-digital-threat-illegal-actions-on-the-internet-image236831505.htmlRFRN8H01–China flag and modern backlit computer mouse. The concept of digital threat, illegal actions on the Internet
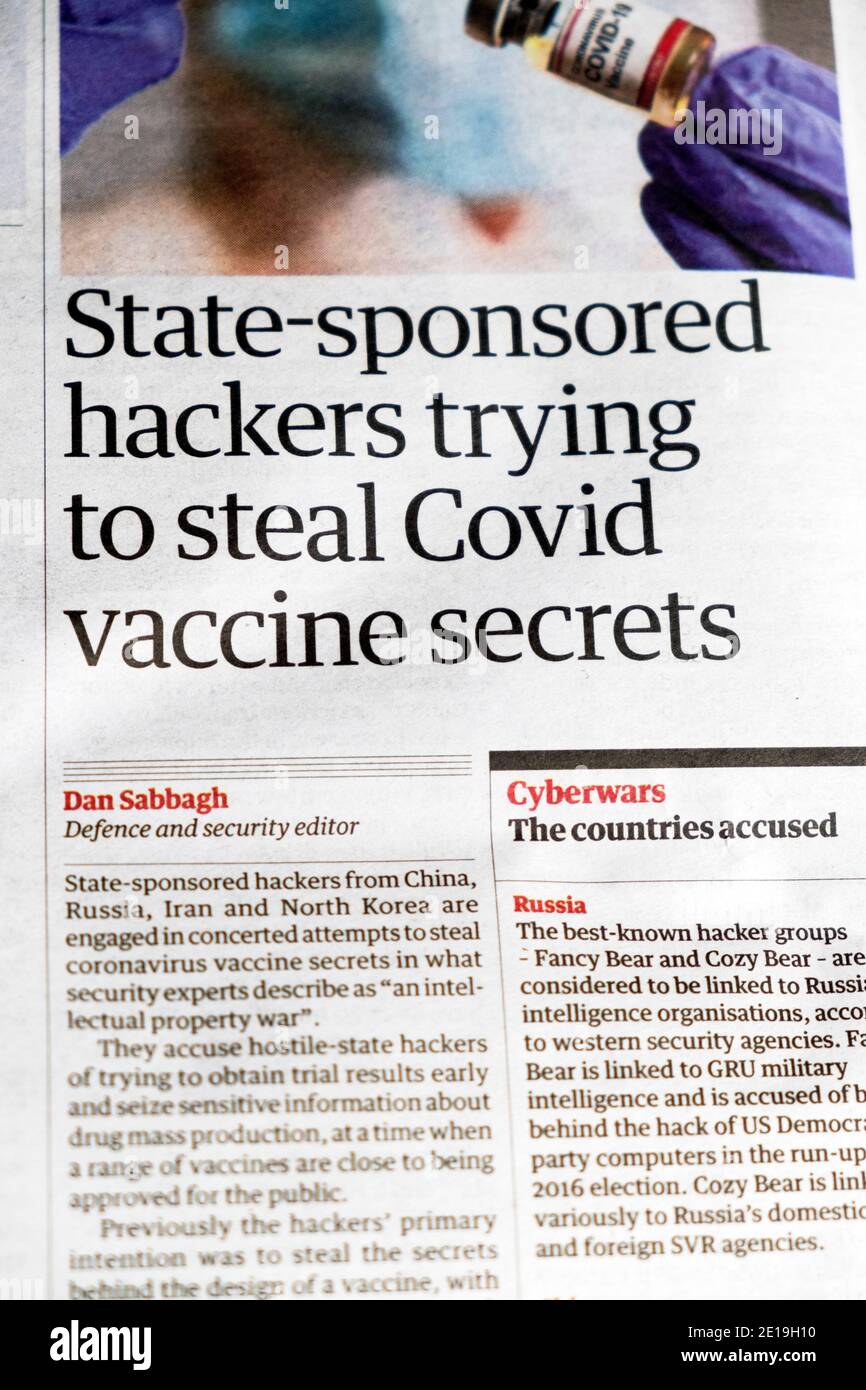 'State-sponsored hackers trying to steal Covid vaccine secrets' Covid-19 news in Guardian newspaper headline 23 November 2020 London England UK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/state-sponsored-hackers-trying-to-steal-covid-vaccine-secrets-covid-19-news-in-guardian-newspaper-headline-23-november-2020-london-england-uk-image396664044.html
'State-sponsored hackers trying to steal Covid vaccine secrets' Covid-19 news in Guardian newspaper headline 23 November 2020 London England UK Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/state-sponsored-hackers-trying-to-steal-covid-vaccine-secrets-covid-19-news-in-guardian-newspaper-headline-23-november-2020-london-england-uk-image396664044.htmlRM2E19H10–'State-sponsored hackers trying to steal Covid vaccine secrets' Covid-19 news in Guardian newspaper headline 23 November 2020 London England UK
 ATM in China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-in-china-79874038.html
ATM in China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-atm-in-china-79874038.htmlRMEHXG46–ATM in China
 Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-media-on-display-with-cyberwarfare-hacking-and-security-breach-searching-on-tablet-pad-phone-or-smartphone-screen-in-hand-abstract-concept-image493616600.html
Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-media-on-display-with-cyberwarfare-hacking-and-security-breach-searching-on-tablet-pad-phone-or-smartphone-screen-in-hand-abstract-concept-image493616600.htmlRF2KK2508–Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept
 Silhouette of China from binary digits Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silhouette-of-china-from-binary-digits-175198685.html
Silhouette of China from binary digits Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-silhouette-of-china-from-binary-digits-175198685.htmlRMM50YKW–Silhouette of China from binary digits
 Image of cyber security, flag of china and financial data processing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-cyber-security-flag-of-china-and-financial-data-processing-image599822322.html
Image of cyber security, flag of china and financial data processing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-cyber-security-flag-of-china-and-financial-data-processing-image599822322.htmlRF2WRT7DP–Image of cyber security, flag of china and financial data processing
 Symbolic image, China, Russia, ransomware, data centres, servers, cyber security, cyber attacks worldwide, computer crime, digital IT attacks Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-china-russia-ransomware-data-centres-servers-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-image605301441.html
Symbolic image, China, Russia, ransomware, data centres, servers, cyber security, cyber attacks worldwide, computer crime, digital IT attacks Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-china-russia-ransomware-data-centres-servers-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-image605301441.htmlRF2X4NT4H–Symbolic image, China, Russia, ransomware, data centres, servers, cyber security, cyber attacks worldwide, computer crime, digital IT attacks
 Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118592.html
Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118592.htmlRMTA1680–Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China
 Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609195.html
Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609195.htmlRM2X57TKR–Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear
 Newpaper from Hong Kong about Google walking out China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-newpaper-from-hong-kong-about-google-walking-out-china-27548683.html
Newpaper from Hong Kong about Google walking out China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-newpaper-from-hong-kong-about-google-walking-out-china-27548683.htmlRMBGPXHF–Newpaper from Hong Kong about Google walking out China
 China Mobile logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-mobile-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837807.html
China Mobile logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-mobile-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837807.htmlRMR519X7–China Mobile logo is seen on an Android mobile device with a figure of hacker in the background.
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013309.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013309.htmlRFC462RW–Photo illustration showing data and information streams representing national security and cyber crime
 Laptop with lock symbol on screen on background of Industrial and Commercial Bank of China logo. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-lock-symbol-on-screen-on-background-of-industrial-and-commercial-bank-of-china-logo-image458490290.html
Laptop with lock symbol on screen on background of Industrial and Commercial Bank of China logo. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-lock-symbol-on-screen-on-background-of-industrial-and-commercial-bank-of-china-logo-image458490290.htmlRF2HHX116–Laptop with lock symbol on screen on background of Industrial and Commercial Bank of China logo.
 Chinese cyber hacking, conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-chinese-cyber-hacking-conceptual-illustration-92445833.html
Chinese cyber hacking, conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-chinese-cyber-hacking-conceptual-illustration-92445833.htmlRFFAB7GW–Chinese cyber hacking, conceptual illustration.
 An open security lock and key on background of Bank of China logo in mirror reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-open-security-lock-and-key-on-background-of-bank-of-china-logo-in-mirror-reflection-image458487600.html
An open security lock and key on background of Bank of China logo in mirror reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-open-security-lock-and-key-on-background-of-bank-of-china-logo-in-mirror-reflection-image458487600.htmlRF2HHWWH4–An open security lock and key on background of Bank of China logo in mirror reflection
 China Piracy Pirate economy sea trade and money Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-china-piracy-pirate-economy-sea-trade-and-money-73569296.html
China Piracy Pirate economy sea trade and money Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-china-piracy-pirate-economy-sea-trade-and-money-73569296.htmlRME7KAAT–China Piracy Pirate economy sea trade and money
 A waving mixed USA (United States of America and Chinese (People's Republic of China) Flag to symbolize cooperation or tension between the two countri Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-waving-mixed-usa-united-states-of-america-and-chinese-peoples-republic-of-china-flag-to-symbolize-cooperation-or-tension-between-the-two-countri-image389938965.html
A waving mixed USA (United States of America and Chinese (People's Republic of China) Flag to symbolize cooperation or tension between the two countri Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-waving-mixed-usa-united-states-of-america-and-chinese-peoples-republic-of-china-flag-to-symbolize-cooperation-or-tension-between-the-two-countri-image389938965.htmlRF2DJB73H–A waving mixed USA (United States of America and Chinese (People's Republic of China) Flag to symbolize cooperation or tension between the two countri
RF2R7CT91–Vancouver, CANADA - Jun 14 2023 : Twitter icon seen in an iPhone on Chinese flag background. Twitter and China concept image
 Wooden hand stealing password from a computer screen concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-wooden-hand-stealing-password-from-a-computer-screen-concept-91676303.html
Wooden hand stealing password from a computer screen concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-wooden-hand-stealing-password-from-a-computer-screen-concept-91676303.htmlRFF9461K–Wooden hand stealing password from a computer screen concept
 Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581872.html
Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581872.htmlRMHKKHET–Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News
 View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263944433.html
View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263944433.htmlRMW9BKPW–View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S
 Spying Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spying-image366518816.html
Spying Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spying-image366518816.htmlRM2C88ADM–Spying
 Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-media-on-display-with-cyberwarfare-hacking-and-security-breach-searching-on-tablet-pad-phone-or-smartphone-screen-in-hand-abstract-concept-image493616606.html
Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/social-media-on-display-with-cyberwarfare-hacking-and-security-breach-searching-on-tablet-pad-phone-or-smartphone-screen-in-hand-abstract-concept-image493616606.htmlRF2KK250E–Social media on display with Cyberwarfare, hacking and security breach. Searching on tablet, pad, phone or smartphone screen in hand. Abstract concept
 Spying Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spying-image366380800.html
Spying Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/spying-image366380800.htmlRM2C822CG–Spying
 USA China hacking cyber espionage. Chinese hacker investigation of surveillance or security breach Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/usa-china-hacking-cyber-espionage-chinese-hacker-investigation-of-surveillance-or-security-breach-image262987010.html
USA China hacking cyber espionage. Chinese hacker investigation of surveillance or security breach Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/usa-china-hacking-cyber-espionage-chinese-hacker-investigation-of-surveillance-or-security-breach-image262987010.htmlRFW7T2H6–USA China hacking cyber espionage. Chinese hacker investigation of surveillance or security breach
 Google's Chinese homepage, google.cn, is seen on a computer screen in New York Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-googles-chinese-homepage-googlecn-is-seen-on-a-computer-screen-in-27521926.html
Google's Chinese homepage, google.cn, is seen on a computer screen in New York Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-googles-chinese-homepage-googlecn-is-seen-on-a-computer-screen-in-27521926.htmlRMBGNMDX–Google's Chinese homepage, google.cn, is seen on a computer screen in New York
 Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118596.html
Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118596.htmlRMTA1684–Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China
 Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609191.html
Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609191.htmlRM2X57TKK–Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear
 US Commander of the Pacific Command Adm. Samuel Locklear III meets with People's Republic of China Deputy Chief of the General Staff Lt. Gen. Qi Jianguo during their bilateral discussion at the Shangri-La Dialogue June 2, 2013 in Singapore. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-us-commander-of-the-pacific-command-adm-samuel-locklear-iii-meets-57064812.html
US Commander of the Pacific Command Adm. Samuel Locklear III meets with People's Republic of China Deputy Chief of the General Staff Lt. Gen. Qi Jianguo during their bilateral discussion at the Shangri-La Dialogue June 2, 2013 in Singapore. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-us-commander-of-the-pacific-command-adm-samuel-locklear-iii-meets-57064812.htmlRMD8REN0–US Commander of the Pacific Command Adm. Samuel Locklear III meets with People's Republic of China Deputy Chief of the General Staff Lt. Gen. Qi Jianguo during their bilateral discussion at the Shangri-La Dialogue June 2, 2013 in Singapore.
 Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609192.html
Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-cyber-war-russia-china-cyber-security-cyber-attacks-worldwide-computer-crime-digital-it-attacks-economy-energy-economy-nuclear-image605609192.htmlRM2X57TKM–Symbolic image, cyber war Russia China, cyber security, cyber attacks worldwide, computer crime, digital IT attacks, economy, energy economy, nuclear
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013142.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013142.htmlRFC462HX–Photo illustration showing data and information streams representing national security and cyber crime
 Chinese state-owned telecommunications company China Telecom logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-state-owned-telecommunications-company-china-telecom-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837845.html
Chinese state-owned telecommunications company China Telecom logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-state-owned-telecommunications-company-china-telecom-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837845.htmlRMR519YH–Chinese state-owned telecommunications company China Telecom logo is seen on an Android mobile device with a figure of hacker in the background.
 Symbolic image, China cyber attacks, Huawai critical infrastructure, 5G networks, cyber security, worldwide, computer crime, digital IT attacks Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-china-cyber-attacks-huawai-critical-infrastructure-5g-networks-cyber-security-worldwide-computer-crime-digital-it-attacks-image545344986.html
Symbolic image, China cyber attacks, Huawai critical infrastructure, 5G networks, cyber security, worldwide, computer crime, digital IT attacks Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbolic-image-china-cyber-attacks-huawai-critical-infrastructure-5g-networks-cyber-security-worldwide-computer-crime-digital-it-attacks-image545344986.htmlRF2PK6H2J–Symbolic image, China cyber attacks, Huawai critical infrastructure, 5G networks, cyber security, worldwide, computer crime, digital IT attacks
 An open security lock and key on background of Industrial and Commercial Bank of China logo in mirror reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-open-security-lock-and-key-on-background-of-industrial-and-commercial-bank-of-china-logo-in-mirror-reflection-image458490188.html
An open security lock and key on background of Industrial and Commercial Bank of China logo in mirror reflection Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/an-open-security-lock-and-key-on-background-of-industrial-and-commercial-bank-of-china-logo-in-mirror-reflection-image458490188.htmlRF2HHX0WG–An open security lock and key on background of Industrial and Commercial Bank of China logo in mirror reflection
 China Piracy Pirate economy sea trade and money security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-china-piracy-pirate-economy-sea-trade-and-money-security-73569293.html
China Piracy Pirate economy sea trade and money security Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-china-piracy-pirate-economy-sea-trade-and-money-security-73569293.htmlRME7KAAN–China Piracy Pirate economy sea trade and money security
 Laptop with lock symbol on screen on background of Bank of China logo. Finger points to lock symbol. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-lock-symbol-on-screen-on-background-of-bank-of-china-logo-finger-points-to-lock-symbol-image458487616.html
Laptop with lock symbol on screen on background of Bank of China logo. Finger points to lock symbol. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-lock-symbol-on-screen-on-background-of-bank-of-china-logo-finger-points-to-lock-symbol-image458487616.htmlRF2HHWWHM–Laptop with lock symbol on screen on background of Bank of China logo. Finger points to lock symbol.
 Vancouver, CANADA - Jun 14 2023 : Twitter logo seen in an iPhone on Chinese flag background. Twitter and China concept image Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vancouver-canada-jun-14-2023-twitter-logo-seen-in-an-iphone-on-chinese-flag-background-twitter-and-china-concept-image-image555317020.html
Vancouver, CANADA - Jun 14 2023 : Twitter logo seen in an iPhone on Chinese flag background. Twitter and China concept image Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/vancouver-canada-jun-14-2023-twitter-logo-seen-in-an-iphone-on-chinese-flag-background-twitter-and-china-concept-image-image555317020.htmlRF2R7CTEM–Vancouver, CANADA - Jun 14 2023 : Twitter logo seen in an iPhone on Chinese flag background. Twitter and China concept image
 National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248421.html
National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248421.htmlRF2GPN7B1–National flags of China and United states of America on screens
 Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581867.html
Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581867.htmlRMHKKHEK–Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News
 View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263918053.html
View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263918053.htmlRMW9AE4N–View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S
 A cyber security concept with the countries of America and China overlayered over data and padlocks. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-cyber-security-concept-with-the-countries-of-america-and-china-overlayered-over-data-and-padlocks-image255523544.html
A cyber security concept with the countries of America and China overlayered over data and padlocks. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-cyber-security-concept-with-the-countries-of-america-and-china-overlayered-over-data-and-padlocks-image255523544.htmlRFTRM2TT–A cyber security concept with the countries of America and China overlayered over data and padlocks.
 Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616619.html
Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616619.htmlRF2KK250Y–Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit
 Flag of China on a computer binary codes falling from the top and fading away. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/flag-of-china-on-a-computer-binary-codes-falling-from-the-top-and-fading-away-image569447633.html
Flag of China on a computer binary codes falling from the top and fading away. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/flag-of-china-on-a-computer-binary-codes-falling-from-the-top-and-fading-away-image569447633.htmlRF2T2CG7D–Flag of China on a computer binary codes falling from the top and fading away.
 Computer chip with Chinese flag, 3d conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-chip-with-chinese-flag-3d-conceptual-illustration-image367365284.html
Computer chip with Chinese flag, 3d conceptual illustration. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-chip-with-chinese-flag-3d-conceptual-illustration-image367365284.htmlRF2C9JX4M–Computer chip with Chinese flag, 3d conceptual illustration.
 Close up image of a red printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-red-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961349.html
Close up image of a red printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-red-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961349.htmlRM2G60J3H–Close up image of a red printed circuit board with the words made china printed on it.
 Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118590.html
Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118590.htmlRMTA167X–Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China
 lanterns Macau China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lanterns-macau-china-image595244458.html
lanterns Macau China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lanterns-macau-china-image595244458.htmlRM2WGBMAJ–lanterns Macau China
 NSA USA Government Spy Program Country China Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-nsa-usa-government-spy-program-country-china-81327813.html
NSA USA Government Spy Program Country China Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-nsa-usa-government-spy-program-country-china-81327813.htmlRFEM8PCN–NSA USA Government Spy Program Country China
 Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103140.html
Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103140.htmlRF2B1CPG4–Woman hacker data breach China vs Russia cyber war
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013160.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013160.htmlRFC462JG–Photo illustration showing data and information streams representing national security and cyber crime
 Chinese insurance company China Pacific Insurance (CPIC) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-insurance-company-china-pacific-insurance-cpic-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837747.html
Chinese insurance company China Pacific Insurance (CPIC) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-insurance-company-china-pacific-insurance-cpic-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837747.htmlRMR519T3–Chinese insurance company China Pacific Insurance (CPIC) logo is seen on an Android mobile device with a figure of hacker in the background.
 COVID-19 hacking symbol with skull and binary code in background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/covid-19-hacking-symbol-with-skull-and-binary-code-in-background-image349059883.html
COVID-19 hacking symbol with skull and binary code in background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/covid-19-hacking-symbol-with-skull-and-binary-code-in-background-image349059883.htmlRF2B7W1CB–COVID-19 hacking symbol with skull and binary code in background
 On a yellow surface, an open lock with the image of the flag of China and a sticker with the inscription - hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/on-a-yellow-surface-an-open-lock-with-the-image-of-the-flag-of-china-and-a-sticker-with-the-inscription-hacked-image545309319.html
On a yellow surface, an open lock with the image of the flag of China and a sticker with the inscription - hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/on-a-yellow-surface-an-open-lock-with-the-image-of-the-flag-of-china-and-a-sticker-with-the-inscription-hacked-image545309319.htmlRF2PK4YGR–On a yellow surface, an open lock with the image of the flag of China and a sticker with the inscription - hacked
 23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/23-april-2024-symbolic-image-of-china-espionage-in-germany-computer-screen-with-china-flag-and-a-spy-symbol-photomontage-symbolbild-china-spionage-in-deutschland-computerbildschirm-mit-china-flagge-udn-einem-spion-symbol-fotomontage-image604030240.html
23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/23-april-2024-symbolic-image-of-china-espionage-in-germany-computer-screen-with-china-flag-and-a-spy-symbol-photomontage-symbolbild-china-spionage-in-deutschland-computerbildschirm-mit-china-flagge-udn-einem-spion-symbol-fotomontage-image604030240.htmlRM2X2KXMG–23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE
 Tibetan laborers between Thong La Pass and Nyalam, Friendship Highway, Tibet, China, Asia Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/tibetan-laborers-between-thong-la-pass-and-nyalam-friendship-highway-image61821164.html
Tibetan laborers between Thong La Pass and Nyalam, Friendship Highway, Tibet, China, Asia Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/tibetan-laborers-between-thong-la-pass-and-nyalam-friendship-highway-image61821164.htmlRMDGG5EM–Tibetan laborers between Thong La Pass and Nyalam, Friendship Highway, Tibet, China, Asia
RF2R7CT54–Vancouver, CANADA - Jun 14 2023 : Twitter icon seen in an iPhone on Chinese flag background. Twitter and China concept image
 National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248420.html
National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248420.htmlRF2GPN7B0–National flags of China and United states of America on screens
 Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581890.html
Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581890.htmlRMHKKHFE–Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News
 View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263918094.html
View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/view-of-the-headquarters-of-google-china-in-beijing-china-january-13-2010-googles-threat-to-quit-china-over-censorship-and-hacking-intensified-s-image263918094.htmlRMW9AE66–View of the headquarters of Google China in Beijing, China, January 13, 2010. Googles threat to quit China over censorship and hacking intensified S
 China hacking concept of a computer keyboard and a key painted with the flag of China and the text 'hack' Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-hacking-concept-of-a-computer-keyboard-and-a-key-painted-with-the-flag-of-china-and-the-text-hack-image478022682.html
China hacking concept of a computer keyboard and a key painted with the flag of China and the text 'hack' Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-hacking-concept-of-a-computer-keyboard-and-a-key-painted-with-the-flag-of-china-and-the-text-hack-image478022682.htmlRM2JNKPPJ–China hacking concept of a computer keyboard and a key painted with the flag of China and the text 'hack'
 Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616633.html
Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616633.htmlRF2KK251D–Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit
 Porto, Portugal. 18th Mar, 2019. Matrix code is seen on an android mobile phone with China flag on the background. Credit: Omar Marques/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/porto-portugal-18th-mar-2019-matrix-code-is-seen-on-an-android-mobile-phone-with-china-flag-on-the-background-credit-omar-marquessopa-imageszuma-wirealamy-live-news-image241105814.html
Porto, Portugal. 18th Mar, 2019. Matrix code is seen on an android mobile phone with China flag on the background. Credit: Omar Marques/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/porto-portugal-18th-mar-2019-matrix-code-is-seen-on-an-android-mobile-phone-with-china-flag-on-the-background-credit-omar-marquessopa-imageszuma-wirealamy-live-news-image241105814.htmlRMT078WX–Porto, Portugal. 18th Mar, 2019. Matrix code is seen on an android mobile phone with China flag on the background. Credit: Omar Marques/SOPA Images/ZUMA Wire/Alamy Live News
 Computer keyboards, cabling, binary codes etc.. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-keyboards-cabling-binary-codes-etc-image395726508.html
Computer keyboards, cabling, binary codes etc.. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-keyboards-cabling-binary-codes-etc-image395726508.htmlRF2DYPW5G–Computer keyboards, cabling, binary codes etc..
 Close up image of a red printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-red-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961351.html
Close up image of a red printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-red-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961351.htmlRM2G60J3K–Close up image of a red printed circuit board with the words made china printed on it.
 Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118597.html
Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118597.htmlRMTA1685–Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China
 lanterns Macau China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lanterns-macau-china-image595244448.html
lanterns Macau China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lanterns-macau-china-image595244448.htmlRM2WGBMA8–lanterns Macau China
 Hong Kong, China. 23rd Nov, 2018. China Mobile logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hong-kong-china-23rd-nov-2018-china-mobile-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-credit-miguel-candelasopa-imageszuma-wirealamy-live-news-image226801775.html
Hong Kong, China. 23rd Nov, 2018. China Mobile logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hong-kong-china-23rd-nov-2018-china-mobile-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-credit-miguel-candelasopa-imageszuma-wirealamy-live-news-image226801775.htmlRMR4YKYB–Hong Kong, China. 23rd Nov, 2018. China Mobile logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News
 Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103056.html
Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103056.htmlRF2B1CPD4–Woman hacker data breach China vs Russia cyber war
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013319.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37013319.htmlRFC462T7–Photo illustration showing data and information streams representing national security and cyber crime
 Chinese multinational banking company Industrial and Commercial Bank of China (ICBC) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-multinational-banking-company-industrial-and-commercial-bank-of-china-icbc-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837941.html
Chinese multinational banking company Industrial and Commercial Bank of China (ICBC) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-multinational-banking-company-industrial-and-commercial-bank-of-china-icbc-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837941.htmlRMR51A31–Chinese multinational banking company Industrial and Commercial Bank of China (ICBC) logo is seen on an Android mobile device with a figure of hacker in the background.
 Warning sign to be aware to protect intellectual properties Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/warning-sign-to-be-aware-to-protect-intellectual-properties-image227087488.html
Warning sign to be aware to protect intellectual properties Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/warning-sign-to-be-aware-to-protect-intellectual-properties-image227087488.htmlRFR5CMBC–Warning sign to be aware to protect intellectual properties
 Cyber Security Title with China flag - 3D Illustration fabric texture Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-title-with-china-flag-3d-illustration-fabric-texture-image434228951.html
Cyber Security Title with China flag - 3D Illustration fabric texture Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-title-with-china-flag-3d-illustration-fabric-texture-image434228951.htmlRF2G6CRCR–Cyber Security Title with China flag - 3D Illustration fabric texture
 23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/23-april-2024-symbolic-image-of-china-espionage-in-germany-computer-screen-with-china-flag-and-a-spy-symbol-photomontage-symbolbild-china-spionage-in-deutschland-computerbildschirm-mit-china-flagge-udn-einem-spion-symbol-fotomontage-image604030249.html
23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/23-april-2024-symbolic-image-of-china-espionage-in-germany-computer-screen-with-china-flag-and-a-spy-symbol-photomontage-symbolbild-china-spionage-in-deutschland-computerbildschirm-mit-china-flagge-udn-einem-spion-symbol-fotomontage-image604030249.htmlRM2X2KXMW–23 April 2024: Symbolic image of China espionage in Germany. Computer screen with China flag and a spy symbol. PHOTOMONTAGE *** Symbolbild China Spionage in Deutschland. Computerbildschirm mit China Flagge udn einem Spion Symbol. FOTOMONTAGE
 Wind-up clockwork toy robot on Chinese flag. For Chinese bots influencing US elections, advances in Chinese AI, China troll farm, China AI. Copy space Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/wind-up-clockwork-toy-robot-on-chinese-flag-for-chinese-bots-influencing-us-elections-advances-in-chinese-ai-china-troll-farm-china-ai-copy-space-image376336612.html
Wind-up clockwork toy robot on Chinese flag. For Chinese bots influencing US elections, advances in Chinese AI, China troll farm, China AI. Copy space Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/wind-up-clockwork-toy-robot-on-chinese-flag-for-chinese-bots-influencing-us-elections-advances-in-chinese-ai-china-troll-farm-china-ai-copy-space-image376336612.htmlRM2CT7H58–Wind-up clockwork toy robot on Chinese flag. For Chinese bots influencing US elections, advances in Chinese AI, China troll farm, China AI. Copy space
 Print left palm hand with binary code and inscription hacker China.Concept information warfare Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/print-left-palm-hand-with-binary-code-and-inscription-hacker-chinaconcept-information-warfare-image455342019.html
Print left palm hand with binary code and inscription hacker China.Concept information warfare Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/print-left-palm-hand-with-binary-code-and-inscription-hacker-chinaconcept-information-warfare-image455342019.htmlRF2HCPHAY–Print left palm hand with binary code and inscription hacker China.Concept information warfare
 National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248413.html
National flags of China and United states of America on screens Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/national-flags-of-china-and-united-states-of-america-on-screens-image444248413.htmlRF2GPN7AN–National flags of China and United states of America on screens
 Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581870.html
Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-tokyo-japan-28th-jan-2017-some-90-contestants-in-24-teams-from-nine-132581870.htmlRMHKKHEP–Tokyo, Japan. 28th Jan, 2017. Some 90 contestants in 24 teams from nine nations from China, Japan, Poland, Russia, South Korea, Taiwan, United States, France and Switzerland compete in their hacking skills at the final rounds of the Security Contest, SECCON at the Tokyo Denki University in Tokyo on Saturday, January 28, 2017. A two-day cyber security competition started in Tokyo to find talented young cyber security engineers. Credit: Yoshio Tsunoda/AFLO/Alamy Live News
 Qihoo 360 Chinese antivirus firm logo on the glowing smartphone screen and finger points on it. Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/qihoo-360-chinese-antivirus-firm-logo-on-the-glowing-smartphone-screen-and-finger-points-on-it-concept-image345990758.html
Qihoo 360 Chinese antivirus firm logo on the glowing smartphone screen and finger points on it. Concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/qihoo-360-chinese-antivirus-firm-logo-on-the-glowing-smartphone-screen-and-finger-points-on-it-concept-image345990758.htmlRF2B2W6MP–Qihoo 360 Chinese antivirus firm logo on the glowing smartphone screen and finger points on it. Concept.
 China flag and modern backlit computer mouse. Concept of country representing e-sports team Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-flag-and-modern-backlit-computer-mouse-concept-of-country-representing-e-sports-team-image236828975.html
China flag and modern backlit computer mouse. Concept of country representing e-sports team Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/china-flag-and-modern-backlit-computer-mouse-concept-of-country-representing-e-sports-team-image236828975.htmlRFRN8DNK–China flag and modern backlit computer mouse. Concept of country representing e-sports team
 Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616608.html
Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/headline-news-across-international-media-with-cyberwarfare-cyber-attack-security-and-war-abstract-concept-of-news-titles-on-noise-displays-tv-glit-image493616608.htmlRF2KK250G–Headline news across international media with Cyberwarfare, cyber attack, security and war. Abstract concept of news titles on noise displays. TV glit
 Computer Keyboard Key with China Flag and text 'CHINA' Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-keyboard-key-with-china-flag-and-text-china-image478022653.html
Computer Keyboard Key with China Flag and text 'CHINA' Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-keyboard-key-with-china-flag-and-text-china-image478022653.htmlRM2JNKPNH–Computer Keyboard Key with China Flag and text 'CHINA'
 hacker scam phishing attack during covid19 coronavirus pandemic cyber security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-scam-phishing-attack-during-covid19-coronavirus-pandemic-cyber-security-concept-image355755804.html
hacker scam phishing attack during covid19 coronavirus pandemic cyber security concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-scam-phishing-attack-during-covid19-coronavirus-pandemic-cyber-security-concept-image355755804.htmlRF2BJP24C–hacker scam phishing attack during covid19 coronavirus pandemic cyber security concept
 Close up image of a purple printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-purple-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961318.html
Close up image of a purple printed circuit board with the words made china printed on it. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/close-up-image-of-a-purple-printed-circuit-board-with-the-words-made-china-printed-on-it-image433961318.htmlRM2G60J2E–Close up image of a purple printed circuit board with the words made china printed on it.
 Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118593.html
Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/huawei-mobile-cell-phone-using-google-apps-huawei-was-founded-in-1987-in-shenzhen-china-image247118593.htmlRMTA1681–Huawei Mobile Cell Phone using Google apps, Huawei was founded in 1987 in Shenzhen, China
 Chinese trade policy threatening American companies Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-trade-policy-threatening-american-companies-image210508281.html
Chinese trade policy threatening American companies Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-trade-policy-threatening-american-companies-image210508281.htmlRFP6DDCW–Chinese trade policy threatening American companies
 Hong Kong. 23rd Nov, 2018. Chinese banking company Agricultural Bank of China logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hong-kong-23rd-nov-2018-chinese-banking-company-agricultural-bank-of-china-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-credit-miguel-candelasopa-imageszuma-wirealamy-live-news-image228161139.html
Hong Kong. 23rd Nov, 2018. Chinese banking company Agricultural Bank of China logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hong-kong-23rd-nov-2018-chinese-banking-company-agricultural-bank-of-china-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-credit-miguel-candelasopa-imageszuma-wirealamy-live-news-image228161139.htmlRMR75HT3–Hong Kong. 23rd Nov, 2018. Chinese banking company Agricultural Bank of China logo is seen on an Android mobile device with a figure of hacker in the background. Credit: Miguel Candela/SOPA Images/ZUMA Wire/Alamy Live News
 Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103147.html
Woman hacker data breach China vs Russia cyber war Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-hacker-data-breach-china-vs-russia-cyber-war-image345103147.htmlRF2B1CPGB–Woman hacker data breach China vs Russia cyber war
 Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37012425.html
Photo illustration showing data and information streams representing national security and cyber crime Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-photo-illustration-showing-data-and-information-streams-representing-37012425.htmlRFC461M9–Photo illustration showing data and information streams representing national security and cyber crime
 Chinese multinational banking company China Construction Bank Corporation (CCB) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-multinational-banking-company-china-construction-bank-corporation-ccb-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837937.html
Chinese multinational banking company China Construction Bank Corporation (CCB) logo is seen on an Android mobile device with a figure of hacker in the background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/chinese-multinational-banking-company-china-construction-bank-corporation-ccb-logo-is-seen-on-an-android-mobile-device-with-a-figure-of-hacker-in-the-background-image226837937.htmlRMR51A2W–Chinese multinational banking company China Construction Bank Corporation (CCB) logo is seen on an Android mobile device with a figure of hacker in the background.
Search Results for China hacking Stock Photos and Images (502)
Page 1 of 6
