Quick filters:
Malware Stock Photos and Images
 Computer code on a screen with a skull representing a computer virus / malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-code-on-a-screen-with-a-skull-representing-a-computer-virus-177629036.html
Computer code on a screen with a skull representing a computer virus / malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-code-on-a-screen-with-a-skull-representing-a-computer-virus-177629036.htmlRFM8YKJ4–Computer code on a screen with a skull representing a computer virus / malware attack.
 Security breach warning on smartphone screen, device infected by internet virus or malware after cyberattack by hacker, fraud alert with red padlock i Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-warning-on-smartphone-screen-device-infected-by-internet-virus-or-malware-after-cyberattack-by-hacker-fraud-alert-with-red-padlock-i-image185067426.html
Security breach warning on smartphone screen, device infected by internet virus or malware after cyberattack by hacker, fraud alert with red padlock i Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/security-breach-warning-on-smartphone-screen-device-infected-by-internet-virus-or-malware-after-cyberattack-by-hacker-fraud-alert-with-red-padlock-i-image185067426.htmlRFMN2FAX–Security breach warning on smartphone screen, device infected by internet virus or malware after cyberattack by hacker, fraud alert with red padlock i
 computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image368546048.html
computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image368546048.htmlRF2CBGM6T–computer virus malware attack. computer code on a screen with a skull symbol
 Malware Ahead Refers to Malicious Danger for Computer Future Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-ahead-refers-to-malicious-danger-for-computer-future-122413777.html
Malware Ahead Refers to Malicious Danger for Computer Future Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-ahead-refers-to-malicious-danger-for-computer-future-122413777.htmlRFH34C0H–Malware Ahead Refers to Malicious Danger for Computer Future
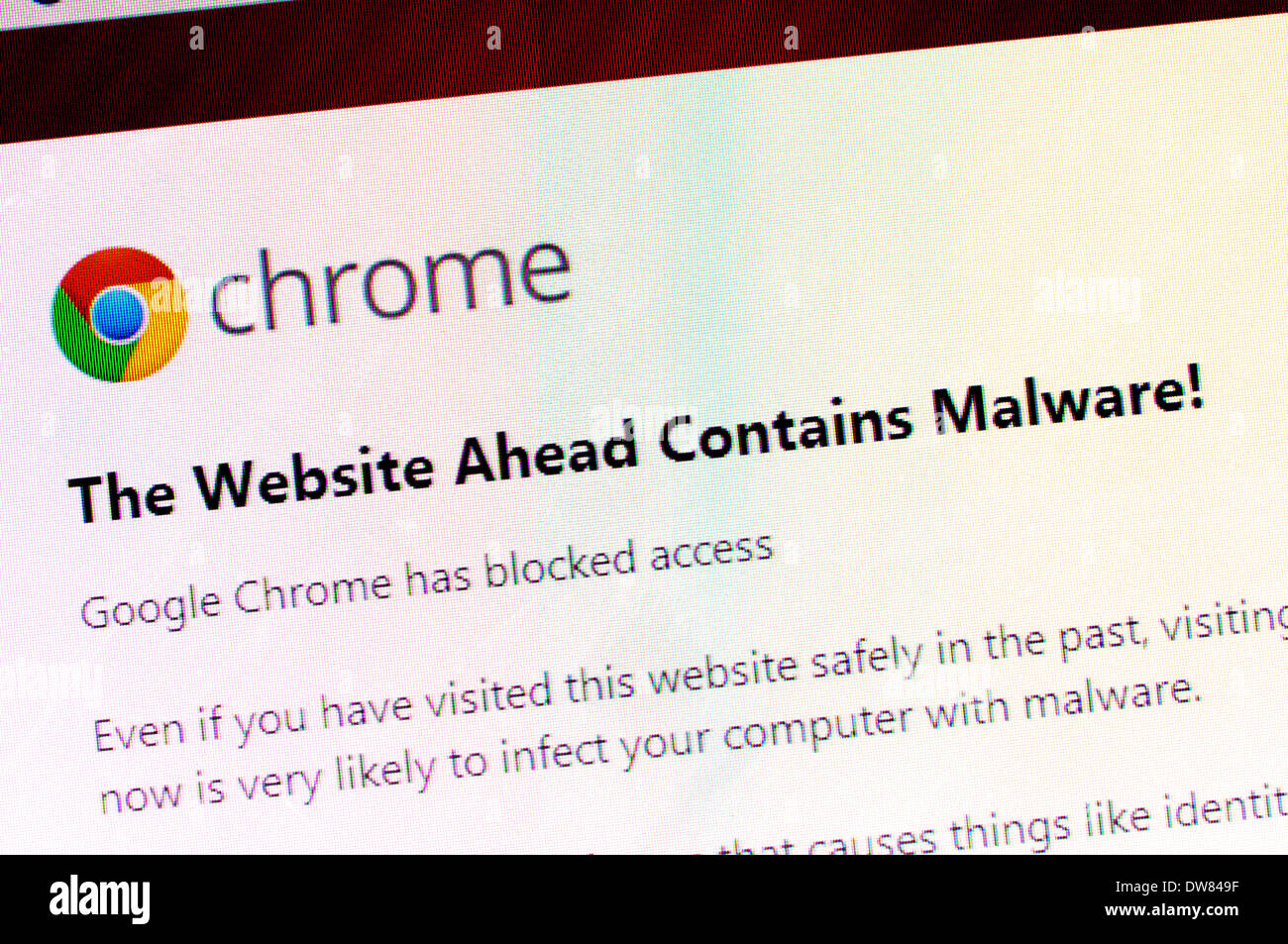 Computer screen shot: Malware warning from Google Chrome Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-screen-shot-malware-warning-from-google-chrome-image67176523.html
Computer screen shot: Malware warning from Google Chrome Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-screen-shot-malware-warning-from-google-chrome-image67176523.htmlRMDW849F–Computer screen shot: Malware warning from Google Chrome
 malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146770778.html
malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146770778.htmlRFJENYHE–malware or ransomware attack concept padlock with money, clipping path, 3d illustration
 Concept of hacking or phishing a login and password with malware program Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-hacking-or-phishing-a-login-and-password-with-malware-program-image60189329.html
Concept of hacking or phishing a login and password with malware program Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-hacking-or-phishing-a-login-and-password-with-malware-program-image60189329.htmlRFDDWT2W–Concept of hacking or phishing a login and password with malware program
 Red Malware and Binary code, Concept Security Malware and RansomWare attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-red-malware-and-binary-code-concept-security-malware-and-ransomware-144748372.html
Red Malware and Binary code, Concept Security Malware and RansomWare attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-red-malware-and-binary-code-concept-security-malware-and-ransomware-144748372.htmlRFJBDT0M–Red Malware and Binary code, Concept Security Malware and RansomWare attack.
 Ransomware Malware Attack And Breach. Business Computer Hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-business-computer-hacked-image477078601.html
Ransomware Malware Attack And Breach. Business Computer Hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-business-computer-hacked-image477078601.htmlRF2JM4PHD–Ransomware Malware Attack And Breach. Business Computer Hacked
 Spyware Computer Hacker Virus Malware Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-spyware-computer-hacker-virus-malware-concept-126073704.html
Spyware Computer Hacker Virus Malware Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-spyware-computer-hacker-virus-malware-concept-126073704.htmlRFH93488–Spyware Computer Hacker Virus Malware Concept
 Malware against green and black circuit board Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-against-green-and-black-circuit-board-image67342671.html
Malware against green and black circuit board Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-against-green-and-black-circuit-board-image67342671.htmlRFDWFM7B–Malware against green and black circuit board
 Computer virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-image68358771.html
Computer virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-image68358771.htmlRFDY608K–Computer virus
 Concept image of a hooded cyber criminal lurking behind lines of digital binary code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-image-of-a-hooded-cyber-criminal-lurking-behind-lines-of-digital-binary-code-image332401824.html
Concept image of a hooded cyber criminal lurking behind lines of digital binary code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-image-of-a-hooded-cyber-criminal-lurking-behind-lines-of-digital-binary-code-image332401824.htmlRM2A8P5WM–Concept image of a hooded cyber criminal lurking behind lines of digital binary code
 Human skull behind binary digital code software. Malware Virus Cyber threat concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/human-skull-behind-binary-digital-code-software-malware-virus-cyber-threat-concept-image241722943.html
Human skull behind binary digital code software. Malware Virus Cyber threat concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/human-skull-behind-binary-digital-code-software-malware-virus-cyber-threat-concept-image241722943.htmlRFT17C27–Human skull behind binary digital code software. Malware Virus Cyber threat concept
 Methods of cyber attack in computer machine code including virus, worm, Trojan horse, malware and spyware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-methods-of-cyber-attack-in-computer-machine-code-including-virus-worm-32664057.html
Methods of cyber attack in computer machine code including virus, worm, Trojan horse, malware and spyware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-methods-of-cyber-attack-in-computer-machine-code-including-virus-worm-32664057.htmlRFBW3Y9D–Methods of cyber attack in computer machine code including virus, worm, Trojan horse, malware and spyware
 Hacker and malware computer software. Fraud website code in screen. Programmer developing web security with laptop. Data privacy hacking. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-and-malware-computer-software-fraud-website-code-in-screen-programmer-developing-web-security-with-laptop-data-privacy-hacking-image571175241.html
Hacker and malware computer software. Fraud website code in screen. Programmer developing web security with laptop. Data privacy hacking. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-and-malware-computer-software-fraud-website-code-in-screen-programmer-developing-web-security-with-laptop-data-privacy-hacking-image571175241.htmlRF2T577RN–Hacker and malware computer software. Fraud website code in screen. Programmer developing web security with laptop. Data privacy hacking.
 Concept internet crime images, malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-internet-crime-images-malware-image333940435.html
Concept internet crime images, malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-internet-crime-images-malware-image333940435.htmlRM2AB88C3–Concept internet crime images, malware.
 Computer Bug Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-bug-34600402.html
Computer Bug Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-computer-bug-34600402.htmlRMC0854J–Computer Bug
 Laptop with binary numbers on screen. Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-binary-numbers-on-screen-symbol-image-malware-virus-alarm-computer-crime-data-protection-baden-wrttemberg-image233941498.html
Laptop with binary numbers on screen. Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-with-binary-numbers-on-screen-symbol-image-malware-virus-alarm-computer-crime-data-protection-baden-wrttemberg-image233941498.htmlRMRGGXNE–Laptop with binary numbers on screen. Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg
 Cyber security, antivirus, hackers and malware concepts with secure laptop at center Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cyber-security-antivirus-hackers-and-malware-concepts-with-secure-174470332.html
Cyber security, antivirus, hackers and malware concepts with secure laptop at center Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cyber-security-antivirus-hackers-and-malware-concepts-with-secure-174470332.htmlRFM3RPK8–Cyber security, antivirus, hackers and malware concepts with secure laptop at center
 Virus on laptop, malware or network vulnerability vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-on-laptop-malware-or-network-vulnerability-vector-image342179100.html
Virus on laptop, malware or network vulnerability vector Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-on-laptop-malware-or-network-vulnerability-vector-image342179100.htmlRF2ATKGX4–Virus on laptop, malware or network vulnerability vector
 computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image249312087.html
computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image249312087.htmlRFTDH433–computer virus malware attack. computer code on a screen with a skull symbol
 Ransomware concept and infecting computers with hacker malware as a cybersecurityor internet security symbol. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-concept-and-infecting-computers-with-hacker-malware-as-a-cybersecurityor-internet-security-symbol-image434483591.html
Ransomware concept and infecting computers with hacker malware as a cybersecurityor internet security symbol. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-concept-and-infecting-computers-with-hacker-malware-as-a-cybersecurityor-internet-security-symbol-image434483591.htmlRF2G6TC73–Ransomware concept and infecting computers with hacker malware as a cybersecurityor internet security symbol.
 malware detected alert on a digital tablet with a cup of tea Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-detected-alert-on-a-digital-tablet-with-a-cup-of-tea-image69223064.html
malware detected alert on a digital tablet with a cup of tea Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-detected-alert-on-a-digital-tablet-with-a-cup-of-tea-image69223064.htmlRFE0HAM8–malware detected alert on a digital tablet with a cup of tea
 Email virus. Envelope with malware message with skull on laptop screen. E-mail spam, phishing scam and hacker attack vector concept. Spam threat on laptop, virus online malware illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-virus-envelope-with-malware-message-with-skull-on-laptop-screen-e-mail-spam-phishing-scam-and-hacker-attack-vector-concept-spam-threat-on-laptop-virus-online-malware-illustration-image357376802.html
Email virus. Envelope with malware message with skull on laptop screen. E-mail spam, phishing scam and hacker attack vector concept. Spam threat on laptop, virus online malware illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/email-virus-envelope-with-malware-message-with-skull-on-laptop-screen-e-mail-spam-phishing-scam-and-hacker-attack-vector-concept-spam-threat-on-laptop-virus-online-malware-illustration-image357376802.htmlRF2BNBWN6–Email virus. Envelope with malware message with skull on laptop screen. E-mail spam, phishing scam and hacker attack vector concept. Spam threat on laptop, virus online malware illustration
 Keyboard with the word malware elevated Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-keyboard-with-the-word-malware-elevated-91683352.html
Keyboard with the word malware elevated Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-keyboard-with-the-word-malware-elevated-91683352.htmlRFF94F1C–Keyboard with the word malware elevated
 A keyboard with a red button Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-a-keyboard-with-a-red-button-malware-104314088.html
A keyboard with a red button Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-a-keyboard-with-a-red-button-malware-104314088.htmlRFG1KWK4–A keyboard with a red button Malware
 Vector illustration of malware abstract concept with magnifying Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-vector-illustration-of-malware-abstract-concept-with-magnifying-83117428.html
Vector illustration of malware abstract concept with magnifying Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-vector-illustration-of-malware-abstract-concept-with-magnifying-83117428.htmlRFER693G–Vector illustration of malware abstract concept with magnifying
 Hands in the dark hold a tablet with an inscription malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hands-in-the-dark-hold-a-tablet-with-an-inscription-malware-image471213531.html
Hands in the dark hold a tablet with an inscription malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hands-in-the-dark-hold-a-tablet-with-an-inscription-malware-image471213531.htmlRF2JAHHJK–Hands in the dark hold a tablet with an inscription malware.
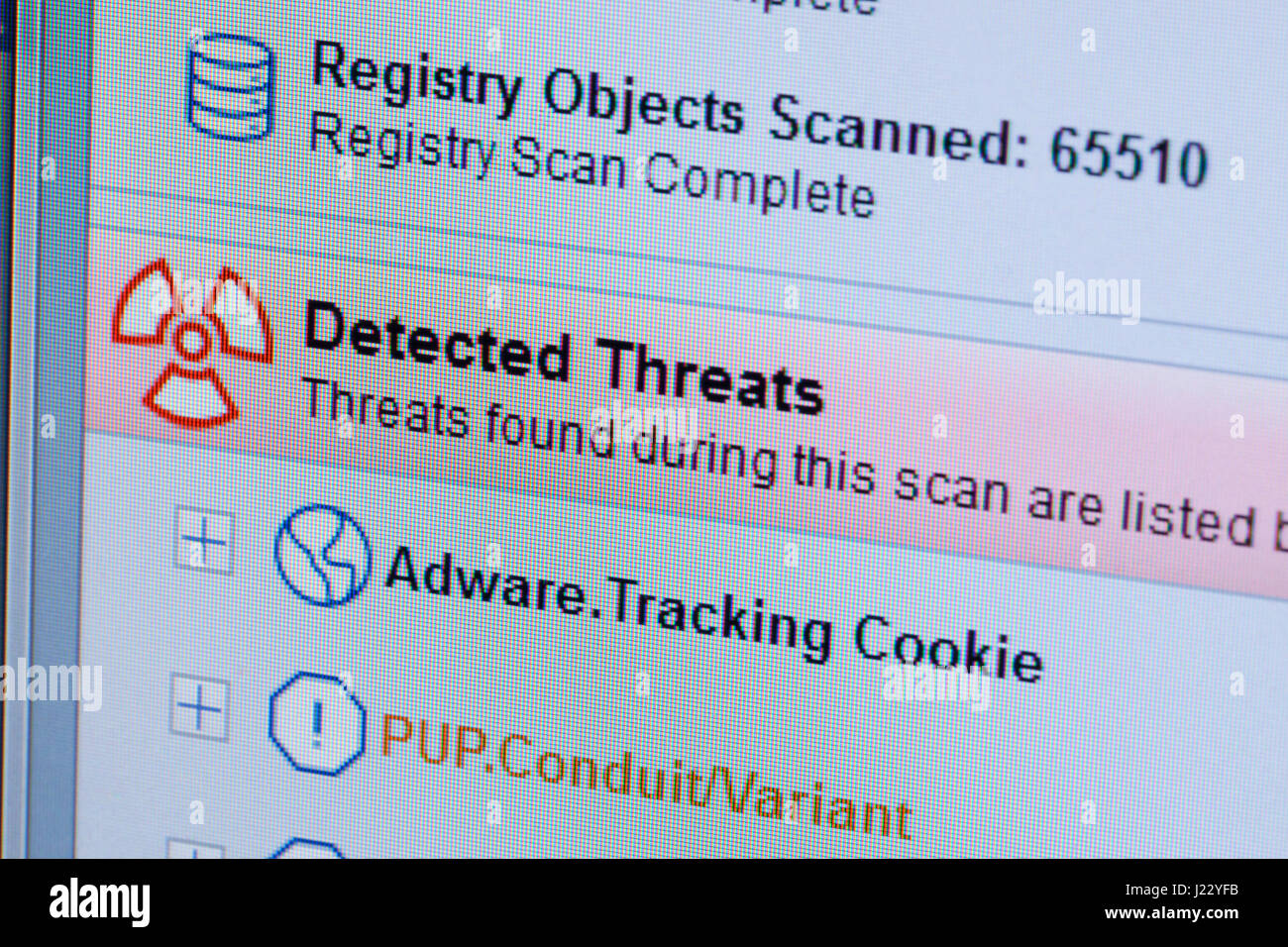 Adware / Malware scanner result on computer screen - USA Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-adware-malware-scanner-result-on-computer-screen-usa-138977759.html
Adware / Malware scanner result on computer screen - USA Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-adware-malware-scanner-result-on-computer-screen-usa-138977759.htmlRMJ22YFB–Adware / Malware scanner result on computer screen - USA
 cyber attcak phishing malware concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attcak-phishing-malware-concept-image400002645.html
cyber attcak phishing malware concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-attcak-phishing-malware-concept-image400002645.htmlRF2E6NKCN–cyber attcak phishing malware concept
 malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146777494.html
malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146777494.htmlRFJEP85A–malware or ransomware attack concept padlock with money, clipping path, 3d illustration
 Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-71963484.html
Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-71963484.htmlRFE5264C–Malware
 Opened email and malware laptop Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-opened-email-and-malware-laptop-147170850.html
Opened email and malware laptop Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-opened-email-and-malware-laptop-147170850.htmlRFJFC5WP–Opened email and malware laptop
 Hacker with malware software code in computer screen. Developing fraud website. Cybersecurity attack and web crime with laptop. Cyber security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-with-malware-software-code-in-computer-screen-developing-fraud-website-cybersecurity-attack-and-web-crime-with-laptop-cyber-security-image505585442.html
Hacker with malware software code in computer screen. Developing fraud website. Cybersecurity attack and web crime with laptop. Cyber security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-with-malware-software-code-in-computer-screen-developing-fraud-website-cybersecurity-attack-and-web-crime-with-laptop-cyber-security-image505585442.htmlRF2MAFBAX–Hacker with malware software code in computer screen. Developing fraud website. Cybersecurity attack and web crime with laptop. Cyber security.
RF2D8D53Y–Trojan attack, computer virus, cyber security, malware, crime and spying software technology icon. Abstract 3d symbol concept rendering illustration.
 The RansomWare and Binary code, RansomWare Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-ransomware-and-binary-code-ransomware-concept-security-and-malware-141866944.html
The RansomWare and Binary code, RansomWare Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-ransomware-and-binary-code-ransomware-concept-security-and-malware-141866944.htmlRFJ6PGMG–The RansomWare and Binary code, RansomWare Concept Security and Malware attack.
 Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg, Germany Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbol-image-malware-virus-alarm-computer-crime-data-protection-baden-wrttemberg-germany-image233941511.html
Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg, Germany Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symbol-image-malware-virus-alarm-computer-crime-data-protection-baden-wrttemberg-germany-image233941511.htmlRMRGGXNY–Symbol image malware, virus alarm, computer crime, data protection, Baden-Württemberg, Germany
 Ransomware Malware Attack And Breach Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-image483263176.html
Ransomware Malware Attack And Breach Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-image483263176.htmlRF2K26F34–Ransomware Malware Attack And Breach
 A server hardware showing MALWARE DETECTED and SCANNING Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-server-hardware-showing-malware-detected-and-scanning-image605927902.html
A server hardware showing MALWARE DETECTED and SCANNING Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-server-hardware-showing-malware-detected-and-scanning-image605927902.htmlRF2X5PB66–A server hardware showing MALWARE DETECTED and SCANNING
 computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image363658172.html
computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image363658172.htmlRF2C3J1KT–computer virus malware attack. computer code on a screen with a skull symbol
 Concept of a hacker as a cyber criminal hacking software or a hack and malware technology crime symbol and computer virus destroying data. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-a-hacker-as-a-cyber-criminal-hacking-software-or-a-hack-and-malware-technology-crime-symbol-and-computer-virus-destroying-data-image329029597.html
Concept of a hacker as a cyber criminal hacking software or a hack and malware technology crime symbol and computer virus destroying data. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/concept-of-a-hacker-as-a-cyber-criminal-hacking-software-or-a-hack-and-malware-technology-crime-symbol-and-computer-virus-destroying-data-image329029597.htmlRF2A38GH1–Concept of a hacker as a cyber criminal hacking software or a hack and malware technology crime symbol and computer virus destroying data.
 Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126103222.html
Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126103222.htmlRFH94DXE–Scam Virus Spyware Malware Antivirus Concept
 Laptop virus alert, hacker attack. Office panic due to hacker attack on computer vector illustration. Alert virus, malware and phishing crime Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-virus-alert-hacker-attack-office-panic-due-to-hacker-attack-on-computer-vector-illustration-alert-virus-malware-and-phishing-crime-image383399924.html
Laptop virus alert, hacker attack. Office panic due to hacker attack on computer vector illustration. Alert virus, malware and phishing crime Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-virus-alert-hacker-attack-office-panic-due-to-hacker-attack-on-computer-vector-illustration-alert-virus-malware-and-phishing-crime-image383399924.htmlRF2D7NAEC–Laptop virus alert, hacker attack. Office panic due to hacker attack on computer vector illustration. Alert virus, malware and phishing crime
 Teenage Hacker Working with His Computer Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit and Has Multiple displays. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/teenage-hacker-working-with-his-computer-infecting-servers-and-infrastructure-with-malware-his-hideout-is-dark-neon-lit-and-has-multiple-displays-image177830405.html
Teenage Hacker Working with His Computer Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit and Has Multiple displays. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/teenage-hacker-working-with-his-computer-infecting-servers-and-infrastructure-with-malware-his-hideout-is-dark-neon-lit-and-has-multiple-displays-image177830405.htmlRFM98TDW–Teenage Hacker Working with His Computer Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit and Has Multiple displays.
 People's fingers are pressing on the phone screen. Represents protection against external hacks, code protection security concepts, viruses, firmware and malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/peoples-fingers-are-pressing-on-the-phone-screen-represents-protection-against-external-hacks-code-protection-security-concepts-viruses-firmware-and-malware-image548228765.html
People's fingers are pressing on the phone screen. Represents protection against external hacks, code protection security concepts, viruses, firmware and malware. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/peoples-fingers-are-pressing-on-the-phone-screen-represents-protection-against-external-hacks-code-protection-security-concepts-viruses-firmware-and-malware-image548228765.htmlRF2PRWYAN–People's fingers are pressing on the phone screen. Represents protection against external hacks, code protection security concepts, viruses, firmware and malware.
 Malware with matrix is shown by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-with-matrix-is-shown-by-businessman-115229869.html
Malware with matrix is shown by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-with-matrix-is-shown-by-businessman-115229869.htmlRFGKD4TD–Malware with matrix is shown by businessman.
 Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718408.html
Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718408.htmlRFHJ884T–Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words.
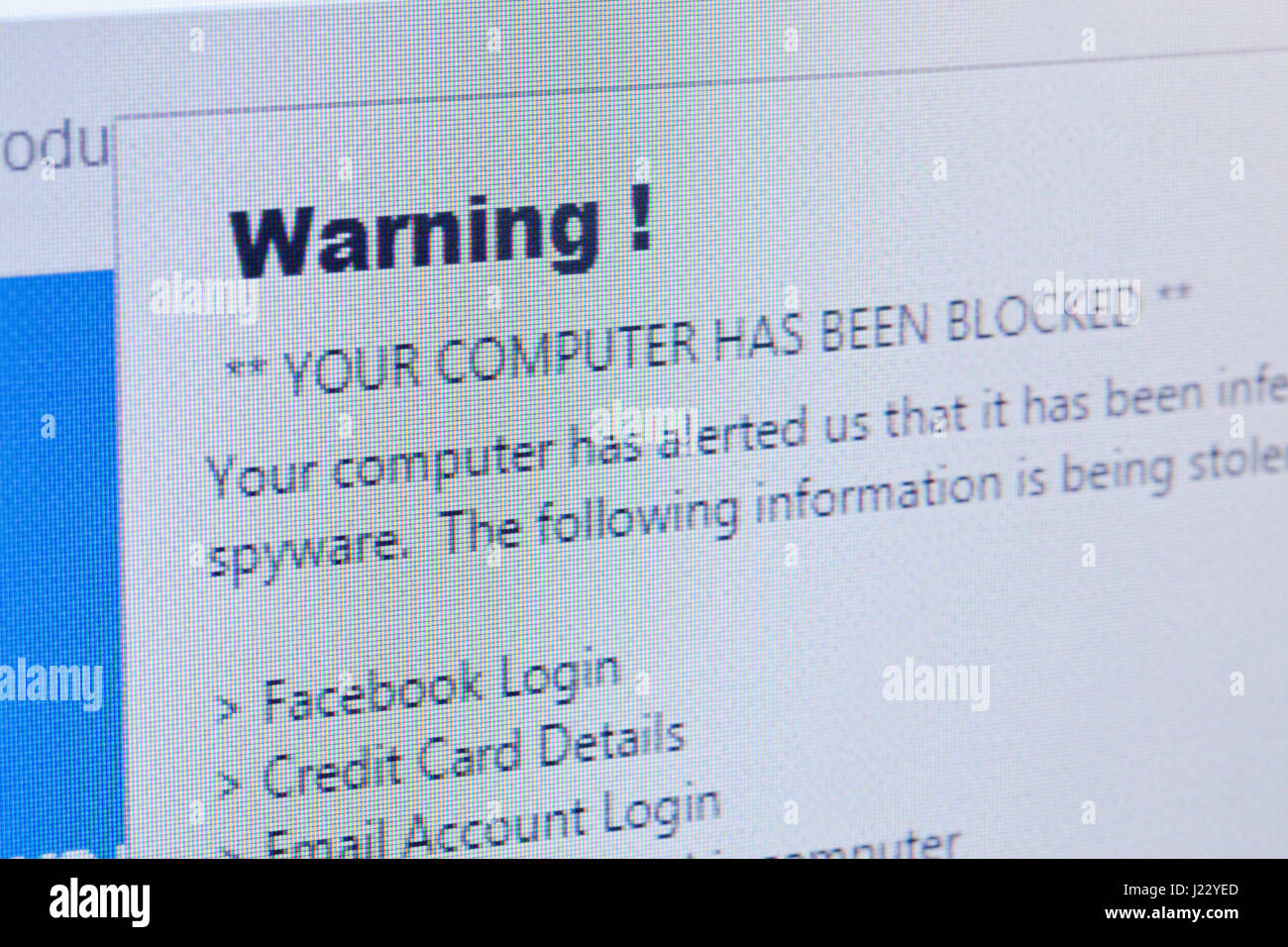 Malware (spyware) warning message on computer screen - USA Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-spyware-warning-message-on-computer-screen-usa-138977733.html
Malware (spyware) warning message on computer screen - USA Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-spyware-warning-message-on-computer-screen-usa-138977733.htmlRMJ22YED–Malware (spyware) warning message on computer screen - USA
 Malware on Dark Digital Background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-on-dark-digital-background-image66147023.html
Malware on Dark Digital Background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-on-dark-digital-background-image66147023.htmlRFDRH75K–Malware on Dark Digital Background.
 malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146776812.html
malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146776812.htmlRFJEP790–malware or ransomware attack concept padlock with money, clipping path, 3d illustration
 RoadSign Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-roadsign-malware-71963114.html
RoadSign Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-roadsign-malware-71963114.htmlRFE525K6–RoadSign Malware
RF2G57Y4N–Phishing mail malware symbol vector icon
 Hacker with malware code in computer screen. Cybersecurity, privacy or cyber attack. Programmer or fraud criminal writing virus software. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-with-malware-code-in-computer-screen-cybersecurity-privacy-or-cyber-attack-programmer-or-fraud-criminal-writing-virus-software-image569522467.html
Hacker with malware code in computer screen. Cybersecurity, privacy or cyber attack. Programmer or fraud criminal writing virus software. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-with-malware-code-in-computer-screen-cybersecurity-privacy-or-cyber-attack-programmer-or-fraud-criminal-writing-virus-software-image569522467.htmlRF2T2FYM3–Hacker with malware code in computer screen. Cybersecurity, privacy or cyber attack. Programmer or fraud criminal writing virus software.
RF2D8D54E–Trojan attack, computer virus, cyber security, malware, crime and spying software technology icon. Abstract symbol concept 3d rendering illustration.
 The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-wannacrypt-and-binary-code-the-wannacry-and-ransomware-concept-142785735.html
The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-wannacrypt-and-binary-code-the-wannacry-and-ransomware-concept-142785735.htmlRFJ88CJF–The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack.
 Trojan horse, conceptual image of Trojan, malware, computer virus ... hidden in binary code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-trojan-horse-conceptual-image-of-trojan-malware-computer-virus-hidden-95193333.html
Trojan horse, conceptual image of Trojan, malware, computer virus ... hidden in binary code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-trojan-horse-conceptual-image-of-trojan-malware-computer-virus-hidden-95193333.htmlRFFETC1W–Trojan horse, conceptual image of Trojan, malware, computer virus ... hidden in binary code
 Ransomware Malware Attack And Breach Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-image547858455.html
Ransomware Malware Attack And Breach Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-image547858455.htmlRF2PR931B–Ransomware Malware Attack And Breach
 Image of interference over malware text, data processing and computer circuit board Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-interference-over-malware-text-data-processing-and-computer-circuit-board-image472350986.html
Image of interference over malware text, data processing and computer circuit board Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-interference-over-malware-text-data-processing-and-computer-circuit-board-image472350986.htmlRF2JCDCE2–Image of interference over malware text, data processing and computer circuit board
 malware computer virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-computer-virus-133373361.html
malware computer virus Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-computer-virus-133373361.htmlRFHMYK29–malware computer virus
 Technology criminal concept as a hacker as a cyber criminal hacking software or a hack and malware internet crime symbol as online security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/technology-criminal-concept-as-a-hacker-as-a-cyber-criminal-hacking-software-or-a-hack-and-malware-internet-crime-symbol-as-online-security-concept-image329034713.html
Technology criminal concept as a hacker as a cyber criminal hacking software or a hack and malware internet crime symbol as online security concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/technology-criminal-concept-as-a-hacker-as-a-cyber-criminal-hacking-software-or-a-hack-and-malware-internet-crime-symbol-as-online-security-concept-image329034713.htmlRF2A38R3N–Technology criminal concept as a hacker as a cyber criminal hacking software or a hack and malware internet crime symbol as online security concept.
 Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126101948.html
Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126101948.htmlRFH94C90–Scam Virus Spyware Malware Antivirus Concept
 Virus alert. Malware notification on smartphone screen. Hacker attack and spam message vector concept. Illustration of alert screen virus, hacking spam attack Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-alert-malware-notification-on-smartphone-screen-hacker-attack-and-spam-message-vector-concept-illustration-of-alert-screen-virus-hacking-spam-attack-image357378692.html
Virus alert. Malware notification on smartphone screen. Hacker attack and spam message vector concept. Illustration of alert screen virus, hacking spam attack Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/virus-alert-malware-notification-on-smartphone-screen-hacker-attack-and-spam-message-vector-concept-illustration-of-alert-screen-virus-hacking-spam-attack-image357378692.htmlRF2BNC04M–Virus alert. Malware notification on smartphone screen. Hacker attack and spam message vector concept. Illustration of alert screen virus, hacking spam attack
 Teenage Hacker is Working With his Computer with Green Screen Mock-up Display Infect Servers and Infrastructure with Malware. His Hideout is Dark. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/teenage-hacker-is-working-with-his-computer-with-green-screen-mock-up-display-infect-servers-and-infrastructure-with-malware-his-hideout-is-dark-image177830403.html
Teenage Hacker is Working With his Computer with Green Screen Mock-up Display Infect Servers and Infrastructure with Malware. His Hideout is Dark. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/teenage-hacker-is-working-with-his-computer-with-green-screen-mock-up-display-infect-servers-and-infrastructure-with-malware-his-hideout-is-dark-image177830403.htmlRFM98TDR–Teenage Hacker is Working With his Computer with Green Screen Mock-up Display Infect Servers and Infrastructure with Malware. His Hideout is Dark.
 Writing displaying text Email Phishing. Business showcase Emails that may link to websites that distribute malware Abstract Creating Online Typing Services, Learning Computer Program Codes Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-displaying-text-email-phishing-business-showcase-emails-that-may-link-to-websites-that-distribute-malware-abstract-creating-online-typing-services-learning-computer-program-codes-image483244255.html
Writing displaying text Email Phishing. Business showcase Emails that may link to websites that distribute malware Abstract Creating Online Typing Services, Learning Computer Program Codes Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/writing-displaying-text-email-phishing-business-showcase-emails-that-may-link-to-websites-that-distribute-malware-abstract-creating-online-typing-services-learning-computer-program-codes-image483244255.htmlRF2K25JYB–Writing displaying text Email Phishing. Business showcase Emails that may link to websites that distribute malware Abstract Creating Online Typing Services, Learning Computer Program Codes
 malware browser is operated by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-browser-is-operated-by-businessman-98285332.html
malware browser is operated by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-browser-is-operated-by-businessman-98285332.htmlRFFKW7XC–malware browser is operated by businessman.
 Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718412.html
Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718412.htmlRFHJ8850–Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words.
RF2D34KBG–SPAM email vector icon. Advertising, phishing, distribution of malware through spam messages. Spam email message distribution, malware spreading virus
 A mock up of a dictionary page with the word malware with selective focussing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-mock-up-of-a-dictionary-page-with-the-word-malware-with-selective-focussing-image503481174.html
A mock up of a dictionary page with the word malware with selective focussing Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-mock-up-of-a-dictionary-page-with-the-word-malware-with-selective-focussing-image503481174.htmlRF2M73FAE–A mock up of a dictionary page with the word malware with selective focussing
 malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146775212.html
malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146775212.htmlRFJEP57T–malware or ransomware attack concept padlock with money, clipping path, 3d illustration
 Roadsign Stop Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-roadsign-stop-malware-80169518.html
Roadsign Stop Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-roadsign-stop-malware-80169518.htmlRFEJC112–Roadsign Stop Malware
RF2G57XTG–Phishing malware for login password on notebook computer or smartphone symbols vector illustration icon set
 Hacker or code developer with laptop. Malware, game or website developing. Cyber criminal, programmer, engineer or coder. Fraud software or privacy. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-or-code-developer-with-laptop-malware-game-or-website-developing-cyber-criminal-programmer-engineer-or-coder-fraud-software-or-privacy-image571175256.html
Hacker or code developer with laptop. Malware, game or website developing. Cyber criminal, programmer, engineer or coder. Fraud software or privacy. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hacker-or-code-developer-with-laptop-malware-game-or-website-developing-cyber-criminal-programmer-engineer-or-coder-fraud-software-or-privacy-image571175256.htmlRF2T577T8–Hacker or code developer with laptop. Malware, game or website developing. Cyber criminal, programmer, engineer or coder. Fraud software or privacy.
RF2CGTN9H–Computer virus attack, cyber security, malware, crime, spying software technology with digital worm icon. Abstract 3d symbol concept rendering illustr
 Ransomware Malware Attack And Breach. Business Computer Hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-business-computer-hacked-image457519508.html
Ransomware Malware Attack And Breach. Business Computer Hacked Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-attack-and-breach-business-computer-hacked-image457519508.htmlRF2HG9PPC–Ransomware Malware Attack And Breach. Business Computer Hacked
 Malware, conceptual artwork Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-conceptual-artwork-56392198.html
Malware, conceptual artwork Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-conceptual-artwork-56392198.htmlRFD7MTR2–Malware, conceptual artwork
 The RansomWare and Binary code, RansomWare Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-ransomware-and-binary-code-ransomware-concept-security-and-malware-144748376.html
The RansomWare and Binary code, RansomWare Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-ransomware-and-binary-code-ransomware-concept-security-and-malware-144748376.htmlRFJBDT0T–The RansomWare and Binary code, RansomWare Concept Security and Malware attack.
 Image of malware text, binary codes, loading bars, changing numbers on connected dots Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-malware-text-binary-codes-loading-bars-changing-numbers-on-connected-dots-image606269988.html
Image of malware text, binary codes, loading bars, changing numbers on connected dots Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/image-of-malware-text-binary-codes-loading-bars-changing-numbers-on-connected-dots-image606269988.htmlRF2X69YFG–Image of malware text, binary codes, loading bars, changing numbers on connected dots
 computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image249312088.html
computer virus malware attack. computer code on a screen with a skull symbol Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-attack-computer-code-on-a-screen-with-a-skull-symbol-image249312088.htmlRFTDH434–computer virus malware attack. computer code on a screen with a skull symbol
 Computer virus malware destroying data and clearing digital code from a hard drive or memory storage server as a hacking or internet security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-destroying-data-and-clearing-digital-code-from-a-hard-drive-or-memory-storage-server-as-a-hacking-or-internet-security-image328931595.html
Computer virus malware destroying data and clearing digital code from a hard drive or memory storage server as a hacking or internet security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/computer-virus-malware-destroying-data-and-clearing-digital-code-from-a-hard-drive-or-memory-storage-server-as-a-hacking-or-internet-security-image328931595.htmlRF2A343GY–Computer virus malware destroying data and clearing digital code from a hard drive or memory storage server as a hacking or internet security.
 Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126034932.html
Scam Virus Spyware Malware Antivirus Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-scam-virus-spyware-malware-antivirus-concept-126034932.htmlRFH91ARG–Scam Virus Spyware Malware Antivirus Concept
 Laptop virus alert. Malware trojan notification on computer screen. Hacker attack and insecure internet connection vector concept. Illustration of internet virus malware Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-virus-alert-malware-trojan-notification-on-computer-screen-hacker-attack-and-insecure-internet-connection-vector-concept-illustration-of-internet-virus-malware-image357376806.html
Laptop virus alert. Malware trojan notification on computer screen. Hacker attack and insecure internet connection vector concept. Illustration of internet virus malware Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/laptop-virus-alert-malware-trojan-notification-on-computer-screen-hacker-attack-and-insecure-internet-connection-vector-concept-illustration-of-internet-virus-malware-image357376806.htmlRF2BNBWNA–Laptop virus alert. Malware trojan notification on computer screen. Hacker attack and insecure internet connection vector concept. Illustration of internet virus malware
 Shot of Teenage Hacker Working with Green Screen Mock-up Display Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/shot-of-teenage-hacker-working-with-green-screen-mock-up-display-infecting-servers-and-infrastructure-with-malware-his-hideout-is-dark-neon-lit-image177830414.html
Shot of Teenage Hacker Working with Green Screen Mock-up Display Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/shot-of-teenage-hacker-working-with-green-screen-mock-up-display-infecting-servers-and-infrastructure-with-malware-his-hideout-is-dark-neon-lit-image177830414.htmlRFM98TE6–Shot of Teenage Hacker Working with Green Screen Mock-up Display Infecting Servers and Infrastructure with Malware. His Hideout is Dark, Neon Lit.
 Hand writing sign Email Phishing. Business concept Emails that may link to websites that distribute malware Laptop Placed Resting On Table Working In The Park Doing Remote Jobs. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-email-phishing-business-concept-emails-that-may-link-to-websites-that-distribute-malware-laptop-placed-resting-on-table-working-in-the-park-doing-remote-jobs-image483241927.html
Hand writing sign Email Phishing. Business concept Emails that may link to websites that distribute malware Laptop Placed Resting On Table Working In The Park Doing Remote Jobs. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hand-writing-sign-email-phishing-business-concept-emails-that-may-link-to-websites-that-distribute-malware-laptop-placed-resting-on-table-working-in-the-park-doing-remote-jobs-image483241927.htmlRF2K25G07–Hand writing sign Email Phishing. Business concept Emails that may link to websites that distribute malware Laptop Placed Resting On Table Working In The Park Doing Remote Jobs.
 malware eye looks at viewer concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-eye-looks-at-viewer-concept-97993550.html
malware eye looks at viewer concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-eye-looks-at-viewer-concept-97993550.htmlRFFKBYNJ–malware eye looks at viewer concept.
 Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718419.html
Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-fake-dictionary-dictionary-definition-of-the-word-malware-including-131718419.htmlRFHJ8857–Fake Dictionary, Dictionary definition of the word Malware. including key descriptive words.
RF2D50KM4–Email with malware, vector icon. Virus, malware, email fraud, e-mail spam, phishing scam, hacker attack concept. Opened mail envelope with infected fi
 Ransomware Malware Cyber Attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-cyber-attack-image483464303.html
Ransomware Malware Cyber Attack Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ransomware-malware-cyber-attack-image483464303.htmlRF2K2FKJ7–Ransomware Malware Cyber Attack
 malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146777889.html
malware or ransomware attack concept padlock with money, clipping path, 3d illustration Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-malware-or-ransomware-attack-concept-padlock-with-money-clipping-path-146777889.htmlRFJEP8KD–malware or ransomware attack concept padlock with money, clipping path, 3d illustration
 FLAT phone iso Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-flat-phone-iso-malware-71963491.html
FLAT phone iso Malware Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-flat-phone-iso-malware-71963491.htmlRFE5264K–FLAT phone iso Malware
 Malware message sign made of wood on a desk in a bright office environment Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-message-sign-made-of-wood-on-a-desk-in-a-bright-office-environment-image556502955.html
Malware message sign made of wood on a desk in a bright office environment Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-message-sign-made-of-wood-on-a-desk-in-a-bright-office-environment-image556502955.htmlRF2R9AW5F–Malware message sign made of wood on a desk in a bright office environment
 Text sign showing Malware Analysis. Business approach activities a company takes to promote and sell products Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-malware-analysis-business-approach-activities-a-company-takes-to-promote-and-sell-products-image547441786.html
Text sign showing Malware Analysis. Business approach activities a company takes to promote and sell products Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/text-sign-showing-malware-analysis-business-approach-activities-a-company-takes-to-promote-and-sell-products-image547441786.htmlRM2PPJ3GA–Text sign showing Malware Analysis. Business approach activities a company takes to promote and sell products
RF2CGTNA2–Computer virus attack, cyber security, malware, crime, spying software technology with digital worm icon. Abstract 3d symbol concept rendering illustr
 Infecting a laptop with a Computer Virus via a memory card, computer virus attack,hacking,malware,computer crime concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/infecting-a-laptop-with-a-computer-virus-via-a-memory-card-computer-virus-attackhackingmalwarecomputer-crime-concept-image565244256.html
Infecting a laptop with a Computer Virus via a memory card, computer virus attack,hacking,malware,computer crime concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/infecting-a-laptop-with-a-computer-virus-via-a-memory-card-computer-virus-attackhackingmalwarecomputer-crime-concept-image565244256.htmlRF2RRH2PT–Infecting a laptop with a Computer Virus via a memory card, computer virus attack,hacking,malware,computer crime concept.
 The malware named 'Silver Sparrow' comes with a mechanism to self-destruct itself, a capability that's typically reserved for high-stealth operations. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-malware-named-silver-sparrow-comes-with-a-mechanism-to-self-destruct-itself-a-capability-thats-typically-reserved-for-high-stealth-operations-image407233063.html
The malware named 'Silver Sparrow' comes with a mechanism to self-destruct itself, a capability that's typically reserved for high-stealth operations. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-malware-named-silver-sparrow-comes-with-a-mechanism-to-self-destruct-itself-a-capability-thats-typically-reserved-for-high-stealth-operations-image407233063.htmlRF2EJF1WY–The malware named 'Silver Sparrow' comes with a mechanism to self-destruct itself, a capability that's typically reserved for high-stealth operations.
 The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-wannacrypt-and-binary-code-the-wannacry-and-ransomware-concept-141867144.html
The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-the-wannacrypt-and-binary-code-the-wannacry-and-ransomware-concept-141867144.htmlRFJ6PGYM–The WannaCrypt and Binary code, The WannaCry and RansomWare, Concept Security and Malware attack.
 Malware infiltration puts security at risk 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-infiltration-puts-security-at-risk-4k-image439231056.html
Malware infiltration puts security at risk 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/malware-infiltration-puts-security-at-risk-4k-image439231056.htmlRF2GEGKKC–Malware infiltration puts security at risk 4k
 Woman using laptop with virtual malware alert. System hacked concept. Cyber attack on computer network, Virus, Spyware, Malware or Malicious software. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-using-laptop-with-virtual-malware-alert-system-hacked-concept-cyber-attack-on-computer-network-virus-spyware-malware-or-malicious-software-image548759404.html
Woman using laptop with virtual malware alert. System hacked concept. Cyber attack on computer network, Virus, Spyware, Malware or Malicious software. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-using-laptop-with-virtual-malware-alert-system-hacked-concept-cyber-attack-on-computer-network-virus-spyware-malware-or-malicious-software-image548759404.htmlRF2PTP464–Woman using laptop with virtual malware alert. System hacked concept. Cyber attack on computer network, Virus, Spyware, Malware or Malicious software.
Search Results for Malware Stock Photos and Images (51,665)
Page 1 of 500