SAVE 40% ON SINGLE IMAGE PURCHASES - OFFER ENDS SOON, USE CODE: IMAGESAVE40%
Quick filters:
Decryption Stock Photos and Images
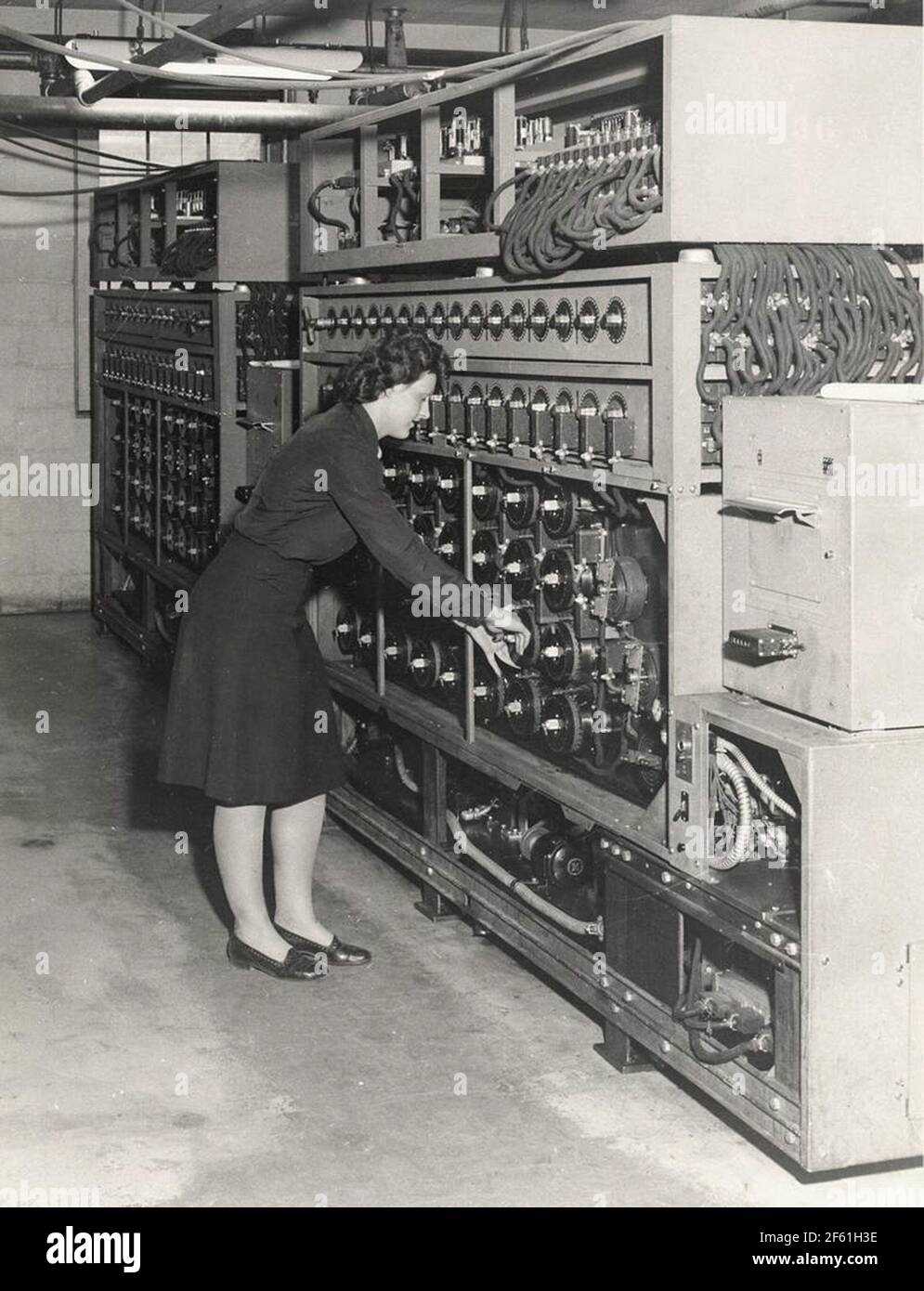 Bombe Decryption Machine, US, 1945 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bombe-decryption-machine-us-1945-image416772146.html
Bombe Decryption Machine, US, 1945 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bombe-decryption-machine-us-1945-image416772146.htmlRM2F61H3E–Bombe Decryption Machine, US, 1945
 Decryption and decrypting data or decode and decoding encrypted digital information and crack the code symbol as a coding technology security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-and-decrypting-data-or-decode-and-decoding-encrypted-digital-171101078.html
Decryption and decrypting data or decode and decoding encrypted digital information and crack the code symbol as a coding technology security. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-and-decrypting-data-or-decode-and-decoding-encrypted-digital-171101078.htmlRFKXA94P–Decryption and decrypting data or decode and decoding encrypted digital information and crack the code symbol as a coding technology security.
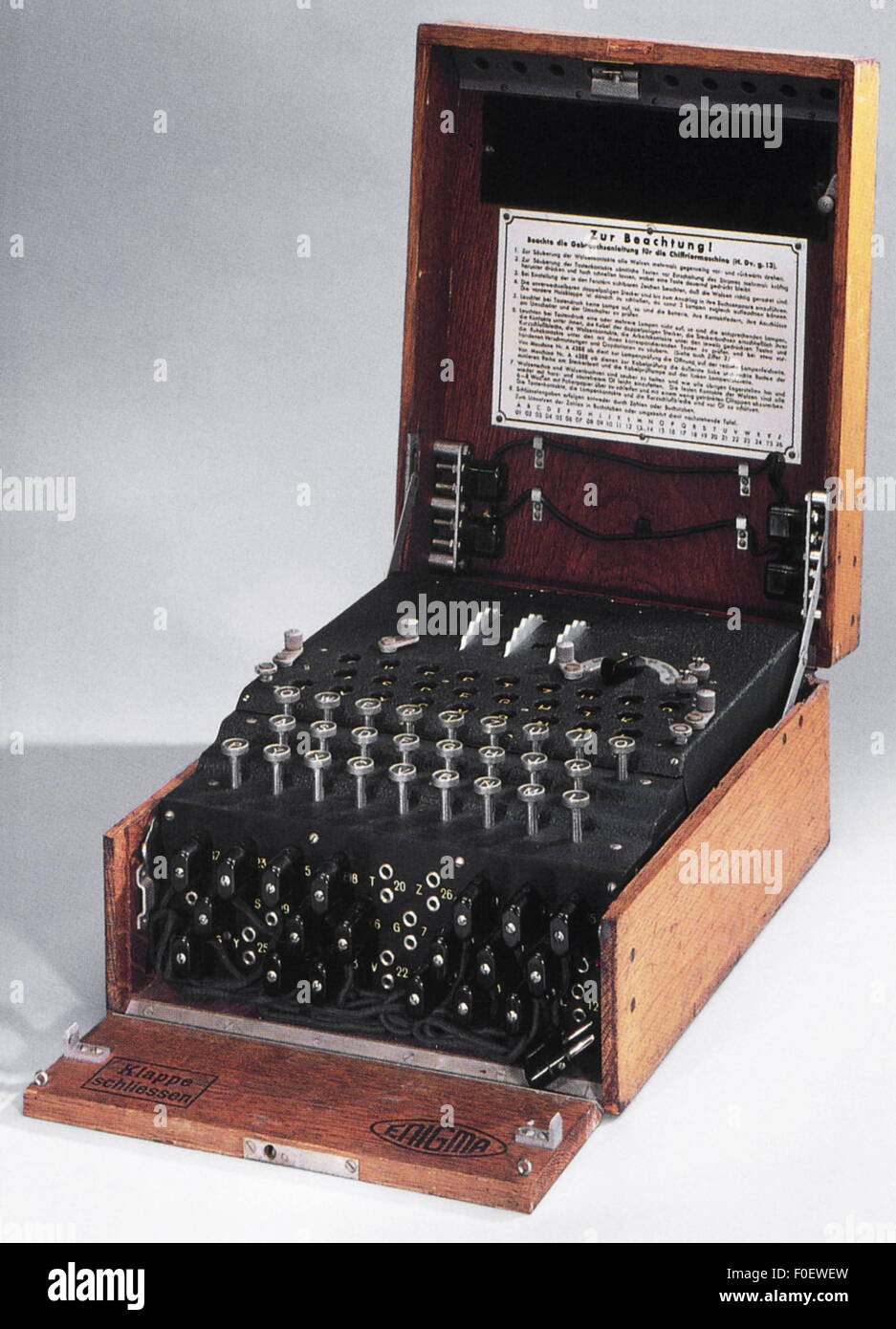 espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-espionage-german-enigma-machine-used-for-the-encryption-and-decryption-86379185.html
espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-espionage-german-enigma-machine-used-for-the-encryption-and-decryption-86379185.htmlRMF0EWEW–espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available
![Ptolemaic general panel, conceiving of the half andern weldt decryption., World map from the 16th century, Fig. 2, according to S. i, 1544, Sebastian Münster: Cosmographia. Beschreibung aller Lender durch Sebastianum Münsterum: in welcher begriffen aller Voelker, Herrschaften, Stetten, und namhafftiger Flecken, herkommen: Sitten, Gebreüch, Ordnung, Glauben, Secten und Hantierung durch die gantze Welt und fürnemlich Teütscher Nation [...]. Basel: durch Henrichum Petri, 1544 Stock Photo Ptolemaic general panel, conceiving of the half andern weldt decryption., World map from the 16th century, Fig. 2, according to S. i, 1544, Sebastian Münster: Cosmographia. Beschreibung aller Lender durch Sebastianum Münsterum: in welcher begriffen aller Voelker, Herrschaften, Stetten, und namhafftiger Flecken, herkommen: Sitten, Gebreüch, Ordnung, Glauben, Secten und Hantierung durch die gantze Welt und fürnemlich Teütscher Nation [...]. Basel: durch Henrichum Petri, 1544 Stock Photo](https://c8.alamy.com/comp/2A2RW9W/ptolemaic-general-panel-conceiving-of-the-half-andern-weldt-decryption-world-map-from-the-16th-century-fig-2-according-to-s-i-1544-sebastian-mnster-cosmographia-beschreibung-aller-lender-durch-sebastianum-mnsterum-in-welcher-begriffen-aller-voelker-herrschaften-stetten-und-namhafftiger-flecken-herkommen-sitten-gebrech-ordnung-glauben-secten-und-hantierung-durch-die-gantze-welt-und-frnemlich-tetscher-nation-basel-durch-henrichum-petri-1544-2A2RW9W.jpg) Ptolemaic general panel, conceiving of the half andern weldt decryption., World map from the 16th century, Fig. 2, according to S. i, 1544, Sebastian Münster: Cosmographia. Beschreibung aller Lender durch Sebastianum Münsterum: in welcher begriffen aller Voelker, Herrschaften, Stetten, und namhafftiger Flecken, herkommen: Sitten, Gebreüch, Ordnung, Glauben, Secten und Hantierung durch die gantze Welt und fürnemlich Teütscher Nation [...]. Basel: durch Henrichum Petri, 1544 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ptolemaic-general-panel-conceiving-of-the-half-andern-weldt-decryption-world-map-from-the-16th-century-fig-2-according-to-s-i-1544-sebastian-mnster-cosmographia-beschreibung-aller-lender-durch-sebastianum-mnsterum-in-welcher-begriffen-aller-voelker-herrschaften-stetten-und-namhafftiger-flecken-herkommen-sitten-gebrech-ordnung-glauben-secten-und-hantierung-durch-die-gantze-welt-und-frnemlich-tetscher-nation-basel-durch-henrichum-petri-1544-image328751077.html
Ptolemaic general panel, conceiving of the half andern weldt decryption., World map from the 16th century, Fig. 2, according to S. i, 1544, Sebastian Münster: Cosmographia. Beschreibung aller Lender durch Sebastianum Münsterum: in welcher begriffen aller Voelker, Herrschaften, Stetten, und namhafftiger Flecken, herkommen: Sitten, Gebreüch, Ordnung, Glauben, Secten und Hantierung durch die gantze Welt und fürnemlich Teütscher Nation [...]. Basel: durch Henrichum Petri, 1544 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/ptolemaic-general-panel-conceiving-of-the-half-andern-weldt-decryption-world-map-from-the-16th-century-fig-2-according-to-s-i-1544-sebastian-mnster-cosmographia-beschreibung-aller-lender-durch-sebastianum-mnsterum-in-welcher-begriffen-aller-voelker-herrschaften-stetten-und-namhafftiger-flecken-herkommen-sitten-gebrech-ordnung-glauben-secten-und-hantierung-durch-die-gantze-welt-und-frnemlich-tetscher-nation-basel-durch-henrichum-petri-1544-image328751077.htmlRM2A2RW9W–Ptolemaic general panel, conceiving of the half andern weldt decryption., World map from the 16th century, Fig. 2, according to S. i, 1544, Sebastian Münster: Cosmographia. Beschreibung aller Lender durch Sebastianum Münsterum: in welcher begriffen aller Voelker, Herrschaften, Stetten, und namhafftiger Flecken, herkommen: Sitten, Gebreüch, Ordnung, Glauben, Secten und Hantierung durch die gantze Welt und fürnemlich Teütscher Nation [...]. Basel: durch Henrichum Petri, 1544
 Businessman holding light bulb with DECRYPTION inscription, innovative technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/businessman-holding-light-bulb-with-decryption-inscription-innovative-technology-concept-image333589024.html
Businessman holding light bulb with DECRYPTION inscription, innovative technology concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/businessman-holding-light-bulb-with-decryption-inscription-innovative-technology-concept-image333589024.htmlRF2AAM85M–Businessman holding light bulb with DECRYPTION inscription, innovative technology concept
 decryption sign is held by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-sign-is-held-by-businessman-96571911.html
decryption sign is held by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-sign-is-held-by-businessman-96571911.htmlRFFH36CR–decryption sign is held by businessman.
 Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drums-ready-for-use-on-the-rebuilt-bombe-decryption-machine-at-bletchely-169040868.html
Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drums-ready-for-use-on-the-rebuilt-bombe-decryption-machine-at-bletchely-169040868.htmlRMKR0D9T–Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England
 Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-and-encoding-93637856.html
Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-and-encoding-93637856.htmlRFFC9G14–Decryption and Encoding.
 Decryption key used in cyber attack 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-key-used-in-cyber-attack-4k-image439231013.html
Decryption key used in cyber attack 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-key-used-in-cyber-attack-4k-image439231013.htmlRF2GEGKHW–Decryption key used in cyber attack 4k
 Improve Your Decryption and Increase or Reach Your Goal Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-improve-your-decryption-and-increase-or-reach-your-goal-84849135.html
Improve Your Decryption and Increase or Reach Your Goal Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-improve-your-decryption-and-increase-or-reach-your-goal-84849135.htmlRMEX15X7–Improve Your Decryption and Increase or Reach Your Goal
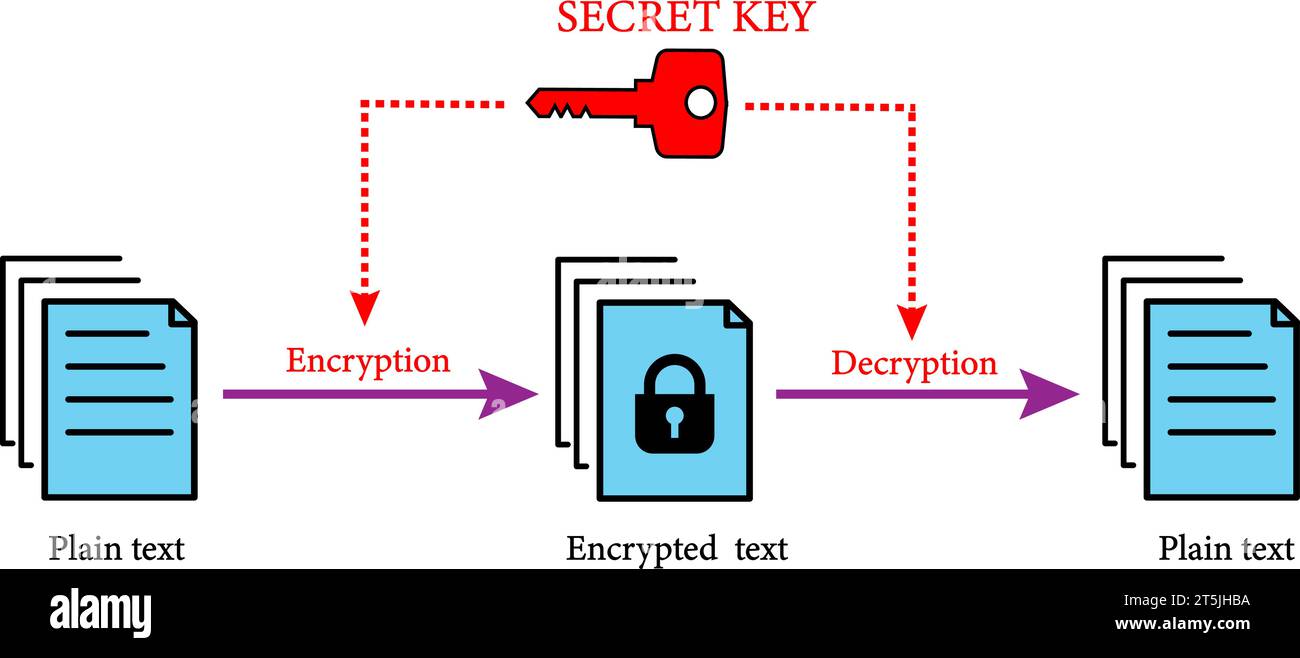 Symmetric encryption scheme: Encryption and decryption use the same key. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symmetric-encryption-scheme-encryption-and-decryption-use-the-same-key-image571424206.html
Symmetric encryption scheme: Encryption and decryption use the same key. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/symmetric-encryption-scheme-encryption-and-decryption-use-the-same-key-image571424206.htmlRF2T5JHBA–Symmetric encryption scheme: Encryption and decryption use the same key.
RF2PNN1B4–Encryption protection line icons collection. Cryptography, Confidentiality, Security, Encryption, Privacy, Decryption, Cipher vector and linear
 Business, Technology, Internet and network concept. Young businessman working on a virtual screen of the future and sees the inscription: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/business-technology-internet-and-network-concept-young-businessman-working-on-a-virtual-screen-of-the-future-and-sees-the-inscription-decryption-image397274724.html
Business, Technology, Internet and network concept. Young businessman working on a virtual screen of the future and sees the inscription: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/business-technology-internet-and-network-concept-young-businessman-working-on-a-virtual-screen-of-the-future-and-sees-the-inscription-decryption-image397274724.htmlRF2E29BY0–Business, Technology, Internet and network concept. Young businessman working on a virtual screen of the future and sees the inscription: Decryption
RF2PP38J3–Data encryption linear icons set. Security, Cryptography, Confidentiality, Protection, Privacy, Decryption, Cipher line vector and concept signs. Key
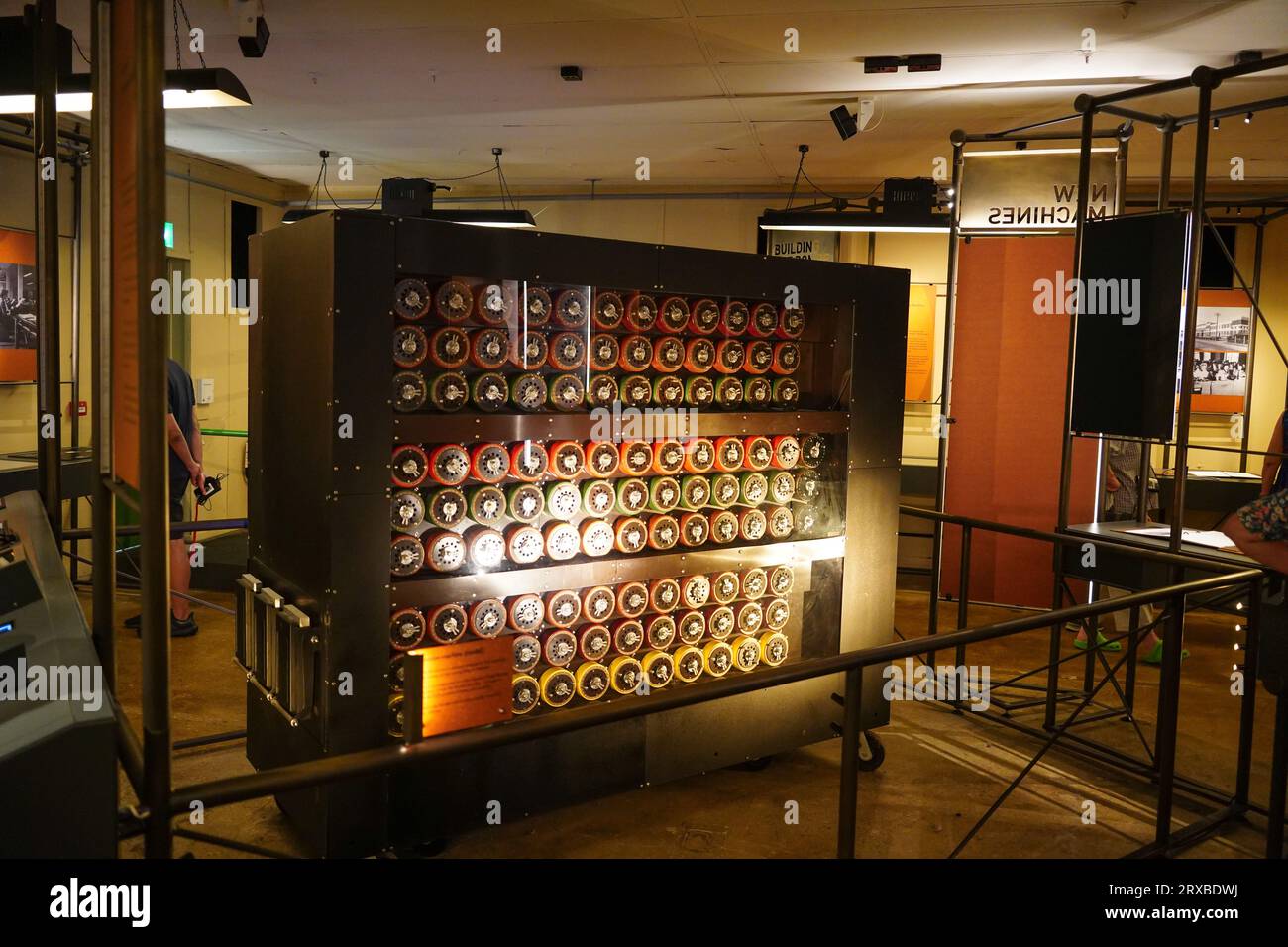 Bletchley, UK: 8 September 2023: A replica of a Turing Bombe codebreaking machine, at Bletchley Park. The Bombe was used to help speed up decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bletchley-uk-8-september-2023-a-replica-of-a-turing-bombe-codebreaking-machine-at-bletchley-park-the-bombe-was-used-to-help-speed-up-decryption-image566965214.html
Bletchley, UK: 8 September 2023: A replica of a Turing Bombe codebreaking machine, at Bletchley Park. The Bombe was used to help speed up decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/bletchley-uk-8-september-2023-a-replica-of-a-turing-bombe-codebreaking-machine-at-bletchley-park-the-bombe-was-used-to-help-speed-up-decryption-image566965214.htmlRM2RXBDWJ–Bletchley, UK: 8 September 2023: A replica of a Turing Bombe codebreaking machine, at Bletchley Park. The Bombe was used to help speed up decryption
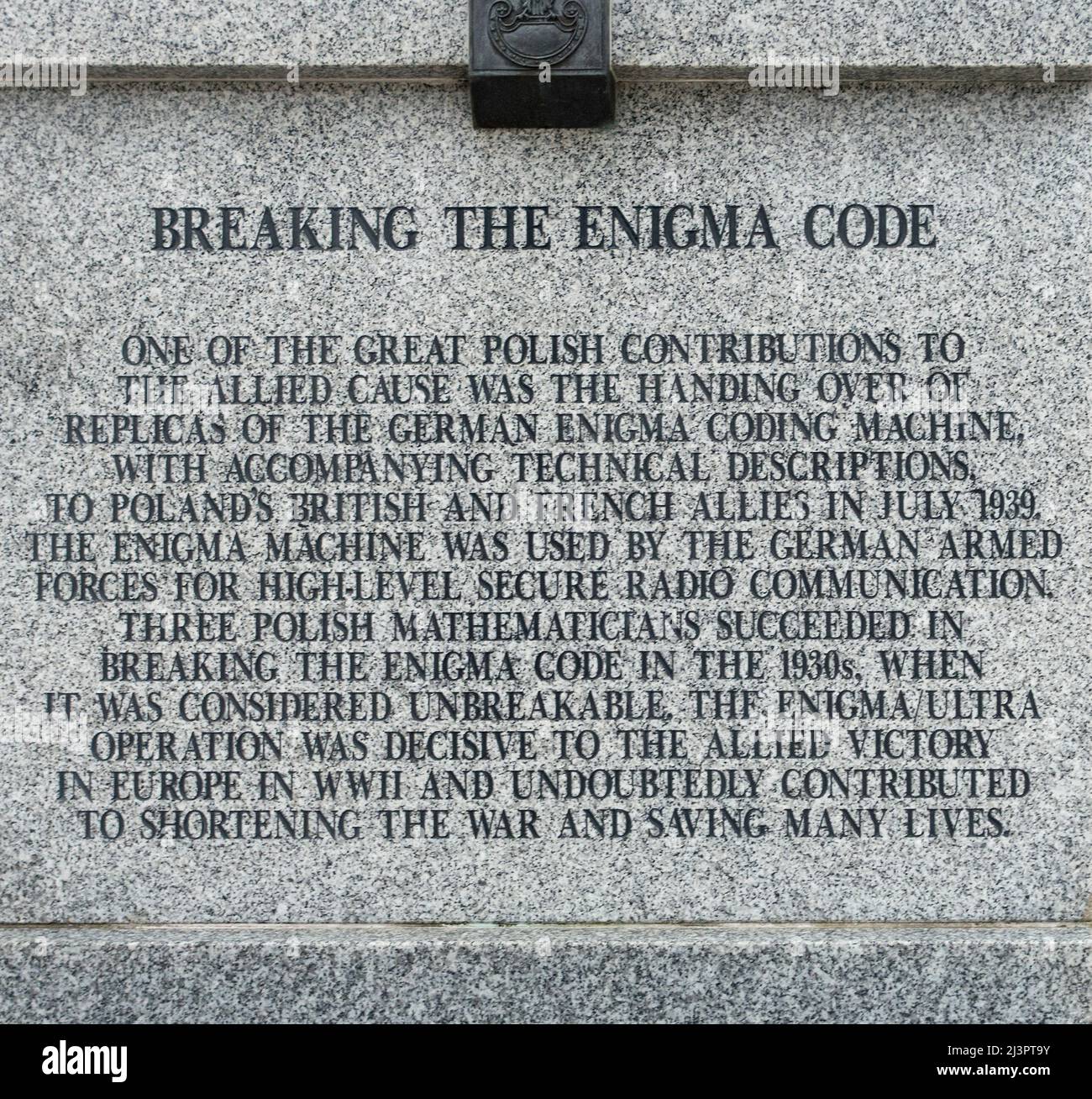 Inscription at the National War Memorial Arboretum, Staffordshire commemorating the Polish breaking of the Enigma Code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/inscription-at-the-national-war-memorial-arboretum-staffordshire-commemorating-the-polish-breaking-of-the-enigma-code-image467025943.html
Inscription at the National War Memorial Arboretum, Staffordshire commemorating the Polish breaking of the Enigma Code Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/inscription-at-the-national-war-memorial-arboretum-staffordshire-commemorating-the-polish-breaking-of-the-enigma-code-image467025943.htmlRM2J3PT9Y–Inscription at the National War Memorial Arboretum, Staffordshire commemorating the Polish breaking of the Enigma Code
 Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722632.html
Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722632.htmlRF2G0N334–Binary code in the future digital abstract background. Modern technology hex code concept.
 solution concept made from metallic letterpress blocks in mixed wooden letters Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-solution-concept-made-from-metallic-letterpress-blocks-in-mixed-wooden-89481660.html
solution concept made from metallic letterpress blocks in mixed wooden letters Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-solution-concept-made-from-metallic-letterpress-blocks-in-mixed-wooden-89481660.htmlRFF5G6NG–solution concept made from metallic letterpress blocks in mixed wooden letters
RF2G474HW–Bitcoin security lock open and closed cryptocurrency for digital security encryption cryptocurrency vector illustration icons
 Rebuilt Bombe Decryption Machine, Bletchley Park Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/rebuilt-bombe-decryption-machine-bletchley-park-image352771340.html
Rebuilt Bombe Decryption Machine, Bletchley Park Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/rebuilt-bombe-decryption-machine-bletchley-park-image352771340.htmlRM2BDX3CC–Rebuilt Bombe Decryption Machine, Bletchley Park
 Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-matrix-background-falling-sign-on-dark-backdrop-abstract-data-concept-blue-and-green-futuristic-cyberspace-image335641879.html
Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-matrix-background-falling-sign-on-dark-backdrop-abstract-data-concept-blue-and-green-futuristic-cyberspace-image335641879.htmlRF2AE1PHY–Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace
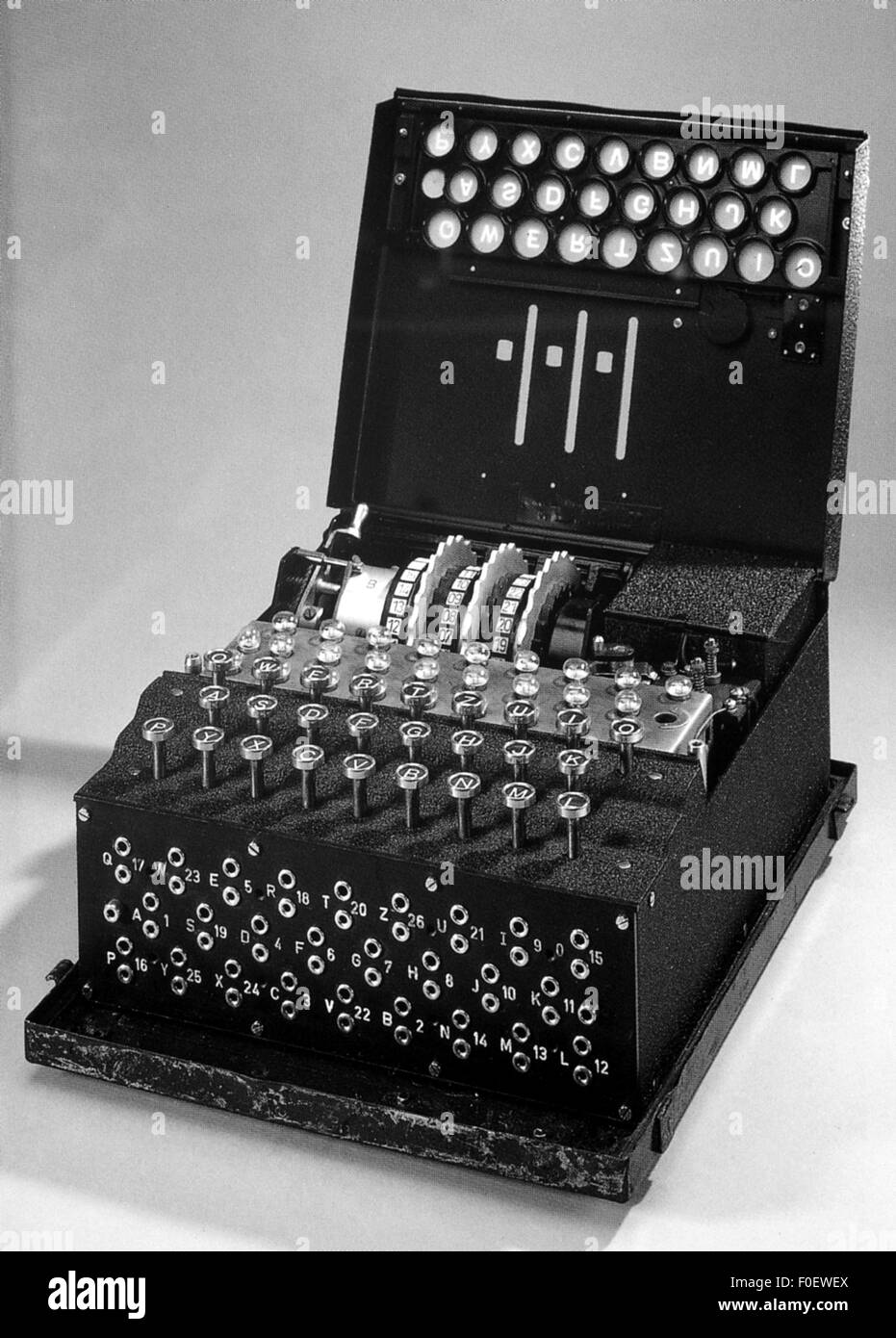 espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-espionage-german-enigma-machine-used-for-the-encryption-and-decryption-86379186.html
espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-espionage-german-enigma-machine-used-for-the-encryption-and-decryption-86379186.htmlRMF0EWEX–espionage, German 'Enigma' machine, used for the encryption and decryption of secret message, in service 1923-1945, Additional-Rights-Clearences-Not Available
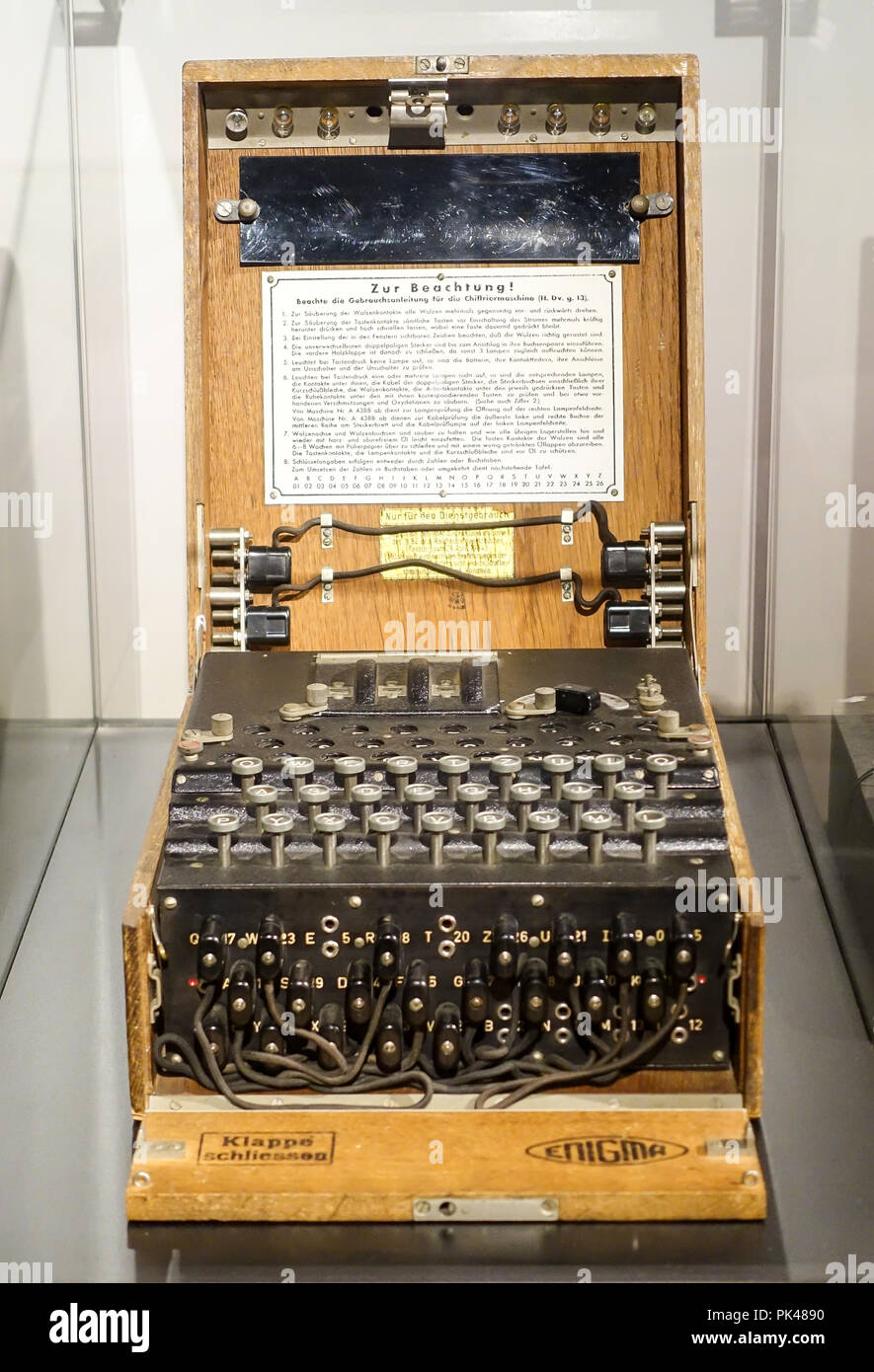 Enigma message encryption machine Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-message-encryption-machine-image218297212.html
Enigma message encryption machine Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-message-encryption-machine-image218297212.htmlRMPK4890–Enigma message encryption machine
 Cyber security concept showing hacker break into mobile phone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-concept-showing-hacker-break-into-mobile-phone-image566030623.html
Cyber security concept showing hacker break into mobile phone Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cyber-security-concept-showing-hacker-break-into-mobile-phone-image566030623.htmlRF2RTTWRB–Cyber security concept showing hacker break into mobile phone
 decryption eye looks at viewer concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-eye-looks-at-viewer-concept-97884665.html
decryption eye looks at viewer concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-eye-looks-at-viewer-concept-97884665.htmlRFFK70TW–decryption eye looks at viewer concept.
 Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drums-ready-for-use-on-the-rebuilt-bombe-decryption-machine-at-bletchely-169040867.html
Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-drums-ready-for-use-on-the-rebuilt-bombe-decryption-machine-at-bletchely-169040867.htmlRMKR0D9R–Drums ready for use on the rebuilt Bombe decryption machine at Bletchely Park, England
 Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127581507.html
Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127581507.htmlRMHBFREB–Data Code, Decryption and Encoding
 Decryption key used in cyber attack 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-key-used-in-cyber-attack-4k-image439230999.html
Decryption key used in cyber attack 4k Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-key-used-in-cyber-attack-4k-image439230999.htmlRF2GEGKHB–Decryption key used in cyber attack 4k
 Decryption as a Futuristic Concept Abstract Background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-as-a-futuristic-concept-abstract-background-101952873.html
Decryption as a Futuristic Concept Abstract Background Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-as-a-futuristic-concept-abstract-background-101952873.htmlRFFWT9X1–Decryption as a Futuristic Concept Abstract Background
 woman reading printed computer code abstract Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-reading-printed-computer-code-abstract-image552142.html
woman reading printed computer code abstract Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/woman-reading-printed-computer-code-abstract-image552142.htmlRMA86CCE–woman reading printed computer code abstract
RF2PNT474–File processing line icons collection. Parsing, Extraction, Compression, Encryption, Decryption, Conversion, Concatenation vector and linear
 The view of Bletchley Park mansion viewed from the lakeside. In the 1990s it was revealed to have been an undercover WWII code breaking centre. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-view-of-bletchley-park-mansion-viewed-from-the-lakeside-in-the-1990s-it-was-revealed-to-have-been-an-undercover-wwii-code-breaking-centre-image569543954.html
The view of Bletchley Park mansion viewed from the lakeside. In the 1990s it was revealed to have been an undercover WWII code breaking centre. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-view-of-bletchley-park-mansion-viewed-from-the-lakeside-in-the-1990s-it-was-revealed-to-have-been-an-undercover-wwii-code-breaking-centre-image569543954.htmlRF2T2GY3E–The view of Bletchley Park mansion viewed from the lakeside. In the 1990s it was revealed to have been an undercover WWII code breaking centre.
RF2PP3PK9–Data encryption linear icons set. Security, Cryptography, Confidentiality, Protection, Privacy, Decryption, Cipher line vector and concept signs. Key
RF2J9H0H5–Decryption black glyph icon
 A lock chip on a computer circuit board, graphic symbol of a computer security system, data protection concept, vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-lock-chip-on-a-computer-circuit-board-graphic-symbol-of-a-computer-security-system-data-protection-concept-vector-illustration-image434266842.html
A lock chip on a computer circuit board, graphic symbol of a computer security system, data protection concept, vector illustration Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/a-lock-chip-on-a-computer-circuit-board-graphic-symbol-of-a-computer-security-system-data-protection-concept-vector-illustration-image434266842.htmlRF2G6EFP2–A lock chip on a computer circuit board, graphic symbol of a computer security system, data protection concept, vector illustration
 Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722636.html
Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722636.htmlRF2G0N338–Binary code in the future digital abstract background. Modern technology hex code concept.
 encrypted concept made from metallic letterpress blocks in mixed wooden letters Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encrypted-concept-made-from-metallic-letterpress-blocks-in-mixed-wooden-89074044.html
encrypted concept made from metallic letterpress blocks in mixed wooden letters Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encrypted-concept-made-from-metallic-letterpress-blocks-in-mixed-wooden-89074044.htmlRFF4WJRT–encrypted concept made from metallic letterpress blocks in mixed wooden letters
 The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241956.html
The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241956.htmlRF2HB0E70–The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire.
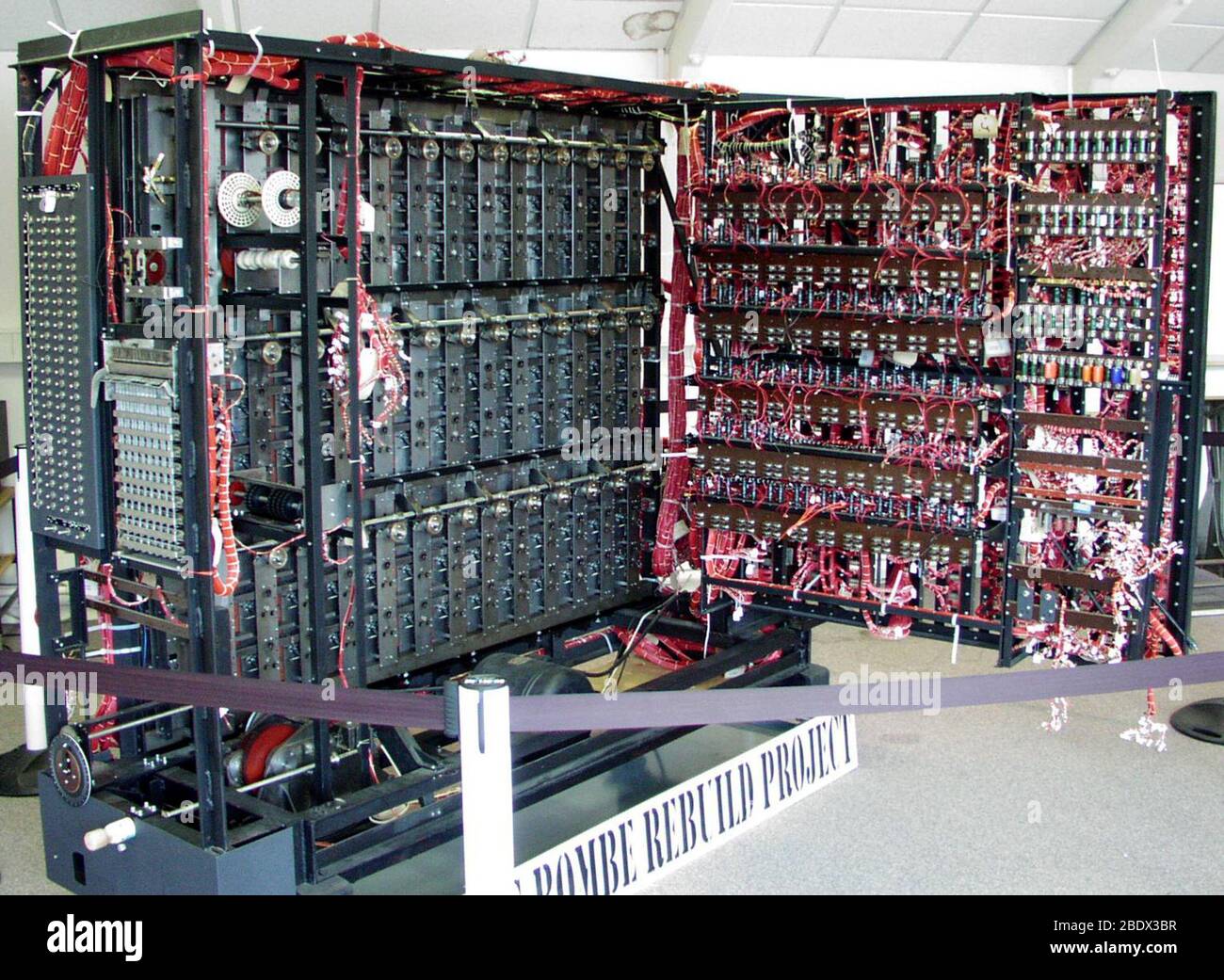 Rebuilt Bombe Decryption Machine, Bletchley Park Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/rebuilt-bombe-decryption-machine-bletchley-park-image352771323.html
Rebuilt Bombe Decryption Machine, Bletchley Park Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/rebuilt-bombe-decryption-machine-bletchley-park-image352771323.htmlRM2BDX3BR–Rebuilt Bombe Decryption Machine, Bletchley Park
 Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-matrix-background-falling-sign-on-dark-backdrop-abstract-data-concept-blue-and-green-futuristic-cyberspace-image335641831.html
Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-matrix-background-falling-sign-on-dark-backdrop-abstract-data-concept-blue-and-green-futuristic-cyberspace-image335641831.htmlRF2AE1PG7–Binary matrix background. Falling sign on dark backdrop. Abstract data concept. Blue and green futuristic cyberspace
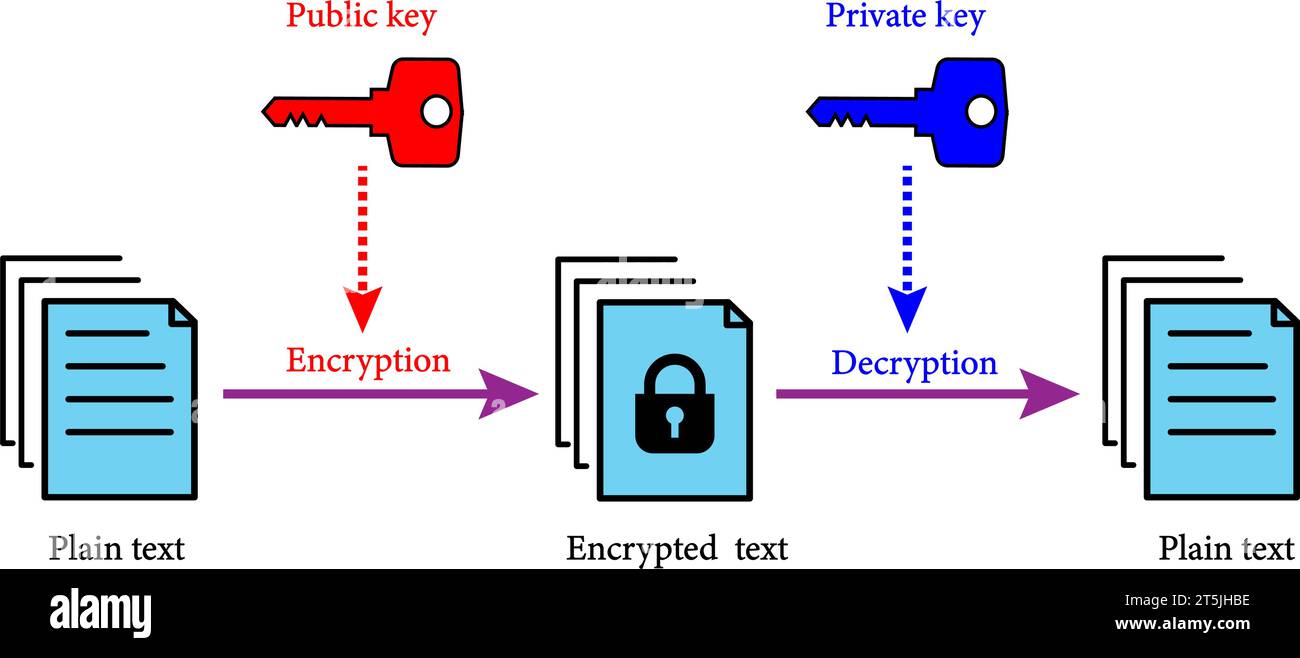 Asymmetric encryption scheme. Key is used to encrypt and a second to decrypt. Vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/asymmetric-encryption-scheme-key-is-used-to-encrypt-and-a-second-to-decrypt-vector-illustration-image571424210.html
Asymmetric encryption scheme. Key is used to encrypt and a second to decrypt. Vector illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/asymmetric-encryption-scheme-key-is-used-to-encrypt-and-a-second-to-decrypt-vector-illustration-image571424210.htmlRF2T5JHBE–Asymmetric encryption scheme. Key is used to encrypt and a second to decrypt. Vector illustration.
 Enigma message encryption machine Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-message-encryption-machine-image218297243.html
Enigma message encryption machine Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-message-encryption-machine-image218297243.htmlRMPK48A3–Enigma message encryption machine
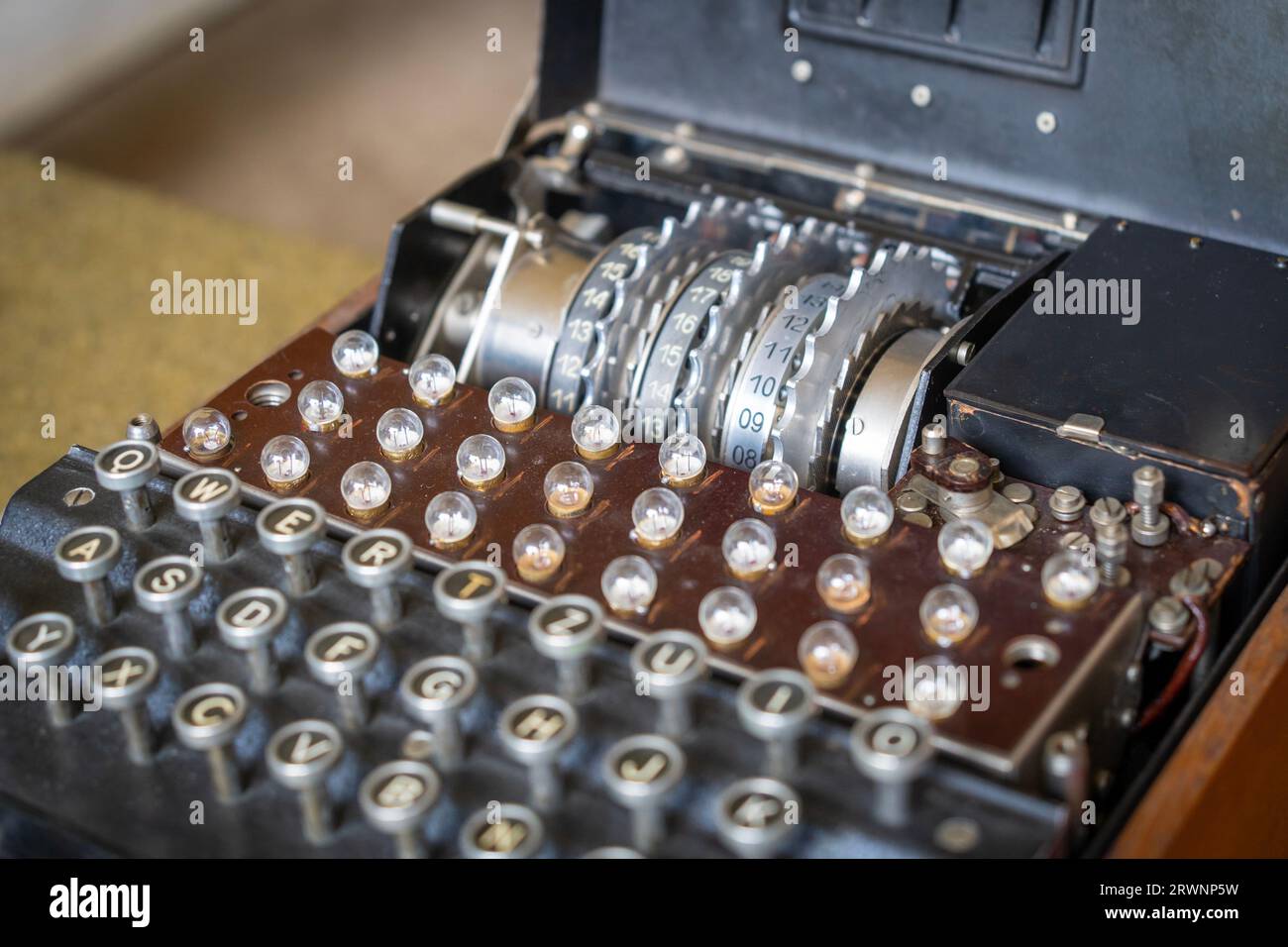 Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576581.html
Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576581.htmlRF2RWNP5W–Enigma, the German cipher machine created for sending messages during World War 2
 encryption touchscreen is operated by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encryption-touchscreen-is-operated-by-businessman-104082001.html
encryption touchscreen is operated by businessman. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encryption-touchscreen-is-operated-by-businessman-104082001.htmlRFG199J9–encryption touchscreen is operated by businessman.
 Decrypt word Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decrypt-word-image482637586.html
Decrypt word Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decrypt-word-image482637586.htmlRM2K1614J–Decrypt word
 Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127586548.html
Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127586548.htmlRMHBG1XC–Data Code, Decryption and Encoding
RF2NAM9DT–Public and Private API key encryption Concept, Secure Hash Algorithm Vector Icon Design, Cloud computing and Web Hosting services Symbol, RSA stock
 Decryption as a Competition Concept Illustration Art Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-as-a-competition-concept-illustration-art-97399796.html
Decryption as a Competition Concept Illustration Art Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-as-a-competition-concept-illustration-art-97399796.htmlRFFJCXC4–Decryption as a Competition Concept Illustration Art
 Cloud computing business Transaction data storage technology concept. vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-computing-business-transaction-data-storage-technology-concept-vector-illustration-eps10-image215907803.html
Cloud computing business Transaction data storage technology concept. vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-computing-business-transaction-data-storage-technology-concept-vector-illustration-eps10-image215907803.htmlRFPF7CGY–Cloud computing business Transaction data storage technology concept. vector illustration eps10.
RF2PNTRH9–Cryptography systems line icons collection. Encryption, Decryption, Cryptanalysis, Cryptology, Cipher, Key, Code vector and linear illustration
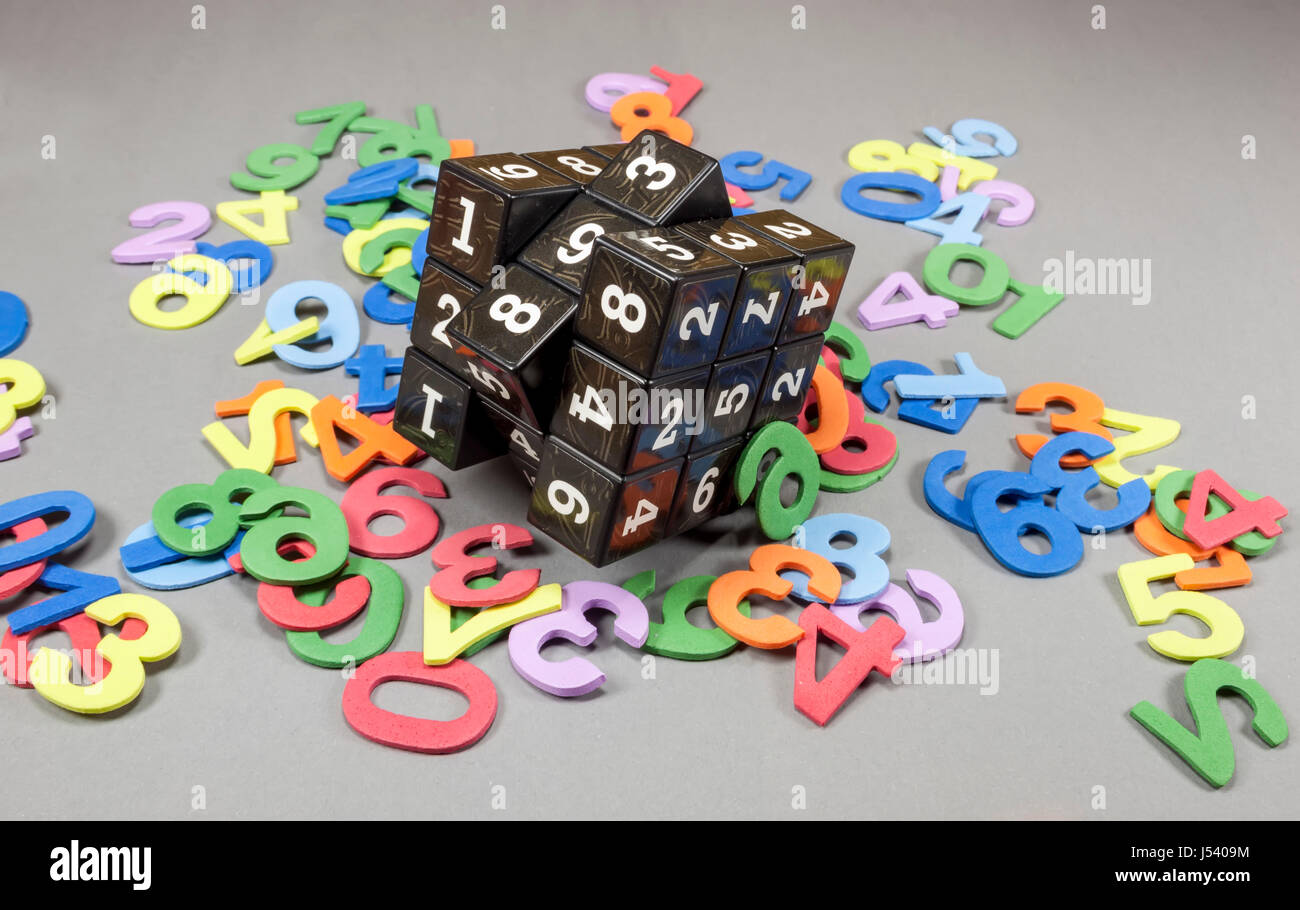 Cube with movable parts having on each side printed numbers with colored numbers around, concept about computer security and cryptography Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cube-with-movable-parts-having-on-each-side-printed-numbers-with-colored-140844304.html
Cube with movable parts having on each side printed numbers with colored numbers around, concept about computer security and cryptography Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cube-with-movable-parts-having-on-each-side-printed-numbers-with-colored-140844304.htmlRFJ5409M–Cube with movable parts having on each side printed numbers with colored numbers around, concept about computer security and cryptography
RF2PP0E5W–Data encryption linear icons set. Security, Cryptography, Confidentiality, Protection, Privacy, Decryption, Cipher line vector and concept signs. Key
RF2J90WXT–Decryption pixel perfect linear icon
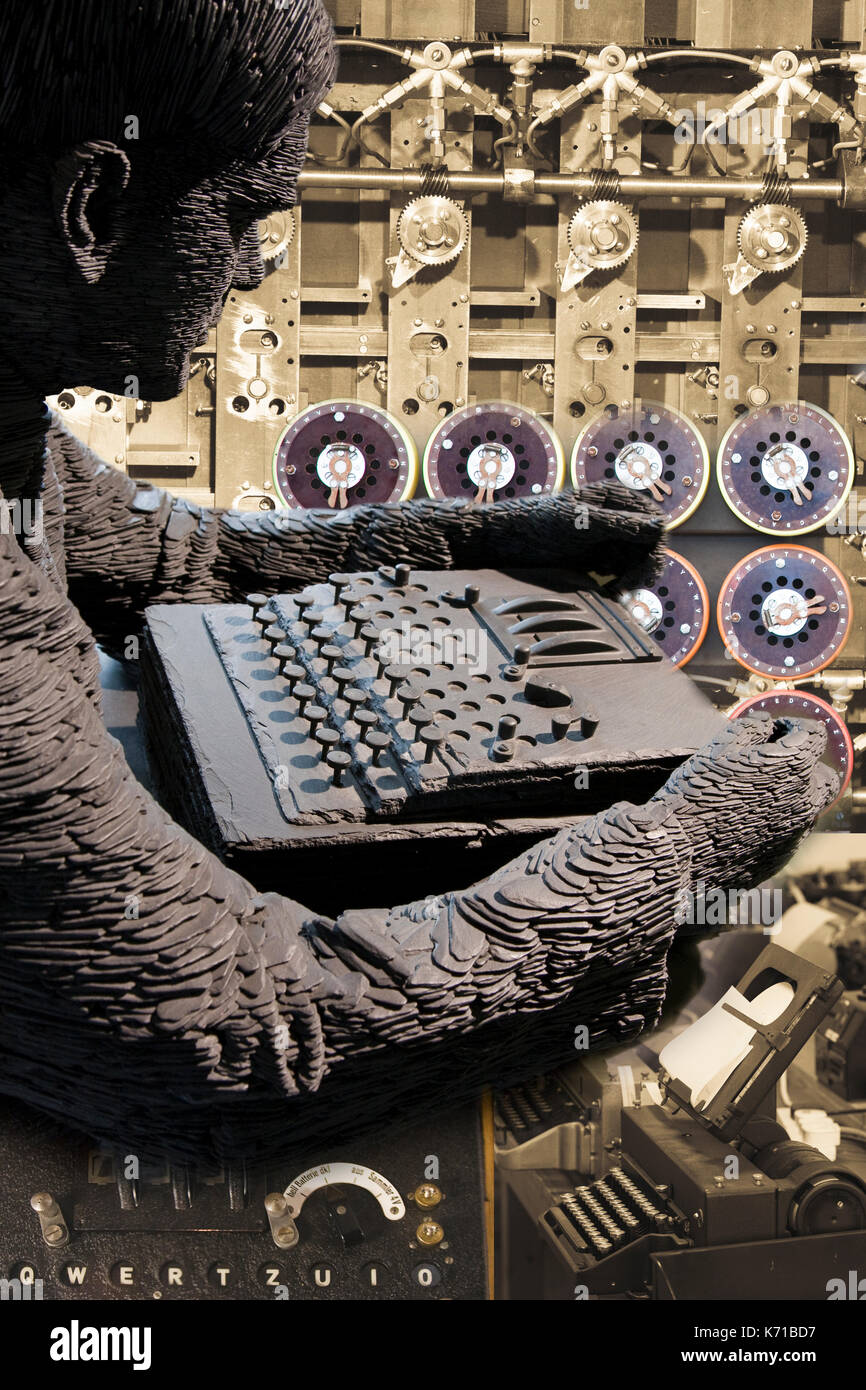 Alan Turing, Bletchley Park Enigma Collage Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/alan-turing-bletchley-park-enigma-collage-image159226851.html
Alan Turing, Bletchley Park Enigma Collage Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/alan-turing-bletchley-park-enigma-collage-image159226851.htmlRMK71BD7–Alan Turing, Bletchley Park Enigma Collage
 Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430723519.html
Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430723519.htmlRF2G0N46R–Binary code in the future digital abstract background. Modern technology hex code concept.
 encryption stencil print on the grunge white brick wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/encryption-stencil-print-on-the-grunge-white-brick-wall-image219095696.html
encryption stencil print on the grunge white brick wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/encryption-stencil-print-on-the-grunge-white-brick-wall-image219095696.htmlRFPMCJP8–encryption stencil print on the grunge white brick wall
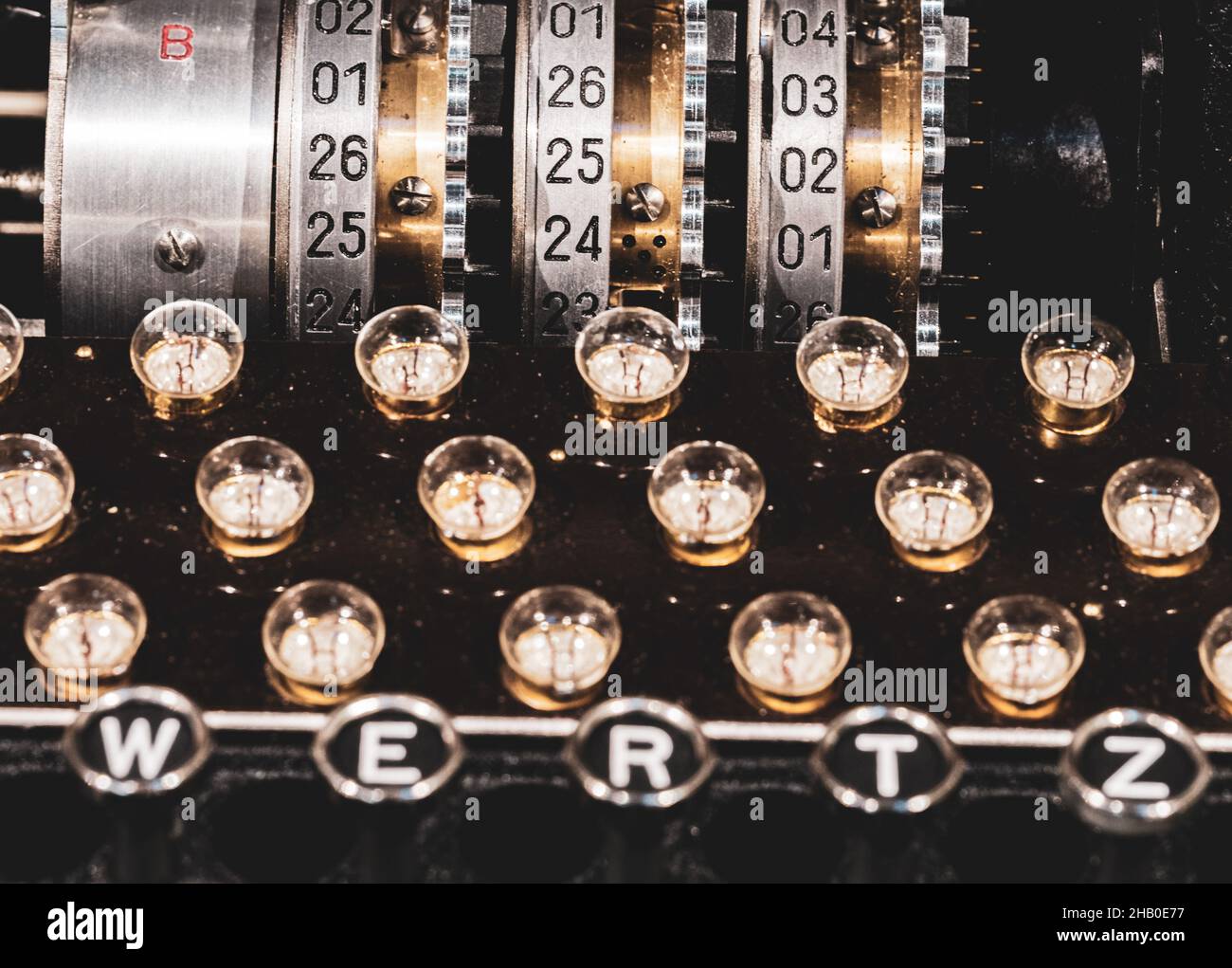 The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241963.html
The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241963.htmlRF2HB0E77–The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire.
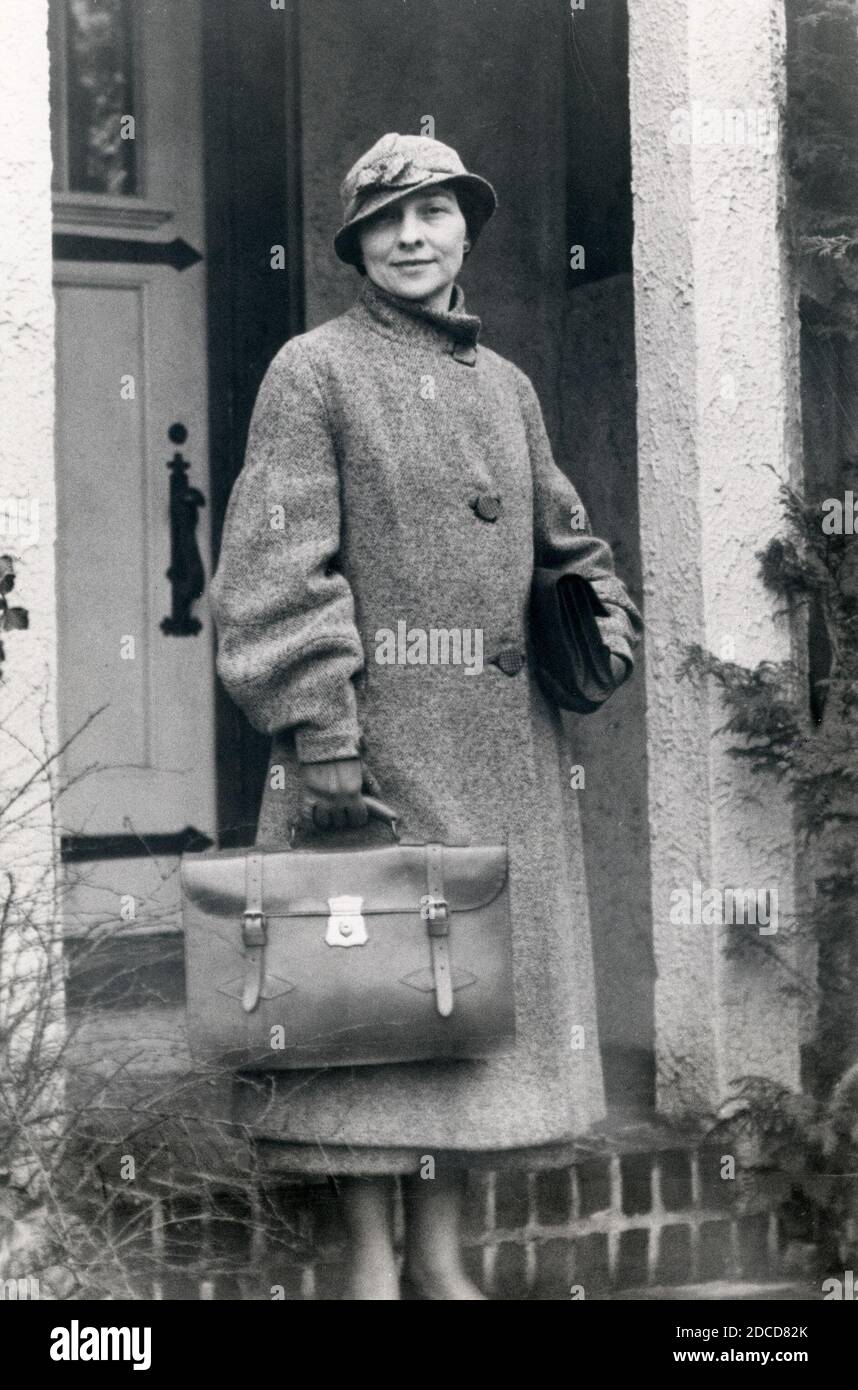
 Dorothy Blum, American Cryptanalyst and Computer Scientist Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dorothy-blum-american-cryptanalyst-and-computer-scientist-image386295672.html
Dorothy Blum, American Cryptanalyst and Computer Scientist Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/dorothy-blum-american-cryptanalyst-and-computer-scientist-image386295672.htmlRF2DCD820–Dorothy Blum, American Cryptanalyst and Computer Scientist
 Global map with binary matrix background. Falling sign on dark backdrop. Global abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/global-map-with-binary-matrix-background-falling-sign-on-dark-backdrop-global-abstract-data-concept-blue-and-green-futuristic-cyberspace-image336421853.html
Global map with binary matrix background. Falling sign on dark backdrop. Global abstract data concept. Blue and green futuristic cyberspace Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/global-map-with-binary-matrix-background-falling-sign-on-dark-backdrop-global-abstract-data-concept-blue-and-green-futuristic-cyberspace-image336421853.htmlRF2AF99E5–Global map with binary matrix background. Falling sign on dark backdrop. Global abstract data concept. Blue and green futuristic cyberspace
 encrypt decrypt concept with lock and key translation secure security Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encrypt-decrypt-concept-with-lock-and-key-translation-secure-security-96358171.html
encrypt decrypt concept with lock and key translation secure security Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encrypt-decrypt-concept-with-lock-and-key-translation-secure-security-96358171.htmlRFFGNDR7–encrypt decrypt concept with lock and key translation secure security
 Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-technology-internet-and-networking-concept-businessman-presses-138960592.html
Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-technology-internet-and-networking-concept-businessman-presses-138960592.htmlRMJ225J8–Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption
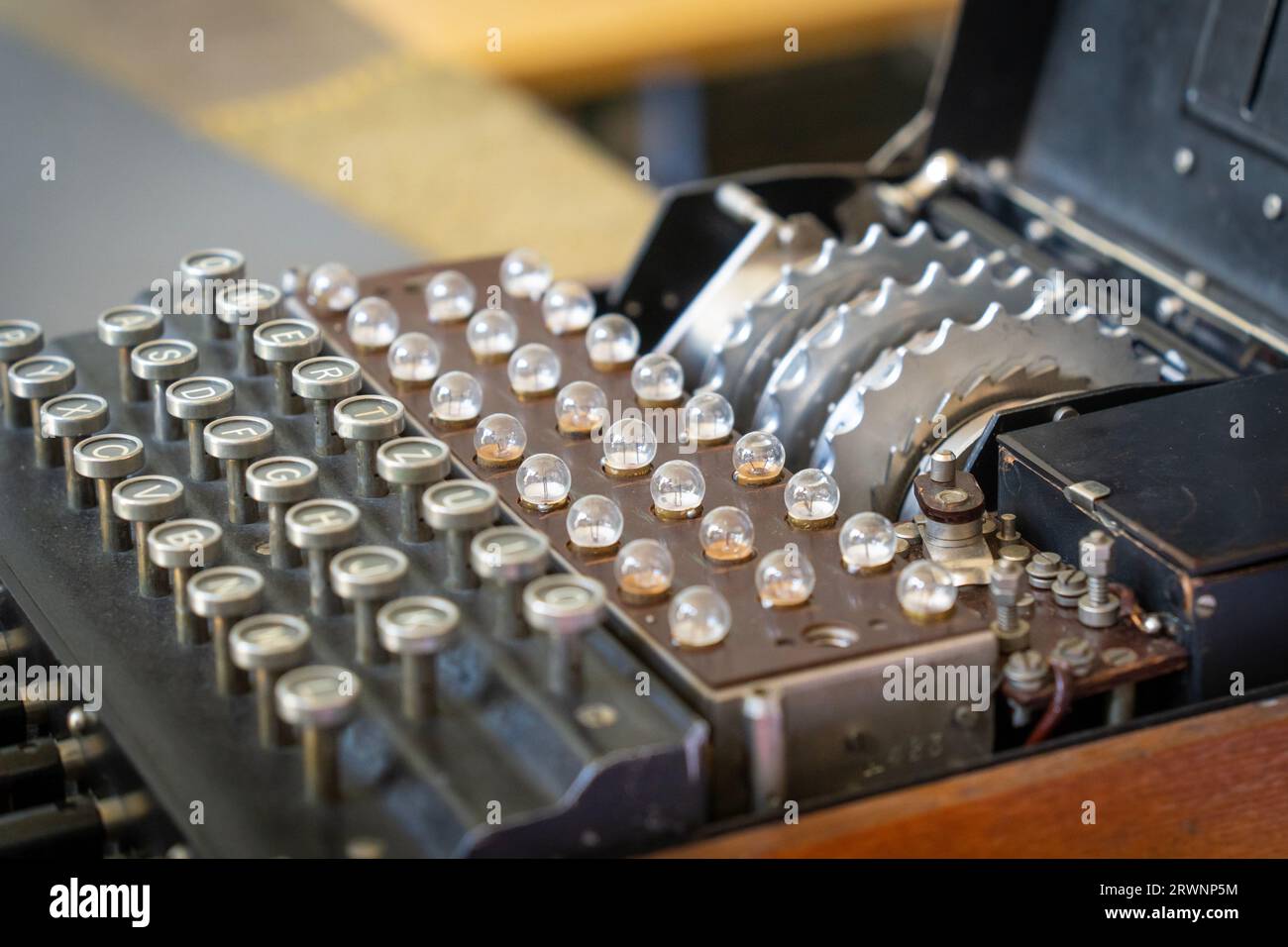 Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576576.html
Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576576.htmlRF2RWNP5M–Enigma, the German cipher machine created for sending messages during World War 2
 encryption eye looks at viewer concept background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encryption-eye-looks-at-viewer-concept-background-104082056.html
encryption eye looks at viewer concept background. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-encryption-eye-looks-at-viewer-concept-background-104082056.htmlRFG199M8–encryption eye looks at viewer concept background.
 Unlocking lock process flat 3d isometry isometric personal data security decryption login log in entrance concept web vector illustration. Creative te Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unlocking-lock-process-flat-3d-isometry-isometric-personal-data-security-decryption-login-log-in-entrance-concept-web-vector-illustration-creative-te-image235822970.html
Unlocking lock process flat 3d isometry isometric personal data security decryption login log in entrance concept web vector illustration. Creative te Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/unlocking-lock-process-flat-3d-isometry-isometric-personal-data-security-decryption-login-log-in-entrance-concept-web-vector-illustration-creative-te-image235822970.htmlRFRKJJGX–Unlocking lock process flat 3d isometry isometric personal data security decryption login log in entrance concept web vector illustration. Creative te
 Binary Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-binary-code-decryption-and-encoding-127586712.html
Binary Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-binary-code-decryption-and-encoding-127586712.htmlRMHBG248–Binary Code, Decryption and Encoding
 Black and white image of the plugboard of a rare German World War II 'Enigma' machine at Bletchley Park. January 2017 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-and-white-image-of-the-plugboard-of-a-rare-german-world-war-ii-enigma-machine-at-bletchley-park-january-2017-image476808026.html
Black and white image of the plugboard of a rare German World War II 'Enigma' machine at Bletchley Park. January 2017 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/black-and-white-image-of-the-plugboard-of-a-rare-german-world-war-ii-enigma-machine-at-bletchley-park-january-2017-image476808026.htmlRF2JKMDE2–Black and white image of the plugboard of a rare German World War II 'Enigma' machine at Bletchley Park. January 2017
 Better Decryption with a Business Team Racing Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-better-decryption-with-a-business-team-racing-concept-101952446.html
Better Decryption with a Business Team Racing Concept Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-better-decryption-with-a-business-team-racing-concept-101952446.htmlRFFWT9AP–Better Decryption with a Business Team Racing Concept
 Global computer network and Cloud computing business Transaction data storage technology concept, vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/global-computer-network-and-cloud-computing-business-transaction-data-storage-technology-concept-vector-illustration-eps10-image215907879.html
Global computer network and Cloud computing business Transaction data storage technology concept, vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/global-computer-network-and-cloud-computing-business-transaction-data-storage-technology-concept-vector-illustration-eps10-image215907879.htmlRFPF7CKK–Global computer network and Cloud computing business Transaction data storage technology concept, vector illustration eps10.
RF2PP389R–Lean startup line icons collection. Cryptography, Security, Encryption, Privacy, Decryption, Algorithms, Keys vector and linear illustration
 Cube with movable parts having on each side printed numbers than can be scrambled , image about data security and cryptography Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cube-with-movable-parts-having-on-each-side-printed-numbers-than-can-140844303.html
Cube with movable parts having on each side printed numbers than can be scrambled , image about data security and cryptography Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-cube-with-movable-parts-having-on-each-side-printed-numbers-than-can-140844303.htmlRFJ5409K–Cube with movable parts having on each side printed numbers than can be scrambled , image about data security and cryptography
 New computer virus protection cyber security concepts Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-new-computer-virus-protection-cyber-security-concepts-165421369.html
New computer virus protection cyber security concepts Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-new-computer-virus-protection-cyber-security-concepts-165421369.htmlRFKH3GJ1–New computer virus protection cyber security concepts
RF2J9140T–Decryption pixel perfect RGB color icon
 Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-and-encoding-image226269678.html
Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/decryption-and-encoding-image226269678.htmlRFR43D7X–Decryption and Encoding.
 Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722643.html
Binary code in the future digital abstract background. Modern technology hex code concept. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/binary-code-in-the-future-digital-abstract-background-modern-technology-hex-code-concept-image430722643.htmlRF2G0N33F–Binary code in the future digital abstract background. Modern technology hex code concept.
 Instant Access to Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-instant-access-to-decryption-169600510.html
Instant Access to Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-instant-access-to-decryption-169600510.htmlRFKRWY52–Instant Access to Decryption
 The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241931.html
The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-keyboard-and-rotors-from-a-historic-german-world-war-2-enigma-machine-on-display-at-bletchley-park-buckinghamshire-image454241931.htmlRF2HB0E63–The plugboard, keyboard and rotors from a historic German World War 2 Enigma machine on display at Bletchley Park, Buckinghamshire.
 William F. Friedman, American Cryptanalyst Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/william-f-friedman-american-cryptanalyst-image386295865.html
William F. Friedman, American Cryptanalyst Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/william-f-friedman-american-cryptanalyst-image386295865.htmlRF2DCD88W–William F. Friedman, American Cryptanalyst
RMH40EFR–Women's hand, key bundle, patent key, gesture, woman, hand, key, icon, conception, seal, close, open, unlock, lock, block, castle up, classified material, security, encryption, encode, decryption, decode, access, authorisation
 Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hut-1-at-bletchley-park-once-the-top-secret-home-of-the-world-war-two-codebreakers-now-a-leading-heritage-attraction-image246161628.html
Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hut-1-at-bletchley-park-once-the-top-secret-home-of-the-world-war-two-codebreakers-now-a-leading-heritage-attraction-image246161628.htmlRMT8DHJM–Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction
 Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-technology-internet-and-networking-concept-businessman-presses-138960658.html
Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-business-technology-internet-and-networking-concept-businessman-presses-138960658.htmlRMJ225MJ–Business, technology, internet and networking concept. Businessman presses a button on the virtual screen: Decryption
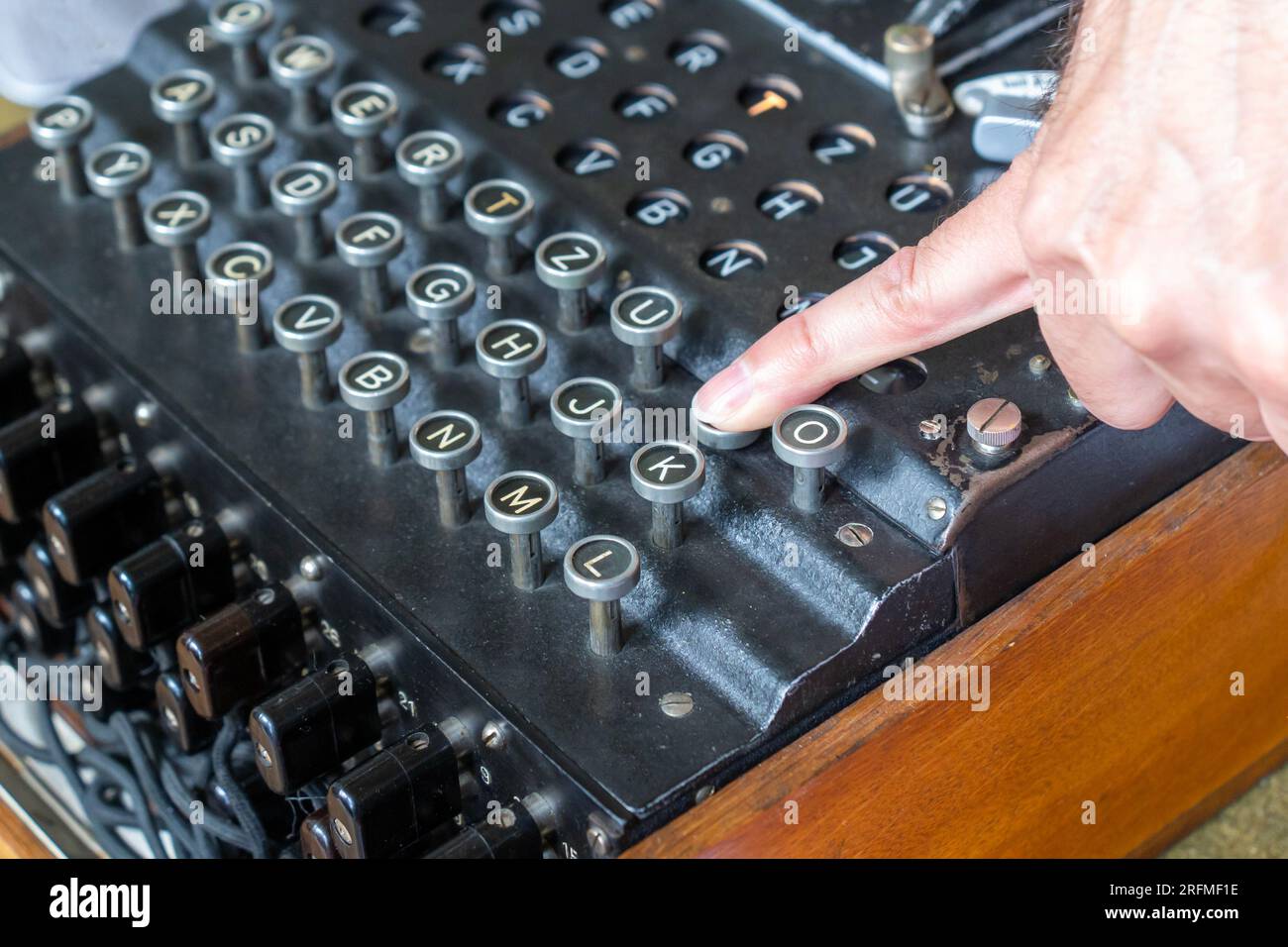 Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image560402458.html
Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image560402458.htmlRF2RFMF1E–Enigma, the German cipher machine created for sending messages during World War 2
 Data entry and text decoding on futuristic interface screen. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-entry-and-text-decoding-on-futuristic-interface-screen-image595138655.html
Data entry and text decoding on futuristic interface screen. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/data-entry-and-text-decoding-on-futuristic-interface-screen-image595138655.htmlRF2WG6WBY–Data entry and text decoding on futuristic interface screen.
 Cipher is an algorithm for performing encryption or decryption it is less common term is encipherment vintage line drawing or engraving illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cipher-is-an-algorithm-for-performing-encryption-or-decryption-it-is-less-common-term-is-encipherment-vintage-line-drawing-or-engraving-illustration-image244586903.html
Cipher is an algorithm for performing encryption or decryption it is less common term is encipherment vintage line drawing or engraving illustration. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cipher-is-an-algorithm-for-performing-encryption-or-decryption-it-is-less-common-term-is-encipherment-vintage-line-drawing-or-engraving-illustration-image244586903.htmlRFT5WW2F–Cipher is an algorithm for performing encryption or decryption it is less common term is encipherment vintage line drawing or engraving illustration.
 Data Code, Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127376522.html
Data Code, Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-data-code-decryption-and-encoding-127376522.htmlRMHB6E1E–Data Code, Decryption and Encoding.
 Indicator dials from the famous 'Bombe' machine at Bletchley Park used for deciphering German encrypted 'Enigma' messages. January 2017 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/indicator-dials-from-the-famous-bombe-machine-at-bletchley-park-used-for-deciphering-german-encrypted-enigma-messages-january-2017-image476808036.html
Indicator dials from the famous 'Bombe' machine at Bletchley Park used for deciphering German encrypted 'Enigma' messages. January 2017 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/indicator-dials-from-the-famous-bombe-machine-at-bletchley-park-used-for-deciphering-german-encrypted-enigma-messages-january-2017-image476808036.htmlRF2JKMDEC–Indicator dials from the famous 'Bombe' machine at Bletchley Park used for deciphering German encrypted 'Enigma' messages. January 2017
 Decryption in Business as Motivation in Stone Wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-in-business-as-motivation-in-stone-wall-59285829.html
Decryption in Business as Motivation in Stone Wall Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-decryption-in-business-as-motivation-in-stone-wall-59285829.htmlRFDCCKK1–Decryption in Business as Motivation in Stone Wall
 Cloud computing business Transaction data network storage technology concept. vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-computing-business-transaction-data-network-storage-technology-concept-vector-illustration-eps10-image215907920.html
Cloud computing business Transaction data network storage technology concept. vector illustration eps10. Stock Vectorhttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/cloud-computing-business-transaction-data-network-storage-technology-concept-vector-illustration-eps10-image215907920.htmlRFPF7CN4–Cloud computing business Transaction data network storage technology concept. vector illustration eps10.
RF2PNHP8T–Data encryption line icons collection. Cryptography, Security, Encryption, Privacy, Decryption, Algorithms, Keys vector and linear illustration
 Lawyer Olivier Martins pictured during a session of a drug trial that started after the decryption of encryption softwares Encrochat and Sky ECC, before the Brussels correctional court, at Justitia, in Brussels, Monday 18 December 2023. 125 people stand trial for their involvement in this case. Belgian and Dutch police cracked the self proclaimed 'most secure messaging platform you can buy' of Sky ECC cryptophone network and intercepted one billion messages. The decipherment has had a major impact on the actions taken by the judiciary and the police against organized crime in recent months. BE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lawyer-olivier-martins-pictured-during-a-session-of-a-drug-trial-that-started-after-the-decryption-of-encryption-softwares-encrochat-and-sky-ecc-before-the-brussels-correctional-court-at-justitia-in-brussels-monday-18-december-2023-125-people-stand-trial-for-their-involvement-in-this-case-belgian-and-dutch-police-cracked-the-self-proclaimed-most-secure-messaging-platform-you-can-buy-of-sky-ecc-cryptophone-network-and-intercepted-one-billion-messages-the-decipherment-has-had-a-major-impact-on-the-actions-taken-by-the-judiciary-and-the-police-against-organized-crime-in-recent-months-be-image576219990.html
Lawyer Olivier Martins pictured during a session of a drug trial that started after the decryption of encryption softwares Encrochat and Sky ECC, before the Brussels correctional court, at Justitia, in Brussels, Monday 18 December 2023. 125 people stand trial for their involvement in this case. Belgian and Dutch police cracked the self proclaimed 'most secure messaging platform you can buy' of Sky ECC cryptophone network and intercepted one billion messages. The decipherment has had a major impact on the actions taken by the judiciary and the police against organized crime in recent months. BE Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/lawyer-olivier-martins-pictured-during-a-session-of-a-drug-trial-that-started-after-the-decryption-of-encryption-softwares-encrochat-and-sky-ecc-before-the-brussels-correctional-court-at-justitia-in-brussels-monday-18-december-2023-125-people-stand-trial-for-their-involvement-in-this-case-belgian-and-dutch-police-cracked-the-self-proclaimed-most-secure-messaging-platform-you-can-buy-of-sky-ecc-cryptophone-network-and-intercepted-one-billion-messages-the-decipherment-has-had-a-major-impact-on-the-actions-taken-by-the-judiciary-and-the-police-against-organized-crime-in-recent-months-be-image576219990.htmlRM2TDD2DA–Lawyer Olivier Martins pictured during a session of a drug trial that started after the decryption of encryption softwares Encrochat and Sky ECC, before the Brussels correctional court, at Justitia, in Brussels, Monday 18 December 2023. 125 people stand trial for their involvement in this case. Belgian and Dutch police cracked the self proclaimed 'most secure messaging platform you can buy' of Sky ECC cryptophone network and intercepted one billion messages. The decipherment has had a major impact on the actions taken by the judiciary and the police against organized crime in recent months. BE
 Cyber attack, target bank database Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-cyber-attack-target-bank-database-167170454.html
Cyber attack, target bank database Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-cyber-attack-target-bank-database-167170454.htmlRFKKY7HA–Cyber attack, target bank database
RF2J956CP–Decryption pixel perfect gradient linear vector icon
 Data Code, Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-data-code-decryption-and-encoding-168897105.html
Data Code, Decryption and Encoding. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-data-code-decryption-and-encoding-168897105.htmlRFKPNWYD–Data Code, Decryption and Encoding.
 The German World War 2 Enigma encryption/decryption device Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-the-german-world-war-2-enigma-encryptiondecryption-device-165211917.html
The German World War 2 Enigma encryption/decryption device Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-image-the-german-world-war-2-enigma-encryptiondecryption-device-165211917.htmlRMKGP1DH–The German World War 2 Enigma encryption/decryption device
 Algorithm Binary, Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/algorithm-binary-data-code-decryption-and-encoding-image226260577.html
Algorithm Binary, Data Code, Decryption and Encoding Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/algorithm-binary-data-code-decryption-and-encoding-image226260577.htmlRFR431JW–Algorithm Binary, Data Code, Decryption and Encoding
 The plugboard from a German World War 2 'Enigma' encryption machine at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-from-a-german-world-war-2-enigma-encryption-machine-at-bletchley-park-buckinghamshire-image454241997.html
The plugboard from a German World War 2 'Enigma' encryption machine at Bletchley Park, Buckinghamshire. Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/the-plugboard-from-a-german-world-war-2-enigma-encryption-machine-at-bletchley-park-buckinghamshire-image454241997.htmlRF2HB0E8D–The plugboard from a German World War 2 'Enigma' encryption machine at Bletchley Park, Buckinghamshire.
 Elizebeth Friedman, American Cryptanalyst Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/elizebeth-friedman-american-cryptanalyst-image386295691.html
Elizebeth Friedman, American Cryptanalyst Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/elizebeth-friedman-american-cryptanalyst-image386295691.htmlRF2DCD82K–Elizebeth Friedman, American Cryptanalyst
RMH40D3Y–Women's hand, key bundle, patent key, gesture, woman, hand, key, icon, conception, seal, close, open, unlock, lock, block, castle up, classified material, security, encryption, encode, decryption, decode, access, authorisation
 Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hut-1-at-bletchley-park-once-the-top-secret-home-of-the-world-war-two-codebreakers-now-a-leading-heritage-attraction-image246161627.html
Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/hut-1-at-bletchley-park-once-the-top-secret-home-of-the-world-war-two-codebreakers-now-a-leading-heritage-attraction-image246161627.htmlRMT8DHJK–Hut 1 at Bletchley Park, once the top-secret home of the World War Two Codebreakers, now a leading heritage attraction
 Concept of business security, safety of information from virus, crime and attack. Internet secure system. Protection system. Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-concept-of-business-security-safety-of-information-from-virus-crime-138960896.html
Concept of business security, safety of information from virus, crime and attack. Internet secure system. Protection system. Decryption Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/stock-photo-concept-of-business-security-safety-of-information-from-virus-crime-138960896.htmlRMJ22614–Concept of business security, safety of information from virus, crime and attack. Internet secure system. Protection system. Decryption
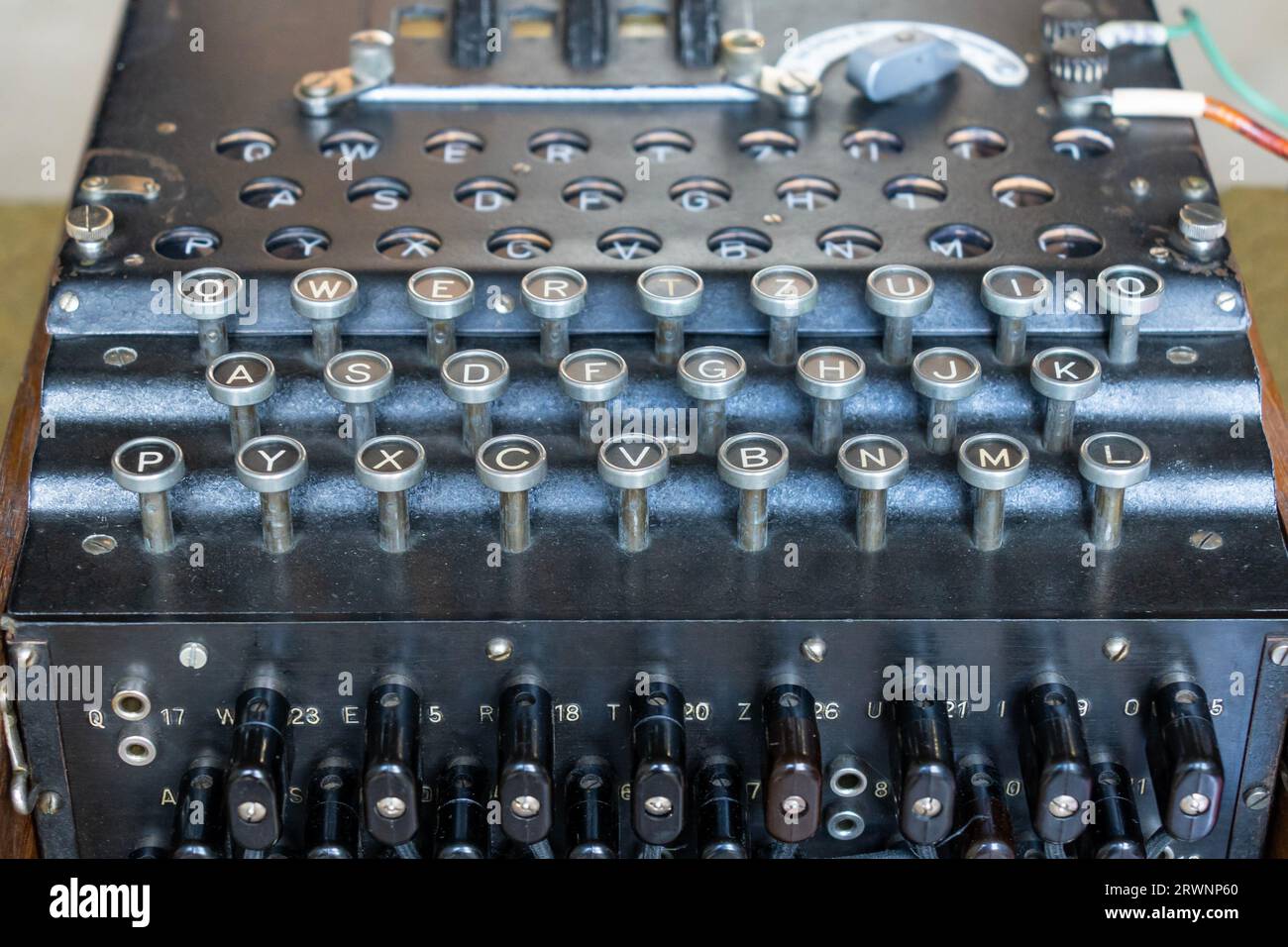 Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576584.html
Enigma, the German cipher machine created for sending messages during World War 2 Stock Photohttps://www.alamy.com/licenses-and-pricing/?v=1https://www.alamy.com/enigma-the-german-cipher-machine-created-for-sending-messages-during-world-war-2-image566576584.htmlRF2RWNP60–Enigma, the German cipher machine created for sending messages during World War 2
Search Results for Decryption Stock Photos and Images (5,346)
Page 1 of 54